Third-party vendors are an essential part of modern enterprise operations, providing critical services such as infrastructure maintenance, application support, system integrations, and managed IT services. To perform these tasks, vendors often require remote access to internal systems, frequently with elevated privileges. While this access enables operational efficiency, it also introduces significant security risks if not managed properly.
In recent years, organizations have increasingly suffered security incidents originating from poorly secured vendor connections. Attackers actively target vendor accounts because they often have broad access, long-lived permissions, and limited oversight. Without strong vendor remote access security in place, a single compromised vendor credential can lead to unauthorized system access, lateral movement, and large-scale data exposure.
To prevent third-party data breaches, teams must adopt a structured approach that prioritizes identity verification, least privilege access, continuous monitoring, and automated governance. This blog outlines proven Vendor remote access security best practices that helps you reduce risk while maintaining secure and efficient collaboration with external partners.
What Is Vendor Remote Access?
Vendor remote access refers to the ability of external vendors, contractors, or service providers to connect remotely to an organization’s internal systems, applications, or infrastructure. Vendors typically require this access to perform tasks such as troubleshooting issues, managing servers, deploying updates, or supporting business-critical applications.
Unlike internal employees, vendors operate outside the organization’s direct security perimeter. They may access systems from unmanaged devices, different networks, or multiple customer environments. This makes securing vendor remote access significantly more challenging, as businesses often lack visibility into vendor activity and struggle to enforce consistent security controls.
Vendor remote access frequently involves privileged permissions, allowing third parties to modify system configurations, access sensitive data, or manage user accounts. If these privileges are not tightly controlled, they can easily exceed their original scope, creating persistent access paths that attackers can exploit.

Vendor Remote Access Security Best Practices
Implementing strong controls around vendor remote access requires a layered approach that combines identity security, access governance, and continuous oversight. The following vendor remote access best practices address the most common risk areas.
1. Conduct a Thorough Vendor Risk Assessment
Before granting any remote access, security teams should evaluate a vendor’s security posture, access requirements, and compliance readiness. This includes reviewing breach history, certifications, internal security controls, and the scope of access requested. Ongoing reassessments ensure that vendor risk does not change unnoticed over time.
2. Enforce Multi-Factor Authentication (MFA)
Multi-factor authentication is one of the most effective remote access security best practices. Requiring MFA for all vendor logins significantly reduces the risk of credential-based attacks, even if passwords are compromised. MFA should be enforced consistently across VPNs, cloud platforms, administrative consoles, and privileged systems.
3. Just-in-Time (JIT) & Time-Bound Access
Standing privileges create unnecessary exposure. Just-in-Time access limits vendor permissions to specific time windows and tasks, automatically revoking access when no longer needed. This approach drastically reduces the opportunity for misuse and is a foundational control for securing vendor remote access.
4. No Shared Vendor Accounts
Each vendor user should have a unique identity tied to their role and responsibilities. Eliminating shared accounts improves accountability, enables precise access controls, and simplifies auditing. Identity-based access also ensures that actions can be traced back to individual users, which is essential for investigations and compliance.
5. Perform Continuous Auditing
Vendor access should be reviewed regularly to ensure permissions remain appropriate. Continuous auditing helps identify excessive privileges, dormant accounts, and policy violations before they are exploited. Automated reviews are especially important in dynamic environments with frequent vendor changes.
6. Record All Vendor Sessions
Real-time monitoring and session recording provide critical visibility into vendor activity. By capturing what vendors do during privileged sessions, you can detect anomalies, investigate incidents faster, and meet audit requirements. Session visibility is a key control for preventing third-party data breaches.
7. Enforce Least Privilege Access
Vendors should only receive the minimum permissions required to complete approved tasks. Least privilege or just enough access reduces the blast radius of compromised accounts and prevents vendors from accessing unrelated systems or sensitive data. Permissions should be granular, role-based, and regularly reviewed.
