Consider this: Your employees log in through Azure AD. Your contractors use Google. Your vendors authenticate via Okta. Your JSM customers are on AWS Cognito. Four identity systems. One Atlassian instance. And natively, only one identity provider is allowed.
That is not a configuration oversight, it is a hard limit built into Atlassian Cloud. If you need multiple identity providers, the only native path is an upgrade to the Atlassian Enterprise tier, a cost increase that applies across your entire user base, not just the teams or workflows that actually need multi-provider authentication.
Most organizations do not need everything that comes with Enterprise. They need one thing: the ability to let different user groups, employees, partners, contractors, and JSM customers, authenticate through the identity provider they already use.
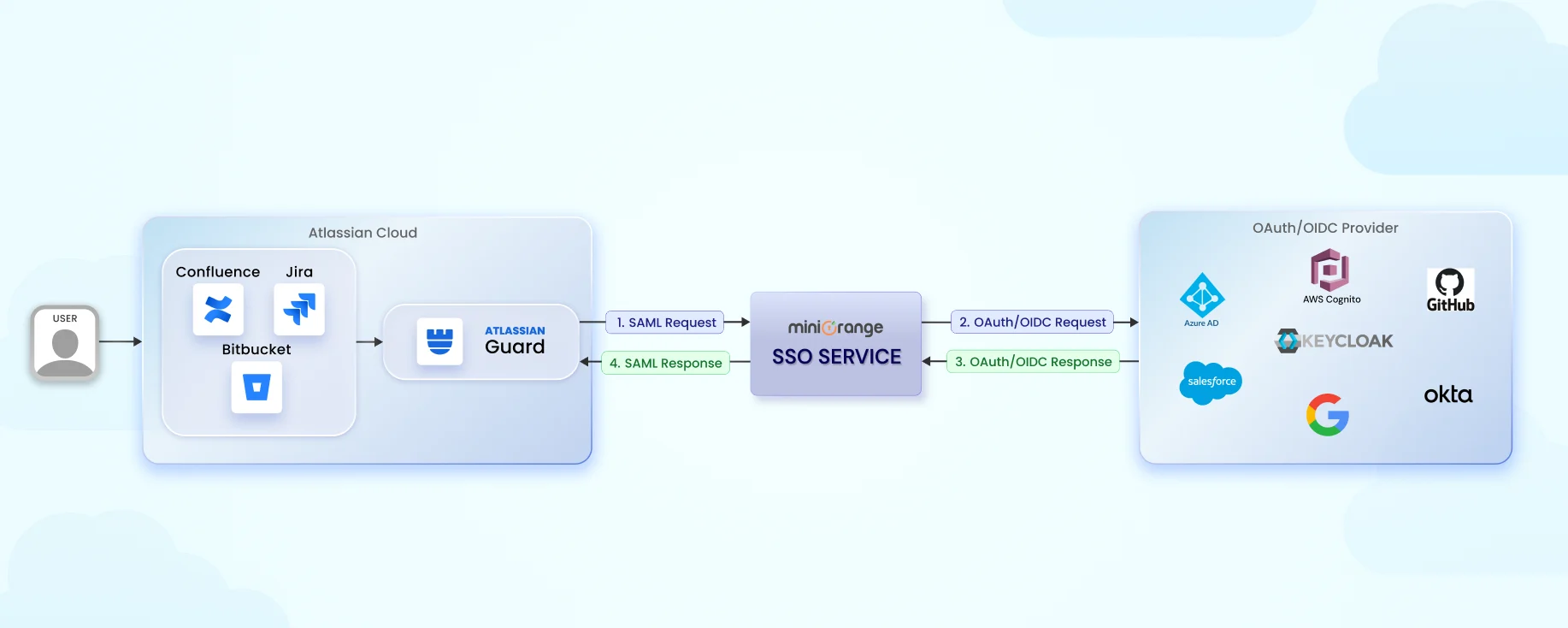
The miniOrange OAuth/OIDC SSO app solves exactly that. It enables simultaneous connections to Azure AD, Okta, Google, Keycloak, AWS Cognito, and any custom OAuth 2.0 or OpenID Connect provider, directly inside Jira Cloud and Confluence Cloud, on your existing Atlassian plan. Domain-based login routing, a central login selection page, JSM customer authentication for external domains, and per-group provider assignment are all included without a plan change.
