What is Password-Based Authentication?
Password-based Authentication is the process of gaining access to resources to which one is entitled with the help of a set of credentials containing a username and password. This is a rampantly used method known for process simplicity and low cost.
Although this approach is convenient and widely used, it carries vulnerabilities that can lead to attacks and breaches. Therefore, organizations must adopt secure authentication and implement the best password practices to mitigate these risks, as failure can result in financial and reputational harm. In this blog, we'll explore the optimal practices for username and password authentication to enhance security for both users and organizations.
An Overview of Username and Password Authentication
Username and Password Authentication is one of the most widely used authentication methods in securing user accounts. The system validates the authenticity of the entered credentials against the database values and, upon a successful match, the user is granted access. As we know, this method is straightforward and user-friendly, making it a prevalent choice for securing user interactions with various systems and online services.
Even though its widespread usage doesn't overshadow its vulnerability to numerous security threats, including brute force attacks, phishing scams, and credential-stuffing instances. Given these vulnerabilities, there is a prevailing trend amongst users to create simplistic, easy-to-remember passwords and deploy them across diverse platforms.
1. Password and Username for registration Upon initially logging into a website, or while signing up the users are prompted to enter their username and password for identification purposes. If an account is not already established, users are guided to create one, necessitating the selection of a username and password.
Ideally, users would consistently opt for robust and distinctive usernames and passwords. However, reality often diverges from this ideal scenario, with many individuals opting for simplistic credentials to facilitate easy recall.
2. Enforcing Strong Password Policies From a security perspective, the efficiency of a password increases with its length and complexity. Therefore it is important to encourage users to adopt good password practices while creating new passwords. A strong password establishes a balance between mandatory minimum requirements and the complexity level, to ensure user-friendly experiences.
To reinforce password strength, consider implementing the following guidelines for your users:
- A minimum length of 8 characters
- Inclusion of at least one uppercase letter
- Inclusion of at least one numeral
- Incorporation of at least one special character
3. Secure Storage of User Credentials After a user selects their username and password and submits it, an appropriate storage location for this information is needed. The first step is to cross-check that the user isn’t already an existing one in the database, after that it is imperative to check that the password is complying with the password guidelines.
Initially, users are validated within the existing database, it is crucial to check if the user isn’t already in the database. Upon assurance of confirmation of users, the password is checked if it meets the predetermined standards and minimum requirements on the server side. However, a crucial step remains the implementation of password hashing.
4.Implementing Password Hashing
Password hashing is like turning a password into a secret code or an unrecognizable string of characters. This code, or 'hash', is made using a special computer trick. Before saving any password, it needs to be changed into this secret code. This way, even if someone sees the code, they can’t easily figure out what the original password is. The majority of programming languages support password hashing either inherently or through auxiliary libraries. It is essential to select a secure and proven hashing algorithm for the implementation of password hashing.
5. Managing Returning Users
Once a user has completed the registration process, they will likely revisit your site. At this point, you will need to authenticate their identity using the credentials they provided. When they log in, you will need to search your database for the corresponding username, a process typically automated by your server. If a match is found, the hashed password input should align with the one stored in the system.
How to increase security for password-based authentication?
