When security leaders talk about risk, the conversation usually drifts toward ransomware gangs, zero-day exploits, or state-sponsored actors. Fair enough. Those threats are loud and visible.
Yet many of the most damaging breaches begin somewhere quieter. Inside the organization. An employee exporting a customer database before resigning. A contractor reusing credentials across systems. A system administrator with broad privileges and very little oversight.
Therefore, Insider threat prevention is not just another security checkbox. It forces uncomfortable questions. Who inside your organization has access to what? How much of that access is truly necessary? And if something goes wrong, how quickly would you even notice?
Understanding how to prevent insider threats requires a mix of governance, monitoring, and technical controls. But it also demands realism. Not every insider is malicious. Not every mistake is negligence. The problem is much layered than most frameworks admit.

What Is an Insider Threat?
An insider threat occurs when a person, maybe employees, contractors, vendors, or partners with legitimate access to organizational systems, misuses that access either intentionally or accidentally, leading to data loss, fraud, or system compromise.
The definition sounds straightforward. But the implications are not always.
Unlike external attackers, insiders are already sitting behind the firewall. They pass authentication checks. They understand internal processes. Some of them even hold privileged access to production servers, financial systems, or identity infrastructure. That makes insider threat prevention significantly harder than blocking an unknown IP address.
In practice, internal threats are often tied to identity and access management (IAM) failures. Excessive permissions accumulate over time. Role changes are not reflected in access controls. Shared admin accounts exist because they are “convenient.” Over months or years, this builds a quiet attack surface inside your environment.
The uncomfortable truth is that preventing insider threats is inseparable from controlling privilege. If you do not know who holds elevated access, you cannot realistically claim to have insider threat prevention in place.
3 Types of Insider Threats You Should Know
All internal threats can’t be lumped into one category. The types of insider threats differ in motivation, behavior, and detection complexity.
1. Malicious Insider Threats
These types of threats are intentional.
Examples include a disappointed employee exporting proprietary designs before joining a competitor. A finance manager manipulating payment workflows. A database admin selling customer records. Motivations can vary, maybe financial gain. Revenge. Ideological conflict. Sometimes simply leverage during a job transition.
From an insider threat prevention standpoint, the challenge here is privilege concentration. Malicious insiders tend to exploit existing elevated access. They do not need to hack in. They log in. If your monitoring cannot distinguish between legitimate administrative tasks and suspicious bulk data extraction, you are exposed.
2. Negligent (Careless) Insider Threats
In this scenario, damage comes unintentionally, which compromises organizational security through poor or ignorant actions of internal users. Examples include an employee clicking a phishing link and exposing VPN credentials. A developer storing API keys in a public repository. A staff member uploading sensitive data to personal cloud storage to “work from home”.
Negligent behavior remains one of the most common types of insider threats in cyber security. Preventing insider threats in this category requires both education and guardrails. Multi-factor authentication, restricted data movement controls, and contextual access policies reduce the blast radius of mistakes.
3. Compromised Insider
This is where things blur. A legitimate user’s credentials are stolen. An attacker logs in as that user and moves laterally. On paper, all activity appears valid. In reality, the account is hijacked. Compromised insiders are particularly dangerous because traditional perimeter defenses see nothing unusual. The activity originates from a trusted identity.
Effective insider threat prevention must therefore include anomaly detection. If a payroll employee suddenly accesses source code repositories at 2 a.m., that is not normal. Detection tools must surface that deviation quickly.
