For years, cybersecurity relied on a secure network perimeter, where users were trusted once inside. This approach was effective when everything was contained in a controlled environment, but it no longer works today.
Modern organizations operate across cloud platforms, SaaS, mobile devices, and distributed teams. Employees and partners connect from various locations while APIs exchange data. As a result, the traditional network boundary no longer exists.
This shift is why the Zero Trust model has gained so much attention in cybersecurity. The principle of zero trust is simple: never trust, always verify. Instead of granting access based on network location, every access request must be validated using identity, context, and risk signals.
Given this change, Zero Trust IAM becomes critical. Identity and Access Management acts as the enforcement layer that determines who can access what, under which conditions, and for how long. Without a strong identity foundation, Zero Trust cannot function effectively.
Modern IAM platforms, such as miniOrange, help organizations operationalize Zero Trust by combining authentication, authorization, adaptive policies, and centralized identity governance across cloud, on-premises, and hybrid environments.
Understanding the Zero Trust Model
The Zero Trust framework is built around a simple idea: trust should never be assumed. Every request to access an application, system, or dataset must be verified before access is granted. This principle emerged as organizations moved away from centralized networks toward cloud infrastructure, SaaS applications, and remote work environments.
Traditional security models relied on perimeter defenses such as firewalls and VPNs. Once users entered the network, they were typically trusted. In contrast, Zero Trust assumes that threats can exist both inside and outside the network. Every access request must therefore be validated using multiple signals such as user identity, device posture, location, and behavioral context.
Several core principles define the Zero Trust approach:
- Least privilege access: Users receive only the access required to perform their tasks.
- Continuous verification: Identity and device posture are validated throughout the session, not just during login.
- Context-aware access decisions: Access policies adapt based on risk signals such as device health, location, and login behavior.
In modern cybersecurity strategies, identity effectively is the new security perimeter. As a result, Identity and Access Management is central to enabling Zero Trust.
What is Zero Trust IAM?
Zero Trust IAM refers to using Identity and Access Management systems to enforce the principles of the Zero Trust security model. Instead of granting access solely based on network location or static credentials, IAM continuously evaluates identity signals before granting access to applications and sensitive data.
In a Zero Trust environment, IAM platforms perform several key functions:
- Authentication: Verifying the user’s identity through methods such as MFA, passwordless login, or biometrics.
- Authorization: Determining whether the authenticated user should be allowed to access a specific resource.
- Risk analysis: Evaluating contextual signals such as device trust, login location, and behavioral anomalies.
Another important aspect of Zero Trust IAM is continuous session validation. Access is not granted permanently after login. Instead, the IAM system regularly checks identity signals, such as device trustworthiness and login location, during the user session. If certain risk conditions occur, for example, if a device fails a security check or a user’s location changes unexpectedly, the system can immediately re-evaluate and adjust access permissions.
This approach ensures that access decisions remain dynamic and aligned with the organization’s security posture.
How Does Zero Trust IAM Extend Traditional IAM?
Traditional IAM solutions primarily focus on managing user identities and controlling access through authentication and role-based permissions. While these capabilities are still essential, they are not sufficient for modern distributed environments.
To address these new requirements, Zero Trust IAM expands traditional IAM by incorporating additional signals beyond identity alone.
With this expanded approach, instead of relying only on who the user is, Zero Trust IAM evaluates multiple factors:
- Identity: Who the user is.
- Device: Whether the device is trusted or compliant.
- Behavior: Whether the login pattern appears suspicious.
- Context: Location, network, and access conditions.
As a result, access control is no longer limited to the login step. Policies can adapt in real time based on signals.
Modern IAM platforms enable adaptive authentication, contextual access policies, and centralized governance, enabling the implementation of Zero Trust IAM across all environments without relying on perimeter defenses.
Why are IAM and Zero Trust Inseparable in Modern Security?
As organizations shift toward identity-first security, IAM becomes the core mechanism that enforces Zero Trust principles across applications, users and devices. Instead of relying on network boundaries, access decisions are made based on verified identity signals and contextual policies.
Here’s why IAM and Zero Trust are inseparable today.
