Every major data breach has one thing in common: attackers don't break in; they log in. And when they do, they almost always use privileged credentials. That's exactly why ISO 27001 Privileged Access Management (PAM) exists.
As one of the most critical pillars of ISO 27001 compliance, PAM ensures that the accounts with the most power in your environment, admins, root users, and service accounts, are tightly controlled, fully traceable, and actively monitored. This guide breaks down what ISO 27001 requires for PAM, which Annex A controls apply, and how to implement them without the jargon.
What Is Privileged Access Management in ISO 27001?
What Counts as a "Privileged Account"?
Not all user accounts are equal. A standard employee account allows users to read email and edit documents. A privileged account does far more: it can install software, access entire databases, modify security settings, or control other user accounts.
Common privileged accounts include:
- Administrator/root accounts: full system control on servers or workstations
- Domain admin accounts: control over an entire Active Directory environment
- Service accounts: used by applications to communicate with each other in the background
- Emergency/break-glass accounts: high-access accounts reserved for crisis scenarios
Why Attackers and Auditors Both Care About Privileged Accounts
They come from completely different directions. One wants to exploit your system, the other wants to verify if it is protected. But both keep an eye on the same thing: who has privileged access, and what they are doing with it.
The Attacker's Perspective
A compromised standard account gives an attacker access to one person's files and a few business apps. A compromised admin or root account gives them the keys to the kingdom. They can disable antivirus tools, access every database in the environment, create backdoor accounts, and move laterally across systems, all while appearing to be legitimate activity.
This technique, called privilege escalation, is a core part of almost every major ransomware and data breach playbook. Attackers rarely start with an admin account. They typically begin with a low-level phishing attack, compromise a regular user, and quietly work their way up to admin-level credentials over days or weeks. By the time the damage is done, the trail is cold.
The Auditor's Perspective
An ISO 27001 auditor is not trying to hack you, but they are stress-testing your controls with a specific set of questions:
- Is there a formal, documented process for approving privileged access?
- Can every admin action be traced back to a unique, verified individual?
- Are privileged sessions recorded and protected from tampering?
- When was the last access review conducted, and what happened to accounts that no longer needed elevated rights?
If your answers rely on memory or spreadsheets, that is a gap. ISO 27001 PAM requirements under Annex A 8.2 and 8.15 exist precisely because informal control of privileged accounts is one of the most common and most serious findings in information security audits.
The auditor's concern extends to prevention of insider threats, too. An admin who accidentally misconfigures a firewall, or a disgruntled employee who exports a customer database, represents the same control failure as an external breach in the eyes of an ISO 27001 assessment.
ISO 27001 Controls That Govern Privileged Access
Annex A mandates formal approval, least privilege, identity traceability, and monitoring of all privileged activities, creating a clear, auditable framework around your most sensitive accounts.
Annex A 8.2 – Privileged Access Rights
This is the most directly relevant control for ISO 27001 PAM requirements. Annex A 8.2 requires that privileged access rights be restricted, formally approved, and regularly reviewed. Organizations must maintain a documented list of who holds elevated permissions, ensure those permissions are granted only for legitimate business need, and revoke them the moment that need no longer exists.
Restrict and Approve Admin Access
Every privileged account must be formally authorized, with a documented request, an approver on record, and a defined scope of access. Ad hoc or informally granted admin rights are a direct non-conformity.
Time-bound Privileged Permissions
Standing privileges, where admins hold elevated access permanently, are one of the biggest risks in any environment. ISO 27001 encourages time-bound access where elevated permissions are granted for a specific task or window and automatically expire, directly limiting the damage window if credentials are ever compromised.
Formal Authorization Workflow
Every privileged access request should follow a repeatable, documented process: request raised, business justification provided, manager or security team approves, access provisioned, access logged. This workflow gives auditors confidence that privileged access is governed, not guessed.
Annex A 5.15–5.18 – Access Control and Identity
These four controls form the identity backbone of ISO 27001 access control requirements, ensuring that privileged access is tied to verified individuals, protected by strong authentication, and scoped to what each role genuinely requires.
Unique Identities (Annex A 5.16)
Every user, especially every admin, must have a unique identity so that all actions can be attributed to a specific person. If three engineers share one root account, there is no way to know who made a change at 2 am. ISO 27001 identity management requires that traceability be possible.