Why Atlassian Cloud's Single Identity Provider Limit Is a Problem for Growing Organizations
Most organizations today run more than one identity system. A typical setup looks like this:
- Azure AD for full-time employees
- Okta for partners or vendors
- Google for contractors or temporary users
- AWS Cognito for customer-facing applications
This multi-provider setup works across most tools in the stack, but not inside Atlassian Cloud.
With native Atlassian authentication:
- Atlassian Guard Standard supports only one identity provider
- Adding more providers requires upgrading to Atlassian Enterprise
- That upgrade increases cost across the entire Atlassian user base, not just for authentication
This creates a real problem for IT teams. They need multiple authentication providers, but the only native path is a full platform upgrade they do not actually need.
A simpler solution exists: enabling multi-provider OAuth SSO directly inside Jira or Confluence using the miniOrange OAuth/OIDC SSO app, without changing your Atlassian plan.
Atlassian Native SSO vs. miniOrange Multi-Provider OAuth SSO
| Capability | Guard Standard | Guard Enterprise | miniOrange OAuth SSO + Guard Standard |
|---|---|---|---|
| Multiple Identity Providers | ✗ | ✓ | ✓ |
| OAuth / OIDC Provider Support | ✗ | ✗ | ✓ |
| Domain-Based Login Routing | ✗ | ✗ | ✓ |
| Cusotmise IDP Selection Page | ✗ | ✗ | ✓ |
The pattern is consistent: Guard Standard handles single-provider SAML well, but organizations with more complex identity needs hit a ceiling. miniOrange removes that ceiling without requiring a plan change.
Why Multiple OAuth Providers Is a Business Requirement
Supporting multiple identity providers is not just a technical preference, it solves real operational problems that appear repeatedly across organizations of different sizes and industries.
Mergers and Acquisitions
When two companies merge, each organization typically has its own identity system. Migrating thousands of users into one directory immediately is time-consuming and carries real risk. Multi-provider authentication allows both directories to authenticate users from day one, without forcing a migration before the business is ready.
B2B Collaboration
