When someone registers for an online service or healthcare portal, logs into an eCommerce store, or uses a streaming platform, the first interaction usually involves identity and authentication. For businesses, this moment is critical because it connects security, customer experience, and trust.
Managing customer identities at scale has become increasingly complex. Organizations now handle millions of users across mobile apps, APIs, partner ecosystems, and global websites. At the same time, privacy regulations such as the General Data Protection Regulation (GDPR), Health Insurance Portability and Accountability Act (HIPAA), Saudi Arabian Monetary Authority (SAMA) and Payment Card Industry Data Security Standard (PCI DSS) require companies to protect personal data while maintaining seamless user experiences.
This is where Customer Identity and Access Management (CIAM) platforms play an important role. CIAM solutions help businesses manage customer authentication, authorization, and identity data across digital services while supporting modern login methods such as passwordless authentication and social login.
The demand for CIAM solutions continues to grow. According to market research firm Grand View Research, the global CIAM market is expected to exceed $26.72 billion by 2030 as organizations prioritize identity security and digital customer experience.
In this guide, we explore the top CIAM vendors of 2026 and compare their key features, strengths, and pricing to help organizations identify the best platform for their needs.
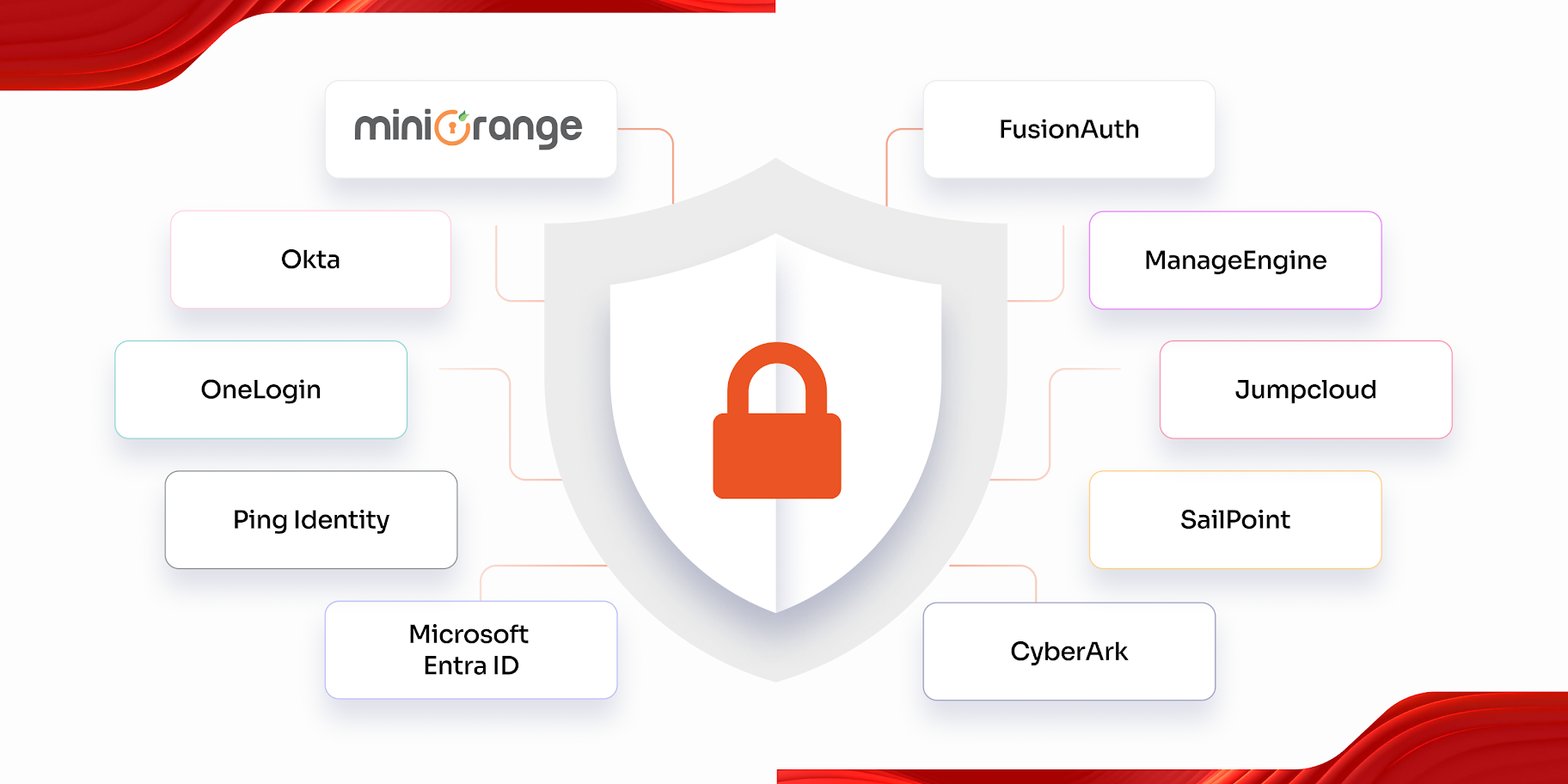
Leading CIAM Solution Vendors in 2026
Below are some of the most widely adopted CIAM solution vendors currently serving enterprises across industries.
