Many enterprises still rely on manual provisioning, which quietly introduces security gaps, compliance risks, and operational inefficiencies. This can be resolved by understanding SCIM vs. SSO, which solves different identity security problems. SSO handles authentication, while SCIM handles user provisioning. You need both to build a secure and scalable identity system.
In this guide, we will break down SCIM provisioning vs. SSO, explain how each works, highlight their differences, and show how they work together to secure modern enterprises.
The Identity Problem in Growing Enterprises (Why This Matters)
Modern organizations run on SaaS. Tools like AWS, GitHub, Jira, Slack, and Salesforce are essential to daily operations. But each tool introduces its own access layer.
Without automation, managing access becomes chaotic.
Common challenges include:
- Manual onboarding and offboarding across systems.
- Inconsistent permissions based on outdated roles.
- Lack of visibility into who has access to what.
This leads to real risks:
- Orphaned accounts that remain active after employees leave.
- Overprovisioned users with more access than needed.
- Delays in granting or revoking access.
Identity has effectively become the largest attack surface in most enterprises. Attackers often exploit weak access controls rather than system vulnerabilities.
What is Single Sign-On (SSO)?
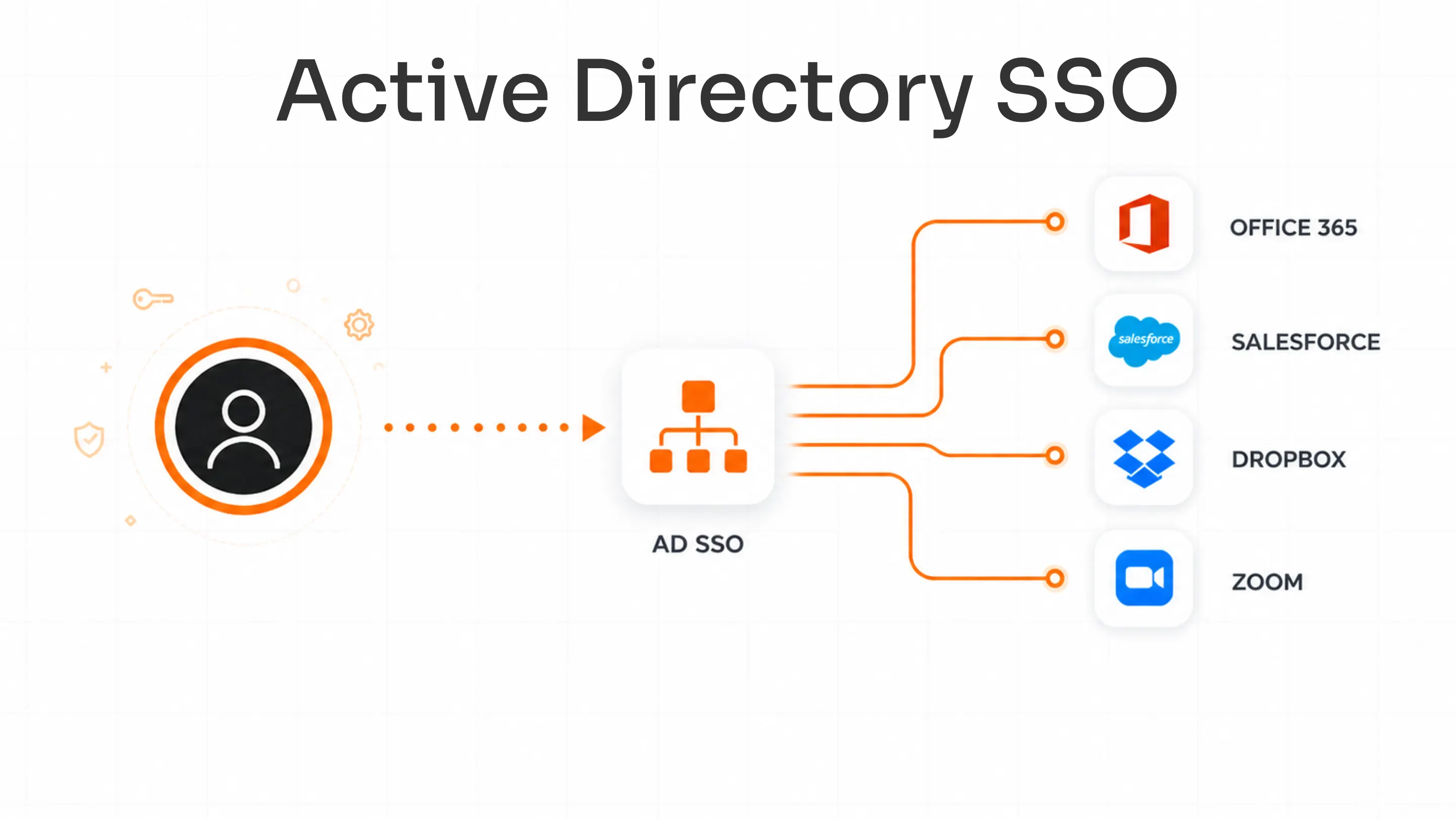
Single Sign-On (SSO) is an authentication mechanism that allows users to log in once and access multiple applications without re-entering credentials.
