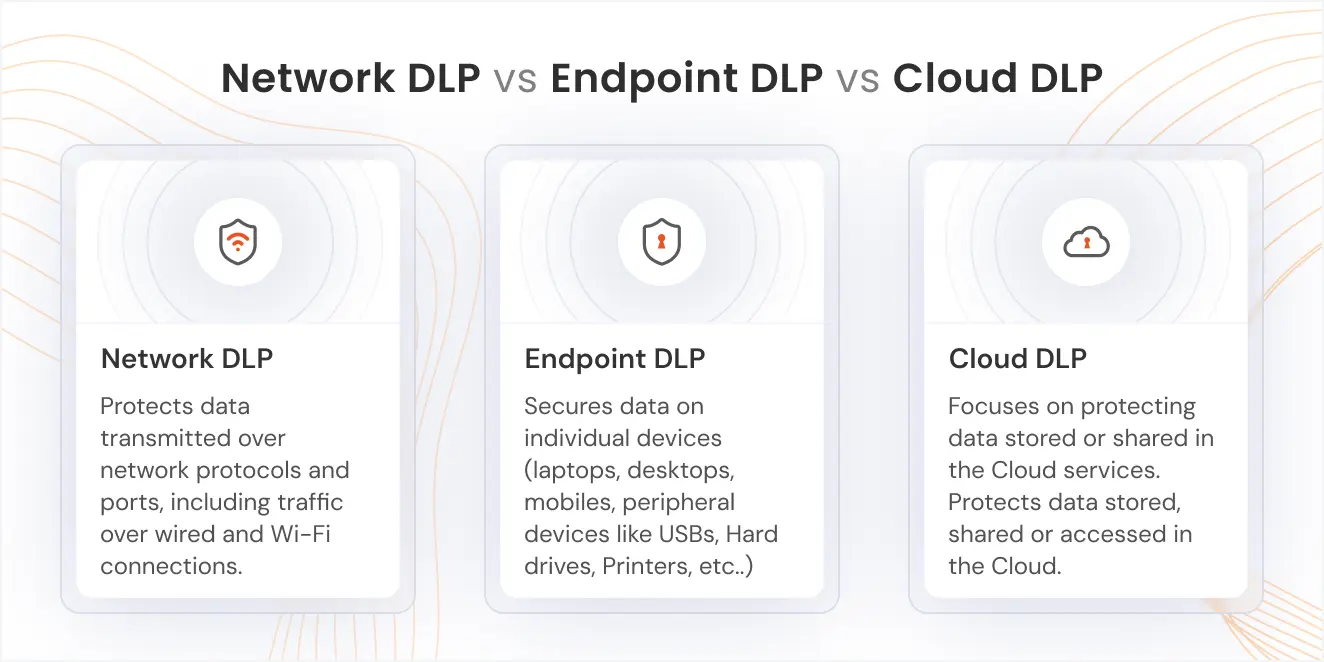
Difference between Network DLP vs Endpoint DLP vs Cloud DLP
When it comes to protecting business-sensitive data, understanding the difference and the scope of Network DLP, Endpoint DLP, and Cloud DLP is essential. Each of these Data Loss Prevention solutions (DLP) plays a unique role in securing data across various environments, whether it is on the Network, on individual devices, or in the Cloud. Knowing how each solution works can help you determine the best approach to safeguard your organization's sensitive information.
In this blog, we will explain the differences between the Network DLP, Endpoint DLP, and Cloud DLP and understand their use cases.
What is Data Loss Prevention (DLP)?
Data Loss Prevention (DLP) is a solution used to protect sensitive data from being exposed, lost, or accessed by unauthorized users. A Data Loss Prevention solution helps organizations prevent data breaches by monitoring, detecting, and responding to potential threats across different environments. Whether the data is stored on the Network, Endpoint devices, or in the Cloud, DLP solutions are essential in ensuring that critical information is protected at all times.
Key Steps and How Does DLP Work?
A Data Loss Prevention solution works through a series of essential steps to safeguard sensitive data. Here are the key steps involved:
- Data Discovery & Classification: The first step is identifying and classifying sensitive data across different channels, such as Network, Endpoint, and Cloud environments, ensuring critical information is categorized based on its sensitivity.