8. Restrict Access by Network and Device
Access should be limited to trusted networks, approved gateways, and authorized devices whenever possible. Network and device restrictions add an additional layer of defense by blocking access from high-risk locations or unmanaged endpoints.
9. Automate Access Provisioning and Deprovisioning
Manual access management often leads to delays and errors. Automating vendor onboarding and offboarding ensures access is granted only when needed and revoked immediately when engagements end. This reduces orphaned accounts, which are a common cause of third-party security incidents.
10. Integrate Logs with SIEM and SOC
Centralizing vendor access logs improves threat detection and response. When vendor activity is correlated with other security events, you gain better context for identifying suspicious behavior and responding quickly to potential breaches.
11. Provide Security Training for All Users
Security awareness is a shared responsibility. Vendors should be trained on acceptable use policies, authentication requirements, and secure access practices. Internal teams should also understand how to manage third-party remote access securely to reduce human error and misconfigurations.
Core Principles for Securing Vendor Remote Access
Least Privilege Access
Implement the principle of least privilege by assigning vendors minimal permissions required for their tasks, such as specific servers, ports, and protocols. Use role-based access control (RBAC) and just-in-time (JIT) provisioning to grant temporary access only during scheduled windows. This zero-trust approach ensures no over-privileging, aligning with NIST guidelines for secure vendor management.
Multi-Factor Authentication
Mandate strong MFA for every vendor login, layering biometrics, hardware tokens, or push notifications beyond passwords. Verify not just identity but device health, like OS updates, antivirus status, and contextual factors. Integrate adaptive authentication that escalates scrutiny for anomalies. This multi-layered defense thwarts 99% of account takeover attempts, per industry reports, making it essential for remote vendor security.
Network Segmentation
Isolate vendor access via DMZ gateways or bastion hosts, preventing direct connectivity to production networks. Employ micro-segmentation to compartmentalize resources, allowing outbound-initiated connections only. Use VPNs with clientless portals or RDP gateways for protocol restriction. This containment strategy limits blast radius during incidents, a core zero-trust tactic recommended by cybersecurity frameworks like MITRE.
Session Monitoring
Continuously record and log all vendor sessions, capturing keystrokes, commands, and file transfers for forensic review. Implement real-time alerts for suspicious behaviors, like unusual data exfiltration attempts. Enforce session timeouts and one-click kill switches for immediate revocation. Integrate SIEM tools for anomaly detection. Full visibility ensures accountability and rapid incident response, transforming remote access into an auditable, controlled process.
Vendor Lifecycle Management
Manage the full vendor lifecycle: vet credentials during onboarding, conduct quarterly access reviews, and automate offboarding to revoke all tokens/rules upon contract end. Require security training, SLAs for patching, and compliance audits. Use centralized IAM platforms for provisioning/deprovisioning. This proactive governance minimizes shadow access risks, ensuring vendors remain secure partners throughout engagement.
Why Vendor Remote Access Is a High-Risk Attack Vector?
Vendor remote access is one of the most exploited entry points in modern enterprise environments. While vendors are essential for business continuity, the way access is traditionally granted often creates systemic security weaknesses that attackers actively target.
Broad and Persistent Access
Vendors frequently require access to multiple systems over extended periods of time. In many companies, this access remains active long after a task is completed, creating standing privileges that significantly expand the attack surface. Persistent access makes it easier for attackers to exploit compromised credentials without triggering immediate detection.
Operate Outside Standard Security Controls
Unlike employees, vendors typically connect from unmanaged devices, external networks, and varying locations. This makes it harder to enforce consistent endpoint security, network policies, and behavioral baselines. Without strong controls, third-party remote access can bypass traditional perimeter defenses entirely.
Shared Credentials and Weak Authentication
Many organizations still rely on shared vendor accounts or static passwords for remote access. These credentials are difficult to rotate, hard to track, and nearly impossible to audit. Once compromised, shared credentials allow attackers to blend in with legitimate vendor activity, increasing dwell time and impact.
