If you’re relying on a password alone to protect sensitive data, the odds are not in your favor. In the U.S. alone, 2.28 billion password-related records were leaked out of 18.4 billion total data points in recent breaches.
Data breaches routinely expose millions of credentials, password reuse remains common, and phishing campaigns harvest login details with alarming success. Traditional passwords can be guessed, reused, stolen, or intercepted, leaving sensitive systems and accounts dangerously exposed.
Multi-Factor Authentication (MFA) strengthens security by requiring more than just a password. By combining something you know with something you have or something you are, MFA significantly reduces risk. TOTP, one of the most widely adopted MFA methods, provides time-based, one-time codes for stronger protection.
Many modern identity platforms, such as miniOrange’s MFA solution, support TOTP alongside push authentication, hardware tokens, and adaptive access policies, allowing organizations to strengthen security without disrupting user experience.
What is TOTP (Time-Based One-Time Passcodes)?
TOTP stands for Time-Based One-Time Password. It is a standardized algorithm defined in RFC 6238 that generates unique, temporary numeric passcodes (typically 6 digits) based on the current time. These codes serve as a second authentication factor, significantly strengthening account security beyond traditional passwords.
Key Characteristics of TOTP Authentication
- Time-Sensitive: Each code is valid for a specific window, typically 30 or 60 seconds. This temporal limitation prevents replay attacks and reduces the window of opportunity for attackers.
- Device-Bound: Codes are generated locally on your device using an authenticator app or hardware token, not transmitted over networks. This eliminates interception vulnerabilities inherent in SMS-based authentication.
- Ephemeral: Once the time window expires, the code becomes invalid and cannot be reused. This automatic expiration provides continuous protection against stolen or compromised codes.
- Cryptographically Secure: TOTP uses HMAC (Hash-based Message Authentication Code) with cryptographic hash functions like SHA-1, SHA-256, or SHA-512 to generate codes that are computationally infeasible to predict. Enterprise-grade 2FA solutions typically allow configurable hashing algorithms, time windows, and policy controls to meet regulatory or organizational security requirements.
