Your Privileged Access Management (PAM) tool is running. Your vaults are configured. Your sessions are monitored. And somewhere in the environment, a former contractor’s account still has domain admin rights.
This is the problem that Privileged Access Governance (PAG) solves. In this blog, we'll see why having the right Privilege Access Management tools isn’t the same as having privileged access under proper control.
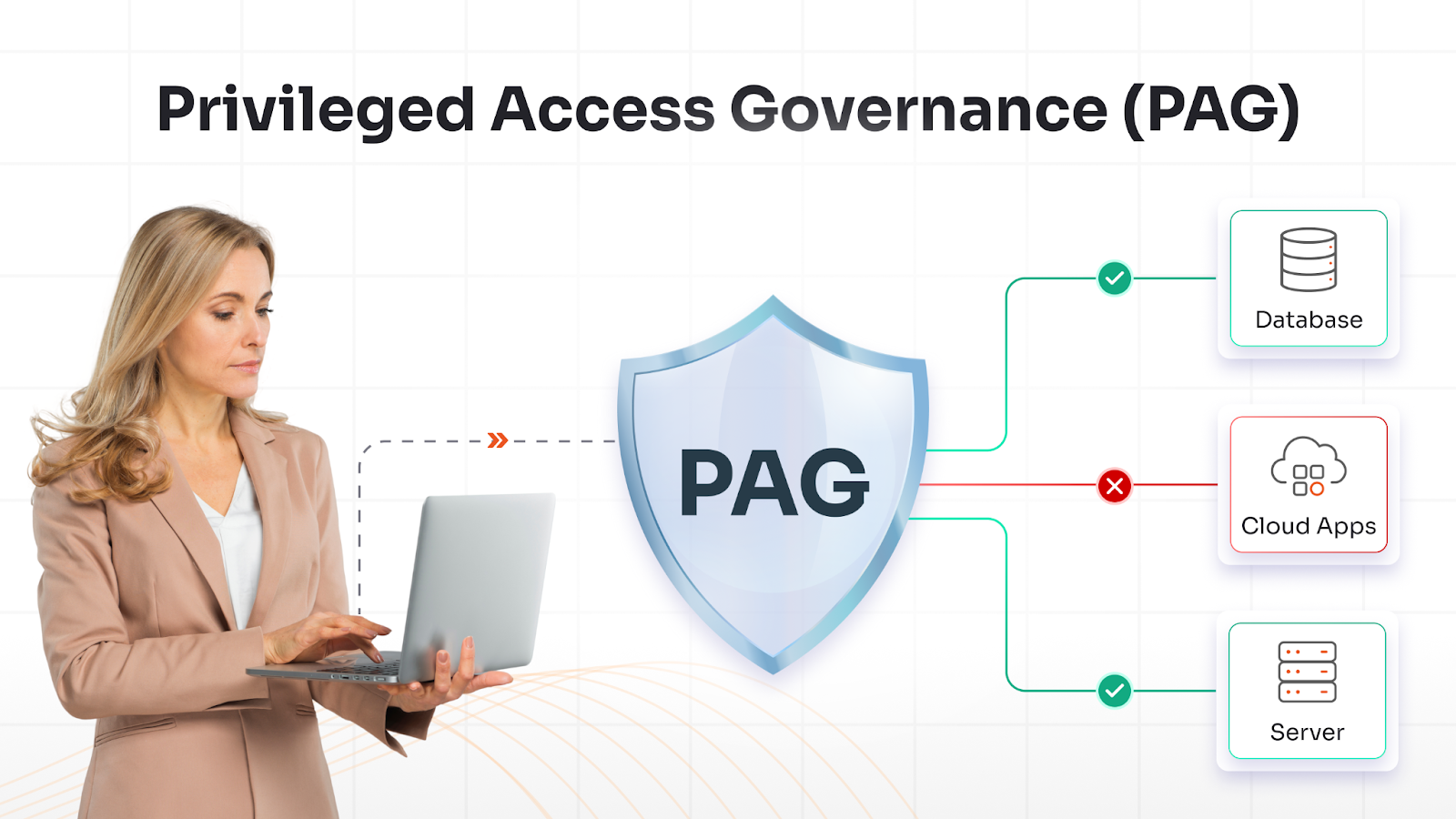
What Is Privileged Access Governance?
Privileged access governance (PAG) is defined as the framework of policies, processes, and controls that answer questions that technology alone can’t. For example:
- Does this person still need domain admin rights?