- Policy Definition: Once the data is discovered and classified, the next step is setting policies that define how sensitive data should be handled, shared, and protected. These policies are customized according to the organization's security requirements and regulatory obligations.
- Data Monitoring & Detection: The DLP solution continuously monitors data movement and user behavior to detect any suspicious activities or potential threats, such as unauthorized access or data transfer.
- Data Exfiltration Prevention: The system actively prevents data exfiltration, ensuring sensitive data is not transferred or leaked to unauthorized users or external systems, whether through email, USB drives, or Cloud storage.
- Response & Remediation: If a data breach or policy violation is detected, the DLP system triggers a response, which may include alerting administrators, blocking the action, or encrypting the sensitive data to prevent further exposure.
By following these steps, a DLP solution provides comprehensive protection for sensitive data across all environments.
DLP Demo
Discover how a DLP solution can safeguard your data. Request a DLP demo today!
Comparison Table (Network DLP vs Endpoint DLP vs Cloud DLP)
| Parameter | Network DLP Solution | Endpoint DLP Solution | Cloud DLP Solution |
|---|---|---|---|
| Scope | Protects data transmitted over network protocols and ports, including traffic over wired and Wi-Fi connections. | Secures data on individual devices (laptops, desktops, mobiles, peripheral devices like USBs, External Hard drives, Printers and more.) | Focuses on protecting data stored or shared in the Cloud services. |
| Data Protection | Protects data in transit across the Network. | Protects data at rest and in use on Endpoints. | Protects data stored, shared, or accessed in the Cloud. |
| Deployment | Deployed on individual endpoints, such as laptops, desktops, and RDPs. Provides direct control over data on those devices. | Installed on individual devices or Endpoints | Deployed in the Cloud environment, integrated with Cloud platforms |
| Scalability | Easily scalable across a variety of devices in an organization without significant hardware requirements, making it ideal for growing businesses. | Scales easily, as each device is independently protected | Highly scalable as it grows with Cloud environments |
| Precision | Effective at detecting data leaks and unauthorized activities on the endpoint, such as file transfers or application access that may violate data policies. | Focuses on device-level threats with more granular control | Effective in detecting Cloud-based threats and unauthorized access |
| Maintenance | Requires minimal maintenance compared to the other types of DLP solutions, but still needs periodic updates and policy adjustments to stay aligned with organizational security goals. | Requires individual updates per Endpoint device | Maintenance is handled by the Cloud provider, with updates typically seamless |
| Benefits | Ensures data security on all user devices, providing visibility and control over data access and transfers at the endpoint level. | Provides protection directly on Endpoints, preventing data loss from lost or stolen devices | Simplifies management of Cloud data security, protects against Cloud-specific threats |
| Challenges | Can become resource-intensive on devices, potentially affecting system performance, especially on older hardware or when scaling across many devices. | Can be bypassed if Endpoints are compromised or offline | Dependent on the Cloud provider's security measures, potential integration complexity |
| Use-cases | Ideal for organizations with remote or mobile workers who need endpoint-level security and for businesses that need control over individual device data. | Best for organizations with mobile or remote workforces, securing devices | Ideal for businesses that heavily use Cloud storage, SaaS, or Cloud-based applications |
Network DLP vs Cloud DLP vs Endpoint DLP: Why Each Matters for Data Protection
When it comes to protecting sensitive data, it is crucial to understand how Network DLP, Endpoint DLP, and Cloud DLP each have a different role in securing an organization’s data across different environments. Each solution addresses a specific area of data protection, and together they form a stronger security posture.
Network DLP
Network DLP focuses on securing data as it moves through the organization’s Network.
It helps prevent sensitive information from leaving the Network without proper authorization by monitoring data traffic and enforcing security policies.
This makes Network DLP especially important for organizations with high volumes of internal and external data transfers.
Endpoint DLP
The endpoint DLP solution is designed to protect data directly on user devices such as laptops, desktops, mobile devices, and more.
It ensures that sensitive information remains secure even when devices are used remotely or outside the corporate Network.
An endpoint DLP solution is particularly valuable for organizations with remote employees or a Bring Your Own Device (BYOD) environment.
