AI agents are rapidly becoming active participants across enterprise systems. They interact with APIs, trigger workflows, query data sources, and make decisions without human intervention. From AI copilots embedded in applications to autonomous agents managing cloud operations, these non-human identities are now a core part of modern infrastructure.
This shift introduces a critical challenge. Traditional authentication models were designed for human users who log in occasionally. AI agents operate continuously and programmatically, often across multiple systems at once.
Authentication becomes the first and most important control in securing these interactions.
What Is AI Agent Authentication?
AI agent authentication is the process of verifying the identity of an autonomous system before granting it access to resources, APIs, or services. It ensures that every request made by an AI agent can be trusted and evaluated against defined access policies.
Unlike human authentication, which often relies on passwords or multi-factor verification, AI agent authentication is entirely programmatic. The process is handled through protocols and identity systems that validate requests without human involvement.
What makes this more complex is the frequency and nature of interactions. AI agents do not authenticate once per session. They authenticate continuously. Every API call or system interaction may require validation, which means authentication must be efficient, scalable, and consistent.
Another important aspect is identity granularity. Each AI agent must have a unique identity so that actions can be traced back accurately. This enables better monitoring, auditing, and enforcement of least-privilege access.
At its core, AI agent authentication is about maintaining trust in a system where access decisions are made automatically and at scale.
Why Traditional API Key Authentication Falls Short
Long-Lived Credentials Increase Security Risk
API keys are typically static and remain valid for long periods unless manually rotated. This extended lifespan creates a larger window of exposure. If a key is compromised, it can be reused repeatedly without detection, allowing unauthorized access to persist until the key is explicitly revoked.
Hardcoded and Poorly Managed Secrets
API keys are often embedded directly into application code or stored in configuration files. This makes them difficult to secure and increases the likelihood of accidental exposure. Keys can leak through version control systems, logs, or misconfigured environments, making them an easy target for attackers.
Lack of Identity Context and Visibility
API keys authenticate access but do not represent a distinct identity. They do not indicate which AI agent or service is making a request. This lack of context makes it difficult to monitor behavior, trace actions, or investigate anomalies within the system.
Limited Access Control and Flexibility
API keys provide minimal control over how access is granted. They do not support fine-grained permissions or context-aware decisions. This means organizations cannot easily restrict access based on specific actions, roles, or conditions, leading to overly broad access.
Difficult Rotation and Operational Challenges
Managing API keys at scale becomes increasingly complex as the number of systems grows. Rotating or revoking keys often requires coordination across multiple services, which can lead to disruptions. When keys are shared across systems, even a single change can impact several workflows.
Risks of Poor AI Agent Authentication
Weak authentication mechanisms can expose organizations to multiple risks, especially when AI agents operate at scale.
- Unauthorized access: Compromised credentials allow attackers to impersonate AI agents
- Credential leakage: Hardcoded or reused credentials can be exposed through logs or code
- Lack of traceability: Without identity-based access, tracking actions becomes difficult
- Expanded attack surface: Shared credentials increase the impact of a breach
- Compliance challenges: Weak authentication fails to meet regulatory requirements
These risks highlight the need for stronger, identity-driven authentication methods.