1. The Collapse of the Network Perimeter
For a long time, cybersecurity strategies assumed that the corporate network itself was a safe zone. Organizations invested heavily in firewalls, VPN gateways, and intrusion detection systems designed to protect the perimeter. Once users entered that perimeter, they were usually trusted.
That model worked when applications stayed in company data centers, and employees were in managed offices. Today, things are very different.
Now, organizations rely on cloud platforms, SaaS tools, mobile applications, and distributed teams. Employees access company systems from home networks, public Wi-Fi, and personal devices. Partners and vendors often need temporary access to internal systems. APIs constantly exchange data between services across different environments.
In this new reality, the traditional network boundary has largely disappeared. Attackers no longer need to breach a firewall to gain access. Compromised credentials, phishing attacks, and session hijacking can all result in the same outcome.
This shift is why IAM and Zero Trust are closely linked in modern cybersecurity strategies.
2. IAM and Zero Trust: The Enforcement Engine
At the heart of the Zero Trust model is a simple requirement: every access request must be verified before it is granted. But verification does not happen automatically. Organizations need systems that can evaluate identity, risk, and context in real time.
This is where Zero Trust IAM becomes the enforcement layer of the entire model.
An IAM platform determines whether a user should be allowed to access an application, API, or dataset. Instead of relying on network trust, access decisions are made based on identity signals and policy rules.
Modern IAM platforms enable this through several capabilities:
- Multi-factor authentication (MFA) to verify user identity beyond passwords.
- Single Sign-On (SSO) to centralize authentication across applications.
- Conditional or contextual access policies that adapt to risk signals.
- Role-based and attribute-based access controls (RBAC and ABAC).
- Just-in-time access provisioning to reduce standing privileges.
- API security integrations that enforce identity policies across services.
These controls grant access only when identity checks pass.
IAM platforms such as miniOrange bring these capabilities together in a unified system, enabling organizations to enforce Zero Trust policies across workforce, customer, and partner identities.
3. Identity as the Control Plane for Zero Trust
In a Zero Trust architecture, identity is the central control layer that governs access to systems and data.
Instead of relying on network location, organizations make security decisions based on identity signals. Every user, device, and application interaction undergoes identity verification and policy evaluation before access is granted.
This identity-centric approach offers several advantages. Security teams gain better visibility into who is accessing resources, when access occurs, and under what conditions. Policies can also adapt dynamically based on real-time signals such as device trust, geographic location, or unusual login behavior.
Centralized IAM platforms play a critical role in enabling this. By consolidating authentication, authorization, and identity governance into a single control plane, organizations can enforce consistent security policies across multiple environments.
Ultimately, this is why Zero Trust IAM is widely considered the operational backbone of Zero Trust security models. Without identity-driven access control, it becomes extremely difficult to enforce continuous verification or least-privilege policies at scale.
Architecture of Zero Trust IAM (Enterprise View)
Implementing Zero Trust is not just about adding new security tools. It requires a structured identity architecture that continuously verifies users, devices, and applications before granting access. At the center of this architecture sits Zero Trust IAM, which acts as the policy enforcement layer for identity-based access decisions.
Core Components of Zero Trust Model IAM
1. Identity Provider (IdP)
The Identity Provider acts as the central authority that verifies user identities. It authenticates users when they attempt to access applications and ensures that identity verification happens consistently across systems.
In Zero Trust environments, the IdP becomes a critical point of policy enforcement. It evaluates authentication requests, verifies identity attributes, and connects users to the appropriate resources in accordance with security policies.
2. Single Sign-On (SSO)
Single Sign-On (SSO) simplifies authentication across multiple applications while maintaining centralized identity control. Instead of requiring users to authenticate separately for each service, SSO allows them to access multiple applications after a single verified login.
In a Zero Trust architecture, SSO also provides visibility into authentication activity. Security teams can monitor login behavior, apply centralized access policies, and reduce credential sprawl across applications.
3. Multi-Factor Authentication (MFA)
Passwords alone are no longer sufficient for protecting sensitive systems. Multi-Factor Authentication (MFA) adds an additional verification step that confirms a user’s identity using something they have or something they are.