1. miniOrange
miniOrange is a global identity and access management provider offering a flexible Customer Identity and Access Management (CIAM) platform for organizations managing large volumes of customer identities. The platform is designed to support both B2B and B2C use cases while maintaining a balance between strong security and smooth customer login experiences.
miniOrange CIAM includes core identity capabilities such as Single Sign-On (SSO) using SAML, OAuth, and OIDC protocols, along with support for social login and identity federation that allow customers to authenticate using trusted external identity providers. The platform also provides more than 15 Multi-Factor Authentication (MFA) methods, including OTP, push notifications, passkeys, and biometric verification.
Organizations can implement passwordless authentication and adaptive authentication policies that evaluate login behavior and risk signals to protect customer accounts from suspicious activity.
Beyond authentication, the platform supports customer provisioning and lifecycle workflows, enabling businesses to automate user onboarding, profile updates, and account management processes. miniOrange also offers multi-tenant architecture, which allows companies to scale customer identity services across multiple applications and user groups.
To support regulatory requirements, the platform includes built-in compliance capabilities aligned with privacy frameworks like the General Data Protection Regulation, making it suitable for organizations operating in regulated industries.
Key Features:
- User Authentication: Secure customer access with multiple authentication options including SSO, social login, passwordless authentication, and multi-factor authentication.
- User Registration: Simplify customer onboarding by allowing users to create accounts through social identity providers or external identity sources.
- SSO + Social Login: Allows users to access multiple applications using one identity, including social accounts like Google or Facebook.
- Multi-layered Security: Strengthens account protection with multiple MFA methods such as passkeys, biometrics, and risk-based authentication.
- Progressive Profiling System: Gradually collect customer information over time instead of requiring long registration forms upfront.
- Consent Management: Give users control over their data and privacy preferences by allowing them to manage and update consent settings, helping organizations build trust and maintain regulatory compliance.
- Self-Service Account Management: Allow customers to manage their own profiles, update personal information, reset passwords, and manage login preferences without administrative support.
- Custom Login and Registration Forms: Build fully branded or customized login and registration pages that provide a seamless user experience across applications.
- Threat Detection: Helps prevent unauthorized access and automated attacks using rate-limiting, adaptive MFA, and suspicious activity monitoring.
Pros:
- Supports more than 6000 integrations across popular enterprise platforms
- Flexible deployment options, including cloud, on-prem, and multi-tenant cloud
- Competitive pricing compared to many enterprise CIAM vendors
- 24/7 global support availability
Cons:
- AI-driven authentication features are still evolving
- Advanced enterprise orchestration may require configuration support
Pricing: miniOrange CIAM pricing starts at approximately $2 per user per month and scales based on enterprise requirements.
2. Okta / Auth0
Okta is one of the most recognized identity providers in the CIAM market. The company strengthened its position in customer identity management after acquiring Auth0, a developer-focused identity platform widely used for building secure authentication systems.
The acquisition brought together Auth0's developer-centric Customer Identity Cloud with Okta's enterprise-grade Workforce Identity Cloud. Together, these platforms provide a comprehensive identity and access management suite that supports both internal workforce authentication and external customer identity management.