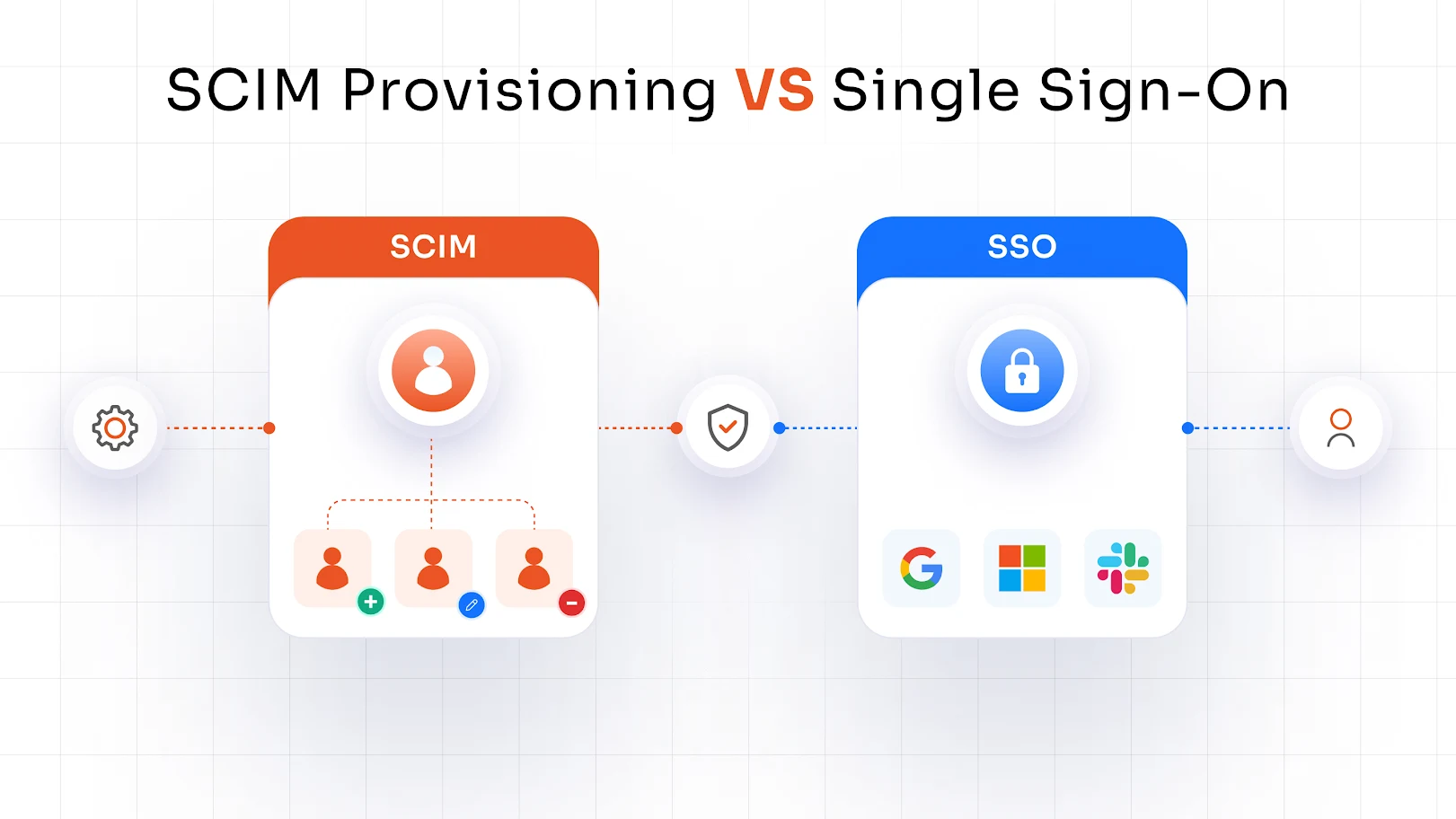
AI Agent Authentication Methods
Modern AI environments require authentication methods that go beyond static credentials. As AI agents operate continuously and interact across multiple systems, authentication must be dynamic, identity-driven, and scalable. The most commonly used approaches include token-based authentication, mutual TLS (mTLS), and short-lived credentials.
Token-Based Authentication (OAuth, JWTs)
Token-based authentication is one of the most widely adopted methods for securing AI agents, especially in API-driven environments. In this model, an AI agent first authenticates with an identity provider, which then issues a short-lived access token. This token is included in subsequent requests to access resources.
These tokens often carry embedded information such as the identity of the agent, its permissions, and the validity period. This allows systems to evaluate not just whether access should be granted, but also what level of access is appropriate.
Benefits:
- Time-bound access reduces the risk associated with long-lived credentials
- Scales effectively across APIs and distributed systems
- Supports fine-grained authorization through scopes and claims
- Improves visibility by linking requests to specific identities
Tradeoffs:
- Requires lifecycle management for issuance, validation, and expiration
- Token refresh and revocation mechanisms must be handled properly
- Integration with legacy systems can require additional effort
Mutual TLS (mTLS) Authentication
Mutual TLS strengthens authentication by requiring both the client and the server to verify each other’s identity using digital certificates. Unlike standard TLS, which only validates the server, mTLS ensures that both sides of the communication are trusted before any data is exchanged.
This creates a strong cryptographic trust model where identities are tied to certificates rather than shared secrets, making impersonation significantly more difficult.