Authentication Security (Annex A 5.17)
Passwords alone are not sufficient for privileged accounts. Annex A 5.17 requires authentication mechanisms strong enough to match the sensitivity of what is being accessed, meaning enforced complexity, secure credential management, and the elimination of default or shared passwords.
Access Rights Based on Least Privilege (Annex A 5.15 and 5.18)
Annex A 5.15 governs how access policies are defined, while 5.18 covers the full lifecycle: provisioning, adjustment, and revocation. Together, they ensure that privilege creep, where users accumulate access over time, is actively prevented and periodically corrected.
Annex A 8.15 – Logging and Monitoring
Even the best access controls mean little if no one is watching. Annex A 8.15 requires that all privileged activity be recorded, protected from tampering, and reviewed regularly, giving organizations both a detection capability and a complete audit trail.
Record all Admin Activities
Every action taken under a privileged account, including logins, configuration changes, data access, and permission modifications, must be captured in logs. Real-time logging is the foundation of detecting anomalous behavior before it becomes a breach.
Protect Logs from Tampering
A log that can be edited is a log that cannot be trusted. ISO 27001 requires audit logs stored securely with write-once or append-only configurations where possible, with access to log data itself restricted. If an admin can delete their own activity trail, the control is worthless.
Periodic Log Review
Generating logs is not enough. Someone has to review them. Annex A 8.15 requires scheduled reviews of privileged activity logs to identify unusual patterns, policy violations, or unauthorized access attempts, and those reviews must be documented.
Core PAM Principles Required for ISO 27001 Compliance
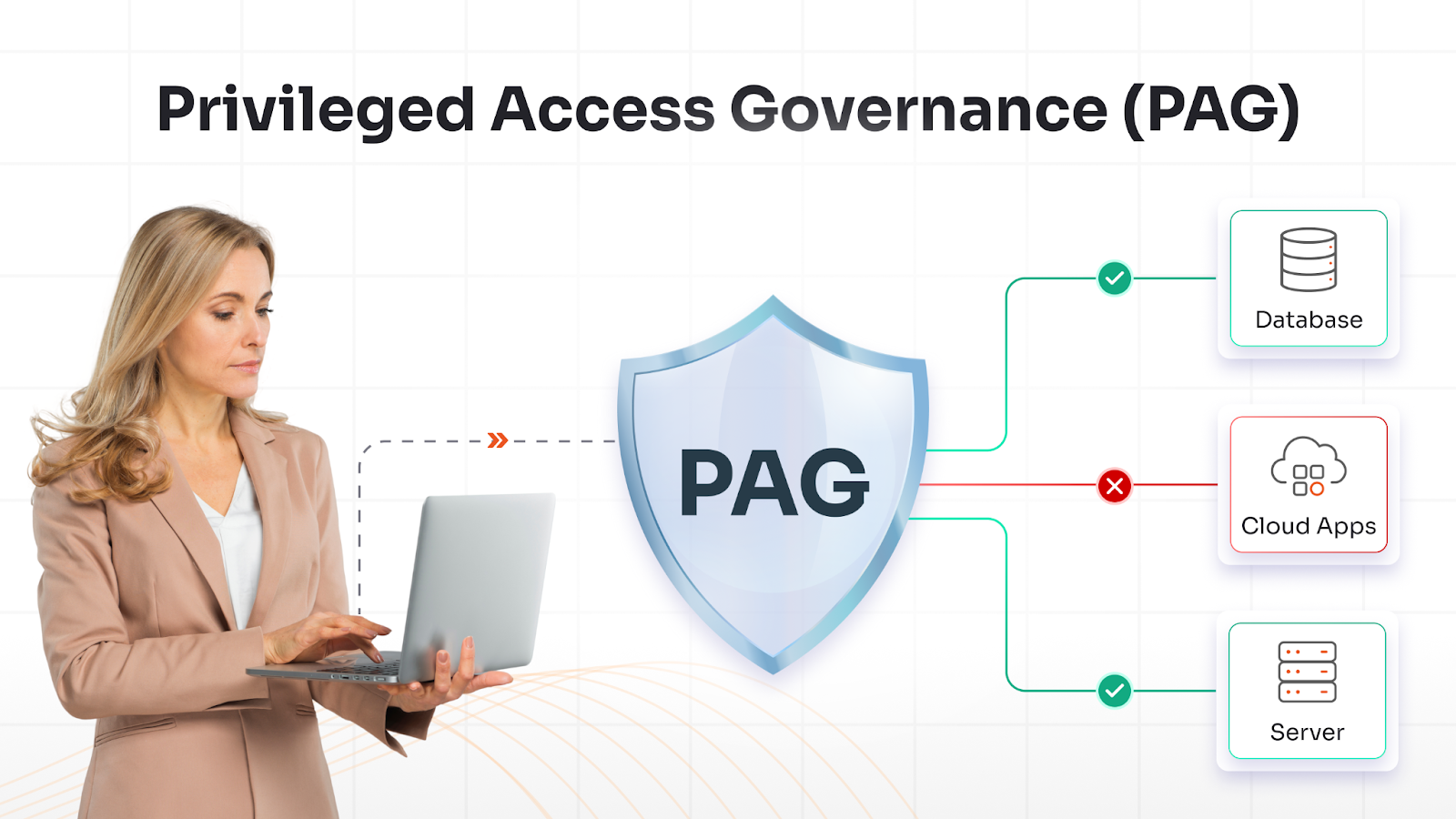
ISO 27001 doesn't prescribe a specific PAM tool, but it enforces a clear set of operational principles that together define what a compliant PAM program looks like in practice.
Least Privilege Principle