Here’s how SSO works:
- A user attempts to access an application.
- The application redirects the user to an Identity Provider (IdP) like Okta, Azure AD, or Google Workspace.
- The IdP authenticates the user.
- A token is issued.
- The user gains access to the application.
Common SSO protocols include Security Assertion Markup Language (SAML), OAuth, and OpenID Connect (OIDC).
There are comparisons like SCIM vs. SAML. Here, SAML is part of SSO authentication, while SCIM is unrelated to login and instead focuses on provisioning.
Why enterprises use SSO:
- One login for multiple applications
- Reduced password fatigue
- Centralized authentication policies
- Better user experience
SSO also has its own limitations, which are:
- Create user accounts in applications
- Remove users when they leave
- Update roles or permissions
The job of the SSO solution is only to verify identity at login. It does not manage the lifecycle of that identity.
What is SCIM Provisioning?
To understand SCIM provisioning vs. SSO, we need to define SCIM clearly.
SCIM stands for System for Cross-domain Identity Management. It is a standard for automating user provisioning and deprovisioning across systems.
If SSO answers "Who are you?", then SCIM provisioning answers "Should you exist in this system, and what access should you have?"
SCIM provisioning is the automated process of:
- Creating user accounts when someone new joins.
- Updated user roles and attributes when the role or department changes.
- Deleting accounts when someone leaves.
This entire process is referred to as user provisioning or lifecycle management.
The essential lifecycle stages (JML) are as follows, which means:
- Joiner: New employee gets accounts across tools.
- Mover: Role change updates permissions.
- Leaver: Access is revoked across all systems.
Here’s how SCIM works (giving a simplified overview):
- A source system, like HR software or an IdP, triggers a change.
- That change is sent via SCIM APIs to connected applications.
- Applications update user data automatically.
Why SCIM matters for enterprises:
- Eliminates manual provisioning tasks.
- Keeps user data consistent across systems.
- Reduces security risks from outdated access.
SCIM is sometimes misunderstood. SCIM does not authenticate users. It only manages the user lifecycle.
SCIM Provisioning vs. SSO: Key Differences Explained
Here is a clear comparison of SCIM vs. SSO:
| Feature | SSO | SCIM Provisioning |
|---|---|---|
| Purpose | Authentication | User provisioning |
| Function | Verifies identity during login | Creates, updates, and deletes user accounts |
| Protocols | SAML, OAuth, OIDC | REST APIs with standardized schemas |
| Security Role | Prevents password sprawl | Prevents orphaned accounts and overprovisioning |
| Timing | Used during logins | Works continuously in the background |
| Automation | Low | High |
| Dependency | Exists without SCIM | SCIM enhances SSO, but doesn’t replace it |
Why SSO Alone is Not Enough for Enterprise Security
SSO significantly strengthens enterprise security, but it only solves part of the identity problem. It centralizes authentication, reduces password fatigue, and improves visibility into who is logging in, yet it still leaves major gaps around what users can access, for how long, and in which systems. Also, with SSO, compromised credentials can still grant access. Adding Multi-Factor Authentication (MFA) strengthens identity verification.