How Does TOTP Work? The Technical Breakdown
The Two Key Ingredients
1. The Shared Secret (Seed): A static cryptographic key (random string of characters) shared between the server and your authenticator device during initial setup. This secret is typically transferred via QR code scanning and encoded in Base32 format. The shared secret must be kept confidential as it forms the foundation of TOTP security.
2. The Moving Factor (Time): Unlike other one-time password systems that use event counters, TOTP uses the current Unix timestamp as the variable input. The time is divided into fixed intervals (time steps), typically 30 seconds, creating synchronized time windows between client and server.
The TOTP Generation and Validation Process
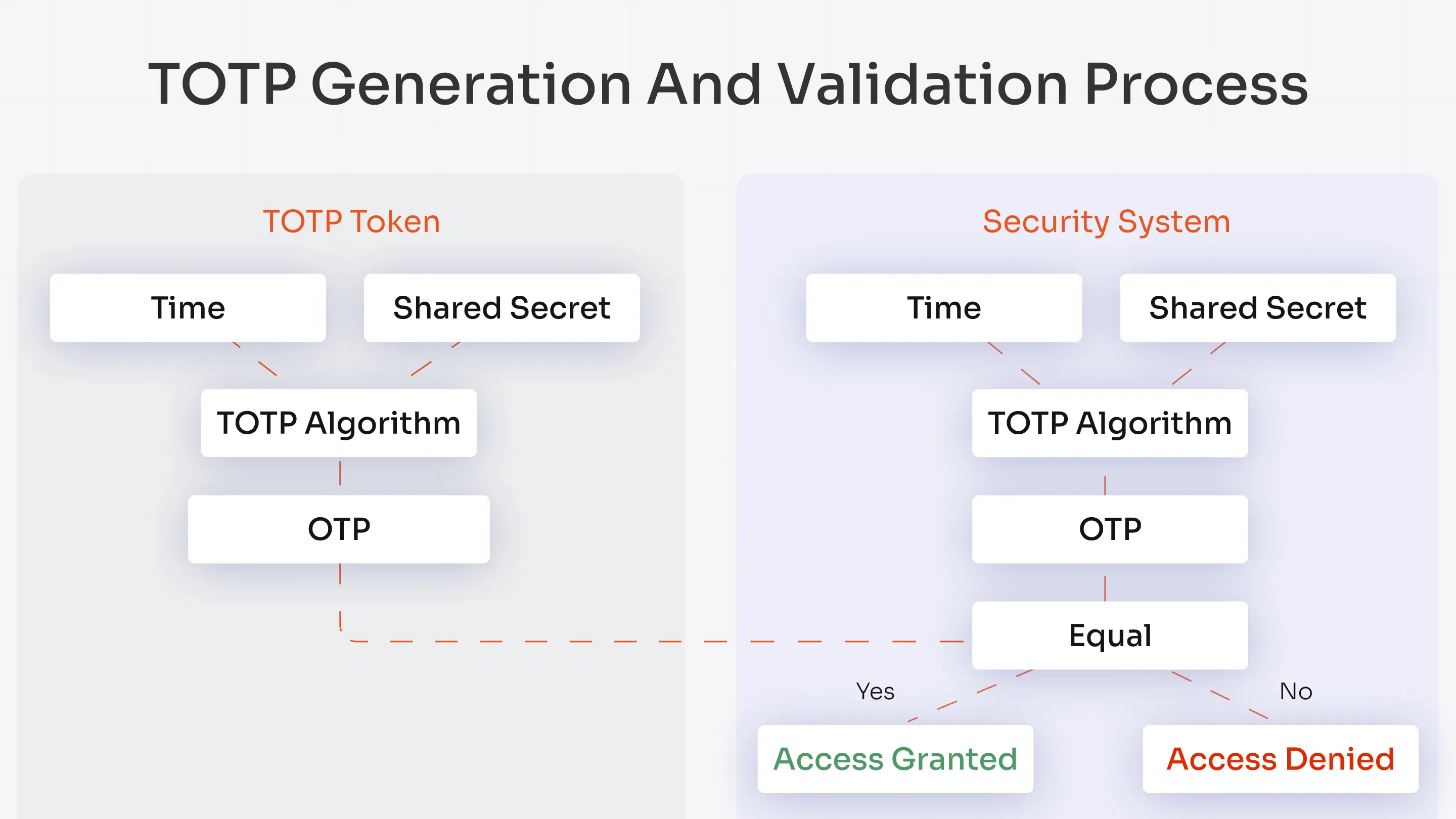
1. Clock Synchronization: Both the server and client device must maintain synchronized clocks.
2. HMAC Calculation: The system combines the shared secret and the current time counter using a cryptographic hash function, typically HMAC-SHA1.
3. Dynamic Truncation: The resulting hash undergoes dynamic truncation to extract a subset of bits, which are then converted into a human-readable numeric code (typically 6-8 digits).
4. Verification: The server independently performs the same calculation. If the user-provided code matches the server-calculated code (accounting for small time drift tolerances), authentication succeeds and access is granted.
TOTP vs. Alternative Authentication Methods
Understanding the differences between TOTP and other authentication methods helps organizations choose the right security approach for their needs.
TOTP vs. HOTP (HMAC-based One-Time Password)
| Characteristic | TOTP (Time-Based) | HOTP (Counter-Based) |
|---|---|---|
| Moving Factor | Current time (Unix timestamp divided by time step) | Event counter (increments with each generation) |
| Code Expiration | Automatic (typically 30-60 seconds) | Never expires until used |
| Synchronization | Requires synchronized clocks between client and server | Requires synchronized counter state |
| Replay Attack Risk | Low - codes expire automatically | Higher - stolen codes remain valid until used |
| Best Use Case | General-purpose authentication, mobile apps, web services | Offline systems, hardware tokens without clocks |
Key Takeaway: TOTP provides superior security through automatic code expiration, preventing attackers from harvesting and reusing codes obtained through phishing or token theft.