While Okta traditionally focused on securing employee access to enterprise applications, Auth0 specializes in customizable authentication flows for customer-facing applications. The integrated platform now allows organizations to manage internal identities and customer identities within a unified identity ecosystem.
Auth0's flexible APIs and developer tools make it easier to build custom authentication experiences, while Okta's enterprise infrastructure provides strong security controls, compliance capabilities, and global scalability.
As a result, organizations can use the combined platform to implement secure login experiences, adaptive multi-factor authentication, and identity federation across web applications, mobile apps, and APIs.
Key Features:
- Universal login experience: Provides a customizable login interface that allows organizations to deliver consistent authentication across all customer applications.
- Adaptive multi-factor authentication: Adds extra verification steps based on login risk signals such as device, location, or unusual user behavior.
- Social login integrations: Allow customers to sign in using popular identity providers like Google, Facebook, or Apple instead of creating new credentials.
- Extensive developer APIs: Offers a wide range of APIs and SDKs that enable developers to integrate authentication and identity management into applications.
- Marketplace integrations: Supports connections with many third-party applications and services through Okta's extensive integration marketplace.
Pros:
- Developer-friendly architecture
- Strong ecosystem of integrations
- Reliable cloud infrastructure
Cons:
- Pricing can increase quickly with MAU-based billing
- Private cloud deployment options for data residency are typically available only in higher-tier enterprise plans
Pricing: Auth0 has plans based on B2C and B2B use cases. B2C starts at $35/month; B2B starts at $150/month.
3. LoginRadius
LoginRadius provides enterprise-grade CIAM solutions designed for organizations handling large volumes of customer identities. The platform focuses heavily on security, scalability, and regulatory compliance.
LoginRadius supports identity federation, adaptive authentication, and customer data management capabilities that allow organizations to manage millions of users securely.
The platform also offers multi-region infrastructure support, which allows companies to store identity data closer to users and comply with regional data protection regulations.
Organizations operating in regulated industries often choose LoginRadius because of its strong compliance features and enterprise-grade security architecture.
Key Features:
- Adaptive MFA authentication: Applies additional authentication steps based on risk signals such as device, location, or unusual login activity.
- Identity federation: Allows users to authenticate using identities from external providers or enterprise directories without creating new credentials.
- Customer data management: Helps organizations securely store, organize, and manage customer identity data across applications and services.
- SCIM provisioning for B2B use cases: Automates user provisioning and deprovisioning between systems using the SCIM standard for partner and enterprise identity management.
Pros:
- Strong focus on global scalability
- Multi-region deployment options
- Compliance support for GDPR and DPDPA
Cons:
- Platform complexity may be excessive for smaller companies
- Enterprise pricing structure
Pricing: Custom enterprise pricing.
4. Ping Identity
Ping Identity is a well-known identity security provider offering CIAM solutions designed for highly regulated industries such as finance and healthcare.
The platform focuses on secure authentication and advanced risk detection. Ping Identity offers features such as identity federation, adaptive authentication, and AI-driven threat detection.
Organizations that require strong security controls often choose Ping Identity because of its mature identity governance capabilities.
However, the platform may require more complex implementation compared to newer cloud-native CIAM solutions.
Key Features:
- Adaptive authentication with risk-based access policies: Evaluates factors like device, location, and user behavior to adjust authentication requirements based on the level of risk.
- No-code identity orchestration: PingOne DaVinci service provides no-code identity orchestration to design custom user journeys.
- Single Sign-On using SAML, OAuth, and OIDC standards: Allows users to access multiple applications with one login using widely adopted identity federation protocols.
- Multi-factor authentication for secure customer login: Adds additional verification methods beyond passwords to strengthen protection against unauthorized access.
- Identity federation and social login support: Enables users to authenticate using identities from external providers such as enterprise directories or social platforms.
- API security and identity orchestration capabilities: Protects application APIs and enables organizations to design customized authentication workflows across digital services.
- Hybrid and multi-cloud identity deployment options: Allow organizations to deploy identity services across cloud, on-premises, or hybrid environments, depending on infrastructure needs.