Benefits:
- Provides strong identity verification through certificates
- Ensures encrypted communication by default
- Reduces risk of credential theft or reuse
- Ideal for securing internal service-to-service communication
Tradeoffs:
- Requires infrastructure for certificate issuance and management
- Rotation and revocation processes must be maintained
- Operational complexity increases as the number of services grows
Short-Lived Credentials
Short-lived credentials are designed to limit how long access remains valid. Instead of relying on static credentials, systems generate temporary credentials that expire after a short duration or session. These credentials are often issued dynamically based on context.
This approach is commonly used in environments where access patterns change frequently and security requirements are high.
Benefits:
- Minimizes exposure window if credentials are compromised
- Reduces reliance on long-term stored secrets
- Supports dynamic and context-aware access control
- Aligns with modern Zero Trust security principles
Tradeoffs:
- Requires reliable infrastructure for real-time credential issuance
- Dependency on identity provider availability
- Can introduce latency if not implemented efficiently
Tokens vs Certificates vs API Keys: A Practical Comparison
Each authentication method offers different levels of security, control, scalability, and operational complexity. Understanding these differences helps in choosing the right approach based on use case, risk level, and system maturity.
| Factor | API Keys | Tokens (OAuth/JWT) | Certificates (mTLS) |
|---|---|---|---|
| Security Strength | Basic security, relies on the secrecy of the key | Strong security with signed tokens and validation | Very strong security using cryptographic identity verification |
| Credential Lifespan | Long-lived and often static | Short-lived with expiration and refresh cycles | Medium to long-lived but rotated on a defined schedule |
| Identity Context | No identity context, represents access only | Rich context including user/agent identity and permissions | Strong identity binding to a specific service or workload |
| Access Control | All-or-nothing access in most cases | Fine-grained access using scopes and claims | Access controlled through certificate trust and policies |
| Revocation | Manual and disruptive, it often affects multiple systems | Dynamic revocation possible via token expiry or blacklisting | Managed through certificate revocation lists or rotation |
| Credential Exposure Risk | High due to reuse and long lifespan | Lower due to short validity and scoped access | Very low, as private keys are not transmitted |
| Scalability | Difficult to manage as systems grow | Highly scalable across distributed systems and APIs | Scalable with proper certificate management infrastructure |
| Operational Complexity | Low initial setup, minimal infrastructure | Moderate, requires token services and validation logic | High, requires certificate issuance, rotation, and trust management |
| Auditability & Monitoring | Limited visibility into usage | High visibility with identity-linked requests | Strong traceability tied to certificate identity |
| Best Use Cases | Legacy systems, simple integrations | API ecosystems, SaaS integrations, AI workflows | Internal services, zero-trust environments, high-security systems |
Engineering Tradeoffs: Security vs Complexity
Organizations often need to balance ease of implementation with long-term security. Simpler authentication methods are faster to deploy, but they can introduce risks that become harder to manage as systems grow.
Why Simpler Methods Still Exist
API keys and other basic authentication approaches are still widely used because they are easy to implement and require minimal setup. Development teams can integrate them quickly without needing complex identity systems. This makes them appealing for early-stage projects or low-risk use cases, even though they do not scale well.
The Hidden Cost of Simplicity
While simple methods reduce initial effort, they often create long-term challenges. Limited visibility, weak access control, and manual management increase the risk of breaches and operational issues. As AI agents scale across systems, these limitations become more difficult to manage and can lead to security gaps.
Key Factors That Influence the Decision
The right authentication approach depends on several factors. The number of AI agents in use determines how scalable the solution needs to be. The sensitivity of the data being accessed defines the level of security required. Compliance requirements may mandate stronger identity controls, and the organization’s technical maturity affects how easily advanced methods can be implemented.
Scaling Security with AI Growth
As AI adoption increases, authentication needs to evolve alongside it. What works for a small deployment may not work at scale. Investing in stronger authentication methods early helps organizations maintain control, reduce risk, and avoid costly transitions later.
Real-World Use Cases of AI Agent Authentication
AI agent authentication is not limited to a single use case. It plays a critical role across different environments where AI systems interact with data and services. Each use case requires a level of security that aligns with the sensitivity and complexity of the task.