Limited Visibility into Their Activity
A lack of monitoring and session visibility makes it difficult to understand what vendors are doing once connected. Without detailed logs or session recordings, suspicious activity often goes unnoticed until damage has already occurred. This visibility gap is a major contributor to delayed breach detection.
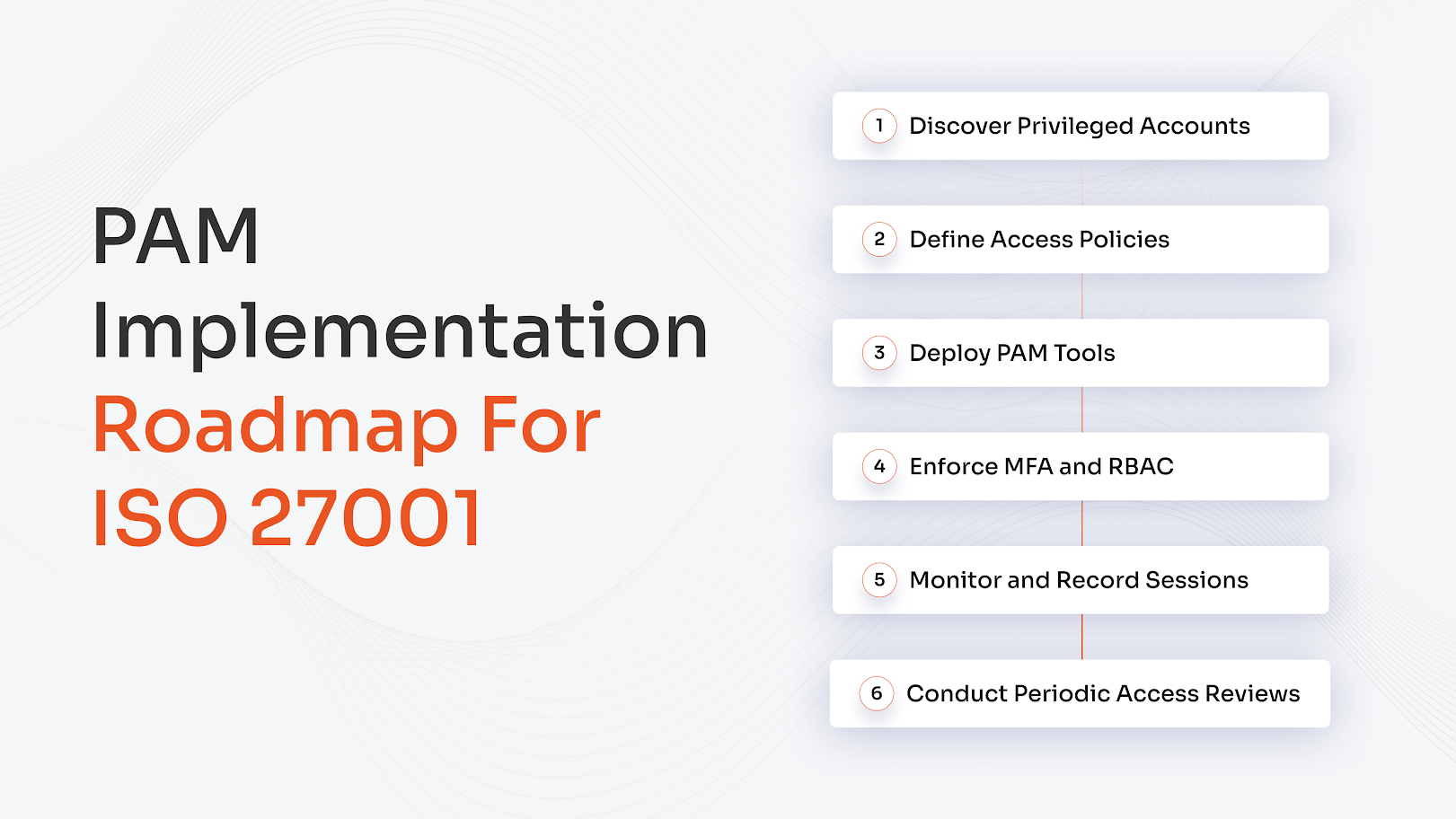
