Every device that connects to your network carries risk.
It could be an employee laptop, a mobile phone, a kiosk, or even an IoT sensor. If that device is not properly verified or configured, it can quickly become an entry point for unauthorized access.
That’s where things start to break.
Most organizations don’t struggle with managing devices. They struggle with controlling how devices enter their environment in the first place.
How do you make sure every device is trusted, secure, and ready to use from day one?
This is where device provisioning comes in. It allows organizations to onboard devices in a structured way, ensuring they are authenticated, configured, and aligned with security policies before they get access.
In this blog, we will break down what device provisioning is, how it works, its types, key challenges, and best practices to help you build a secure and scalable device environment.
What is Device Provisioning?
Device provisioning is the process of setting up a device so it can securely connect to a network or system. It includes registering the device, verifying its identity, applying configurations, and assigning the right access permissions.
The goal is to ensure that every device is trusted and properly configured before it is used. This applies to all types of devices, including laptops, smartphones, and IoT devices.
In simple terms, device provisioning determines whether a device is trusted, what access it should have, and how it should be configured.
Without proper provisioning, devices enter the environment without control or visibility. This increases the risk of unauthorized access, misconfigurations, and security breaches.
Why Device Provisioning is Important?
As organizations grow, the number of devices connecting to systems increases rapidly. Managing these devices manually is not only time-consuming but also introduces security risks and inconsistencies.
Device provisioning brings structure and control to this process by ensuring that every device is properly verified and configured before it is used. Here’s why it matters:
1. Ensures Secure Device Onboarding
Device provisioning makes sure that every device is authenticated and configured before it gets access. This reduces the chances of unverified or misconfigured devices connecting to systems. It also ensures that security policies are applied from the start.
2. Prevents Unauthorized or Rogue Device Access
Only approved and trusted devices are allowed to connect. This helps organizations maintain control and prevents unknown or malicious devices from accessing critical resources. It also reduces the risk of internal and external threats.
3. Reduces Manual IT Effort
Provisioning automates the setup process, eliminating the need for repetitive manual tasks. IT teams can onboard devices faster without handling each one individually. This also minimizes the chances of human errors during setup.
4. Enables Scalability for Enterprise and IoT Deployments
As device volumes increase, manual processes become difficult to manage. Provisioning ensures that devices are set up consistently, whether it is a small batch or thousands of devices. This makes it easier to scale operations without losing control.
5. Supports Compliance and Audit Readiness
Provisioned devices follow predefined security and configuration policies. This makes it easier to meet compliance requirements and maintain proper audit trails. Organizations can also track how devices are configured and used over time.
How Device Provisioning Works?
Device provisioning follows a structured process that ensures every device is securely set up before it connects to a network or system. Instead of relying on manual steps, it standardizes how devices are verified, configured, and assigned access.
Here’s how device provisioning works:
1. Device Registration
The process starts by identifying and registering the device within the system. This includes capturing details such as serial numbers, hardware identifiers, or unique device IDs. Registration ensures that the system is aware of the device before any access is granted. It acts as the first step in establishing visibility and control.
2. Authentication and Trust Establishment
Once registered, the device must prove its identity. This is done using authentication methods such as certificates, tokens, or hardware-backed identities. The goal is to confirm that the device is legitimate and not impersonating another device. Establishing trust at this stage is critical to prevent unauthorized access.
3. Configuration and Policy Assignment
After authentication, the device is configured based on predefined settings and security policies. This may include network configurations, security controls, application installations, and access restrictions. These configurations ensure that every device follows the same security standards. It also reduces inconsistencies that can arise from manual setup.
4. User or System Assignment
The device is then linked to a specific user, role, or system. This determines what resources the device can access and how it will be used. For example, an employee device may have broader access compared to a kiosk or shared device. This step helps align device access with business needs and responsibilities.
5. Ongoing Management
Device provisioning does not end after initial setup. Devices must be continuously monitored and updated to maintain security. This includes applying patches, enforcing policies, and checking compliance. Ongoing management ensures that devices remain secure throughout their user lifecycle.