Common MFA methods include:
- One-time passcodes (OTP)
- Authentication apps
- Push notifications
- Biometrics
In Zero Trust IAM environments, MFA becomes a baseline control that protects against credential theft and phishing attacks.
4. Privileged Access Management (PAM)
Privileged accounts often represent the most sensitive access within an organization. Privileged Access Management (PAM) ensures that administrative access is granted only when necessary and is closely monitored.
Zero Trust architectures typically enforce:
- Just-in-time privileged access
- Session monitoring
- Automatic privilege expiration
This reduces the risk of attackers abusing elevated permissions.
5. Identity Governance and Administration (IGA)
Identity Governance and Administration (IGA) manages the creation, maintenance, and removal of identities across the organization. It ensures that users receive appropriate access throughout their lifecycle.
Key IGA capabilities include:
- Automated provisioning and deprovisioning
- Role lifecycle management
- Access reviews and certification
- Compliance reporting
These governance controls are essential for maintaining least privilege access in Zero Trust environments.
6. Passwordless Authentication
Many organizations are moving toward passwordless authentication to reduce the risk of credential-based attacks. Instead of relying on passwords, users authenticate through more secure methods such as:
- Passkeys
- Device biometrics
- Hardware security keys
- Mobile authentication apps
Passwordless authentication enhances security and user experience while aligning well with Zero Trust identity models.
7. Risk-Based and Adaptive Authentication
Zero Trust environments often require dynamic access decisions based on risk signals. Adaptive authentication analyzes contextual factors such as:
- Device posture
- Login location
- User behavior
- Network trust
If the system detects unusual activity, it can automatically require additional verification before granting access.
8. API and Application Access Controls
Modern enterprises rely heavily on APIs and interconnected services. Zero Trust IAM architectures extend identity verification beyond human users to include applications and service-to-service interactions.
API access policies ensure that:
- Applications authenticate securely.
- Access tokens are validated.
- Unauthorized services cannot interact with protected systems.
How miniOrange Identity and Access Management Aligns with Zero Trust Architecture?
A unified IAM platform makes it significantly easier to implement these Zero Trust components without deploying disconnected security tools.
Platforms such as miniOrange IAM provide capabilities that support Zero Trust IAM implementation across enterprise environments, including:
- Workforce IAM and Customer IAM (CIAM)
- Single Sign-On across 6000+ applications
- Adaptive multi-factor authentication
- Passwordless authentication
- Device trust enforcement
- Automated user provisioning
- Integration with directories such as Active Directory, LDAP, and cloud identity providers
- Compliance-ready audit logs for governance and reporting
By consolidating these capabilities into a centralized platform, organizations can enforce identity-driven security policies consistently across cloud, on-premises, and hybrid infrastructure.
IAM Cyber Security vs Traditional Security Zero Trust Model
For many years, organizations relied on perimeter-based security models to protect their networks. Firewalls, VPN gateways, and internal network segmentation were designed to keep attackers outside the corporate environment. Once users entered the network, they were generally trusted.
However, modern IT environments have changed dramatically. Applications now live across cloud platforms, SaaS services, APIs, and distributed infrastructure. Employees work remotely, partners access internal systems, and mobile devices connect from different networks.
The traditional perimeter no longer provides adequate protection. This is where IAM cybersecurity within a Zero Trust model becomes essential.
Traditional Perimeter-Based Security
Traditional security models assume that everything within the corporate network is trustworthy. Access decisions are often made once during login, after which users may move freely between systems.
Common characteristics of traditional security include:
- Implicit trust within the internal network
- Single authentication at login
- Static role assignments
- VPN-based access for remote users
- Limited visibility into session activity
While this approach works in centralized environments, it becomes difficult to manage when applications and users are distributed across multiple platforms.
IAM Cybersecurity vs Traditional Security Zero Trust Model
Zero Trust security takes a different approach. Instead of trusting users once they enter the network, every access request must be verified continuously.