Pros:
- Strong security controls and risk-based authentication
- Suitable for highly regulated industries
- Flexible deployment across hybrid environments
- Mature enterprise identity platform
Cons:
- Implementation complexity for smaller teams
- Higher cost compared to some CIAM vendors
- Consumer user experience customization can require additional work
Pricing: Enterprise pricing typically starts around $35,000 per year, depending on deployment size and licensing.
5. ForgeRock
ForgeRock is an enterprise identity platform widely used by large organizations that need strong identity governance and access management capabilities. The platform focuses on delivering secure authentication and identity lifecycle management across complex digital ecosystems.
ForgeRock's CIAM solution is often chosen by organizations operating in highly regulated industries such as finance, government, and telecommunications. These sectors require strong identity governance and strict access policies for managing customer data.
The platform supports advanced authentication methods, including passwordless login, multi-factor authentication, and identity federation. ForgeRock also enables organizations to manage digital identities across multiple environments, including cloud infrastructure, on-prem systems, and hybrid deployments.
Another important capability is its identity orchestration engine, which allows organizations to create custom authentication workflows based on business requirements. This flexibility helps enterprises manage identity policies across multiple applications and customer platforms.
However, ForgeRock implementations often require experienced identity teams because of the platform's complexity and customization capabilities.
Key Features:
- Advanced identity governance and access control: Provides centralized control over user identities and permissions to ensure the right users access the right resources.
- Multi-factor authentication and passwordless login: Enhances account security by supporting multiple verification methods and passwordless authentication options.
- Identity federation and social login: Allows users to authenticate using external identity providers or social platforms without creating separate accounts.
- Hybrid and multi-cloud deployment support: Enables organizations to run identity services across on-premises systems, private clouds, and public cloud environments.
- Identity orchestration and workflow management: Allows businesses to design and automate authentication and identity management workflows across applications and services.
Pros:
- Strong governance capabilities for regulated industries
- Flexible deployment across hybrid environments
- Highly customizable authentication workflows
- Enterprise-grade identity security
Cons:
- Complex setup and implementation
- Requires experienced identity administrators
- Higher operational costs for smaller organizations
Pricing: ForgeRock uses enterprise subscription pricing depending on deployment scale and licensing.
6. AWS Cognito
Amazon Web Services offers CIAM functionality through Amazon Cognito, a cloud-based identity service designed for applications built on the AWS ecosystem. Cognito provides authentication and user management capabilities that allow developers to implement secure login systems for web and mobile applications.
The platform allows businesses to manage millions of user identities while maintaining a scalable authentication infrastructure. Since it is integrated directly into AWS, it is often chosen by organizations already hosting applications within the AWS cloud environment.
Amazon Cognito supports social login providers such as Google, Facebook, and Apple, along with enterprise identity federation. It also provides features such as adaptive authentication, multi-factor authentication, and user directory management.
One of Cognito's strengths is its scalability. Because it runs on AWS infrastructure, it can handle rapid growth in user traffic without requiring additional infrastructure management.
However, Cognito often requires developer involvement during implementation. Organizations that prefer no-code identity platforms may find the configuration process more technical compared to some dedicated CIAM providers.
Key Features:
- Managed customer identity directory: Provides a built-in user directory where applications can securely store and manage customer identities.
- Social login and identity federation: Allows users to authenticate using external identity providers such as Google, Facebook, or enterprise identity systems.
- Multi-factor authentication support: Adds additional verification steps like SMS or authenticator apps to strengthen login security.
- AWS ecosystem integrations: Connects seamlessly with other AWS services to support authentication across cloud applications and APIs.
- Scalable cloud-based identity infrastructure: Uses AWS cloud infrastructure to automatically scale authentication services as the number of users grows.
Pros:
- Seamless integration with AWS services
- Highly scalable architecture
- Cost-effective for AWS-native applications
- Reliable global infrastructure
Cons:
- Requires developer expertise for configuration
- User experience customization can require additional development
Pricing: Amazon Cognito offers a free tier for smaller applications with usage-based pricing for larger deployments.
7. Frontegg
Frontegg provides CIAM capabilities designed primarily for SaaS companies and developer platforms. The platform focuses on simplifying customer authentication while also providing tenant management and user onboarding capabilities for modern SaaS applications.
Frontegg is particularly popular among software companies that need to manage customer identities within multi-tenant environments. Instead of building authentication infrastructure from scratch, SaaS teams can use Frontegg to implement secure login systems quickly.