Types of Device Provisioning:
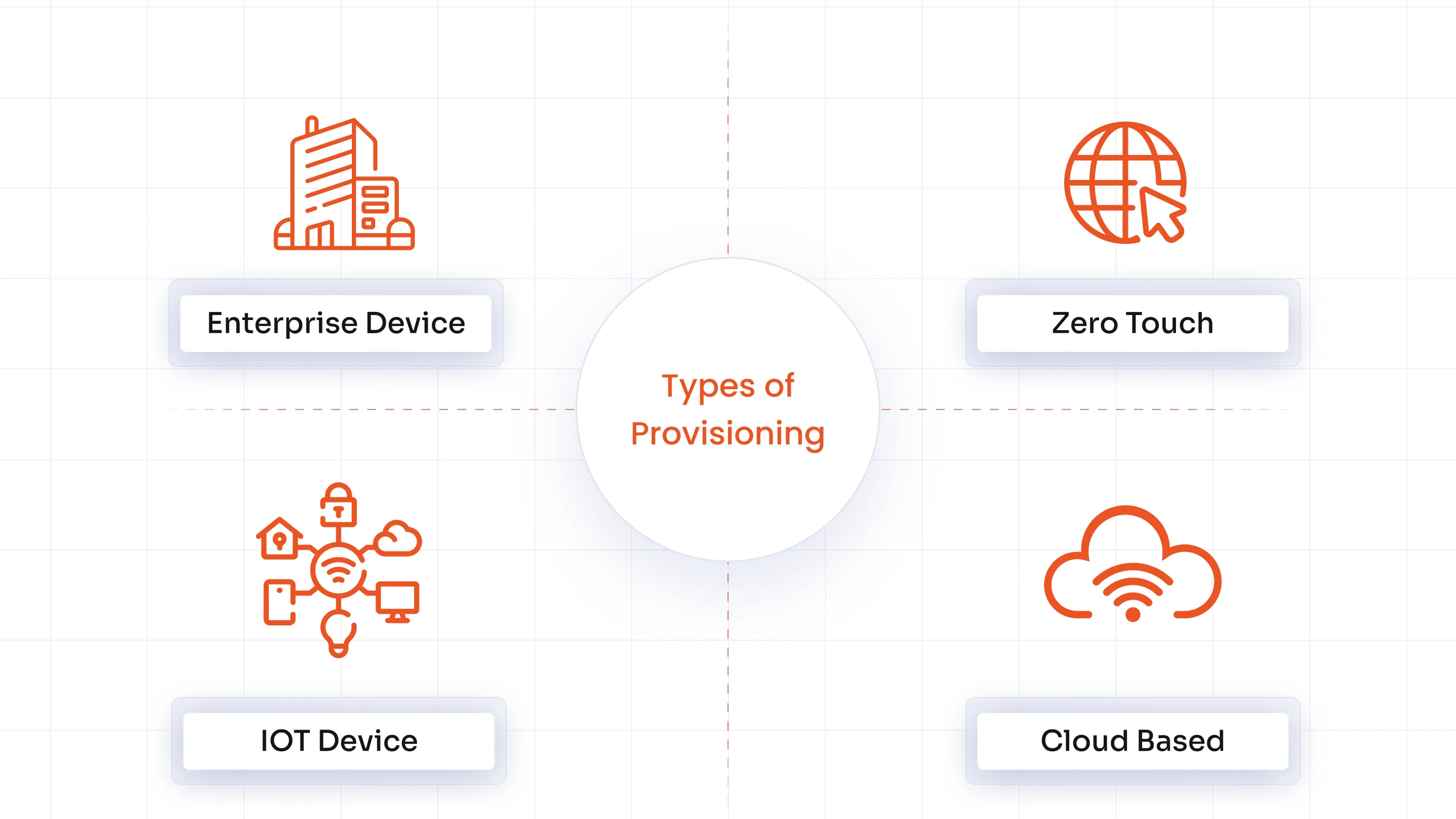
Device provisioning is not a one-size-fits-all process. The approach can vary depending on the type of devices, scale of deployment, and how systems are managed.
Choosing the right provisioning method helps organizations maintain consistency, improve security, and simplify device onboarding. Here are some of the key types of device provisioning:
1. Enterprise Device Provisioning: Enterprise device provisioning is used to onboard employee devices such as laptops, desktops, and mobile phones. It ensures that devices are pre-configured with company policies, applications, and security settings before use. This helps maintain consistency across devices and reduces setup time for employees.