Every user, system, and process should have access to only what it needs and nothing beyond that. In practice, this means regularly auditing who has what, stripping back permissions that exceed role requirements, and never granting broad access as a convenience. It is a foundational ISO 27001 access control requirement that runs across multiple Annex A controls.
Segregation of Duties (SoD)
No single person should have end-to-end control over a sensitive process. The person who approves a privileged access request should not be the same person who provisions it. SoD reduces the risk of both fraud and insider misuse, and it is a key expectation in any ISO 27001 PAM audit.
Multi-Factor Authentication (MFA)
MFA is non-negotiable for privileged accounts. Even if a password is stolen, phished, or brute-forced, MFA ensures that a credential alone is not enough to gain access. Organizations should enforce MFA at every privileged login, not just at initial setup, and maintain proof of enforcement for auditors.
Privileged Session Monitoring
Access monitoring and logging of privileged sessions go beyond capturing login events. It means recording what was done during the session: commands run, files accessed, and configurations changed. This gives security teams real-time visibility to detect misuse and gives auditors the evidence trail they need to verify that privileged activity stayed within approved boundaries.
Just-in-Time (JIT) Access
JIT access eliminates standing privileges entirely. Users request elevated access for a specific task, receive it for a defined window, and have it automatically revoked when that window closes. A privileged account that only exists for 30 minutes is far harder to exploit than one that is always active.
Privileged Account Inventory
You cannot protect what you do not know exists. Maintaining a complete, up-to-date inventory of all privileged accounts, including service accounts and emergency accounts that are frequently overlooked, is a baseline ISO 27001 PAM requirement. The inventory should capture account owner, access scope, approval date, and last review date, and it should be treated as a living document.
