Remote and hybrid operating models have fundamentally changed how enterprises secure users, systems, and data.
In 2026, the "workplace" is no longer limited to a traditional corporate office setup; it is a distributed ecosystem of home offices, transit hubs, and cloud-native applications.
Workforce Identity and Access Management (IAM) has therefore evolved from an IT convenience into a primary security control governing how modern organizations operate safely at scale.
The Disappearance of the Network Perimeter
For decades, enterprise security was built on the "Castle and Moat" philosophy: if you were inside the network, you were trusted; if you were outside, you weren't. Corporate offices, managed devices, and internal infrastructure created a clearly defined perimeter that organizations could control. Remote and hybrid work have largely dismantled that assumption.
SaaS-First Enterprises: With the average enterprise now utilizing dozens, if not hundreds, of SaaS applications, the bulk of corporate data lives outside the traditional perimeter. Protecting a physical office is irrelevant when your data resides across a variety of distributed cloud platforms.
Cloud and On-Prem Coexistence: Most organizations aren't 100% cloud-native yet. They operate in a "messy middle" where legacy on-premise servers must communicate with modern cloud stacks. This hybrid reality creates fragmented identity silos, making it difficult for IT teams to maintain a single source of truth for workforce identity management.
VPN Limitations in Distributed Workforces: Traditional VPNs were never designed for the scale of a global hybrid workforce. They create significant latency, impacting productivity, and more concerningly, they provide flat network access. During a breach, this flat access model enables lateral movement across systems, significantly amplifying risk.
Identity as the New Security Control Plane
As corporate boundaries disappear, identity becomes the only consistent control layer across users, devices, and applications.
Users, devices, and applications outside corporate boundaries
Employees are increasingly operating outside managed enterprise environments.
Consider a typical hybrid employee:
- Logging into SaaS tools from home Wi-Fi networks
- Using mobile devices for approvals
- Accessing shared cloud collaboration platforms
- Working across personal and corporate endpoints
Whether they are using a managed laptop in London or a personal tablet in Singapore, their identity is the common thread that grants access to corporate resources.
Without strong identity governance, organizations lose visibility into who is accessing resources, from where, and under what level of risk.
Identity-Based Attacks Are Now the Dominant Breach Vector
Security leaders have realized that attackers no longer "break in" by exploiting software bugs; they "log in" by exploiting weak workforce authentication.
Recent incident response research shows that 90% of analyzed breaches involved identity weaknesses, with attackers frequently leveraging stolen credentials, phishing campaigns, MFA fatigue attacks, and session hijacking techniques for initial access.
Additionally:
- Valid credentials account for an estimated 85% intrusion success rate, allowing attackers to bypass perimeter defenses and progress from authentication to ransomware deployment within hours.
- Phishing-as-a-Service ecosystems have reduced exploitation timelines dramatically, with some attacks occurring within minutes of credential theft.
These trends illustrate how quickly identity compromise escalates into organizational risk.
Why Remote Workforce Security Must Start With Identity
In the face of these threats, the only viable defense is an identity-centric security (like Zero Trust) that assumes no implicit trust, regardless of a user's location or previous login status.
Instead of granting blanket access once a user clears a single login gate, a sophisticated workforce IAM strategy evaluates access requests in real-time based on five critical pillars:
1. Identity: Who is the user?
2. Context: What is their specific role and level of clearance?
3. Device: Is the hardware managed and recognized?
4. Geography: Where are they connecting from, and is that location expected?
5. Behavior: Does this request deviate from the user's established patterns?
By unifying these variables into a centralized Workforce IAM platform, organizations can enforce adaptive authentication and least-privilege access across SaaS, cloud, and legacy environments simultaneously.
This doesn't just block attackers; it provides IT teams with a single, clear pane of glass to monitor every workforce identity in the ecosystem.
Business Risks of Weak Workforce IAM
Weak workforce identity management rarely results in immediate failure. Instead, risk accumulates quietly.
- A contractor account that remains active after project completion.
- An employee who transfers departments but retains administrative permissions.
- A SaaS integration that continues accessing sensitive data months after business needs change.
Individually, these issues appear minor. Collectively, they create systemic exposure.
Unauthorized access and credential compromise:
This remains one of the most financially damaging threat vectors organizations face. Stolen credentials are notoriously difficult to detect because the attacker appears as a legitimate user.
Recent breach analysis research indicates that compromised credentials consistently rank among the leading initial access methods. They contribute to roughly 1 in 10 data breaches, with organizations often taking more than 6 months on average to fully identify and contain such incidents.
Compliance penalties (GDPR, HIPAA, ISO 27001, SOC 2):
Standards such as GDPR, HIPAA, ISO 27001, and SOC 2 require organizations to demonstrate controlled provisioning, enforce least-privilege access, and maintain verifiable authentication practices.
Fragmented workforce identities make maintaining consistent compliance significantly more difficult. Manual provisioning processes and delayed deprovisioning introduce audit blind spots that can ultimately lead to penalties, failed certifications, or reputational damage.
Productivity loss due to fragmented authentication systems:
Security friction directly affects workforce efficiency. Employees juggling multiple credentials, repeated login prompts, or inconsistent access approvals experience workflow disruption. IT teams, meanwhile, spend significant time resetting passwords, onboarding users manually, or troubleshooting access failures.
Workforce IAM platforms address this by consolidating authentication, automating identity lifecycle management, and aligning access with organizational roles from the moment employees join to the moment they leave.