- Was this level of access ever formally approved?
- Has anyone reviewed these entitlements in the last 90 days?
PAM enforces access, and PAG governs it. One without the other leaves gaps, and gaps are exactly what attackers look for.
PAG is in the broader Identity and Access Management (IAM) landscape, specifically under Identity Governance and Administration (IGA). But IGA covers all identities across the organization. And PAG narrows its focus to only privileged accounts.
Privileged accounts are the accounts that carry the highest risks, the ones that, if abused or compromised, can do the most damage.
In practice, that means:
- Admin & root accounts: The accounts with unrestricted system access, the ones that can change anything and delete anything
- Service accounts & non-human identities (NHIs): API keys, OAuth tokens, and machine credentials that run automated processes, often with elevated permissions and almost no human oversight
- Cloud roles with elevated rights: IAM roles in AWS, Azure, GCP, and similar environments that carry broad permissions across cloud infrastructure. These are often provisioned quickly and reviewed rarely
- Third-party & vendor privileged access: External accounts like contractors, managed service providers, and software vendors
But why exactly do these privileged access accounts need governance when they’re already under management tools?
Why Privileged Access Needs Governance?
Access doesn’t stay clean on its own. For example:
- An engineer gets elevated rights for a migration project. The project ends. But the rights don’t.
- A contractor wraps up an engagement. But their service account keeps running.
- An application gets provisioned with admin permissions because it was the quickest way to get things working.
Nobody does this maliciously. It just happens, and over time, it builds up.
Here are 2 incidents from 2024 that show exactly where that build-up leads.
Midnight Blizzard Breach
In the Microsoft “Midnight Blizzard” breach, attackers got in through a forgotten, low-value test account. From there, the attackers moved through over-privileged OAuth application roles. Those roles include accounts with full mailboxes and executive communications access.
The credentials were legitimate. The access was also real. The problem was that nobody had reviewed whether any of it was still appropriate. Microsoft's own post-incident analysis pointed directly at over-privileged legacy applications and misconfigured high-privileged roles.
Snowflake Customer Breach
The 2024 Snowflake customer breach cluster followed the same pattern. Accounts with far broader data-read permissions than the job required. Attackers pulled bulk data without technically “hacking” anything. These weren’t zero-day exploits. They were the privileged accounts left ungoverned long enough to be useful to an attacker.
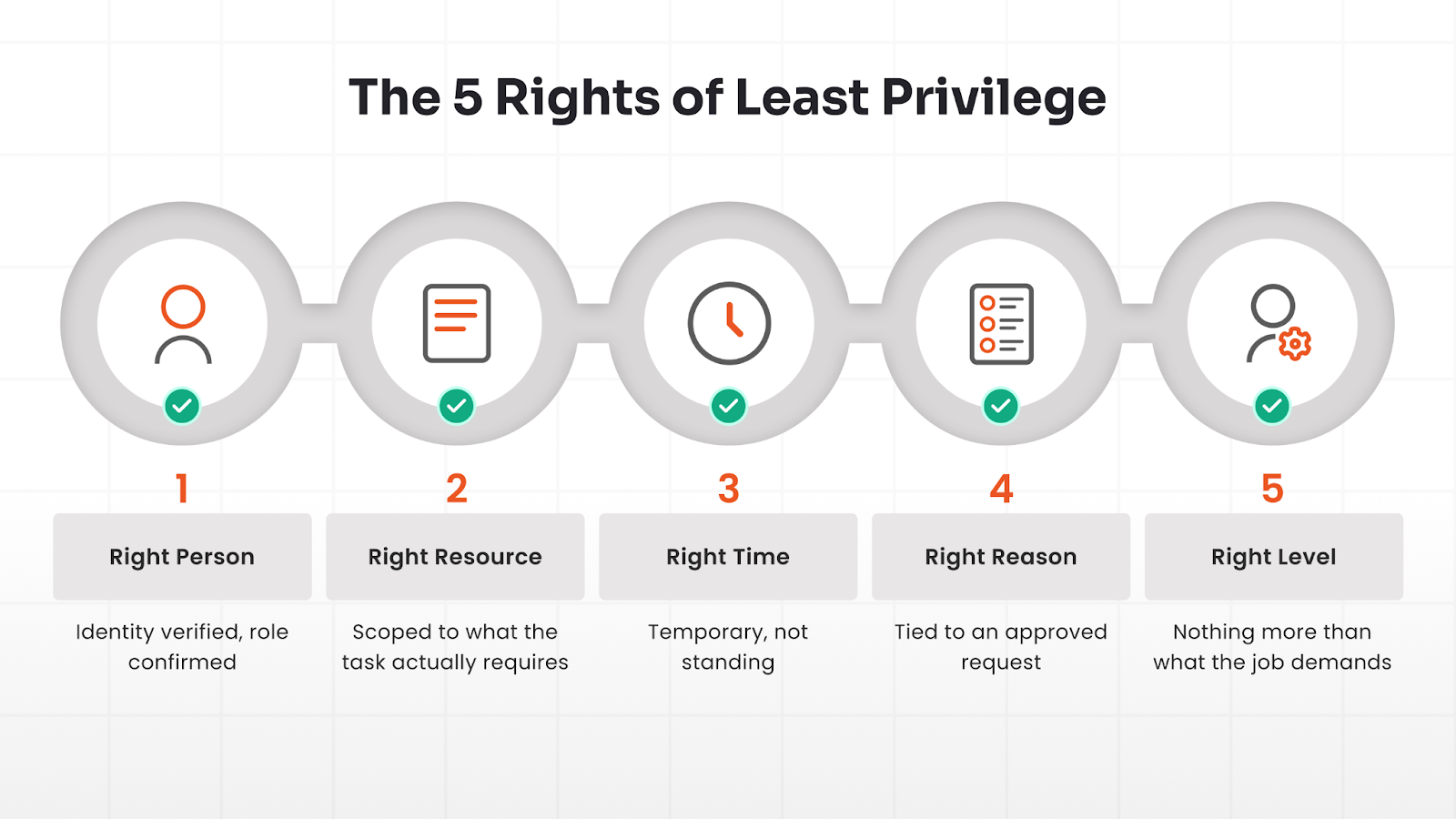
The principle of least privilege is what PAG enforces in practice. It means access should be granted to the:
- Right person — identity verified, role confirmed
- Right resource — scoped to what the task actually requires
- Right time — temporary, not standing
- Right reason — tied to an approved request
- Right level — nothing more than what the job demands
How Privileged Access Governance Works and Key Components
The Privileged Access Governance framework is a lifecycle. It covers privileged access from when a user gains the privileges to when they are revoked. Here's how the stages work.
1. Discovery of Privileged Accounts & Entitlements
You cannot govern what you have not found. The first step in any PAG program is a complete inventory of privileged accounts. This includes:
- Human user accounts with elevated permissions
- Service accounts and application accounts
- Shared administrative accounts
- Dormant accounts that no longer map to an active identity
- Privileged identities provisioned in cloud platforms, SaaS applications, and databases
Without this visibility, everything after this step is incomplete.
2. Define User Roles and Access Policies
Once the organization has mapped the inventory, they need to define what privileged access should look like for each role. This means policies tied to real job functions, not to whatever was provisioned years ago.
This is where the PAG framework connects to Zero Trust Architecture (ZTA) principles. ZTA states that access should be explicitly authorized and should be minimal by default, not broad and persistent. Access policies define the baseline. Anything outside the baseline becomes auditable.
3. Just-in-Time & Just-Enough Access Requests and Approvals
Standing privilege is one of the most common governance failures. It's when users hold elevated access continuously, whether they need it or not. Just-in-Time (JIT) access addresses this:
- A user requests elevated access when a task requires it
- The request goes through an approval workflow
- Access is granted for a defined time window
- It expires automatically when the window closes
Every instance of privileged access now has an approval record behind it. In a compliance audit, this is evidence. And this evidence becomes a hard constraint for an attacker who would otherwise find standing credentials ready.
4. Monitoring, Session Tracking, & Audit Logging
Granting access correctly is only half the job; what happens during the session matters too. Session monitoring records privileged user activity in real time. It includes commands executed, files accessed, and configuration changes made.
When this data is fed into a SIEM tool (Security Information and Event Management), it gives SOC teams the context needed to distinguish legitimate activity from an attacker's activity.
5. Access Reviews & Recertification
Access that made sense six months ago may not make sense today. Roles change. Projects end. People move teams. Access recertification is the scheduled process of asking managers and resource owners to confirm or revoke the current entitlements.