2. Zero-Touch Provisioning: Zero-touch provisioning allows devices to be automatically configured as soon as they are powered on and connected to the internet. There is no need for manual setup by IT teams or end users. This approach is ideal for large-scale deployments where devices need to be rolled out quickly and consistently.
3. IoT Device Provisioning: IoT device provisioning is designed for onboarding connected devices such as sensors, smart devices, and industrial systems. It focuses on securely assigning identities and authenticating devices at scale. Since IoT environments often involve a large number of devices, strong security and automation are essential.
4. Cloud-Based Provisioning: Cloud-based provisioning enables devices to be configured and managed remotely through cloud platforms. This allows IT teams to set up devices without needing physical access. It is especially useful for distributed teams, remote workers, and organizations operating across multiple locations.
Device Provisioning vs Device Management: Key Differences Explained
Device provisioning and device management are closely related, but they serve different roles in the device lifecycle. While both are essential for maintaining security and control, they operate at different stages.
Understanding the difference helps organizations build a more complete and effective device strategy.
| Aspect | Device Provisioning | Device Management |
|---|---|---|
| Purpose | Prepares devices for use | Maintains and secures devices over time |
| Stage | Initial setup and onboarding | Ongoing operations and control |
| Focus | Registering, authenticating, and configuring devices | Monitoring, updating, and enforcing policies |
| Identity & Trust | Establishes device identity and trust | Ensures devices remain compliant and secure |
| Timing | One-time or event-driven process | Continuous and ongoing process |
| Activities | Enrollment, configuration, access setup | Patch management, monitoring, policy enforcement |
| Outcome | Device is ready for use | Device remains secure and compliant |
Device provisioning focuses on preparing a device before it is used. It ensures that the device is registered, authenticated, configured, and assigned the right access. This step establishes trust and ensures that only approved devices can connect to systems.
Device management, on the other hand, begins after provisioning is complete. It involves continuously monitoring devices, applying updates, enforcing security policies, and maintaining compliance over time. This ensures that devices remain secure throughout their lifecycle.
In simple terms, provisioning gets the device ready, while management ensures it stays secure and compliant as it continues to be used.
Common Use Cases of Device Provisioning
Device provisioning is used wherever devices need to be onboarded quickly, securely, and consistently. It helps organizations reduce setup time, maintain control, and ensure that every device meets security and configuration standards from the start.
Here are some of the key use cases of device provisioning:
Employee Laptop Onboarding
When new employees join, their devices need to be ready from day one. User Provisioning ensures that laptops are pre-configured with required applications, security settings, and access permissions. This reduces setup time and allows employees to start working without delays.
Mobile Device Enrollment (BYOD and COPE)
Organizations often support both personal and corporate-owned devices. Provisioning helps securely onboard these devices while ensuring that business data remains protected. It also allows organizations to apply policies without affecting personal usage.
Secure IoT Deployments
IoT environments involve a large number of connected devices that need to be managed securely. Provisioning assigns unique identities and credentials to each device, ensuring only trusted devices can connect. This reduces the risk of unauthorized access and device impersonation.
Retail Kiosks and POS Systems
Devices used in retail, such as kiosks and POS systems, are typically designed for specific tasks. Provisioning ensures these devices are locked down and configured for limited use. This prevents misuse and keeps operations running smoothly.
Mergers and Acquisitions Device Integration
During mergers or acquisitions, integrating devices from different organizations can be challenging. Provisioning helps standardize configurations and security policies across all devices. This ensures a smooth transition without introducing security gaps.
Security Challenges in Device Provisioning
Device provisioning plays a key role in securing how devices connect to systems. However, if it is not implemented correctly, it can introduce gaps that attackers can exploit.
These challenges often arise from weak controls, inconsistent processes, or lack of visibility across devices. Here are some of the key security challenges in device provisioning:
Device Spoofing and Impersonation
Attackers may attempt to mimic legitimate devices to gain unauthorized access. If device identity is not strongly verified, it becomes easier to bypass security controls. This is especially risky in large-scale environments where many devices are being onboarded. Without strong identity validation, it becomes difficult to distinguish between trusted and malicious devices.