In a Zero Trust IAM model, identity signals and contextual data are evaluated before granting access. Security policies can change dynamically depending on risk conditions.
Key characteristics of IAM-driven Zero Trust security include:
- Continuous authentication instead of one-time verification.
- Context-aware authorization policies that consider device health, location, and behavior.
- Micro-segmentation of applications and services.
- Risk-based access decisions that adapt to unusual activity.
- Device posture validation before granting access.
This model ensures that users only access the resources they are authorized to use, and only under trusted conditions.
Traditional IAM vs Zero Trust IAM: Side-by-Side Comparison
| Capability | Traditional IAM | Zero Trust IAM | miniOrange Approach |
|---|---|---|---|
| Authentication | Password-based login | MFA + adaptive authentication | Adaptive MFA and passwordless authentication |
| Access Control | Static role-based permissions | Context-aware policies | RBAC + ABAC + conditional access |
| Privileged Access | Manual privilege assignment | Just-in-time access | PAM with session monitoring |
| Visibility | Limited audit logs | Continuous monitoring | Centralized dashboards and audit logs |
| Security Enforcement | Login-based verification | Continuous identity validation | Adaptive policies across users, devices, and apps |
This comparison highlights how Zero Trust IAM extends traditional identity management by incorporating contextual signals, continuous verification, and dynamic access policies.
Organizations that rely solely on traditional IAM controls may still leave gaps in their security posture. By integrating identity governance, adaptive authentication, and centralized visibility, modern IAM platforms such as miniOrange help organizations move toward a true Zero Trust identity architecture.
Key Benefits of Implementing Zero Trust IAM
Adopting Zero Trust IAM is not only about improving security. It also helps organizations gain better visibility into access activities, simplify identity governance, and create a smoother user experience across applications.
When identity becomes the foundation of security decisions, organizations can enforce consistent access policies while still supporting modern digital workflows.
Here are some key benefits organizations gain from implementing Zero Trust IAM.
1. Reduced Identity-Based Attacks
Many modern cyberattacks target user identities rather than network infrastructure. Phishing campaigns, credential stuffing, and account takeover attempts often rely on stolen or reused passwords.
Zero Trust IAM helps reduce these risks by strengthening identity verification. Multi-factor authentication, passwordless authentication, and adaptive access policies make it significantly harder for attackers to compromise accounts.
Continuous session monitoring also plays an important role. Instead of trusting a login indefinitely, Zero Trust systems can re-evaluate identity signals during the session and respond if suspicious behavior is detected.
2. Stronger Least Privilege Enforcement
The principle of least privilege ensures that users receive only the permissions necessary to perform their tasks. However, managing access manually across many systems can quickly become complex.
Zero Trust IAM platforms automate many of these processes through:
- Automated provisioning and deprovisioning.
- Role-based and attribute-based access controls.
- Access lifecycle management.
These capabilities reduce the risk of privilege sprawl and prevent users from retaining unnecessary access over time.
3. Compliance and Audit Readiness
Regulatory frameworks increasingly require organizations to maintain strict control over how identities access sensitive systems and data.
A centralized IAM platform helps organizations meet these requirements by providing:
- Detailed access logs.
- Centralized audit trails.
- Automated access reviews.
- Policy enforcement aligned with frameworks such as DPDP, HIPAA, GDPR, and SOC2.
By consolidating identity governance into a single system, organizations can demonstrate compliance more easily during audits.
4. Seamless User Experience
Security controls should not create unnecessary friction for users. In fact, modern IAM platforms often improve the user experience while strengthening security.
Capabilities such as Single Sign-On (SSO) allow users to access multiple applications with a single verified login. Passwordless authentication methods remove the need for users to manage complex passwords, while adaptive authentication can reduce verification steps when risk is low.
Additional capabilities, such as identity brokering, two-factor authentication (2FA), adaptive MFA, directory authentication, and lifecycle management, enable organizations to streamline access workflows without compromising security.
IAM solutions like miniOrange combine these features into a unified platform that supports identity-driven security while maintaining a smooth authentication experience across enterprise applications.