Many organizations give partners, vendors, or agencies access to Jira or Confluence. These external users already authenticate through their own identity providers. Without OAuth SSO, IT teams end up managing separate accounts, repeated password resets, and duplicated user records across directories. Allowing users to log in with their existing provider eliminates that overhead entirely.
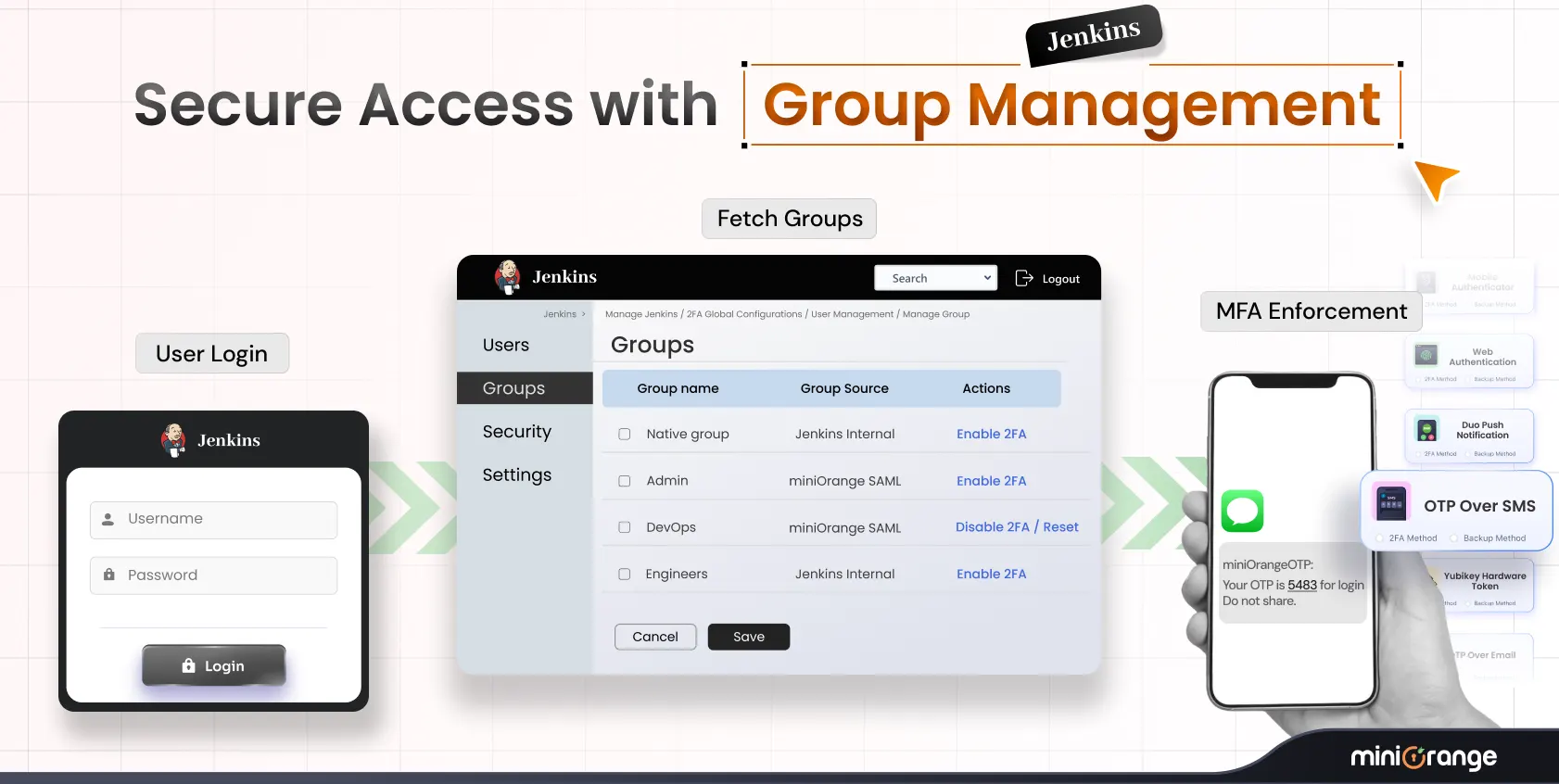
Security Segmentation
Different user groups often require different authentication paths. Keeping these flows separate reduces risk while maintaining centralized visibility and control. A common model looks like this:
- Employees: Azure AD or Okta
- Contractors: Google login
- Vendors: Custom OAuth provider
- JSM Customers: AWS Cognito or any OAuth-compatible provider
Each group authenticates through the appropriate system, and no single compromise affects the others.
How miniOrange Handles Multi-Provider Authentication
Supporting multiple providers requires a reliable way to route users to the correct identity provider at login. miniOrange provides three complementary options, which can be used independently or together depending on the organization's needs.
Domain-Based Login Routing
The app automatically routes users to the correct identity provider based on their email domain. Users are redirected without needing to choose their login method, the experience is seamless.
| Email Domain | Identity Provider |
|---|---|
| @company.com | Azure AD |
| @partner.com | Okta |
| @contractor.org | |
| @customer.io | AWS Cognito |
Central Login Selection Page
For environments where multiple organizations access the same Atlassian instance, administrators can enable a Choose Your Login Provider page. Users see clearly labeled options such as:
- Login with Azure AD
- Login with Okta
- Login with Google
- Login with AWS Cognito
This works particularly well for JSM portals where customers arrive from different organizations and need to authenticate through their own provider.
Multiple OAuth / OpenID Connections
Administrators can configure multiple providers in the app simultaneously, including:
- Azure AD
- Okta
- Keycloak
- AWS Cognito
- Any custom OAuth 2.0 or OpenID Connect provider
Each provider can be scoped to specific user groups, giving administrators granular control over who authenticates through which system.