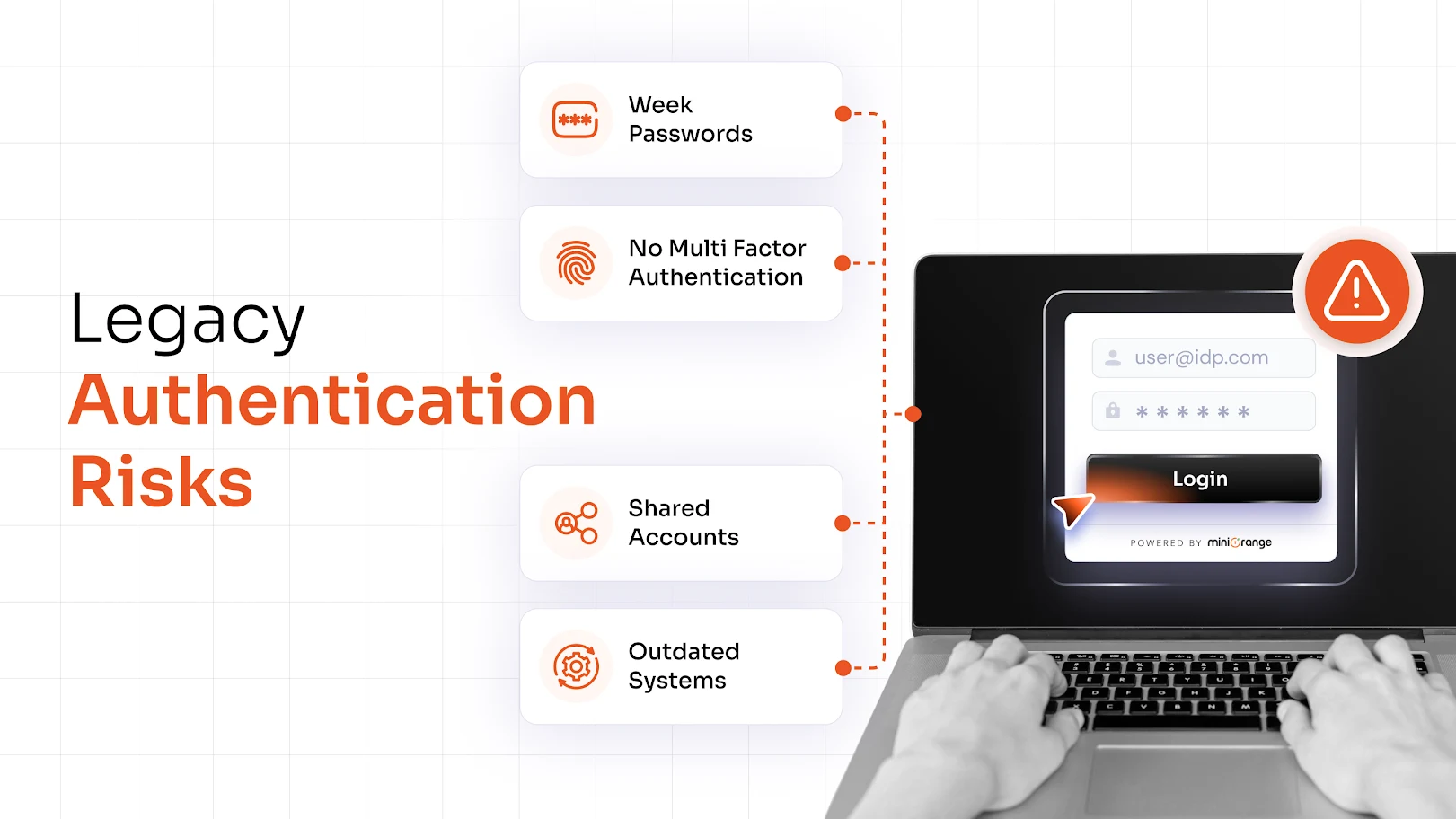
Weak Authentication Mechanisms
Using basic or outdated authentication methods can expose devices to security risks. Simple credentials or shared secrets can be easily compromised by attackers. Strong authentication, such as certificate-based or hardware-backed identity, is essential to establish trust. Without it, devices may be accepted without proper verification.