Step-by-Step Guide to Implementing Zero Trust IAM
Moving toward a Zero Trust IAM architecture does not happen overnight. Organizations typically adopt the model gradually by strengthening identity controls, centralizing authentication, and introducing context-aware access policies.
The process usually begins with understanding the current identity landscape and then building the necessary controls to enforce continuous verification across users, devices, and applications.
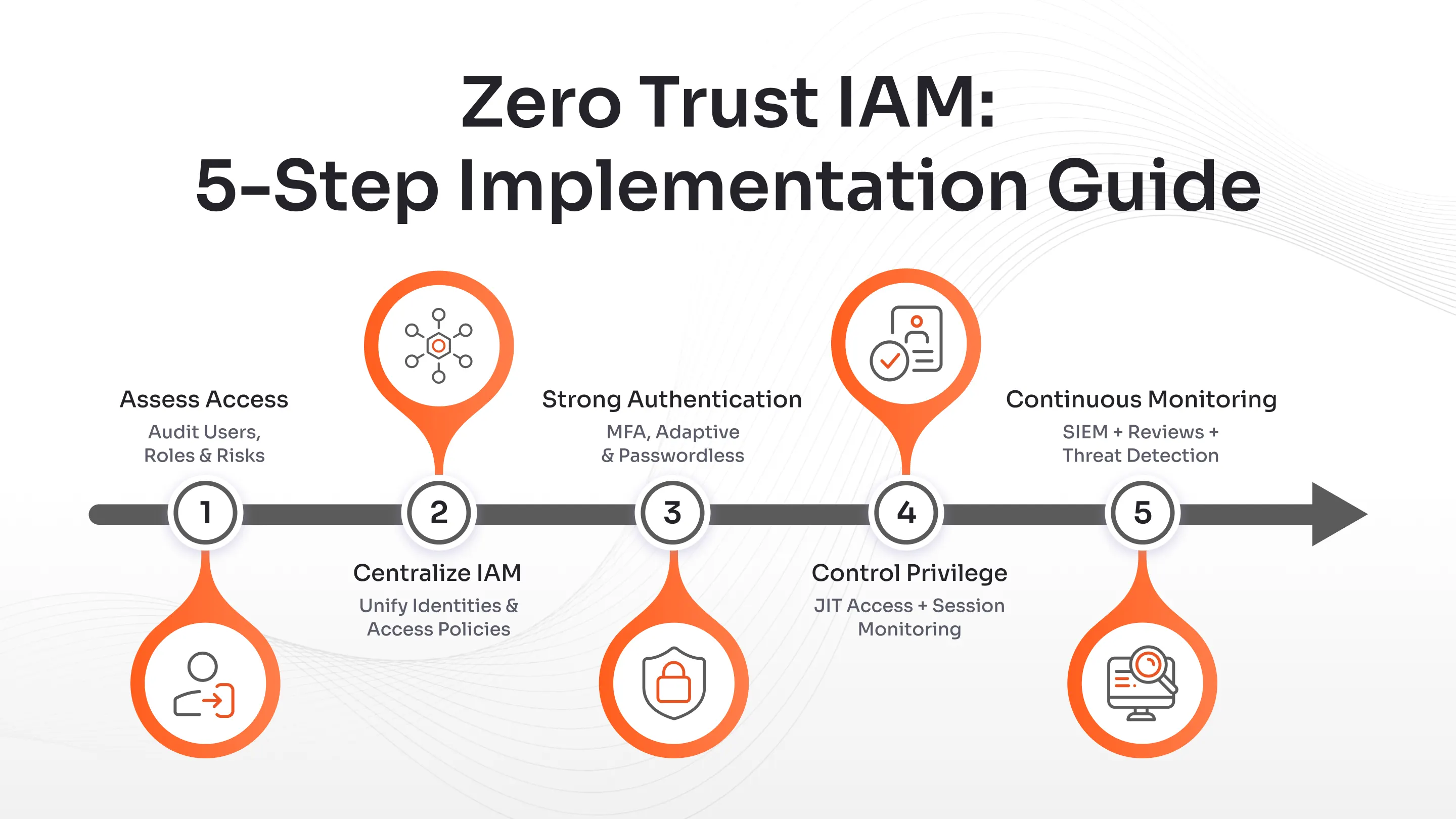
Step 1: Identity and Access Assessment
The first step in implementing Zero Trust IAM is to understand how identities currently interact with your systems.
