In October 2025, WordPress announced native support for the Model Context Protocol (MCP). This changed how AI agents like Claude, ChatGPT, Cursor, Gemini, and others interact with WordPress sites. With MCP, these agents can read data, make changes, and modify site behavior based on the instructions you give them.
This, however, introduces a real challenge. When an AI agent has a direct line into your WordPress site, how do you ensure it only performs the actions you authorize? The answer cannot be trust the agent.
What you need is a security protocol that defines exactly who can read data, who can update settings, and who can publish. It should expire automatically, let you remove access at any time, and keep a clear record of what the AI agent is allowed to do. That is what OAuth provides, and it is the authentication model that makes WordPress MCP integrations production-ready.
What is OAuth and What Does it Actually Do
OAuth is an open standard for authorization. It lets one application access another application’s resources on behalf of a user or service, without sharing the original login credentials. Instead of handing over a username and password, OAuth issues an access token.
OAuth does not just confirm identity. It governs access. Each token carries defined permissions, called scopes, plus a time limit. That way, the client can only perform the actions you approve, for the time window you allow.
Think of it as a hotel key card. The front desk does not give you a master key to the whole building. They program a card that opens only your room, and only until checkout. OAuth works the same way. Rather than giving an AI agent your WordPress credentials, WordPress issues a scoped, time-limited token. The token spells out what the agent can and cannot do. When it expires, access ends automatically.
In MCP terms, OAuth acts as the control layer for your API abilities. Agents like Claude, ChatGPT, and Cursor can only run the actions your site exposes when their token includes the right scopes. This keeps MCP access predictable, traceable, and ready for real deployment.
Note - For an introduction to MCP and WordPress API abilities, read our latest blog that covers the basics.
The Core Components of OAuth
Understanding OAuth becomes much clearer once you know the four roles involved in every exchange:
- Resource Owner: The user who owns the data. In the WordPress MCP context, this is the site owner or admin who decides what an AI agent is allowed to access.
- Client: The application requesting access. This is your MCP‑connected AI agent, whether ChatGPT, a custom AI agent, or a backend content pipeline.
- Authorization Server: The system that handles authentication and issues tokens. In the WordPress MCP model, your WordPress site takes on this role.
- Resource Server: The system that stores the protected data. For WordPress MCP, this is WordPress itself, holding posts, media, analytics, and settings that the AI agent wants to work with.
These four components interact through a defined sequence of steps. The client requests access, the resource owner approves it, the authorization server issues a token, and the resource server validates that token on every subsequent request. Nothing passes through the integration without following this sequence.
What an Access Token Actually Carries
An access token is a structured credential, typically a JSON Web Token (JWT), that carries verifiable claims about the authorization. Inside every token issued through OAuth are the answers to three questions:
- Who issued it? The authorization server signs the token with a private key. Any resource server holding the corresponding public key can verify the token is legitimate without making a network call.
- What is it allowed to do? The token carries a scope claim, which is a list of permissions the client was granted. A token with posts:read scope can read posts. It cannot write, delete, or touch anything outside that defined boundary.
- When does it expire? The token includes an expiry timestamp. Once that time passes, the token becomes invalid, and the client must request a new one. The process happens automatically, without any manual rotation.
This combination of issuer verification, scope enforcement, and automatic expiry is what separates OAuth from every simpler alternative.
Why OAuth Matters for WordPress MCP Specifically
As we have already discussed, WordPress MCP offers a wide set of API abilities. It can read and write posts, manage media, access user data, retrieve analytics, and change site settings. That range makes MCP genuinely useful for AI agents. It also increases the impact of any access mistake, because an agent can do more than fetch data.
However, many teams still rely on static API keys or application passwords. These options can stay active for too long, and they often carry broader privileges than an agent actually needs. If one leaks, it can keep working until someone rotates it.
OAuth matters for WordPress MCP because it enables:
- Permissions stay limited per task
- Access ends automatically on expiry
- Each agent gets its own access
- Actions map back to one client
This beats static keys and application passwords because it:
- Avoids long lived shared credentials
- Reduces accidental over permissioning
- Supports quick access removal
- Keeps integration changes isolated
How OAuth Secures WordPress MCP Adapter Connection with AI Agents
OAuth defines several authorization flows for different scenarios. For WordPress MCP, two of them cover essentially every real-world use case you will encounter.