The platform includes features such as passwordless authentication, social login, and role-based access control. It also provides tools for managing user permissions and account provisioning across SaaS products.
Another advantage of Frontegg is its compliance-ready architecture. The platform supports security frameworks commonly required by SaaS companies serving regulated industries, including healthcare and finance.
While Frontegg offers strong functionality for SaaS identity management, it is still a relatively newer player in the CIAM market compared to long-established identity vendors.
Key Features:
- SaaS-focused CIAM platform: Designed specifically to manage customer authentication and identity services for SaaS applications.
- Multi-tenant identity management: Allows SaaS platforms to manage identities for multiple organizations or customers within a single system.
- Role-based access control: Restricts access to application features and resources based on predefined user roles and permissions.
- Passwordless authentication: Enables users to log in without passwords using methods such as magic links, passkeys, or one-time codes.
- Compliance-ready architecture: Supports security and privacy requirements needed to meet regulatory standards for customer identity management.
Pros:
- Built specifically for SaaS platforms
- Simplifies identity infrastructure for developers
- Strong tenant management capabilities
- Supports compliance-focused deployments
Cons:
- Smaller ecosystem compared to major CIAM vendors
- Limited enterprise brand recognition
- Feature maturity is still evolving
Pricing: Frontegg pricing depends on the selected features, deployment scale, and whether the platform is used for B2B or B2C identity management.
8. Descope
Descope is a modern CIAM platform that focuses heavily on passwordless authentication and simplified identity implementation. The platform allows organizations to create secure authentication experiences without requiring extensive coding.
Descope is particularly attractive for companies that want to replace traditional password-based login systems with more secure authentication methods. The platform supports passkeys, magic links, and other passwordless authentication flows designed to improve both security and user experience.
Another notable capability is Descope's no-code workflow builder. This tool allows developers and product teams to design authentication flows visually instead of building them entirely from code.
Descope also integrates with modern application environments, APIs, and microservices architectures, making it suitable for digital-first companies.
However, because the platform is relatively new compared to older CIAM providers, some organizations may evaluate its long-term enterprise scalability before adoption.
Key Features:
- Passwordless authentication methods: Allow users to sign in without passwords using secure alternatives such as passkeys, one-time codes, or magic links.
- Passkey and magic link login options: Enable quick authentication through device-based passkeys or secure login links sent to a user's email.
- No-code authentication flow builder: Let teams create and customize login workflows without writing code using visual configuration tools.
- Identity orchestration capabilities: Allow organizations to design and manage authentication processes across multiple identity providers and systems.
- API-first architecture: Provides developer-friendly APIs that make it easy to integrate authentication and identity services into applications.
Pros:
- Strong passwordless authentication features
- No code identity flows
- Modern user experience
Cons:
- Smaller market presence than established vendors
- Enterprise scalability is still developing
- Advanced identity governance capabilities are still evolving compared to traditional enterprise IAM platforms
Pricing: Descope offers freemium options along with enterprise plans for larger organizations.
9. Microsoft Entra External ID
Microsoft offers CIAM functionality through Microsoft Entra External ID, which extends Microsoft's identity platform to support customer and partner authentication.
Organizations that already rely on Microsoft cloud services often choose Entra External ID because of its seamless integration with the broader Microsoft ecosystem.
The platform supports features such as Single Sign-On, multi-factor authentication, and identity federation. It allows businesses to create secure login experiences across customer applications while leveraging Microsoft's global infrastructure.
Microsoft Entra also supports customizable authentication policies and identity governance features. These capabilities allow organizations to control how users authenticate and access services.
However, the platform works best for organizations already invested in the Microsoft ecosystem. Companies using other cloud providers may find integration slightly more complex.
Key Features:
- Customer identity authentication: Allows businesses to securely authenticate customers and manage their access to applications and digital services.
- Integration with Azure and Microsoft services: Works seamlessly with Microsoft cloud services and Azure infrastructure to support identity management across applications.
- Multi-factor authentication: Enhances account security by requiring additional verification methods beyond passwords during login.
- Identity federation and SSO: Enables users to access multiple applications with a single login using federated identity protocols.