Organizations should start by auditing:
- user accounts across directories and applications.
- access privileges assigned to employees and third-party users.
- authentication mechanisms currently in place.
- privileged accounts and administrative access.
This assessment helps security teams identify areas where excessive privileges or outdated authentication methods may introduce risk.
Many organizations discover that users accumulate access permissions over time, a phenomenon often referred to as privilege sprawl. Addressing these issues early creates a stronger foundation for Zero Trust policies.
Step 2: Centralize Identity with an IAM Platform
Once identity risks are identified, the next step is to consolidate identity management through a centralized IAM platform.
A unified IAM system allows organizations to:
- Manage identities from a single control plane.
- Integrate directory services such as Active Directory or LDAP.
- Consolidate authentication across applications.
- Apply consistent access policies across environments.
Modern IAM platforms such as miniOrange IAM support both cloud-based and on-premises environments, allowing organizations to centralize identity management without disrupting existing infrastructure.
This centralization is critical because Zero Trust policies rely on consistent identity verification across all systems.
Step 3: Enforce Strong and Adaptive Authentication
Strong authentication controls are essential for preventing unauthorized access. Once identities are centralized, organizations should introduce stronger authentication mechanisms.
This typically includes:
- Rolling out multi-factor authentication (MFA) across critical applications.
- Implementing adaptive authentication policies based on risk signals.
- Introducing passwordless authentication strategies.
Adaptive authentication can analyze contextual signals such as device posture, login location, and user behavior to determine when additional verification is required.
These dynamic controls reduce the risk of credential-based attacks while maintaining a smooth login experience for legitimate users.
Step 4: Implement Privileged Access Controls
Administrative accounts often have the ability to access sensitive systems, modify configurations, or manage other users. These privileges make them attractive targets for attackers.
Zero Trust IAM architectures address this risk through Privileged Access Management (PAM) practices such as:
- Just-In-Time Privilege Elevation.
- Session Monitoring and Recording.
- Automatic Expiration of Elevated Privileges.
By limiting how long privileged access remains active, organizations reduce the potential damage caused by compromised accounts.
Step 5: Enable Continuous Monitoring and Governance
Zero Trust is not a one-time implementation. It requires ongoing monitoring to ensure that access policies remain effective.
Organizations should integrate IAM platforms with security monitoring systems such as SIEM tools to track authentication activity and detect anomalies in real time.
Continuous governance practices may include:
- Automated deprovisioning when users leave the organization.
- Periodic access reviews.
- Real-time alerts for suspicious login behavior.
Modern IAM providers for Zero Trust architectures simplify this process by combining identity governance, authentication controls, and monitoring capabilities within a unified platform.
How to Evaluate IAM Providers for Zero Trust Architectures?
Selecting the right identity platform is one of the most important decisions when implementing a Zero Trust security strategy. Not every IAM solution is designed to support continuous verification, contextual access policies, or identity-driven security architectures.
Organizations should evaluate IAM providers for Zero Trust architectures based on how effectively their platforms enforce identity-centric security across users, devices, and applications.
Below are several key capabilities and evaluation criteria to consider.
Must-Have Capabilities
A modern Zero Trust IAM platform should provide more than basic authentication and user management. Instead, it should support dynamic security controls that adapt to risk signals and evolving access patterns.
Some essential capabilities include:
- Unified identity platform: Organizations should avoid stitching together multiple disconnected security tools. A unified IAM platform allows authentication, authorization, governance, and monitoring to operate within a single control layer.
- Adaptive authentication: Zero Trust environments require authentication mechanisms that adapt to context. Adaptive authentication evaluates factors such as device trust, login location, and behavioral patterns before granting access.
- API-first integrations: Modern enterprises rely heavily on APIs and microservices. IAM platforms should provide secure API integrations that allow identity policies to extend across applications, services, and infrastructure.