AI Copilots in Enterprise Systems
AI copilots often access enterprise tools such as customer relationship platforms, internal dashboards, or knowledge bases. These systems contain sensitive information, which means authentication must ensure that access is both secure and limited to what the agent actually needs to perform its task.
Autonomous Workflows and Automation
AI agents are increasingly used to automate workflows such as provisioning infrastructure, processing transactions, or triggering business processes. Authentication ensures that these actions are executed by trusted entities and within predefined boundaries, preventing unauthorized or unintended operations.
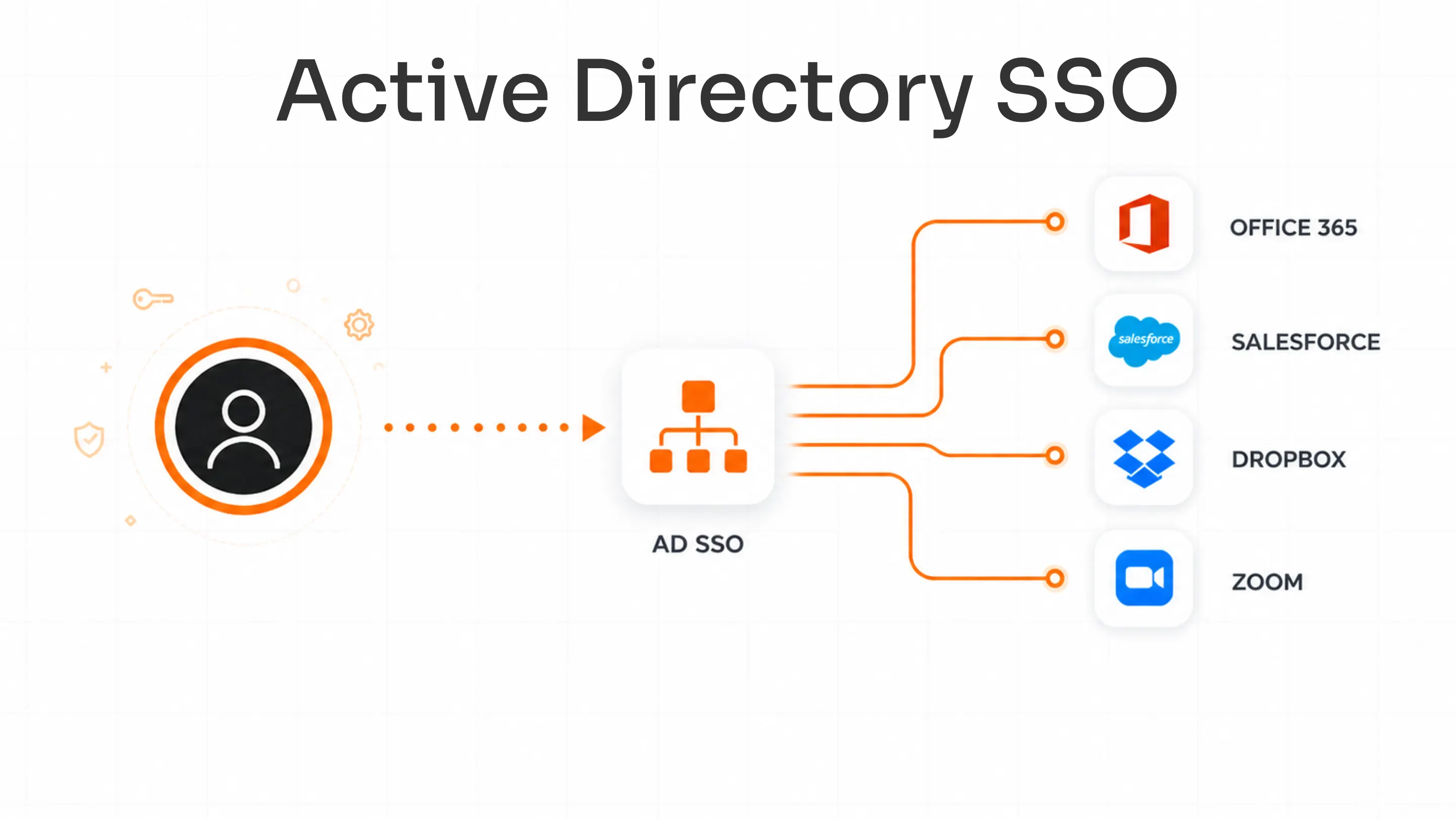
SaaS and Multi-System Integrations
In many environments, AI agents connect multiple SaaS applications to enable data exchange and workflow automation. Secure authentication enables seamless integration while maintaining control over access permissions across different platforms.