Coming Soon: Based on a high volume of feature requests from customers, several additional configuration options and provider-specific enhancements are planned for upcoming releases. These will extend routing flexibility and group-level controls further.
Real-World Use Cases for Multi-Provider OAuth SSO in Jira Cloud and Confluence Cloud
Partner Access to Jira
Many companies allow partners to collaborate directly inside Jira projects. With multi-provider OAuth SSO, partners authenticate through their own identity provider, no local accounts, no separate credentials, no IT overhead for provisioning.
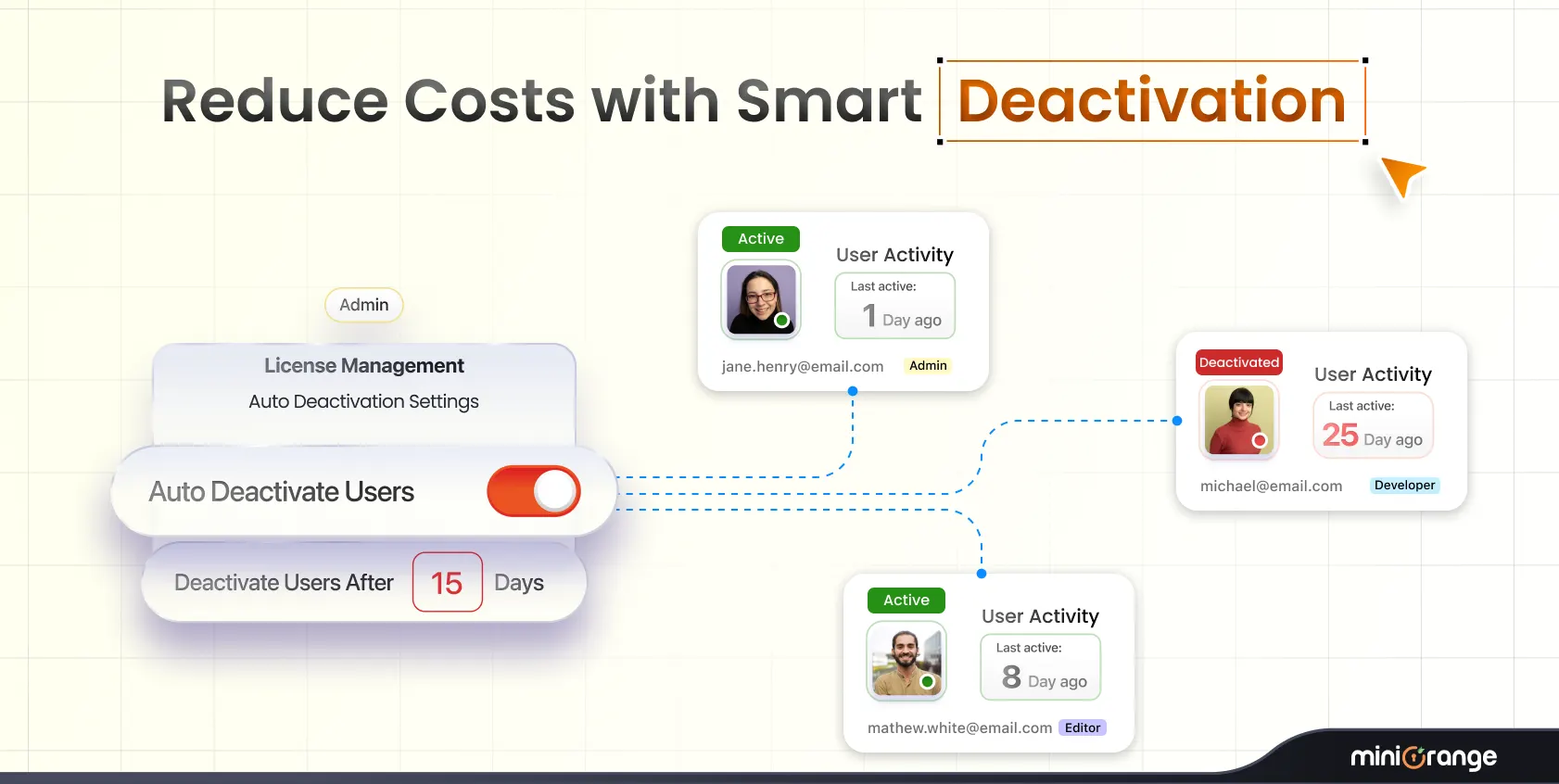
Contractor Access to Confluence
Consultants and contractors often work temporarily inside Confluence workspaces. Instead of creating manual user accounts that need to be cleaned up later, they authenticate using Google or their corporate OAuth provider and are automatically deprovisioned when access is revoked at the source.
