Jira silently accumulates PII, credentials, and sensitive data through everyday team use. Security and compliance teams can detect and remediate this exposure using miniOrange's DLP PII Scanner, which scans historical and real-time content without disrupting workflows.
There's a moment every security or compliance professional dreads. It's not a dramatic breach. It's quieter than that. It's the moment during a routine audit when someone pulls up a Jira ticket from six months ago, and right there, in plain text inside a comment, is a customer's phone number. Or a Social Security Number. Or worse, a live API key that's been sitting there, exposed, across dozens of user permissions, for half a year.
Nobody put it there maliciously. That's the thing. Someone just needed to give context fast, and Jira was where the work was happening. But that's exactly how sensitive data finds its way into places it should never be.
And the problem doesn't stop at Jira's walls, if an external breach ever occurs, sensitive data sitting unredacted in your Jira tickets, like API keys connected to third-party apps, becomes a direct entry point into systems far beyond Atlassian.
And if you think your Jira instance is the exception, consider this:
| Statistic | What It Means |
|---|---|
| 65% of organizations have found sensitive data in unexpected places | Cloud collaboration tools are among the top sources |
| $4.45 million, average cost of a data breach in 2025 | Internal tools and cloud misconfigurations are key contributors |
The Problem: Jira Was Built for Collaboration, Not Data Security
Jira is genuinely excellent at what it's designed to do, track work, manage sprints, organize projects, and keep teams aligned. The very things that make it great are also what make it a quiet data security risk.
Think about how your team uses Jira on a normal day:
- A support agent copies a customer's email address into a ticket for context
- A developer pastes an API token into a bug report to help reproduce an issue
- An HR manager logs a contractor's details in a task while the HR system is temporarily down
- A QA engineer drops test account credentials into a comment to assist a colleague
None of these feel like security incidents at the moment. They feel like people are doing their jobs efficiently. But over weeks and months, across hundreds of projects and thousands of issues, your Jira instance quietly accumulates a sprawling inventory of sensitive information, accessible to far more people than it should be.
What Kind of Sensitive Data Are We Talking About?
| Category | Examples |
|---|---|
| Personally Identifiable Information (PII) | Full names, email addresses, phone numbers, home addresses |
| Financial Data | Credit card numbers, bank account details, billing information |
| Government IDs | Social Security Numbers, passport numbers, national ID numbers |
| Credentials & Secrets | API keys, OAuth tokens, passwords, private keys |
| Protected Health Information (PHI) | Medical record numbers, diagnosis details, insurance IDs |
| Custom / Internal Data | Internal employee IDs, project codenames, proprietary codes |
If it's sensitive, chances are it's shown up in a Jira ticket somewhere, possibly yours.
Why Sensitive Data Leaks Harder to Fix Than You Think
You might be thinking: we have policies for this. Or: we can just run a search and clean it up. The reality is considerably messier.
Manual Auditing Doesn't Scale
A mid-sized organization running Jira for two or three years can easily have tens of thousands of issues across dozens of projects. Searching for sensitive data manually, even with JQL, is like looking for a needle in a haystack when you're not even sure what the needle looks like in every context.
Policies Without Enforcement Are Just Documents
You can tell your team not to paste PII into Jira tickets. But when someone is in the middle of a critical support escalation and needs to move fast, that policy is the last thing on their mind. The behavior isn't malicious, it's human.
Native Jira Controls Only Go So Far
Issue security schemes and field-level permissions help restrict who can see data, but they don't help you find sensitive data that's already been entered incorrectly. They're access controls, not detection tools.