Regulators under PCI DSS, HIPAA, and SOX specifically look for evidence of recurring access reviews. And recertification generates and stores the evidence.
6. Reporting, Compliance, & Continuous Improvement
Every step in the Privileged Access Governance process produces data. And reporting turns this data into something useful:
- Audit trails that map user access to policies
- Anomaly reports that flag unusual privileged use
- Dashboards that give security leadership a live view of ongoing activities
All this data drives improvement. Meaning, with time, it leads to improvements in policies, shorter JIT windows, broader governance coverage, and smooth integration of new systems as they come in scope.
Privileged Access Governance (PAG) vs. Privileged Access Management (PAM)
PAM and PAG are not the same thing. They are complementary, work in sequence, and both are necessary.
- PAM is the technology layer. It includes the password vault, session proxy, credential rotation, and JIT provisioning engine. When an administrator requests database access, PAM retrieves the credential, opens the session, and records what happens.
- PAG is the governance layer. It decides whether that administrator should have had access at all, whether the level granted was proportionate, and whether someone has reviewed that entitlement recently.
To understand Privileged Access Governance vs. Privileged Access Management better, think of a building’s security.
A policy committee decides who should access sensitive areas and under what conditions. The access control system enforces those decisions. PAG is the policy committee. PAM is the access control system. Without governance, enforcement has no coherent policy to act on. Without enforcement, governance is just a document that no one acts on.
Organizations that run PAM without PAG are enforcing access "technically" but not governing it "strategically." Over time, ungoverned entitlements accumulate, and as the breach examples above show, that is exactly what attackers look for.
7 Benefits of Privileged Access Governance
Governance done right doesn’t just reduce risk, it makes the entire security program easy to run, easy to prove, and easier to scale. Here’s what that looks like in practice.
1. Audit-ready compliance: GDPR, HIPAA, PCI DSS, and SOX all require proof of controls over who accesses sensitive systems. PAG generates the access logs, approval records, and recertification histories that auditors ask for
2. Elimination of standing privilege: JIT access means no standing privilege admins are available for an attacker to pivot through. This is one of the most exploited conditions in modern breach chains
3. Early detection of entitlement drift: Users accumulate access over time without anyone noticing. PAG's recertification cycles catch this before it becomes a compliance issue or a breach vector
4. Faster incident response: When a security incident involves a privileged account, session logs and access history tell you what happened, when it happened, in less time
5. Reduced attack surface: Regular reviews remove entitlements. Less standing access means less space for an attacker to move through
6. Scalability across cloud and SaaS: With every new cloud environment and SaaS platform, privileged identities multiply. PAG provides the governance structure to manage that growth without losing visibility
7. Zero Trust in practice: ZTA requires access to be explicitly granted, continuously verified, and minimal in scope. PAG operationalizes those principles for privileged identities
Also read: Easy Steps to Implement Zero Trust in Your Organization
The question isn’t whether these benefits matter. It’s whether your current setup is actually delivering them. If not, you need a Privileged Access Governance solution that does that, and helps scale your organization.
Enable Privileged Access Governance at Scale with miniOrange
Managing privileged access governance across a modern, distributed environment is not a problem that policy documents solve on their own.
miniOrange PAM platform supports every stage of the privileged access lifecycle. From account discovery and role-based policy definition to session monitoring and JIT provisioning.
Whether you are establishing policies for the first time or upgrading your PAM, miniOrange can help you close the gap between what your access policies say and what is actually happening in your environment.
FAQs
Is Privileged Access Governance Part of IGA?
PAG is related to IGA but is more specialized. IGA covers identity lifecycle management across all users. PAG applies the same principles specifically to privileged accounts and deeper integration with PAM tooling.
How do PAG, PAM, and IGA Work Together?
IGA sets the overall governance framework. PAG applies it to privileged identities. PAM enforces it technically. In practice, IGA governs, PAG specializes, and PAM executes.
What Are the Core Pillars of Privileged Access Governance?
Four pillars of Privileged Access Governance:
- Visibility — finding all privileged accounts
- Control — defining access policies
- Oversight — monitoring and recording activities
- Accountability — running access reviews and producing compliance records
What are Privileged Access Governance Best Practices?
Start with a full discovery exercise. Enforce least-privilege policies tied to actual job functions. Replace standing privileges with JIT access. Run scheduled, substantive recertification reviews. Integrate data from the Privileged Access Governance solution with your SIEM.



Leave a Comment