- Scalability and performance: IAM systems must support thousands or even millions of users across distributed environments. The platform should scale reliably while maintaining consistent authentication and policy enforcement.
Questions to Ask IAM Providers for Zero Trust Architectures
When evaluating IAM vendors, security teams should ask specific questions to determine whether the platform truly supports Zero Trust principles.
Some important questions include:
- Does the platform support continuous authentication and session validation?
- Can access policies adapt to contextual signals such as device posture, location, or risk level?
- Are privileged access management and identity governance built into the platform?
- Can the IAM system integrate with existing cloud services, on-prem infrastructure, and SaaS applications?
- Does the platform support hybrid environments and multi-directory identity sources?
The answers to these questions often reveal whether a solution is designed for modern identity-first security architectures.
Why a Unified IAM Platform Accelerates Zero Trust Adoption?
Implementing Zero Trust becomes significantly easier when organizations rely on a single platform that consolidates identity services rather than managing separate tools for authentication, governance, and monitoring.
Unified IAM platforms provide several advantages:
- centralized identity visibility
- consistent access policies across environments
- simplified integration with enterprise applications
- reduced operational complexity
Platforms such as miniOrange IAM provide end-to-end identity capabilities across both workforce IAM and customer IAM (CIAM) use cases. With flexible deployment options and built-in security controls, organizations can enforce identity-driven policies across cloud, on-premises, and hybrid environments while maintaining scalability.
By reducing integration overhead and consolidating identity services, unified IAM platforms help organizations operationalize Zero Trust faster and with fewer operational challenges.
Identity-First Security Starts with miniOrange Zero Trust IAM
The shift toward Zero Trust security reflects a broader change in how organizations protect digital environments. Traditional perimeter-based defenses were designed for networks where users, applications, and infrastructure existed within clearly defined boundaries. Modern IT ecosystems are far more distributed, making identity the most reliable point of control.
This is why Zero Trust IAM has become the operational backbone of modern cybersecurity strategies. Instead of relying on network location, organizations can verify every access request based on identity, context, device posture, and risk signals. Continuous verification, least-privilege enforcement, and centralized visibility enable security teams to protect resources more effectively while supporting flexible work environments.
However, implementing Zero Trust requires more than individual security tools. Organizations need an IAM platform that unifies authentication, authorization, identity governance, and adaptive access policies within a single system.
Platforms such as miniOrange IAM help organizations operationalize Zero Trust by providing capabilities such as Single Sign-On, adaptive multi-factor authentication, passwordless authentication, identity lifecycle management, and centralized identity governance across cloud and on-premises environments.
As identity increasingly becomes the new security perimeter, organizations should assess whether their current identity infrastructure can support Zero Trust principles at scale. A strong IAM foundation is essential for enforcing continuous verification and maintaining secure access across modern digital ecosystems.
FAQs
What is Zero Trust?
Zero Trust is a security model based on the principle of “never trust, always verify.” Instead of assuming users or devices inside a network are safe, every access request is verified using identity, device posture, and contextual risk signals before access is granted.
How does Zero Trust security help enforce access restrictions?
Zero Trust security enforces access restrictions by verifying identity and contextual signals before allowing access to applications or data. Policies evaluate factors such as user role, device trust, location, and risk level to ensure only authorized users can access specific resources.
What is least privilege access?
Least privilege access is a security principle where users are given only the minimum permissions required to perform their tasks. By limiting unnecessary access rights, organizations reduce the risk of data exposure, privilege abuse, and insider threats.
How can organizations implement Zero Trust strategies?
Organizations can implement Zero Trust strategies by centralizing identity management, enforcing multi-factor authentication, applying least-privilege access policies, and continuously monitoring user sessions. Deploying an IAM platform that supports adaptive authentication and contextual access controls helps operationalize Zero Trust.
What is just-in-time access?
Just-in-time access is a security approach that grants privileged permissions only for a limited time when they are needed. Once the task is completed, the elevated access is automatically revoked, reducing the risk of privilege misuse or unauthorized activity.



Leave a Comment