Atlassian Guard Has Real Blind Spots
Atlassian Guard Detect does offer native scanning, but it comes with meaningful limitations:
| Limitation | Impact |
|---|---|
| Only scans on create or update events | Existing sensitive data goes undetected |
| Doesn't scan file attachments | A major blind spot for PDFs, Docs, spreadsheets |
| Limited field type coverage | Custom fields and certain free-text areas are excluded |
| Requires Guard Premium plan | Adds cost and is not available on Government Cloud |
The Solution: DLP PII Scanner for Jira by miniOrange
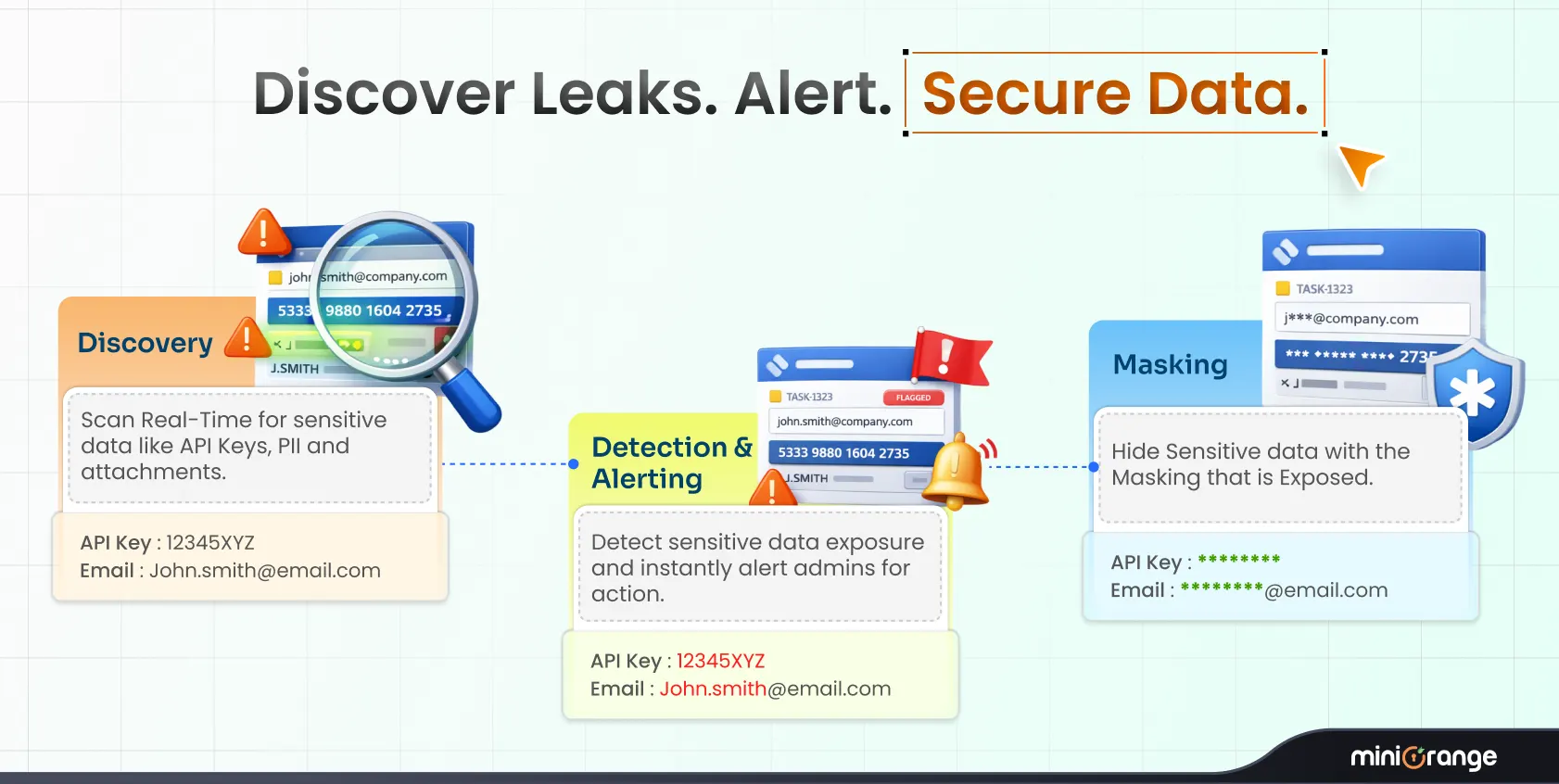
This is exactly the gap that miniOrange's Data – PII Scanner (DLP) for Jira is designed to close.
Rather than overhauling how your team uses Jira or adding friction to daily workflows, it works in the background, systematically scanning your Jira content, surfacing sensitive data, and giving you the tools to act on what it finds. It moves you from hoping nothing sensitive is in there to actually knowing what's there and being able to do something about it.
Read more about how to prevent data leaks in your Atlassian stack.
Ready to Take Control of Sensitive Data in Your Jira Instance?