JSM Customer Authentication
For organizations running Jira Service Management externally, miniOrange supports authentication for JSM customers even when their email domains are not owned or verified by your organization. Customers log in using their own identity provider, whether that is Google, AWS Cognito, or a custom OAuth setup, without requiring a managed Atlassian account.
Multi-Organization Atlassian Instances
Organizations managing multiple subsidiaries or business units can route users to different identity providers based on email domain. Separate identity management is preserved without needing separate Atlassian environments.
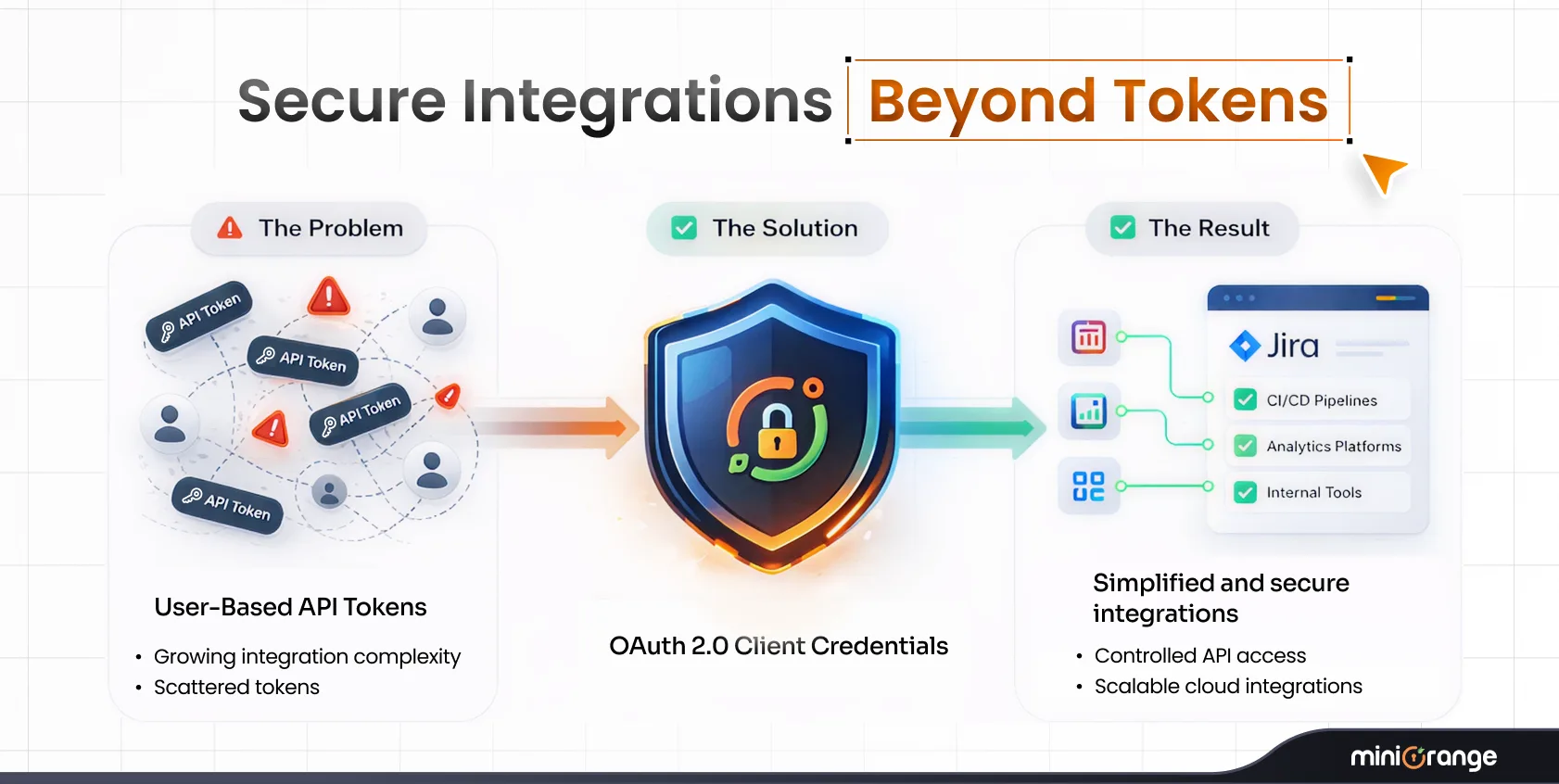
Business Impact: Right-Sized Security Without the Enterprise Price Tag
Avoid Enterprise Upgrade Costs
Multi-provider OAuth SSO for Jira Cloud and Confluence Cloud works on any Atlassian plan. Organizations get Enterprise-grade authentication flexibility without the Enterprise-tier price increase applied across their entire user base.
Support JSM Customers and External Users
miniOrange supports authentication for JSM customers on domains your organization does not own or manage. This is essential when working with vendors, partners, or end customers who need access to Atlassian tools but exist entirely outside your directory.
Faster Deployment
Identity consolidation projects typically take weeks. Multi-provider OAuth SSO can be configured in a fraction of that time and requires no directory migration. Organizations can onboard partners quickly, support post-merger access from day one, and defer or avoid complex directory consolidation projects entirely.
Frequently Asked Questions
Q. Can Atlassian Cloud support multiple OAuth providers natively?
No. Native Atlassian authentication supports only one identity provider unless you upgrade to the Enterprise tier. Multi-provider SSO for Jira Cloud and Confluence Cloud requires a third-party app such as miniOrange.