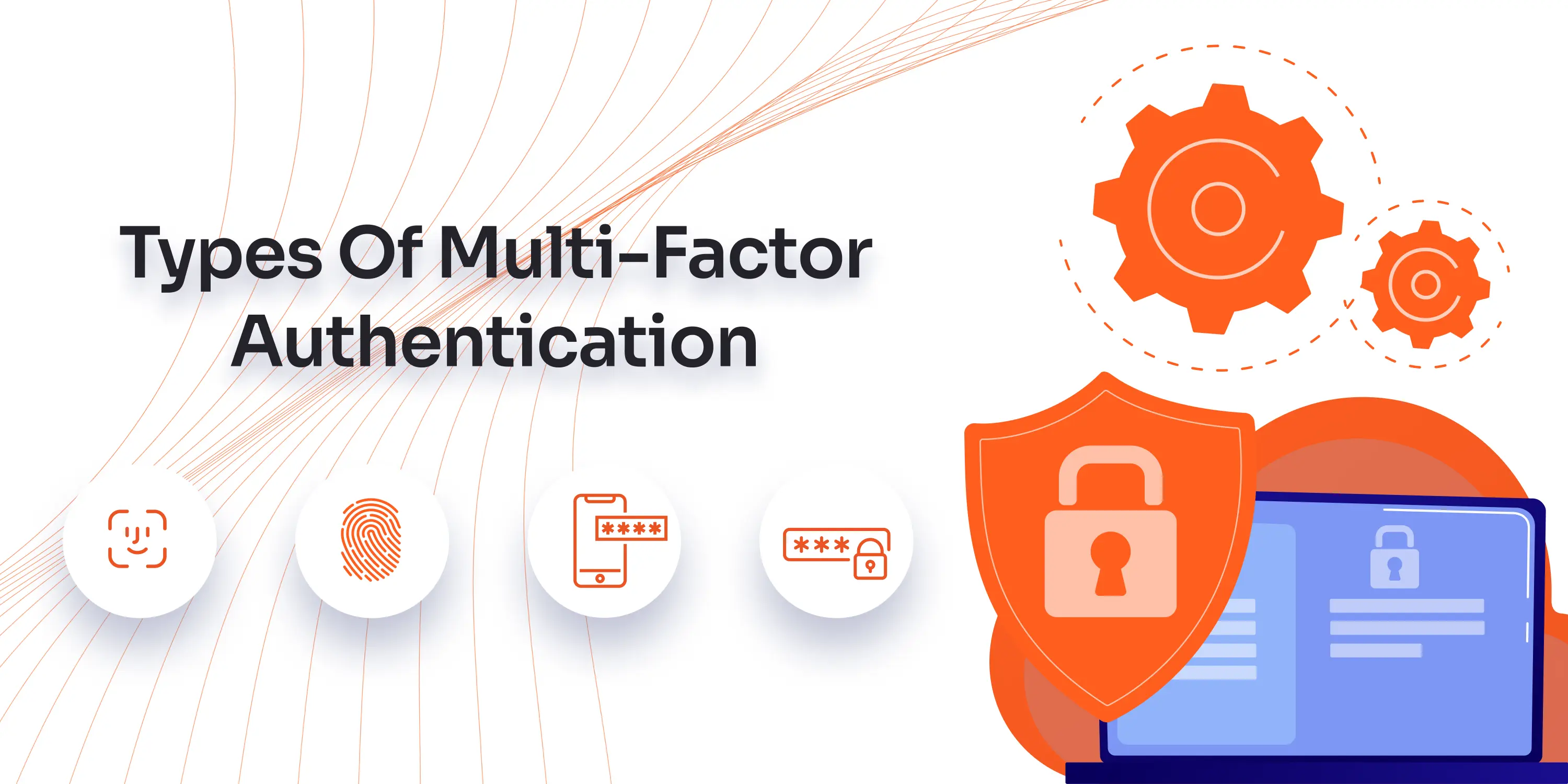
To enhance the security of password-based authentication systems, it's essential to implement robust password policies and regular updates while integrating additional layers of security. Despite vulnerabilities, traditional username and password methods remain crucial in security infrastructures as a primary layer of defense. Strengthening password protocols and incorporating frequent modifications are key steps in enhancing security. Moreover, the widespread adoption of Multi-Factor Authentication (MFA) adds an extra security layer, thereby reducing dependency on passwords alone and significantly enhancing overall security resilience against unauthorized access and potential breaches.
In a scenario when users can’t recall their login details, what should be done?
Assuming the required username is an email address, you would need to create a password reset link and send it to the user’s email, allowing them to establish a new password. Since you only have access to the user’s hashed password in the database, it’s impossible to retrieve the original password, necessitating the creation of a new one by the user.
What are Some Challenges of Password-Based Authentication?
Password-based authentication, while a prevalent security measure, is riddled with challenges and vulnerabilities, primarily stemming from user behavior and advanced hacking techniques. Below are some of the notable challenges associated with password-based authentication:
1. Repetitive Use of Passwords Across Platforms The prevalent practice of reusing passwords across multiple platforms exposes users to heightened risks. When one system is compromised, it potentially makes all accounts using the same password vulnerable to unauthorized access.