Even with SSO in place, many SaaS apps and legacy tools remain outside its control, and SSO does not handle user lifecycle events like onboarding, role changes, or offboarding.
Without something like SCIM-based user provisioning to complement it, organizations are still exposed to risks such as orphaned accounts, stale access, and overprivileged users. In practice, that means you may know who is logging in via SSO, but you cannot reliably ensure they have the right level of access everywhere.
This is why SSO alone is not enough for enterprise security: it is a powerful front door, but it needs automated provisioning, deprovisioning, and strong verification layered around it to actually reduce your attack surface.
How SCIM and SSO Work Together

The real value comes from combining SCIM provisioning vs. SSO into a unified system.
Think of it this way: SSO verifies identity at login. SCIM ensures the right identities exist and removes them when they should not.
A typical lifecycle looks like this:
- A new employee has been added to the HR system.
- SCIM provisions accounts across applications.
- The employee logs in using SSO.
- If their role changes, SCIM updates permissions automatically.
- When they leave, SCIM deprovisions access across all systems.
This creates a closed-loop identity system where access is always accurate and up to date.
Real-World Use Cases of SCIM + SSO
- SaaS Onboarding at Scale: SCIM provisioning automates user provisioning across multiple SaaS tools, ensuring new hires get instant access without manual setup. SSO then allows login across these apps, improving productivity and reducing IT workload.
- Employee Lifecycle Automation: SCIM keeps user provisioning aligned with HR systems, automatically creating, updating, or removing access as roles change. SSO ensures employees can securely access everything they need with a single login.
- Mergers and Acquisitions: During M&A, SCIM provisioning helps unify user provisioning across different organizations quickly and consistently. SSO simplifies access by enabling users from both entities to log in through a centralized identity system.
- Remote Workforce Management: SCIM ensures remote employees are provisioned with the right access from day one and deprovisioned instantly when needed. SSO provides secure, easy access to company systems from any location without password fatigue.
- Zero Trust Architecture: SCIM supports continuous user provisioning based on identity and role changes, ensuring access is always appropriate. SSO, combined with MFA, verifies identity at every login, reinforcing a Zero Trust security model.
Compliance and Security Benefits
SCIM provisioning, when combined with SSO, enables organizations to meet key compliance frameworks such as GDPR, HIPAA, PCI DSS, SAMA, and more with greater efficiency and accuracy.
Automated user provisioning reduces human error by ensuring access is granted and revoked based on real-time role changes. Detailed, audit-ready logs track every provisioning event, making it easier to demonstrate control and accountability during audits.
This setup also enforces least privilege access consistently, limiting users to only what they need. As a result, audits become faster and less stressful, and compliance shifts from a manual effort to a natural outcome of strong identity management practices.
Best Practices for Implementing SCIM Provisioning and SSO
To get the most out of SCIM provisioning vs. SSO, follow these practices:
- Use HR systems as the source of truth for identity data.