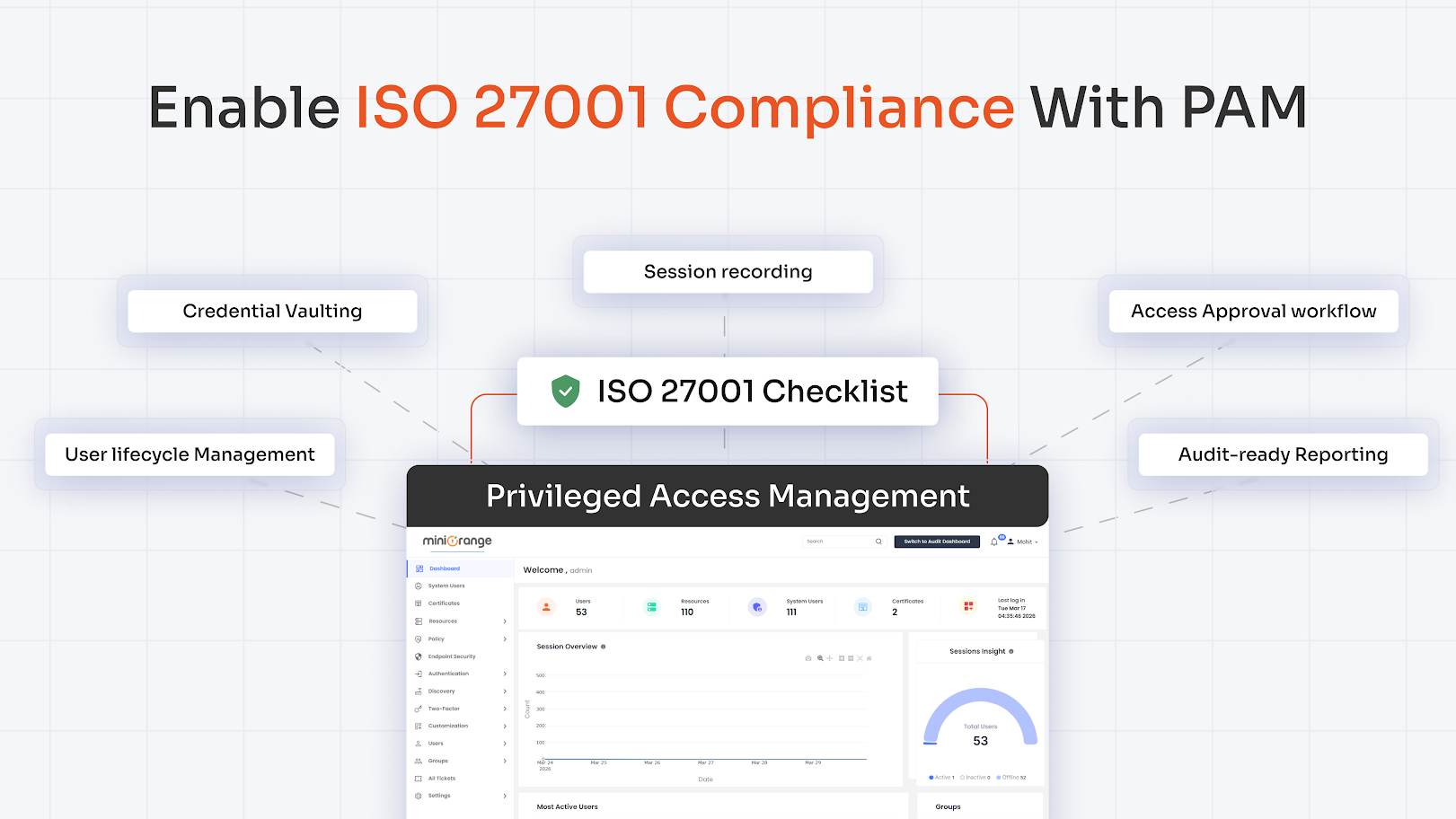
How PAM Enables ISO 27001 Compliance
Understanding what ISO 27001 requires is one thing. Operationalizing those requirements across a real environment is another. A dedicated PAM platform acts as a compliance engine that generates the evidence, workflows, and controls auditors expect to see.
Credential Vaulting centralizes all privileged passwords in an encrypted vault, ensuring credentials are never exposed in plaintext, rotated automatically on schedule, and accessed only through an approved, logged request. This directly supports Annex A 8.2 by controlling access at the credential level, not just the policy level.
Session Recording captures full privileged sessions, including keystrokes, commands, and screen activity, creating a tamper-proof audit trail for every admin interaction. If an incident occurs, security teams can replay the session exactly, and auditors get the evidence they need to verify Annex A 8.15 compliance.
Approval Workflows replace informal access grants with structured, timestamped processes: a request is raised, routed to an approver, justification captured, and access provisioned only after sign-off. This creates the formal authorization trail Annex A 8.2 requires.
Automated Provisioning and Deprovisioning triggered by HR system signals or predefined expiry rules ensure that privileged access is revoked immediately when someone changes roles or leaves, keeping the account inventory clean and Annex A 5.18 requirements consistently met.
Audit-ready Reporting generates pre-built compliance outputs covering account inventory, approval records, session activity, MFA status, and access review outcomes, turning weeks of manual audit preparation into hours.