Insider Threat Prevention: Step-by-Step Framework
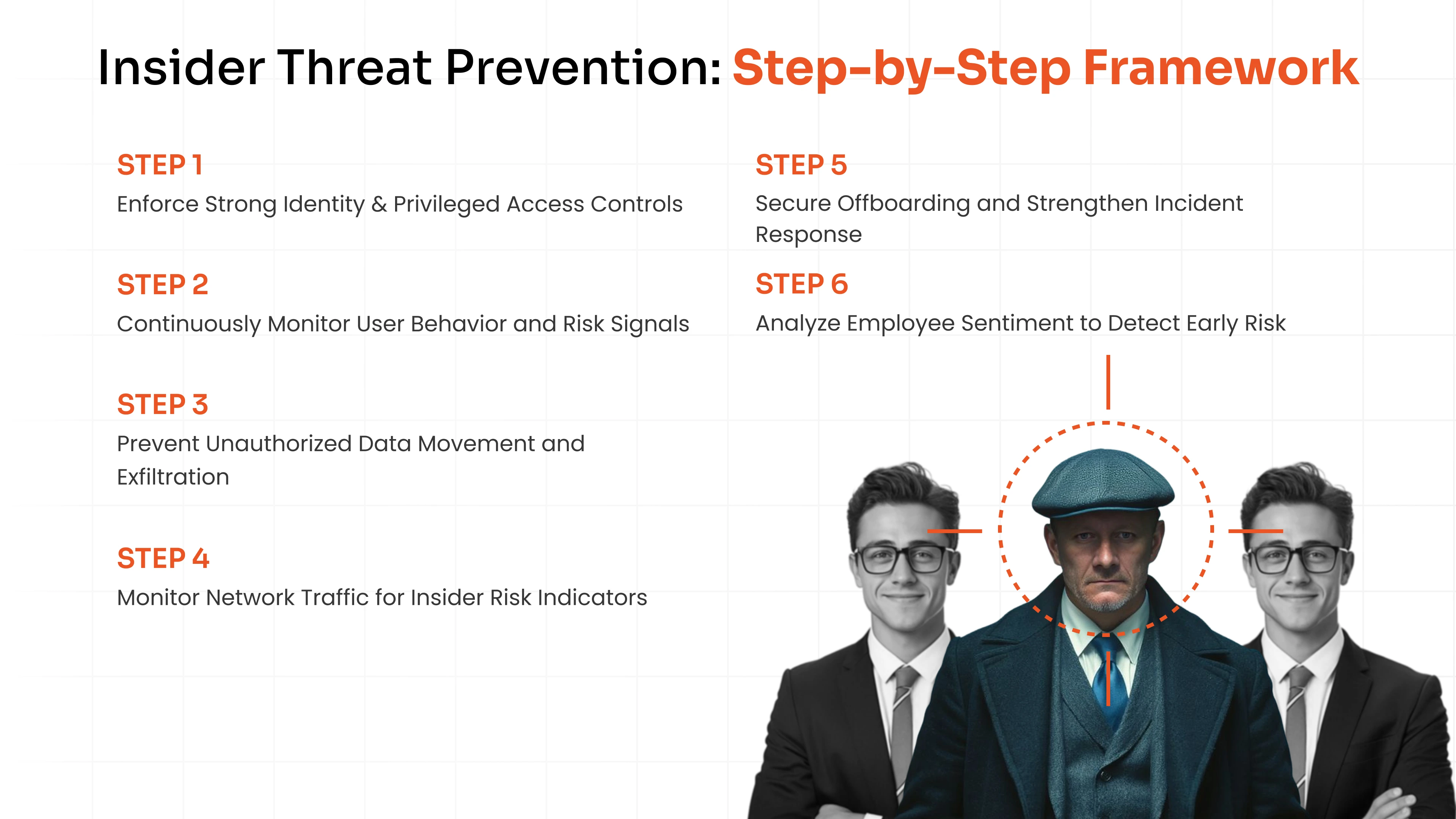
There are some ways and methods which can be implemented across your organization to limit the insider threats and reduce the probability of it.
Step 1: Enforce Strong Identity & Access Controls Using IAM and PAM
Mature IAM or PAM solutions, like miniOrange PAM, plays a central role in preventing insider threats. By vaulting privileged credentials, enforcing session recording, applying role based access control and overall implementing the principle of least privileged by giving temporary elevated access on just in time basis. A single PAM solution can limit both malicious and compromised insider activity.
If your organization still relies on shared admin passwords or standing privileges, insider threat prevention is more theoretical than real. It may be time to reassess your privileged access strategy and evaluate a dedicated PAM deployment.
Step 2: Monitor User Behavior Continuously
Insider threat prevention depends on visibility. Logging, session monitoring, and behavioral analytics must work together. Anomalies should trigger alerts, not sit buried in logs.
User behavior analysis helps identify insider threat behavioral indicators such as unusual login times, abnormal data downloads, or access to systems outside normal job scope.
However, monitoring must be tuned carefully. Excessive false positives create alert fatigue, and then real signals get ignored. Precision matters.
Step 3: Protect Sensitive Data
Restrict clipboard actions during privileged sessions. Block unauthorized USB transfers. Limit uploads to unsanctioned cloud storage. Enforce data classification and tagging.
Privileged session monitoring is particularly effective here. If an administrator attempts to export large volumes of sensitive data, the session can be recorded, terminated, or flagged in real time.
Insider threat detection tools are useful, but without data protection controls, detection becomes post-incident forensics rather than prevention.
Step 4: Monitor Your Network
Most internal activity flows through your corporate network. That is both an advantage and a blind spot.
Enforce VPN usage. Block known malicious domains. Monitor outbound traffic patterns. Watch for encrypted tunnels to unsanctioned endpoints. If an employee bypasses security protocols or connects to suspicious infrastructure, that is an early signal. Internal threats often leave subtle traces before escalating.
Yet network monitoring alone is insufficient. Without identity context, traffic logs remain abstract. Integrating network data with IAM and PAM insights strengthens insider threat prevention significantly.