2. Creation of Weak and Predictable Passwords To remember passwords, users end up creating easy-to-remember passwords, which more often than not are weak and predictable, thus inviting security threats. The majority of user-generated passwords lack strength and are susceptible to hacking due to a lack of adherence to security best practices and the subconscious use of patterns.
3. Risks of Password Sharing The intentional or unintentional sharing of passwords compromises the integrity of the security infrastructure, making systems more prone to unauthorized access.
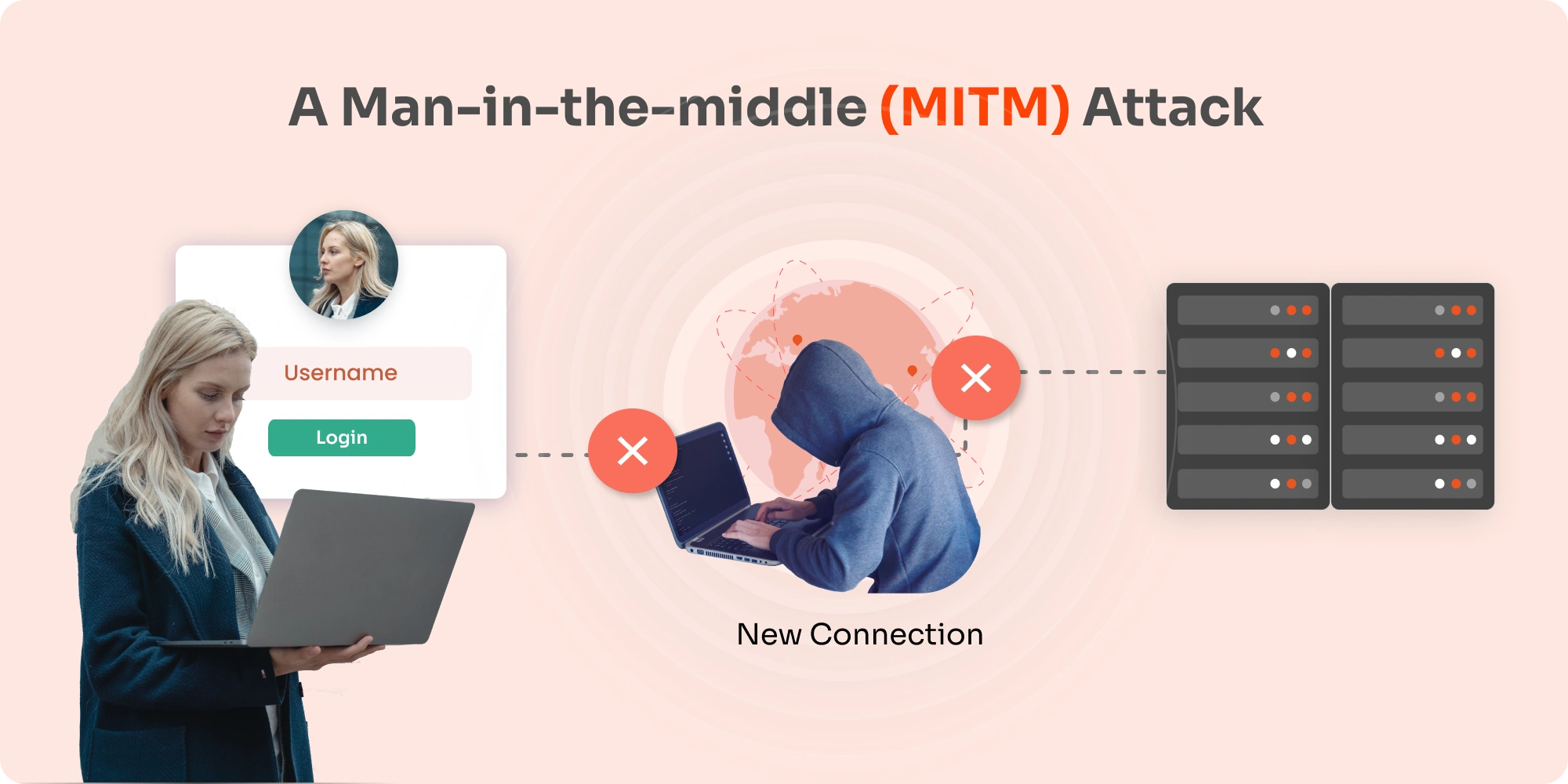
4. Vulnerability to Phishing Attacks Deceptive phishing attacks can trick users into disclosing their passwords, providing attackers with unauthorized access to secured systems.