Internal AI Systems and Microservices
Within internal environments, AI-powered services often communicate with each other. These interactions require strong authentication methods such as mTLS or short-lived credentials to ensure that only trusted services can exchange data and perform operations.
How to Implement Secure AI Agent Authentication
Implementing secure authentication requires a structured approach that focuses on identity, control, and continuous validation. Organizations need to ensure that authentication is not only secure but also scalable and manageable.
Assign Unique Identities to AI Agents
The first step is to ensure that each AI agent has its own identity. Shared credentials should be avoided because they limit visibility and control. Unique identities allow organizations to track behavior, enforce policies, and respond to incidents more effectively.
Choose the Right Authentication Method
Selecting the appropriate authentication method depends on the use case. Token-based authentication is commonly used for APIs and external systems, while mTLS is better suited for internal communication. In many cases, a combination of methods provides the best balance of security and flexibility.
Eliminate Long-Lived Credentials
Replacing static API keys with short-lived tokens or temporary credentials is a critical step. This reduces the exposure window and limits the impact of credential compromise. It also aligns with modern security practices that focus on minimizing trust.
Ensure Consistent Validation Across Systems
All services and APIs should validate credentials consistently. This ensures that access policies are enforced uniformly and prevents gaps in security where certain systems may bypass authentication checks.
Enable Monitoring
Monitoring authentication activity provides visibility into how systems are being accessed. Automation plays a key role in managing credential lifecycles, including rotation, expiration, and revocation. This reduces manual effort and helps maintain a strong security posture over time.
AI Authentication Best Practices
Maintaining secure AI environments requires a consistent set of best practices that focus on reducing risk while supporting scalability. These practices help ensure that authentication remains effective as systems grow.
Use Short-Lived and Dynamic Credentials
Short-lived credentials reduce the risk associated with long-term exposure. By limiting how long access remains valid, organizations can minimize the impact of credential compromise and maintain tighter control over system access.
Avoid Hardcoding Secrets in Code
Storing credentials in code or configuration files increases the risk of accidental exposure. Instead, secrets should be managed through secure storage mechanisms and accessed dynamically when needed.
Automate Credential Rotation
Manual credential management is not sustainable at scale. Automating rotation and expiration ensures that credentials remain up to date without introducing operational overhead or security gaps.
Apply Least-Privilege Access Controls
AI agents should only have access to the resources they need to perform their tasks. Limiting permissions reduces the potential impact of misuse or compromise and helps maintain better control over system interactions.
Monitor, Audit, and Adopt Zero Trust Principles
Continuous monitoring of authentication activity helps detect unusual behavior and respond to threats quickly. Adopting a Zero Trust approach ensures that every request is verified, regardless of its origin, reinforcing a strong and consistent security model.
How IAM Enables Secure AI Agent Authentication
Identity and Access Management systems provide the foundation for managing AI agent authentication at scale. They allow organizations to assign identities, issue credentials, and enforce access policies consistently.
IAM systems also provide centralized visibility into authentication activity. This helps detect anomalies, support audits, and ensure compliance.
By managing both human and non-human identities, IAM platforms enable organizations to maintain control as their environments grow more complex.
The Future of AI Agent Authentication
Authentication is evolving alongside AI technologies. Organizations are moving toward identity-first security models where access decisions are based on verified identity rather than static credentials.
Short-lived credentials and dynamic access controls are becoming more common. Automation is playing a larger role in managing credential lifecycles and enforcing policies.
As AI adoption continues to grow, authentication will remain a critical component of securing these systems.
FAQs
What is the most secure authentication method for AI agents?
A combination of certificate-based authentication and short-lived credentials provides strong security.
Are API keys suitable for AI systems?
They are not recommended due to their long lifespan and lack of identity context.
How do AI agents authenticate with APIs?
They typically use token-based authentication or certificate-based methods, depending on the environment.
What is the difference between tokens and mTLS?
Tokens provide flexible access control with defined permissions, while mTLS ensures strong identity verification between systems.
Leave a Comment