PAM Implementation Roadmap for ISO 27001
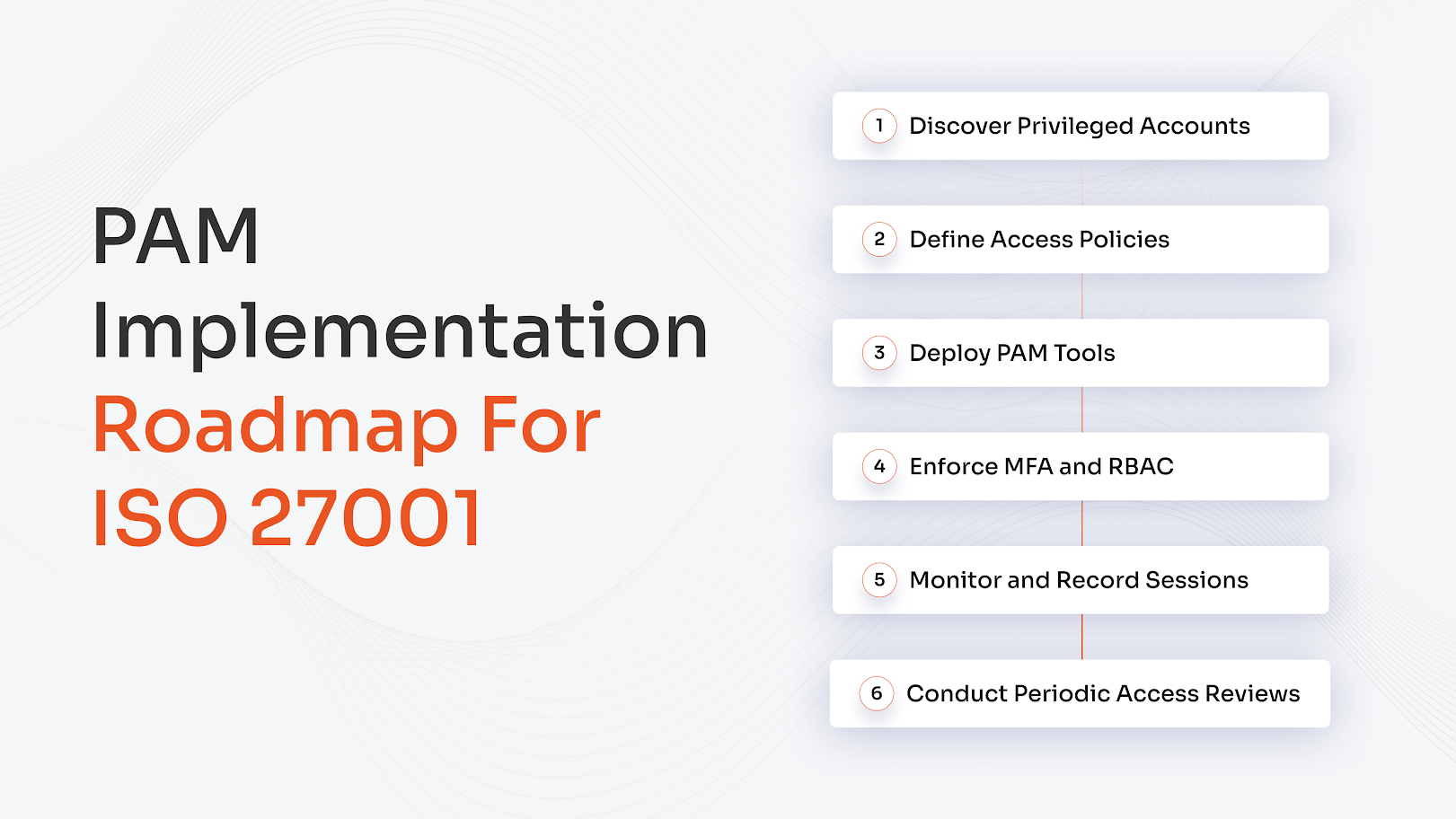
Step 1: Discover Privileged Accounts
Run a comprehensive discovery exercise across on-premises systems, cloud infrastructure, SaaS platforms, and applications to surface every account with elevated rights, including service and shared admin accounts that often go undetected. This becomes your privileged account inventory.
Step 2: Define Access Policies
Define who should have privileged access, under what conditions, and for how long. Policies should reflect the least privilege principle and include rules around time-bound permissions, approval requirements, and acceptable use. These are among the first documents an ISO 27001 auditor will request.