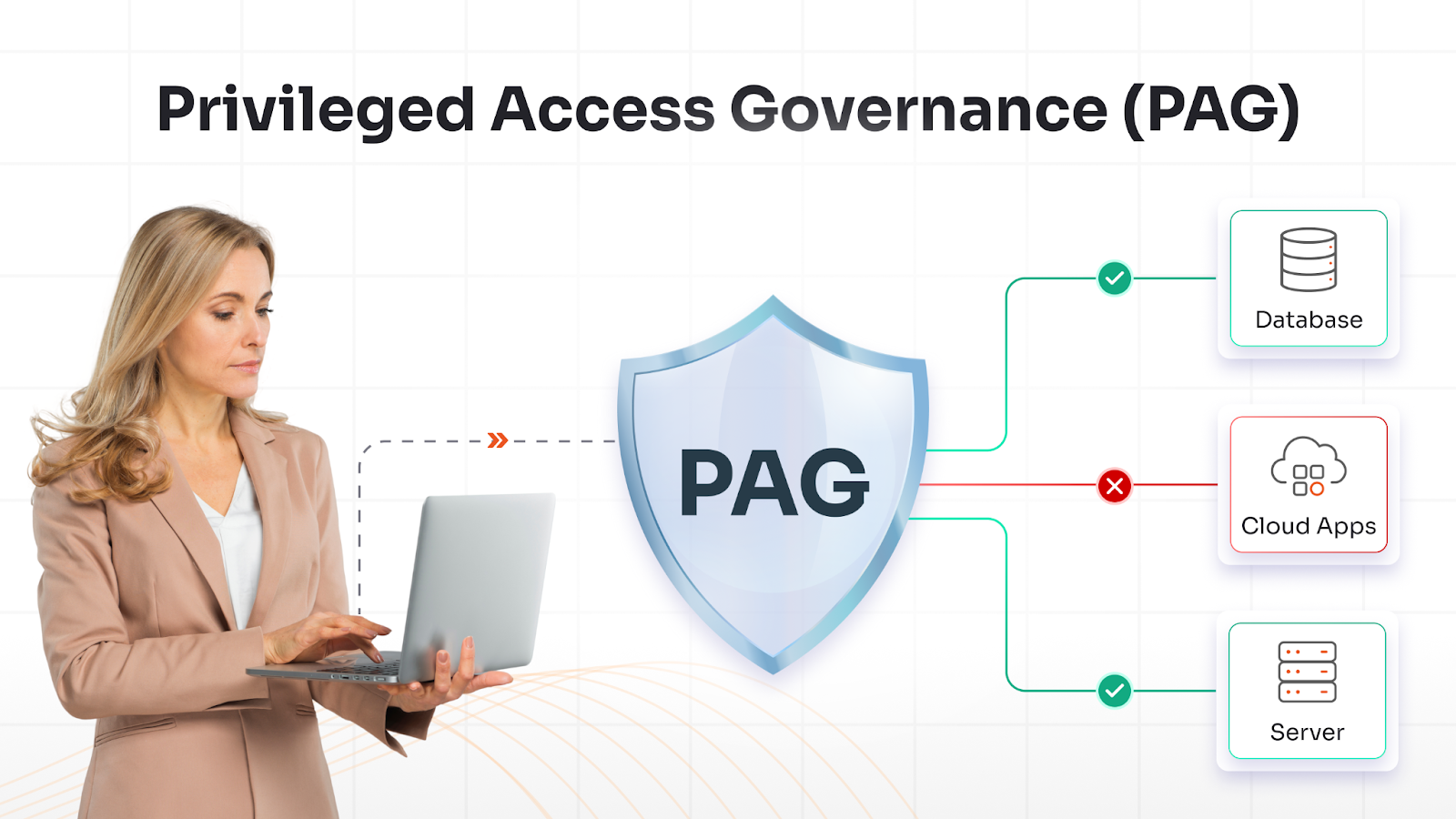
How miniOrange PAM Secures Vendor Privileged Access at Scale
As organizations expand their vendor ecosystem, managing privileged access manually becomes unsustainable. miniOrange Privileged Access Management (PAM) provides a centralized and scalable approach to securing vendor privileged access by replacing broad, always-on connectivity with controlled, auditable access workflows.