Authorization Code Flow
This flow is designed for situations where a human user is actively granting access. A site owner connecting their WordPress account to an AI assistant, a developer tool acting on behalf of a logged-in user, or any scenario where a real person needs to review and consciously approve what the client is going to be allowed to do. Here is what happens at each step:
Step 1: The client initiates the request: The MCP client sends the user to a WordPress authorization page, listing exactly what permissions it is requesting, things like reading posts, accessing media, or viewing site analytics.
Step 2: The user reviews and decides: The user sees a consent screen with a clear breakdown of what access is being requested. They approve or deny. If they deny, the process stops. If they approve, WordPress generates a short-lived, single-use authorization code.
Step 3: The code is exchanged for tokens: The client takes that authorization code and makes a secure, server-side POST request to the token endpoint. WordPress validates the code and responds with an access token and a refresh token. The authorization code itself is now invalid and cannot be reused.
Step 4: The token authenticates every MCP request: Every request the AI client makes to your MCP server includes the access token in the Authorization header as a Bearer token. The server validates it on every call, checks that the scopes match the requested operation, and either processes or rejects the request.
Step 5: The refresh token handles silent renewal: When the access token approaches expiry, the client presents the refresh token to get a new access token automatically. The user never sees a re-authentication prompt unless the refresh token itself has expired or been revoked.
Client Credentials Flow
This flow is for automated or backend integrations where no human user is present. Scheduled content pipelines, AI agents running autonomously, backend services managing WordPress programmatically: these are all scenarios where the system itself is authenticating, not a user on its behalf.
The client presents its own client ID and secret directly to the token endpoint. There is no consent screen, no redirect, and no user interaction. The system has been pre-authorized by an administrator to operate within a fixed set of permissions, and it receives a token directly whenever it needs one.
The choice between these two flows comes down to a single question: is a real user actively approving access, or is an automated system authenticating on its own? That question must be answered before implementation begins.
Implementing OAuth for MCP Adapter with the miniOrange WordPress OAuth AI Agent Connector
Setting up OAuth correctly involves a lot of moving parts: issuing tokens, storing them securely, enforcing scope rules, handling expiry, managing refresh logic, and building revocation endpoints.
Doing all of that from scratch inside WordPress is a substantial project, and getting any part of it wrong creates security gaps that are genuinely difficult to catch.
The miniOrange WordPress OAuth AI Agent Connector handles all of it for you out of the box. You install the plugin, and your WordPress site is immediately capable of acting as a proper OAuth authorization server for any AI agent connecting through MCP. There is no custom code to write and no infrastructure to maintain. Everything from token issuance to access control is managed through a straightforward admin interface inside your WordPress dashboard.