Step 3: Deploy PAM Tools
Deploy a PAM platform covering credential vaulting, session monitoring, and access request workflows, prioritized by risk. Integration with Active Directory, LDAP, or cloud IAM ensures PAM controls sit within your broader ISO 27001 identity and access management framework rather than operating in isolation.
Step 4: Enforce MFA and RBAC
Enforce MFA across all privileged accounts without exception. Implement role-based access control (RBAC) so that elevated permissions are tied to defined roles rather than individuals, making access easier to manage, review, and revoke in line with Annex A 5.15 through 5.18.
Step 5: Monitor and Record Sessions
Activate session recording and real-time monitoring across all privileged access points. Configure alerts for anomalous behavior such as off-hours access or bulk data downloads. Store logs in a tamper-proof location and retain them per your logging policy to fully operationalize Annex A 8.15.
Step 6: Conduct Periodic Access Reviews
Schedule formal access reviews at a defined frequency, typically quarterly for high-privilege accounts, and document the outcome of each review. These records demonstrate that your organization treats privileged access as an ongoing governance responsibility, not a one-time task.
Evidence Required for ISO 27001 PAM Audit
ISO 27001 is a documentation-heavy standard. Auditors need proof that controls are not just deployed but actively maintained. Here is what to have ready:
| Evidence Item | What Auditors Look For |
|---|---|
| Privileged access policy | Current, version-controlled, formally approved by management |
| Privileged account inventory | All accounts, including service and shared accounts, with owner, scope, and review date |
| Approval records | Documented requests, approver sign-off, justification, and access scope for every privileged account |
| Access review reports | Records of reviews conducted, decisions made, and changes actioned |
| PAM logs and session records | Tamper-proof logs are retained for the required period and subject to regular review |
| MFA enforcement proof | Policy configurations, enrollment reports, or logs showing non-MFA logins are blocked |
Choosing the Right PAM Solution for ISO 27001
Not all PAM tools are built with compliance in mind. The right platform should actively support audit readiness across every relevant Annex A control, not just vault credentials. Look for:
- Credential vaulting with automatic rotation so privileged passwords are never static or exposed
- Session recording and playback in a tamper-proof format aligned to Annex A 8.15
- Approval and workflow automation that creates documented, auditable access trails per Annex A 8.2
- MFA enforcement built into the privileged access flow, with reporting that proves enforcement
- Compliance reporting that generates audit-ready outputs without manual data assembly
- Identity lifecycle integration with HR systems, Active Directory, and cloud IAM platforms
miniOrange PAM is built to address exactly these requirements, offering a unified platform covering vaulting, session monitoring, JIT access, MFA enforcement, and compliance reporting across on-premises and cloud environments. For organizations pursuing or maintaining ISO 27001 certification, it closes the gap between having a PAM policy and being able to prove it is working.
Frequently Asked Questions
Is PAM mandatory for ISO 27001 compliance?
Yes. While ISO 27001 does not mandate a specific PAM product, the controls in Annex A 8.2, 5.15 through 5.18, and 8.15 collectively require formal governance of privileged accounts. Meeting these requirements without a dedicated PAM capability is extremely difficult to sustain and even harder to evidence at audit.
What ISO 27001 controls relate to PAM?
The primary controls are Annex A 8.2 (privileged access rights), Annex A 5.15 through 5.18 (access control and identity management), and Annex A 8.15 (logging and monitoring). Together, they govern how privileged access is approved, scoped, authenticated, recorded, and reviewed.
What evidence is required for ISO 27001 PAM audits?
Auditors look for a privileged access policy, a complete account inventory, approval records, access review reports, tamper-proof PAM logs and session records, and documented proof that MFA is enforced across all privileged accounts.
What is the difference between access management and privileged access management?
Access management handles general user access across business systems. PAM specifically governs high-risk administrative privileges with the potential for system-wide impact. PAM applies a higher level of control, monitoring, and documentation because the consequences of misuse are far greater.
How often should privileged access be reviewed under ISO 27001?
ISO 27001 requires periodic reviews but does not specify a fixed frequency. Best practice for high-privilege accounts is quarterly, with additional reviews triggered by role changes, departures, or security incidents. Reviews must be documented and outcomes retained as audit evidence.


Leave a Comment