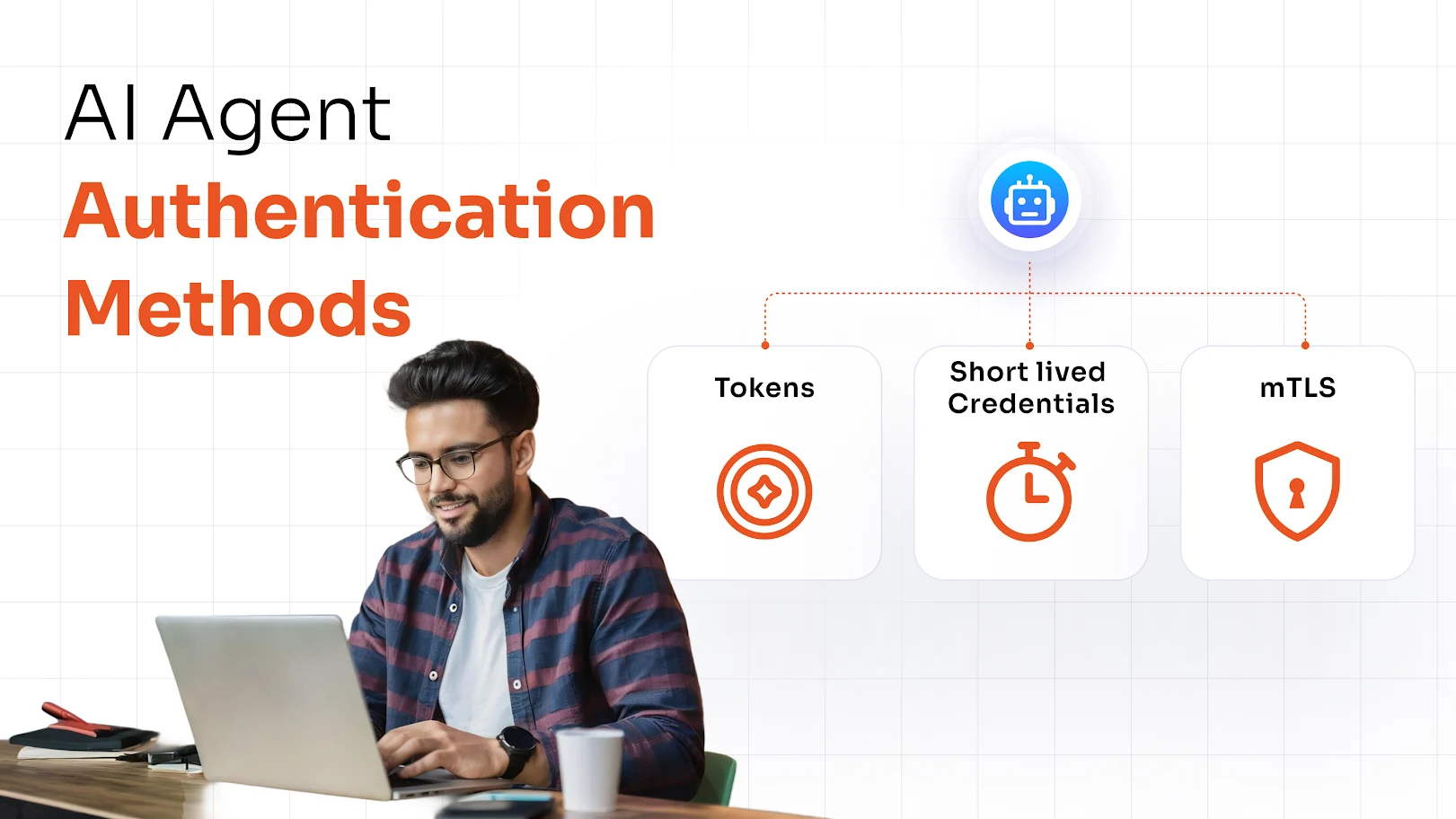
- Enforce MFA alongside SSO for stronger authentication.
- Implement role-based access control to standardize permissions.
- Conduct regular access reviews to catch anomalies.
- Monitor provisioning logs to detect issues early.
These steps ensure your identity system remains secure and scalable.
How to Choose the Right SCIM Provisioning and SSO Solution
Not all solutions are equal.
Look for:
- SCIM provisioning support across applications.
- SSO integration with major identity providers.
- Built-in MFA enforcement capabilities.
- Scalability to support organizational growth.
- Compliance readiness with audit features.
Choosing the right platform can significantly reduce implementation complexity.
miniOrange offers a complete IAM suite to meet your security needs. Connect with our experts for a demo.
FAQs
What is the difference between SCIM and SSO?
SSO is used for authentication and allows users to log in to multiple applications with one set of credentials. SCIM is used for user provisioning and automates the creation, updating, and removal of user accounts across systems.
Is SCIM used for authentication?
No, SCIM does not handle authentication. It manages identity data and user lifecycle processes.
Do you need both SCIM and SSO?
Yes, SSO simplifies login and improves user experience, while SCIM ensures access is correctly provisioned and removed. Using both together provides complete identity management.
What is SCIM provisioning?
SCIM provisioning is the automated process of managing user accounts across systems, including creating new users, updating roles, and deprovisioning access when users leave.
Leave a Comment