For a deeper understanding of how one-time passwords work, including the differences between TOTP, HOTP, and other OTP methods, explore our detailed guide on one time password (OTP) authentication.
TOTP vs. SMS Two-Factor Authentication
| Characteristic | TOTP | SMS 2FA |
|---|---|---|
| Network Dependency | Works offline (codes generated locally) | Requires cellular network connectivity |
| SIM Swapping Vulnerability | Immune (not tied to phone number) | Highly vulnerable to SIM swap attacks |
| Interception Risk | None (codes never transmitted) | Vulnerable to SS7 exploits and network interception |
| Privacy | No PII required (phone number not needed) | Requires phone number disclosure |
| Delivery Cost | Free (open-source algorithm) | Per-message fees (can be significant at scale) |
| International Travel | Works seamlessly worldwide | May face delays or delivery failures abroad |
Key Takeaway: TOTP offers superior security, privacy, and reliability compared to SMS-based authentication, eliminating network dependencies and SIM swap vulnerabilities.
Comprehensive Authentication Method Comparison
| Method | Phishing Resistance | Offline Capability | User Friction | Implementation Cost | Overall Security |
|---|---|---|---|---|---|
| TOTP | Moderate | Yes | Low | Low | Good |
| SMS | Low | No | Very Low | Medium-High | Weak |
| Push Notification | Moderate-High | No | Very Low | Medium | Good |
| FIDO2/WebAuthn | Excellent | Yes | Low | Medium-High | Excellent |
| Passkeys | Excellent | Yes | Very Low | Low | Excellent |
The Benefits of TOTP Authentication
1. Offline Functionality
TOTP authentication provides a critical advantage in connectivity-challenged scenarios. Since the cryptographic calculation happens entirely on your local device, you can generate authentication codes without internet or cellular connectivity.
2. Enhanced Privacy Protection
Unlike SMS-based authentication that requires sharing your phone number (personally identifiable information) with every service, TOTP operates without any PII disclosure. This privacy advantage is particularly valuable in jurisdictions with strict data protection regulations like GDPR.
3. Cost-Effective Implementation
Organizations implementing TOTP benefit from zero per-authentication costs. Unlike SMS authentication that incurs fees for each message delivered (which can reach significant costs at enterprise scale), TOTP uses an open-source algorithm that runs locally on user devices.
4. Widespread Industry Standardization
TOTP enjoys near-universal support across the authentication ecosystem. Major platforms like Google, Microsoft, GitHub, AWS, and thousands of other services accept TOTP codes.
5. Resistance to Network Interception
SMS messages travel through telecommunications infrastructure vulnerable to interception through network-level attacks. TOTP codes never traverse any network during generation, completely eliminating this attack vector.
Implementation Best Practices for Organizations
Successful TOTP deployment requires attention to both technical implementation details and operational security practices.
Technical Implementation Requirements
Rate Limiting and Brute-Force Protection
Implement aggressive rate limiting as the primary defense against brute-force attacks:
- Limit to 3-5 failed TOTP attempts before implementing a temporary account lockout (5-15 minutes)
- Implement CAPTCHA challenges after 2 failed attempts
- Log all failed authentication attempts with IP addresses, timestamps, and user agents for forensic analysis
Time Window and Tolerance Configuration
- Use 30-second time windows as standard (30 seconds provides security while maintaining usability)
- Never accept codes more than 1 minute old, as extended windows significantly increase brute-force vulnerability
Cryptographic Security
- Generate shared secrets using cryptographically secure random number generators (at least 160 bits of entropy for SHA-1, 256 bits for SHA-256)
- Use SHA-256 or SHA-512 instead of SHA-1 for new implementations (though SHA-1 remains acceptable for TOTP due to the truncation process)
Secure Enrollment Process
- Implement QR code expiration (5-minute validity window, invalidated after first successful scan)
- Require immediate password change after TOTP enrollment to invalidate any potentially compromised credentials
The Future of Authentication: Beyond TOTP
With the rise of AiTM and proxy-based attacks, password + TOTP alone is no longer enough. To stay secure, organizations are moving toward phishing-resistant authentication built for modern threats.