Manual Provisioning Errors
Manual provisioning increases the chances of human error during device setup. Misconfigured settings, missing security controls, or incorrect access permissions can create vulnerabilities. These errors may not be immediately visible but can lead to long-term security issues. Automation helps reduce these risks by ensuring consistent configurations.
Lack of Visibility Across Devices
Without centralized visibility, it becomes difficult to track which devices are connected and how they are behaving. This makes it harder to detect suspicious activity or enforce policies consistently. Organizations may struggle to identify non-compliant or unauthorized devices. Proper monitoring is essential to maintain control over device access.
Certificate and Key Mismanagement
Certificates and keys are critical for establishing device identity and secure communication. If they are not properly managed, they can become a point of failure. Expired, compromised, or improperly stored certificates can break trust and expose devices to attacks. Automating certificate lifecycle managementis essential to maintain security.
Best Practices for Device Provisioning
Device provisioning is only effective when it is implemented with the right security and operational controls. Without a structured approach, even well-designed provisioning processes can introduce risks and inconsistencies.
To ensure provisioning is secure, scalable, and reliable, organizations need to follow a set of proven practices. Here are some of the best practices for device provisioning:
Use Hardware-Backed Identities
Devices should be assigned unique identities that are tied to hardware components rather than software-based identifiers. This makes it significantly harder for attackers to replicate or spoof devices. Hardware-backed identities provide a stronger foundation for establishing trust during onboarding. They also improve overall security by ensuring that only genuine devices can authenticate.
Implement Zero-Touch Provisioning
Zero-touch provisioning automates the entire setup process, allowing devices to be configured as soon as they are powered on and connected. This removes the need for manual intervention and ensures consistent configurations across all devices. It is especially useful for large-scale deployments where speed and accuracy are critical. Automation also reduces the chances of configuration errors.
Enforce Least-Privilege Access
Devices should only be granted access to the resources they actually need. Limiting permissions reduces the potential impact if a device is compromised. This approach ensures that sensitive systems are not exposed unnecessarily. It also helps organizations maintain tighter control over device access.
Automate Certificate Lifecycle Management
Certificates play a key role in verifying device identity and securing communication. Managing them manually can lead to expired or misconfigured certificates, which creates security risks. Automating certificate issuance, renewal, and revocation ensures that trust is maintained at all times. It also reduces the operational burden on IT teams.
Integrate with IAM Solutions
Device provisioning should work alongside Identity and Access Management systems to provide unified control. This integration ensures that both user and device identities are validated before access is granted. It also helps enforce consistent policies across systems. As a result, organizations gain better visibility and control over access.
Continuously Monitor Device Posture
Provisioning is not a one-time activity. Devices need to be continuously monitored to ensure they remain compliant and secure over time. This includes checking for outdated software, policy violations, and unusual activity. Continuous monitoring helps identify risks early and maintain a strong security posture.
Future of Device Provisioning
Device provisioning is evolving to keep up with growing security demands and increasing device volumes. As organizations adopt more connected devices and distributed systems, traditional provisioning methods are no longer enough.
The focus is shifting towards more automated, intelligent, and security-driven approaches. Organizations are increasingly adopting AI-driven provisioning to make smarter decisions, Zero Trust frameworks for continuous verification, and automated workflows to handle large-scale deployments.
At the same time, stronger device identity models based on hardware-backed security are becoming more important. With the rise of IoT, remote work, and cloud-based systems, device provisioning will continue to play a critical role in securing access and maintaining control.
Simplify Device Provisioning with miniOrange
Managing device provisioning at scale requires more than just basic setup processes. Organizations need a solution that can securely onboard devices while maintaining visibility and control.
miniOrange offers a unified platform that helps organizations manage device provisioning along with identity and access controls. It enables secure onboarding, policy enforcement, and integration with IAM systems to ensure that only trusted devices can access critical resources.
By combining device provisioning with identity-driven security, organizations can reduce risk, improve efficiency, and scale operations without complexity.


Leave a Comment