5. Susceptibility to Brute Force Attacks These attacks, involving automated programs running through every possible password combination to find a match, are a common and effective method used by hackers to gain unauthorized access. The rapid processing of combinations means shorter and common passwords are particularly vulnerable.
6. Recycling of Passwords and Insecure Storage The difficulty in remembering unique, complex passwords for multiple accounts often leads to password recycling. The storage of these passwords in insecure locations like sticky notes or unprotected documents makes them easy targets for theft or loss.
7. Consequences of Large-Scale Breaches The improper storage of user credentials and weak internal passwords can lead to large-scale breaches, affecting businesses and organizations of all sizes. When one service is broken into, it can cause a chain reaction, putting the accounts of employees and regular users in danger.
8. Damage due to external Breaches A breach in the security of one website or service can have ripple effects, compromising the security of other platforms and putting users and their data at risk.
Addressing the Challenges
Addressing these challenges necessitates a holistic approach, combining robust password policies, user education on password security best practices, and the incorporation of additional security layers like Multi-Factor Authentication (MFA) to fortify defenses against unauthorized access and potential breaches.
Best Alternatives of Password-Based Authentication
The best substitute for Password-based authentication would be a protocol that doesn’t just rely on traditional IDs and passwords for authentication. An alternative to passwords encompasses any authentication protocol that does not require conventional IDs and keys to authorize user access, often leaning on possession or inheritance-based methods instead.
Let us now have a look at a few of the many Passwordless Authentication methods offered by miniOrange
1. OTP over SMS & Phone call back Users can opt for various multi-factor authentication methods. One method is receiving a One-Time Password (OTP) via SMS, wherein a numeric key is sent to the registered mobile number, which needs to be entered as a second factor to gain access. Another method is through an SMS link sent to the registered mobile number, where users can click to accept or deny, with acceptance completing the second-factor authentication challenge. Lastly, users can opt for OTP over a phone call, where a voice call relays a numeric key to be used for completing the second-factor authentication challenge.
2. Utilizing Third-Party Authenticator Apps For enhanced security, users can utilize authenticator apps like Google Authenticator, Microsoft Authenticator, or Authy Authenticator as MFA methods. Each requires the user to scan a QR code to link the account, after which a 6-digit code is generated by the app to complete the MFA challenge and access resources, ensuring a streamlined yet secure access process.
3. Secure Access with miniOrange Authenticator Using miniOrange Authenticator, users have several MFA options. They can use a soft token method, entering a 6-8 digit key from the app to gain secure access. Alternatively, users can enable push notifications as MFA, receiving and accepting notifications on the miniOrange app to complete the second-factor challenge. Lastly, QR code authentication allows users to scan a barcode using the app to link their account and authenticate the MFA challenge seamlessly.
4. OTP over SMS & E-mail With OTP Over Email, users receive a one-time password (OTP) over email, which is sent to their registered email address. Whenever a login attempt is made the server will automatically send a One-Time Password (OTP) to the user's registered email address as an added security measure. Alternatively, the Email Link method sends users an email containing a link to accept or deny transactions, with acceptance completing authentication. Additionally, users can opt for OTP Over SMS where they again, receive a one-time OTP to their registered mobile number to authenticate themselves.
You can implement any of these solutions with the miniOrange Multifactor-Authentication method in addition, they can all be used along with password-based authentication.
FAQs
1. How does authentication ensure that the username and password are correct? Ans - Authentication verifies the correctness of the username and password by matching the entered credentials with the stored values in the system.
2. What are the 3-factor authentication for username and password? Ans - The 3-factor authentication involves something you know (password), something you have ( smart card or phone), and something you are (biometric method).
3. What is the strongest authentication factor? Ans - Biometric authentication is generally considered the strongest authentication factor as it is based on unique attributes.

Leave a Comment