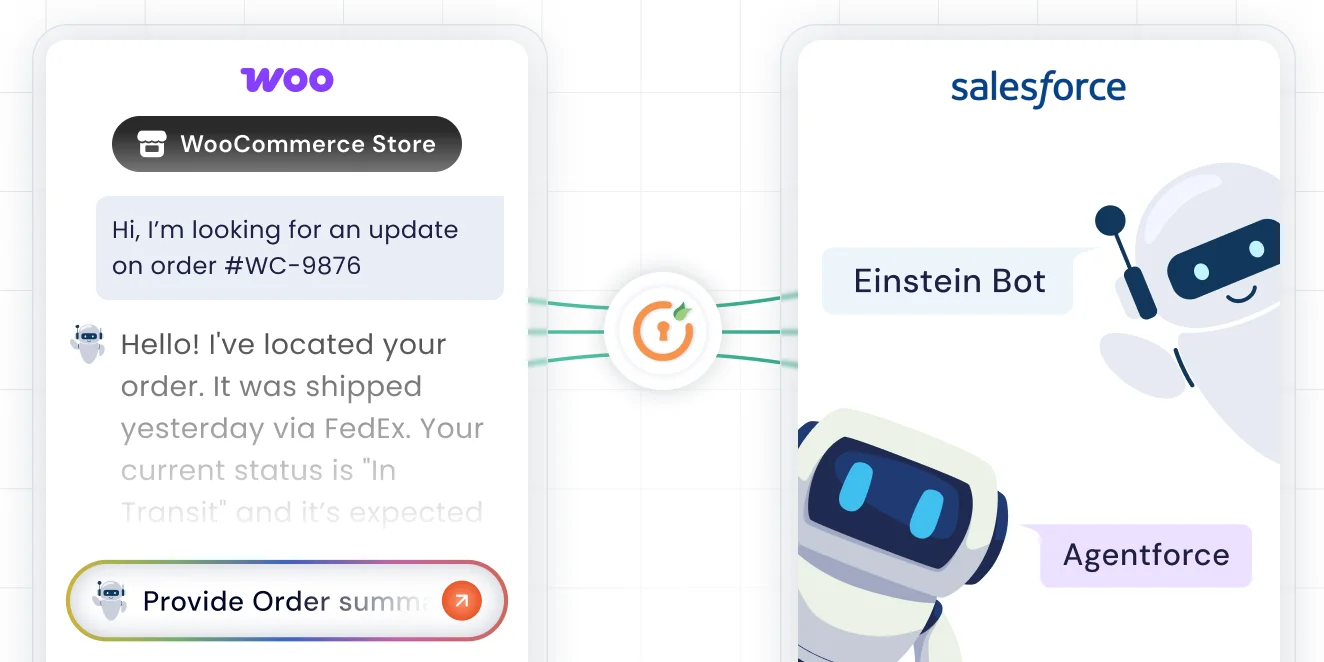
In practical terms, the plugin sits between your AI agents and your site's API abilities. Every time an agent makes a request through MCP, the plugin checks whether that agent holds a valid token and whether that token covers the specific action it is trying to perform. Approved requests go through. Everything else is blocked before it gets anywhere near your content or settings.
Benefits of Using AI Agent OAuth Connector for WordPress MCP Adapter
Here are some advantages of using our plugin to secure your WordPress MCP integrations:
- Native WordPress Capability Enforcement: The miniOrange OAuth AI Agent Connector integrates directly with WordPress’s permission system. Every OAuth scope you define maps to a WordPress capability check that runs on each request. For example, if an AI agent only has a scope, it cannot write or delete posts. WordPress itself blocks the action before any other logic runs.
- Short‑Lived Tokens That Limit Risk: Tokens issued through the plugin expire automatically after the time you configure. If a token is intercepted or leaked, it only works for a short window. This is a major improvement over static API keys, which remain valid until someone rotates them, often too late.
- Granular Scope‑Based Access Control: Scopes let you define exactly what each AI agent can do. A content analytics agent might only get, while a publishing agent gets. Neither can step outside its assigned scope. This precision is especially important when MCP exposes a wide range of API abilities across posts, media, users, and site settings.
- Per‑Client Identity and Easy Revocation: Each MCP client registered through the plugin has its own credentials, scopes, and token lifecycle. Adding a new integration does not affect existing ones. When you retire an agent, you simply remove its client registration, and its access ends immediately. There is no need for credential rotation, and other integrations continue without disruption.
- User Consent and Transparent Access: For user‑facing integrations, the OAuth consent screen shows users exactly what an AI agent can access before approval. Users can revoke that access anytime from their account settings. This transparency is now expected by users and, in many regions, is becoming a regulatory requirement.
- Audit‑Ready Logging: Every token includes client identity and scope details, so your logs automatically become a meaningful audit trail. If something unexpected happens, you can trace it to a specific agent, authorization grant, and time window. That makes compliance, incident investigation, and debugging far easier.
- Standards‑Based and MCP‑Compatible: OAuth is the same standard used by Google, Microsoft, GitHub, and other major platforms. MCP’s own security guidance is aligning with OAuth as the default model for MCP servers. Using it now ensures your WordPress MCP integration fits naturally into the ecosystem and avoids future migration headaches.
Conclusion
WordPress MCP and OAuth are just the beginning. We are actively building in this direction, working to make AI agent integrations on WordPress more secure, flexible, and significantly easier to set up and manage.
If you have questions about your current setup, want help choosing the right OAuth flow for your use case, or just want to explore what is possible with the miniOrange WordPress OAuth AI Agent Connector, our team is happy to help. Drop us an email at samlsupport@xecurify.com, and we will take it from there.


Leave a Comment