Step 5: Secure Offboarding & Incident Response
A surprising number of breaches involve former employees whose access was never revoked.
Immediate deprovisioning is mandatory. Access to email, VPN, cloud applications, and privileged systems must be terminated at once. Notice-period users should be monitored more closely. That is not paranoia. It is risk management.
Moreover, organizations should maintain a documented insider incident response plan. Who investigates? How are sessions reviewed? When are legal teams involved? Without a predefined process, response becomes improvised. That rarely ends well.
Step 6: Conduct Employee Sentiment Analysis
Sometimes this step is dismissed as “soft.” But it is one of the most important.
Disgruntled employees are not automatically malicious, but dissatisfaction can increase vulnerability to recruitment or risky behavior. Understanding workplace sentiment provides context.
Surveys, structured interviews, or ethical monitoring of collaboration platforms can surface early warning signs. Of course, privacy considerations apply. Overly intrusive monitoring may damage trust, ironically increasing insider risk.
Insider threat prevention is not purely a technical challenge. Employee disengagement contributes to an estimated 84% to 95% of insider-related data breaches. Organizational culture plays a measurable role in reducing overall risk.
What Causes Insider Threats?
The root causes are usually systemic, not dramatic. Over-privileged accounts accumulate because access reviews are irregular. Credential reuse persists because password policies are inconsistent. Offboarding processes fail because HR and IT operate in silos.
Low security awareness compounds the issue. If employees do not understand why controls exist, they circumvent them.
Ultimately, internal threats occur in environments where identity governance is weak and monitoring is fragmented.
Insider Threat Detection Tools & Technologies
Technology does not completely eliminate insider risk. It narrows the window of opportunity. Let’s look at the tools and solutions that can help you detect insider threats before they occur.
1. Privileged Access Management (PAM)
A robust PAM solution plays a foundational role in preventing insider threats. By centralizing credential vaulting, enforcing Just-in-Time access, and recording privileged sessions, PAM reduces standing privileges and increases accountability. It directly addresses one of the primary causes of insider incidents: excessive, unmanaged access.
For organizations evaluating how to mitigate insider threats, implementing PAM tools like miniOrange PAM is often the most immediate structural improvement. Activating a controlled PAM trial can help validate its impact on privilege governance and monitoring.
2. User & Entity Behavior Analytics (UEBA)
UEBA platforms analyze user behavior patterns and detect deviations. They are particularly useful for identifying compromised insiders and subtle malicious activity.
However, behavioral analytics without strong access controls can generate noise. Detection must be paired with enforcement.
3. SIEM & EDR
Security Information and Event Management systems aggregate logs across infrastructure. Endpoint Detection and Response tools monitor device-level activity.
Combined, they provide visibility across endpoints and networks. Yet they rely heavily on identity context. Without integrating with IAM and PAM, they may miss subtle privilege misuse.
miniOrange PAM Solution’s Role in Preventing Insider Threats
When discussing the PAM solution role in preventing insider threats, specifics matter.
A platform like miniOrange PAM enforces principle of least privilege, supports identity-based role-based controls, and enables time-bound privileged elevation. More importantly, it provides session recording, real-time monitoring and audit trails that transform administrative access from opaque to observable.
For CISOs and CIOs, that visibility translates into measurable risk reduction. For security analysts, it means actionable alerts rather than scattered logs. For IT administrators, it removes the operational burden of managing shared credentials manually.
No single solution guarantees perfect insider threat prevention. But reducing standing privileges, monitoring privileged sessions, and enforcing contextual access controls dramatically lowers the probability of internal abuse.
If your organization is evaluating how to prevent insider threats in a scalable way, reviewing your privileged access architecture is not optional. It is foundational.
Conclusion
Insider threat prevention is not glamorous. It lacks the drama of external cyber warfare narratives. Yet in many environments, it represents the more probable risk.
The question is not whether insiders can cause damage. They can. The real question is whether your access controls, monitoring systems, and privileged management architecture are mature enough to stop them before the damage becomes irreversible.
FAQs
Who Can Be Considered an Insider?
Employees, contractors, vendors, partners, and even former staff with lingering access. Anyone with legitimate system credentials qualifies.
What Causes Insider Threats?
Excessive access, weak monitoring, poor offboarding processes, credential compromise, and low security awareness are common causes. Insider threat prevention begins by addressing these systemic gaps.
Which Industries Are Most Vulnerable to Insider Threats?
Financial services, healthcare, technology, and government sectors face heightened risk due to sensitive data and concentrated privileged access. However, any organization with digital assets is exposed to internal threats.
What Are Best Practices for Responding to an Insider Incident?
Immediately contain access. Preserve logs and session recordings. Conduct forensic analysis. Involve legal and HR teams early. Finally, reassess access governance policies to prevent recurrence.



Leave a Comment