We just got back from Atlassian Team '26 in Anaheim. Three days, thousands of attendees, and Atlassian's biggest push yet toward human-AI collaboration. The Founder Keynote set the tone, Rovo agents got smarter, and the Teamwork Collection took center stage. It was a packed, high-energy week.
But the most interesting part of our three days wasn't on stage. It was at Booth #211.
What we actually heard at the booth
Over three days, we spoke with hundreds of attendees, from Fortune 500 enterprises and healthcare organizations to government teams, financial institutions, and solution partners across the Atlassian ecosystem. The themes were remarkably consistent.
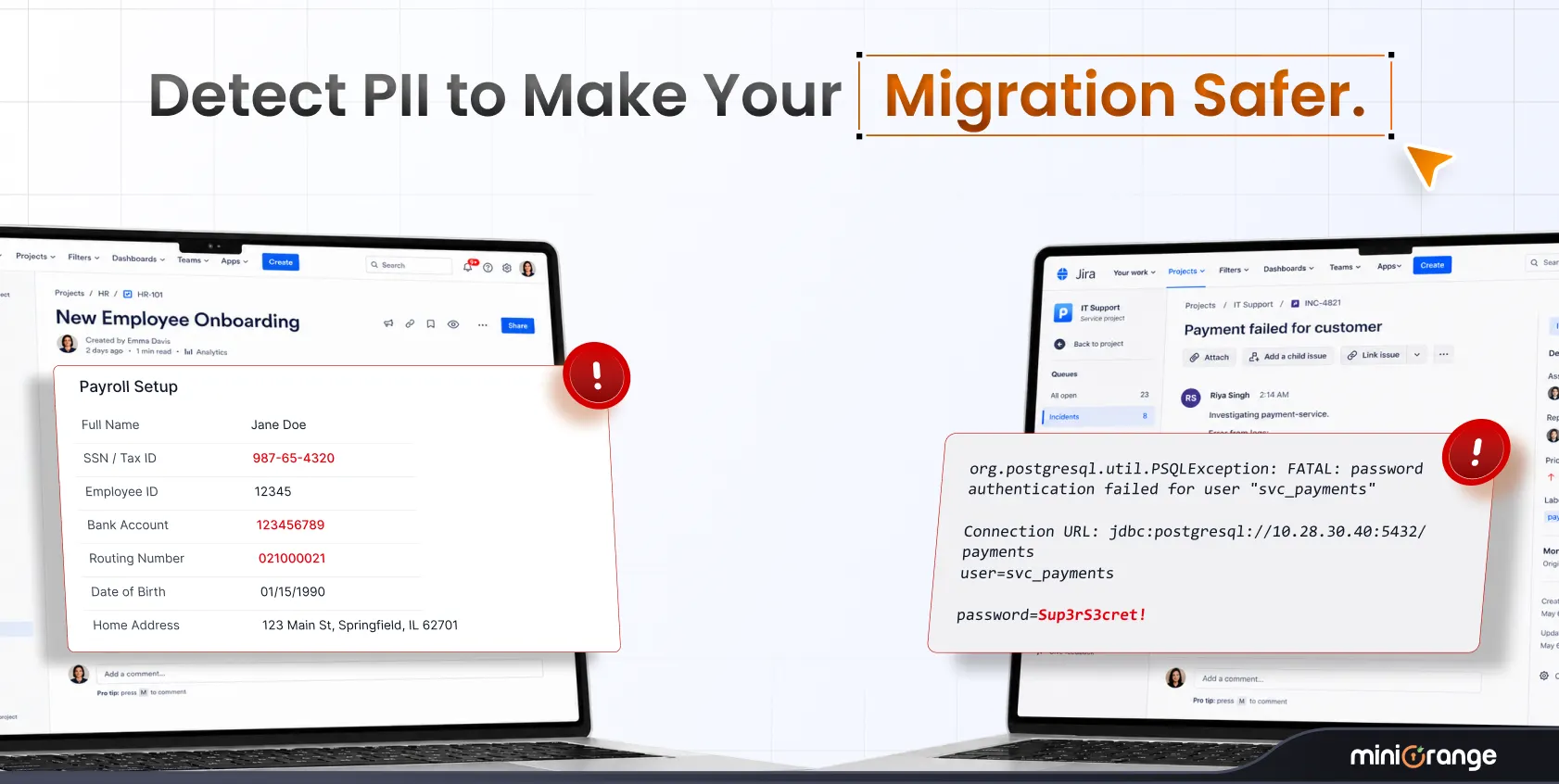
Nobody walked up asking for a feature list. The questions were outcome-oriented. How do we manage SSO across multiple IDPs when we're on Enterprise Cloud? How do we control who sees what in a shared Jira project without over-licensing? How do we get audit-ready without building a manual tracking system? How do we protect PII that's scattered across Jira tickets and Confluence pages?
That last one came up more than anything else. DLP and PII protection for Atlassian Cloud was the single highest-interest topic across all three days. As organizations migrate to Cloud and adopt Enterprise plans, the surface area for sensitive data exposure grows, and the native tools don't quite cover it.
The other conversations followed a similar pattern. Teams dealing with multiple Atlassian organizations, wrestling with site-level access that Atlassian Guard Standard doesn't fully address, needing granular group syncing from Okta or Entra ID, and wanting audit trails for who approved access and when. These aren't edge cases. This is the norm for any organization running Atlassian at scale.
The Braindate conversations confirmed it
We hosted and attended Braindate sessions focused on identity management in Cloud and managing access requests in JSM. In one session, a customer had configured SCIM from Entra ID to Atlassian Cloud but was struggling with group management. They mentioned that managing site-level access is difficult and that there's no proper auditing around who approved access and when it was granted.
This reinforces what we kept hearing at the booth. The need for stronger access governance, approval tracking, and audit-ready reporting on top of Atlassian Cloud is real and growing. The native tooling gets you part of the way there. The last mile is where apps like ours come in.
Where we go from here
Team '26 gave us a clear picture of where Enterprise Atlassian customers are headed: deeper into Cloud, deeper into Enterprise plans, and dealing with identity and data security challenges that get more complex with every migration. The demand for PII protection, access governance, automated user management, and audit readiness is not hypothetical. It's active, it's urgent, and it's growing.
If we crossed paths in Anaheim, great to meet you. If we didn't, let's fix that.
Book a meeting with our team or explore our Atlassian apps.
— The miniOrange Atlassian Team



Leave a Comment