- Global cloud identity infrastructure: Uses Microsoft's worldwide cloud network to deliver scalable and reliable identity services across regions.
Pros:
- Strong integration with the Microsoft cloud ecosystem
- Enterprise-grade security controls
- Global infrastructure scalability
- Reliable identity governance features
Cons:
- Works best within Microsoft environments
- Customization may require Azure expertise
- Pricing tied to Microsoft cloud consumption
Pricing: Microsoft Entra External ID uses consumption-based pricing through Azure.
10. FusionAuth
FusionAuth is a developer-focused CIAM platform designed for organizations that want a flexible authentication infrastructure with strong customization capabilities.
FusionAuth provides identity management tools that allow developers to implement authentication systems tailored to their applications. The platform supports both cloud-hosted and self-hosted deployment models, which gives organizations greater control over their identity infrastructure.
The platform supports modern authentication features such as Single Sign-On, multi-factor authentication, passwordless login, and social identity integrations.
FusionAuth is particularly attractive for organizations that prefer open architecture and flexible APIs. Developers can build custom authentication flows and integrate identity services into complex application environments.
However, compared to larger enterprise identity vendors, FusionAuth has a smaller ecosystem and may require more technical resources during implementation.
Key Features:
- Flexible CIAM platform for developers: Provides customizable authentication tools that allow developers to tailor identity workflows to their application needs.
- Social login and identity federation: Allows users to authenticate using external identity providers or social platforms without creating new credentials.
- Multi-factor authentication: Adds additional verification layers such as OTP or authenticator apps to improve account security.
- Self-hosted and cloud deployment options: Gives organizations the flexibility to run the identity platform either on their own infrastructure or in the cloud.
- Extensive API support: Offers comprehensive APIs that enable developers to integrate identity and authentication features into applications easily.
Pros:
- Flexible deployment options
- Strong developer control over authentication flows
- Open architecture identity platform
- Active developer community
Cons:
- Smaller integration ecosystem
- Requires technical expertise for implementation
- 24/7 engineering-led support is available only with paid tiers
Pricing: FusionAuth offers a free community edition along with enterprise plans starting from $37 per month depending on monthly active users.
CIAM Vendors Quick Comparison
| Vendor | Security & Compliance | UX Features | Scalability | Integrations | Pricing |
|---|---|---|---|---|---|
| miniOrange | GDPR, HIPAA, SOC 2 support | Passkeys, social login, passwordless | High | 6000+ integrations | $2/user |
| Okta/Auth0 | SOC 2, ISO 27001, GDPR | Universal login, social login | High | Large marketplace | B2C: $35/month B2B: $150/month |
| LoginRadius | GDPR, SOC 2, ISO 27001 | Adaptive authentication, social login | Enterprise scale | API-driven integrations | Custom |
| Ping Identity | GDPR, SOC 2, FedRAMP | Passwordless login, federated authentication | High | Enterprise federation | ~$35K/year |
| ForgeRock | GDPR, SOC 2, ISO 27001 | Custom authentication flows | Enterprise scale | Federation protocols | Subscription |
| AWS Cognito | SOC 2, ISO 27001, PCI DSS | Hosted UI, social login | Elastic cloud scale | AWS ecosystem | Usage based |
| Frontegg | SOC 2, HIPAA support | Passwordless login, SaaS onboarding | SaaS scale | SaaS integrations | Feature based |
| Descope | SOC 2, GDPR support | Passkeys, passwordless login | Growing scale | API-first integrations | Freemium |
| Microsoft Entra | SOC 2, ISO 27001, GDPR | SSO, passwordless authentication | Global scale | Azure ecosystem | Usage based |
| FusionAuth | GDPR support | Custom login flows | Moderate | Developer APIs | Tiered |
How to Choose a CIAM Vendor?
Choosing the right CIAM vendor is not just about comparing feature lists. The platform you select will directly impact how customers register, authenticate, and interact with your digital services. A well-chosen CIAM solution should balance security, scalability, and user experience while integrating smoothly with your existing technology stack.
Here are a few important factors organizations should evaluate before selecting a CIAM platform.