Q. Why do organizations need multiple identity providers in Atlassian?
Organizations work with partners, vendors, contractors, and JSM customers who authenticate through different identity providers. Multi-IDP authentication allows each group to log in using their existing system without creating or managing new accounts.
Q. Does Atlassian Guard Standard support OAuth providers?
Guard Standard primarily supports SAML identity providers and does not provide flexible multi-provider OAuth or OIDC routing.
Q. Can JSM customers authenticate without domain verification?
Yes. With the miniOrange OAuth/OIDC SSO app, JSM customers can authenticate through their own identity provider even if their domain is not owned or verified by your organization.
Q. How does domain-based login routing work?
The app reads the user's email domain during login and automatically redirects them to the correct identity provider. For example, @company.com routes to Azure AD while @partner.com routes to Okta. Users never have to select their provider manually.
Q. Is AWS Cognito supported?
Yes. AWS Cognito is supported as a fully configurable OAuth/OIDC provider, making it a strong option for organizations running customer-facing Jira Service Management portals.
Ready to Enable Multi-Provider OAuth SSO?
If your organization works with partners, contractors, or JSM customers, or if you're managing multiple identity systems after a merger, multi-provider OAuth SSO is the most cost-effective way to handle authentication in Atlassian Cloud without upgrading your plan.
The miniOrange OAuth/OIDC SSO app is available for both Jira Cloud and Confluence Cloud, with a free trial so you can validate the setup against your environment before committing.
- Jira OAuth SSO, Configure multi-provider authentication for Jira Cloud
- Confluence OAuth SSO, Set up SSO for Confluence Cloud
- Explore All Atlassian SSO Solutions, View the full miniOrange Atlassian app portfolio
Leave a Comment