How It Works, At a Glance
| Step | What Happens |
|---|---|
| 1. Install | Add the app from the Atlassian Marketplace in minutes |
| 2. Define Rules | Create individual detection rules for 80+ data types or add custom regex patterns for data unique to your organization |
| 3. Build Reusable Templates | Combine related rules into reusable templates that can be shared across multiple policies |
| 4. Create Policies | Build policies from one or more templates and apply them to relevant Jira projects |
| 5. Scan | Run scans across issues; real-time for new and updated content (including existing issues when edited), on-demand for everything else |
| 6. Review Violations | View detailed reports on the dashboard identifying affected issues and owners |
| 7. Remediate | Redact, flag for review, or remove sensitive content directly within Jira |
Key Features
| Feature | What It Does |
|---|---|
| 80+ Data Type Detection | Scans for PII, PHI, credentials, financial data, and more out of the box |
| Real-Time Scanning | Catches sensitive data as issues are created or updated |
| Custom Regex Rules | Build detection rules for data types unique to your organization |
| Classifications & Policies | Group rules and apply them selectively across projects |
| Concise Dashboard | Monitor all violations and PII leaks from one clear view |
| Detailed Findings | Pinpoint the exact issue, field, and owner for every violation |
| Automated Redaction | Redact sensitive content via Atlassian Forge, no external data transfer |
| Data Stays in Jira | Everything is processed within the Atlassian ecosystem. Critically, even if an external breach occurs, the damage is contained—sensitive data like API keys to third-party apps gets redacted before it can be exploited outside Jira |
| Attachment Scanning | Extend coverage to PDFs, Docs, spreadsheets, and other file types |
| Audit & Redaction Logs | Full traceability for compliance and governance reporting |
Who Needs This?
The short answer: any organization that uses Jira at scale and has to think about data privacy, compliance, or security. That covers most of them. But some teams feel this pain more acutely than others.
| Who | Why It Matters |
|---|---|
| Security & Compliance Teams | Audit readiness, demonstrable DLP controls, reduced breach risk |
| Jira Admins | Visibility into what's in your instance without manual effort |
| Healthcare Organizations | HIPAA requires strict controls over PHI, Jira is not exempt |
| Financial Services | PCI-DSS compliance, credit card and account data exposure risks |
| Legal & HR Teams | Handle highly sensitive personal data as part of daily workflows |
| Fast-Growing Teams | More users + more integrations = growing exposure surface |
| Companies Facing Audits | SOC 2, ISO 27001, GDPR audits demand documented DLP evidence |
The Bottom Line
Jira was never designed to be a data vault, but for thousands of organizations, that's quietly what it has become. Every ticket, every comment, every custom field is a potential home for sensitive data that shouldn't be there.
The good news is that this isn't an unsolvable problem. It just requires the right cloud DLP solution, one built specifically for the Jira environment, that understands how teams actually work, and that gives admins real visibility and real control without demanding that everyone change how they do their jobs.
miniOrange's Data – PII Scanner (DLP) for Jira does exactly that. It's practical, policy-driven, and built on Atlassian Forge. It works quietly in the background, surfaces problems before they become crises, and gives your team the confidence to say, for the first time, that you actually know what's inside your Jira instance.
That kind of clarity is hard to put a price on. Especially when the alternative is finding out the hard way.
FAQs
1. What types of sensitive data does miniOrange DLP PII Scanner for Jira detect?
The app detects over 80 types of sensitive data out of the box, including personally identifiable information (PII), financial data, credentials, and protected health information (PHI). You can also create custom regex-based rules to detect data types specific to your organization.
2. Will it scan Jira issues that were created before the app was installed?
Yes, and this is one of the key advantages over native tools like Atlassian Guard Detect. Guard only scans content at the point it's created or updated, which means historical data goes undetected. miniOrange DLP PII Scanner allows you to run scans across existing Jira issues so you can identify sensitive data that's already there, not just what gets added going forward.
3. Is our data sent to external servers during scanning?
No. The app is built on Atlassian Forge, which means all scanning and redaction happens entirely within the Atlassian ecosystem. Your sensitive data is never transferred to external servers, it stays inside your Jira environment throughout the entire process.
4. How is this different from Atlassian Guard Detect?
Atlassian Guard Detect is a solid native option, but it has meaningful limitations, it only scans on create or update events, doesn't cover file attachments, requires a Guard Premium plan, and offers limited policy control at the project level. miniOrange DLP PII Scanner fills those gaps: it scans existing content, supports 80+ data types, enables custom regex rules, applies project-level policies, and is available as a standalone app without needing Guard Premium.

Leave a Comment