1. Assess Your Identity Requirements
Start by identifying the type of users your organization manages and how they access your services. Some businesses manage millions of consumer identities, while others focus on partner or B2B access. Consider authentication requirements such as social login, passwordless authentication, or adaptive MFA. Understanding these needs helps narrow down the CIAM platforms that best match your use cases.
2. Evaluate Integration Capabilities
A CIAM platform should integrate easily with your existing applications, APIs, and Identity Providers (IdPs). Look for vendors that support standard protocols such as SAML, OAuth, and OIDC, along with prebuilt integrations for common platforms like CRM systems, CMS platforms, and mobile applications.
3. Test Scalability
Customer identity systems must handle large spikes in user traffic, especially for consumer platforms. Before selecting a vendor, organizations should evaluate how the platform performs under high user volumes. Scalability tests or proof-of-concept deployments can help ensure the platform supports future growth.
4. Verify Compliance and Security
Organizations operating in regulated industries must ensure the CIAM solution supports relevant compliance frameworks. Features such as consent management, audit logs, and data protection controls help meet regulations like GDPR, HIPAA, and other privacy standards.
5. Calculate Total Cost of Ownership
Pricing should be evaluated beyond the base subscription cost. Organizations should consider implementation time, integration effort, infrastructure requirements, and ongoing operational costs. Understanding the full cost of ownership helps avoid unexpected expenses later.
6. Evaluate Vendor Support and Documentation
Identity platforms often require configuration and ongoing maintenance. Vendors that provide strong documentation, onboarding assistance, and responsive technical support can significantly reduce deployment challenges and help teams resolve issues faster.
Why Choose miniOrange for CIAM?
miniOrange stands out among CIAM vendors because it combines strong security controls with flexible deployment options and competitive pricing.
Organizations benefit from features such as adaptive authentication, passwordless login, customer lifecycle management workflows, and extensive integration support.
The platform supports both B2B and B2C identity use cases, allowing companies to manage customer, partner, and workforce identities from a unified identity platform.
Its hybrid deployment capabilities also make it attractive for organizations operating in regulated industries or regions with strict data residency requirements.
Conclusion
As digital services continue to expand, identity management has become one of the most critical components of application security and user experience.
Choosing the right CIAM vendor can help organizations improve customer onboarding, protect sensitive data, and deliver seamless authentication experiences across digital platforms.
While several CIAM providers offer strong capabilities, platforms such as miniOrange stand out for their flexibility, integration ecosystem, and enterprise readiness.
Organizations evaluating CIAM platforms should carefully assess their security requirements, scalability needs, and integration environments before making a final decision.
FAQs
What are the top CIAM vendors for enterprises?
Some of the most widely used CIAM vendors for enterprise environments include miniOrange, Okta/Auth0, Ping Identity, LoginRadius, and ForgeRock. These platforms offer advanced identity security features such as multi-factor authentication, identity federation, adaptive authentication, and scalable infrastructure to manage millions of customer identities.
Is miniOrange HIPAA-compliant?
Yes. miniOrange supports HIPAA-compliant identity management through features such as secure authentication, audit logging, adaptive MFA, and access control policies. These capabilities help organizations protect sensitive user data and meet regulatory security requirements.
What is the difference between CIAM and IAM?
CIAM (Customer Identity and Access Management) focuses on managing external customer identities across websites, mobile apps, and digital services. IAM (Identity and Access Management) is typically used for internal workforce identity management, controlling employee access to enterprise applications and systems.
Which CIAM platform is best for scalability?
Platforms such as miniOrange, Okta/Auth0, LoginRadius, and AWS Cognito are known for supporting large-scale customer identity deployments. These platforms provide cloud infrastructure and multi-tenant architecture that allow organizations to manage millions of users while maintaining secure authentication experiences.
What pricing models do CIAM vendors typically use?
CIAM vendors generally use several pricing models depending on deployment type and scale. Common models include per-user pricing, monthly active user (MAU) pricing, usage-based pricing, and enterprise subscription plans. Organizations should evaluate the total cost of ownership, including integration and operational costs, when selecting a CIAM vendor.
How do you choose a CIAM vendor for fast user onboarding?
To enable fast user onboarding, organizations should select a CIAM platform that supports social login, passwordless authentication, progressive profiling, and automated identity workflows. These features simplify registration processes and reduce friction during customer sign-up.

Leave a Comment