Evolution Toward Passwordless Authentication
Here’s how organizations are moving towards passwordless authentication:
- Passkeys and WebAuthn Adoption: Next-generation authentication leveraging platform authenticators (biometrics, device PINs) synchronized across user devices via secure cloud enclaves
- Phishing-Resistant Requirements: Organizations increasingly require authentication methods that cryptographically bind to specific domains, immune to phishing and AitM attacks
- Risk-Based and Adaptive Authentication: Modern authentication systems, such as miniOrange’s Adaptive MFA, adapt security requirements based on context (device trust, location, behavior patterns)
- Behavioral Biometrics Integration: Continuous authentication using behavioral biometrics (typing patterns, mouse movements) as alternative to periodic re-authentication
TOTP's Role in the Future Landscape
Despite emerging technologies, TOTP will remain relevant for the foreseeable future:
- TOTP serves as accessible baseline MFA for users and organizations unable to adopt FIDO2/passkeys immediately
- Critical for systems requiring offline authentication capabilities
- Provides fallback option when primary authentication methods fail
- Continues supporting legacy systems incompatible with modern authentication protocols
Organizations should view TOTP as a stepping stone toward phishing-resistant authentication while maintaining TOTP support for backward compatibility and accessibility.
Conclusion
TOTP authentication represents a massive improvement over static passwords and SMS-based two-factor authentication, offering a practical balance of security, usability, and cost-effectiveness. Key benefits include offline functionality, immunity to SIM swap attacks, privacy protection, and widespread industry support.
While highly effective, the rise of sophisticated phishing tools and AitM attack platforms suggests organizations should actively plan transitions toward phishing-resistant authentication methods like FIDO2 security keys and passkeys and token-based authentication mechanisms. At the same time, modern security strategies increasingly incorporate contextual based authentication, evaluating device trust, geolocation, network risk, and behavioral signals to dynamically adjust authentication requirements. This adaptive approach strengthens protection without introducing unnecessary user friction.
For organizations seeking to strengthen account security without sacrificing usability, standards-based TOTP integrated into a centralized multi-factor authentication platform offers a practical and future-ready solution.
FAQs
What is the meaning of TOTP?
TOTP stands for Time-Based One-Time Password. It is an authentication method that generates temporary numeric codes based on the current time and a shared secret key.
How do I get my TOTP code?
To get TOTP codes, download an authenticator app like Google Authenticator, Microsoft Authenticator, Authy, or 2FAS on your smartphone. During account setup, scan the QR code displayed by the service or manually enter the provided secret key.
What is the difference between TOTP and OTP?
OTP (One-Time Password) is a general term for any password used only once. TOTP is a specific type of OTP that uses time as its moving factor. TOTP's time-based approach offers advantages like automatic expiration and offline generation, making it more secure than SMS OTP.
Is TOTP security better than SMS?
Yes, TOTP security is significantly superior to SMS-based authentication. TOTP is immune to SIM swap attacks, works offline, doesn't require sharing your phone number, and cannot be intercepted through network vulnerabilities.
Can TOTP be hacked or phished?
While TOTP is much more secure than passwords alone, it can be compromised through sophisticated real-time phishing attacks where attackers use a proxy server to capture both your password and TOTP code, then immediately relay them to the legitimate service.
Do TOTP codes work without the internet?
Yes, TOTP codes generate entirely offline once the initial setup is complete. Since the calculation happens locally on your device using the shared secret and device time, no internet or cellular connection is required.



Leave a Comment