Our blogs

IAM
What is Identity and Access Management (IAM)?
Sep 26, 2025
PAM
Top 10 Benefits of Privileged Access Management (PAM)
Aug 20, 2025
Concept
What is the Difference Between SAML vs OAuth vs OpenID Connect?
Aug 14, 2025
MDM
Lockdown Android Tablet for Business with miniOrange MDM
Aug 1, 2025
concepts
Zero Trust Security Model: Complete Guide to Implementation in 2025
Jul 1, 2025
Latest Posts

AD Tools
Active Directory Management Challenges You Must Know in 2026
Nov 26, 2025

MDM
What is Android Fastboot Mode?
Nov 25, 2025

AD Tools
Complete Guide to Active Directory Management: A Must-Read for Every IT Admin
Nov 25, 2025

MDM
How to Manage Multiple Android Devices Remotely
Nov 25, 2025
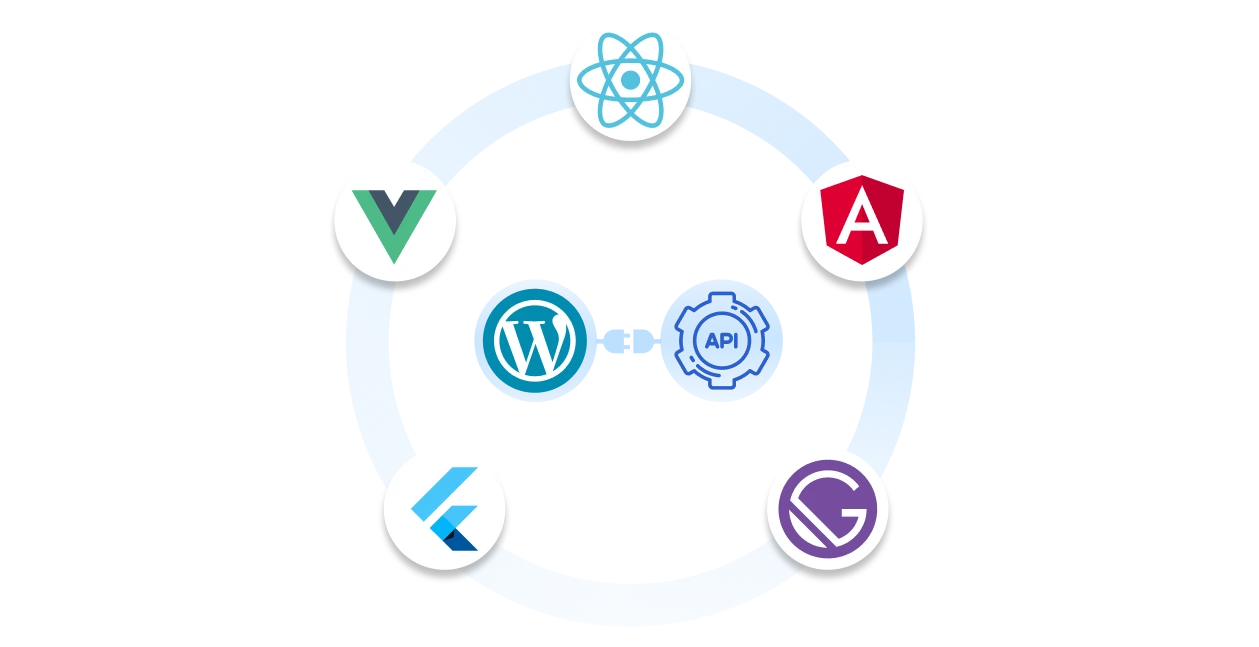
WordPress
What is Headless WordPress and How Single Sign On (SSO) Secures It
Nov 24, 2025
AD Tools
How to Reduce Password Reset Tickets and Enhance Password Security
Nov 24, 2025