Cloud DLP
Cloud DLP focuses on protecting data stored and shared within Cloud platforms.
As businesses increasingly rely on Cloud applications and Cloud storage, Cloud DLP helps prevent unauthorized access and data exposure in these environments.
It ensures sensitive data remains protected while enabling secure collaboration in the Cloud.
Each of these DLP solutions plays an important role in a complete data protection strategy, depending on where data is stored, accessed, and shared within the organization.
Need for Network, Endpoint, and Cloud DLP
Organizations today handle sensitive data across multiple environments, which makes relying on a single security layer risky. Network, Endpoint, and Cloud DLP work together to provide complete data protection and reduce the chances of data loss. Below are the key reasons why all three are essential.
1. Data Visibility
Network, Endpoint, and Cloud DLP provide clear visibility into sensitive data such as personally identifiable information (PII), PHI, and PCI data. This visibility helps organizations understand where critical data is stored, how it is accessed, and how it is shared across systems.
2. Location-Based Data Protection
Data moves between corporate Networks, user devices, and Cloud platforms. Network, Endpoint, and Cloud DLP ensure data is protected at every location, including environments that support BYOD policies, where employees use personal devices to access business data.
3. Use of Cloud and SaaS Applications
As organizations increasingly rely on Cloud and SaaS applications, sensitive data like PII, PHI, and PCI data is often stored and shared outside traditional Networks. Cloud DLP helps secure this data, while Network and Endpoint DLP add additional layers of protection.
4. Insider Threats and Human Errors
Data loss is often caused by accidental actions or internal misuse. Endpoint DLP solution and Network DLP help reduce risks related to insider threats and human errors by controlling how sensitive data, such as PII and PHI is accessed, shared, or transferred.
5. Compliance and Regulatory Requirements
Organizations must comply with regulations that mandate the protection of sensitive data, including PII, PHI, and PCI information. Network DLP, Endpoint DLP solution, and Cloud DLP solutions support compliance efforts by enforcing consistent data protection policies across all environments.
Benefits of Network, Endpoint, and Cloud DLP
Using Network DLP, Endpoint DLP, and Cloud DLP together provides a strong and balanced approach to data security. These solutions help organizations protect sensitive information across all environments while reducing risk and operational effort.
1. Reduced Data Breaches
Network DLP, Endpoint DLP, and Cloud DLP help prevent unauthorized access, sharing, or transfer of sensitive data. By protecting data across Networks, devices, and Cloud platforms, organizations can significantly reduce the risk of data breaches.
2. Improved Visibility
DLP solutions offer better visibility into where sensitive data is stored and how it is used. This allows security teams to monitor data movement, detect risky behavior, and take action before data loss occurs.
3. Automated Compliance Enforcement
DLP solutions help enforce data protection policies automatically. This ensures sensitive data is handled according to regulatory requirements without relying solely on manual processes or user awareness.
4. Lower Incident Response Costs
By detecting and preventing data loss early, DLP solutions reduce the time and resources needed to respond to security incidents. This leads to lower investigation, remediation, and recovery costs for the organization.
How to Protect Your Data with miniOrange DLP?
miniOrange DLP helps organizations secure sensitive data across the Network, Endpoints, and Cloud environments. Below are the key ways it protects your data:
- Centralized Data Discovery and Classification
Identifies and classifies sensitive data such as personally identifiable information, PHI, and PCI data across Networks, Endpoints, and Cloud platforms. - Unified Policy Enforcement
Applies consistent data protection policies across Network traffic, user devices, and Cloud applications to prevent unauthorized data access and sharing. - Real Time Monitoring and Alerts
Continuously monitors data movement and user activity to detect suspicious behavior and prevent data loss in real time. - Protection Against Insider Threats and Human Errors
Reduces the risk of accidental or intentional data exposure by enforcing controls on data usage across Endpoints and Cloud environments. - Compliance and Audit Readiness
Supports regulatory compliance by automating data protection controls and providing detailed logs and reports for audits. - Simplified Management
Offers a centralized dashboard to manage DLP policies and monitor data security across the entire organization.
Contact us at uemsupport@xecurify.com to learn more and get started with a DLP solution that fits your organization’s needs!


Leave a Comment