Need Help? We are right here!
Search Results:
×Highly sensitive and confidential data is accessible to the higher authorities, including system administrators, DevOps engineers, database teams, third-party vendors, and automated services. These authorities hold privileged accounts through which these sensitive datasets can be accessed. If these accounts are compromised, then the entire organization can collapse.
To prevent this situation, a Privileged Session Management (PSM) solution is used. It ensures that all the privileged accounts are visible, monitored, controlled, and traced. So, any threat is detected and dealt with swiftly. Simply put, a Privilege Session Manager is the backbone of a mature PAM product. To add further, in modern environments, controlling access is not enough, controlling the session is critical.
miniOrange PSM software streamlines privileged access control while strengthening oversight through continuous monitoring and reporting.
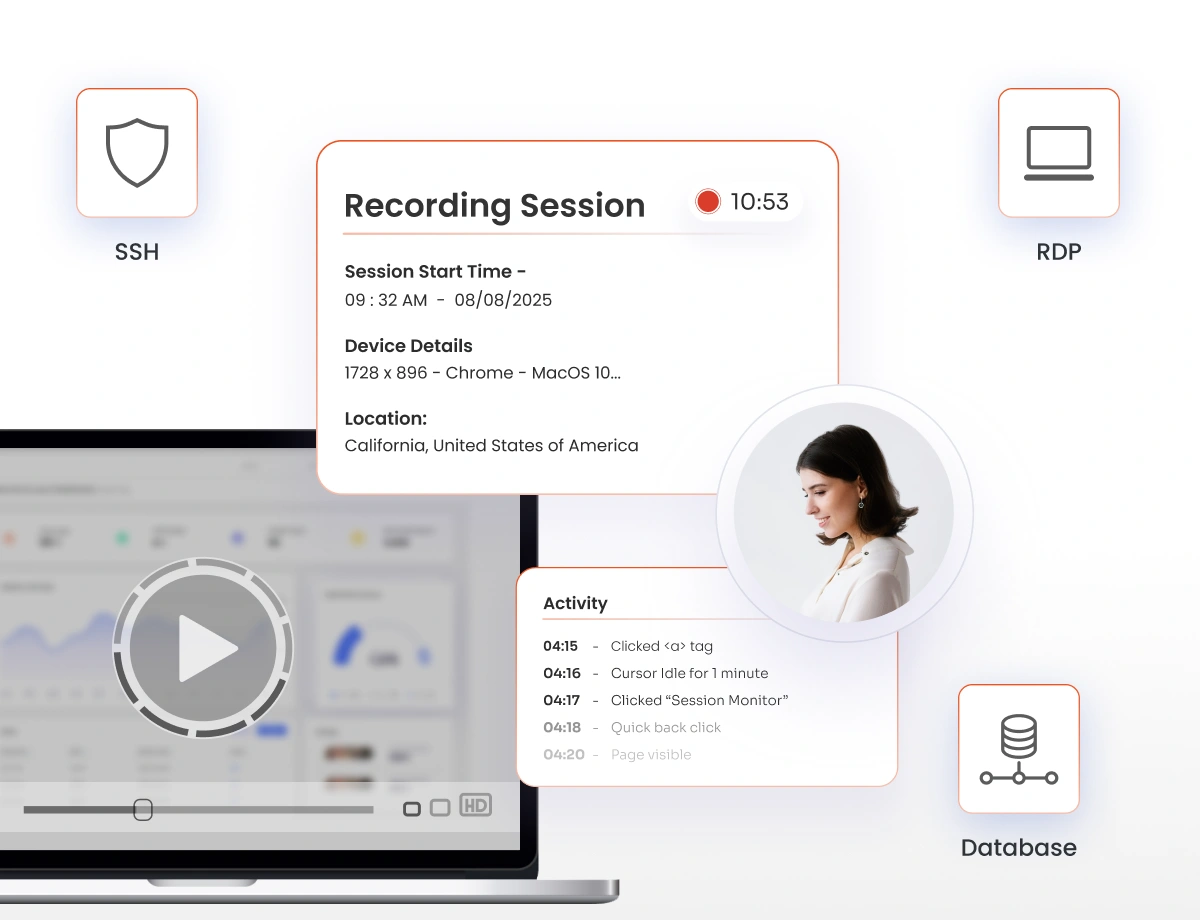
Capture and monitor privileged user activities across SSH, RDP, and database connections in real time. Track actions of privileged users, and record on-screen activity, giving security teams complete visibility and control.
The PSM tool uses AI anomaly detection to baseline normal behavior and flag deviations, such as unusual commands, abnormal access times, or risky navigation patterns, so your team can intervene early. This helps to prevent insider threats and compromised accounts.
Session Collaboration Allow multiple admins to securely join a single privileged session for troubleshooting, training, or knowledge transfer without sharing passwords or losing accountability.
Record every privileged session as video with rich metadata, commands, timestamps, user identity, and target system, so you can replay exactly what happened in seconds. Use recordings for incident forensics, internal reviews, and regulator-ready evidence.
Generate unchangeable logs of all privileged session activities with detailed timestamps and event tracking. Ensure compliance with regulations such as PCI-DSS, HIPAA, and ISO 27001 through complete audit readiness.
The PSM controls and monitors live sessions, and works together with Privileged Account Management capabilities such as credential vaulting, rotation, Just-in-Time (JIT) access. This ensures that only authorized, time-bound access is initiated on privileged sessions.
Privileged session management tools make sure that every session is secure - right from access request to archiving logs for compliance.
Users request privileged access through a self‑service portal/automated workflow tied to RBAC or predefined policies. Requests include ticket IDs, reasons for access, and time limits.
The system validates identity using authentication methods and routes the request to the right approvers if needed. Authorized users receive time‑bound privileged access aligned with policy.
The session is brokered through the miniOrange PSM gateway and never directly to the endpoint. Credentials are vaulted, and they are used securely, but never revealed to the user.
The PSM solution begins full privileged session monitoring and video recording with metadata capture. Admins can watch live sessions and receive alerts for suspicious behavior.
For suspicious activities, security teams can instantly pause, terminate, or restrict the session. AI‑driven anomaly detection speeds up response and highlights risky behavior in real-time.
Data is stored in a secure repository with searchable logs and reporting for audit trails and compliance checks. SIEM integration centralizes data and helps detect and respond to threats.
PSM brokers all sessions through a secure gateway, eliminating direct access and removing the need to share or expose privileged credentials.
Quickly grant, monitor, and revoke time-bound access for admins and vendors with role-based controls and full activity tracking.
Maintain detailed session logs, user activity reports, and audit trails to meet standards like PCI DSS, NIST, and SOC with minimal effort.
Round-the-clock support ensures instant resolution to issues, customization, optimization, and training worldwide.
miniOrange integrates smoothly with existing PAM, IAM, SIEM, and ITSM tools, reducing implementation friction.
The PSM solution offers detailed audit trails, live monitoring, session recording, and AI-driven anomaly detection, so you have complete visibility of user activities.
miniOrange scales with your growth and is backed by responsive technical support and continuous product innovation.
Start your free trial of the Privileged Session Management today and gain full visibility and control over your sensitive sessions.