Instead of granting vendors unrestricted VPN access, miniOrange PAM enforces identity-based access to specific systems and resources. Vendors receive access only after authentication, authorization, and policy validation, significantly reducing the attack surface associated with third-party remote access.
Traditional Remote Access vs PAM-Based Access
Traditional remote access models rely on static credentials, shared accounts, and persistent network access, making it difficult to track activity or revoke permissions promptly. In contrast, miniOrange PAM enables Just-in-Time, time-bound privileged sessions that automatically expire once the task is completed.
Each vendor session is tied to an individual identity, improving accountability and eliminating shared credentials. Sensitive passwords are vaulted and never exposed to vendors, further strengthening security.
PAM and Zero Trust Alignment
miniOrange PAM aligns closely with Zero Trust principles by continuously verifying vendor identities and enforcing least privilege access. Vendors are granted only the minimum permissions required for approved tasks, and access decisions can be enforced based on context, such as role, system, and duration.
This approach ensures that no vendor is implicitly trusted and that access remains tightly controlled throughout the session lifecycle.
Audit, Visibility, and Compliance
miniOrange PAM provides full visibility into vendor activity through centralized logs and session recording. Security teams can monitor vendor actions in real time, investigate incidents faster, and maintain detailed audit trails for compliance requirements.
By combining granular access controls, session monitoring, and automated governance, miniOrange PAM enables you to secure vendor privileged access at scale while reducing operational complexity and helping prevent third-party data breaches.
Conclusion
Third-party remote access is now a fundamental requirement for maintaining operational agility, but it also represents one of the most significant security risks facing modern enterprises. Without structured controls, vendor connections can evolve into persistent entry points that attackers actively seek to exploit.
Adopting vendor remote access security best practices, including least privilege access, continuous monitoring, strong authentication, and automated governance, enables businesses to dramatically reduce their exposure.
As cyber threats grow more sophisticated, enterprises must treat securing vendor remote access as a strategic priority rather than a technical checkbox. A proactive approach not only helps prevent third-party data breaches but also builds a resilient security posture capable of supporting long-term growth and trusted vendor collaboration.
FAQs
What is vendor privileged access?
Vendor privileged access refers to elevated permissions granted to third-party vendors that allow them to manage systems, configure infrastructure, access administrative functions, or support critical applications. Because this access often includes high-impact capabilities, it must be tightly controlled to reduce security risk and prevent unauthorized activity.
Why is vendor remote access risky?
Vendor remote access is risky because external users often operate outside standard organizational security controls. Vendors may use unmanaged devices, shared credentials, or persistent access that remains active longer than necessary. Without proper governance, compromised vendor accounts can be exploited to bypass defenses and cause third-party data breaches.
How does PAM secure third-party access?
Privileged Access Management (PAM) secures third-party access by enforcing identity-based authentication, least privilege access, and time-bound permissions. PAM platforms provide controlled access to specific systems instead of broad network connectivity, while also monitoring and recording sessions for visibility, auditing, and faster incident response.
What is Just-in-Time vendor access?
Just-in-Time (JIT) vendor access provides temporary, task-specific permissions that automatically expire after a defined time or when work is completed. This eliminates standing privileges, reduces the attack surface, and significantly lowers the risk associated with long-term vendor access.

Leave a Comment