Traditional Perimeter Security vs Identity-First Security Architecture
Legacy Approach: Network-Centric Access
For decades, enterprise access management revolved around protecting the corporate network itself.
Security teams focused on firewalls, internal segmentation, and VPN gateways under the assumption that users connecting from inside the network could be trusted.
VPN dependency
Virtual Private Networks were once considered the default method for enabling remote work. While effective for extending network access, VPNs were never designed for large-scale SaaS ecosystems or globally distributed teams.
Static trust
Traditional models rely heavily on one-time authentication decisions. After users successfully log in, access typically persists without continuous evaluation of risk signals such as device posture, behavioral anomalies, or location changes.
Limited visibility into SaaS
As organizations adopt cloud collaboration platforms, developer tools, and HR systems, critical business data increasingly resides outside internal infrastructure. Network-centric controls struggle to provide granular insight into who accessed which SaaS application, from where, and under what conditions, leaving significant monitoring gaps.
Modern Approach: Identity-First Security with miniOrange
In contrast, identity-first architecture shifts the focus from protecting networks to securing workforce identities themselves.
Rather than assuming trust based on location, access decisions are continuously validated through centralized authentication and contextual policy enforcement.
Solutions like the miniOrange Workforce IAM Platform enable organizations to consolidate authentication, governance, and access enforcement across SaaS, cloud, and legacy environments within a unified framework.
Centralized authentication authority
A single authentication layer acts as the control point for workforce access across applications. Employees authenticate once through secure Single Sign-On, while administrators gain centralized visibility into login activity, risk signals, and access behavior across the organization.
Policy-driven access controls
Access decisions are governed by contextual policies rather than static permissions. Using Workforce Access Management policies, the context of every login is evaluated. Access is granted or denied based on real-time risk, such as role assignments, device posture, geographic location, or session risk, not just a valid password.
Continuous verification
Modern workforce IAM does not treat authentication as a one-time event. Continuous verification evaluates sessions throughout their lifecycle, enabling adaptive authentication or session termination if risk conditions change.
Why Identity-First Security Enables Secure Hybrid Workforce Access Management
Hybrid work environments require secure access regardless of whether employees operate from corporate offices, home networks, or temporary remote locations. Identity-first security enables consistent enforcement without relying on network boundaries.
Secure access across office, home, and remote locations
Users authenticate through identity policies rather than network presence. This allows organizations to extend secure workforce access management globally while maintaining consistent governance standards.
Whether an employee is in the corporate headquarters, at a coffee shop, or working from home, the security posture remains consistent.
Device-aware conditional access
In a hybrid work environment, "Bring Your Own Device" (BYOD) is common. Identity-first security allows organizations to make authentication decisions that incorporate device health and ownership signals.
For instance, an employee can check their email on a personal phone, but they can only access the financial ERP from a managed, encrypted laptop.
SaaS + legacy application coverage
Most enterprises operate in hybrid environments combining modern SaaS tools with legacy on-premise applications. Identity-first architecture bridges these ecosystems, allowing organizations to apply uniform workforce identity management policies across both environments without maintaining separate security controls.
Core Components of miniOrange Workforce IAM Solutions
1. Single Sign-On (SSO) for Distributed Teams
Single Sign-On (SSO) establishes a centralized authentication gateway that enables workforce identities to securely access thousands of integrated applications through a single verified login.
Unified access across 5,000+ cloud and on-prem apps
Unified access across more than 5,000 cloud and on-prem applications allows organizations to eliminate credential sprawl while maintaining consistent access policies.
Reduced password fatigue
Employees move seamlessly between platforms without repeated authentication interruptions, significantly reducing password fatigue and the likelihood of unsafe password reuse.
Centralized access monitoring
Instead of investigating incidents across disconnected systems, admins can track authentication events, enforce policies, and identify anomalies from a centralized dashboard, giving IT and security teams real-time visibility into login activity across the workforce.
Improved employee onboarding speed
SSO also accelerates user onboarding. New employees receive immediate application access aligned with their roles rather than waiting for manual provisioning across departments; an essential capability for scaling teams and distributed hiring models.
2. Adaptive Multi-Factor Authentication (MFA)
Adaptive Multi-Factor Authentication adds an intelligent layer to remote workforce security by evaluating the risk of every login attempt before it is granted.
Instead of forcing repetitive verification for low-risk scenarios, authentication requirements dynamically adjust based on device trust, location, login time, IP risk, etc.
Risk-based authentication:
Risk-based authentication policies allow organizations to apply stronger verification only when necessary. For instance, a trusted employee logging in from a corporate-managed device may experience seamless access, while an unfamiliar device or unusual geographic login triggers additional verification steps.
Device, location, and behavior-based policies:
Adaptive MFA evaluates workforce authentication attempts using device fingerprinting, behavioral patterns, and contextual signals such as login location, time, and endpoint trust posture. Familiar access patterns allow seamless entry, while unfamiliar devices or abnormal behavior automatically trigger stronger verification or access restrictions.
Phishing-resistant MFA (FIDO2, passkeys):
Phishing-resistant authentication methods such as passkeys and FIDO2-based credentials further reduce exposure to credential theft and MFA fatigue attacks. These modern authentication mechanisms eliminate shared secrets and significantly limit phishing exploitation.
Step-up authentication for sensitive resources:
Step-up authentication adds another layer to remote workforce security for high-risk actions. Accessing financial systems, downloading sensitive datasets, or modifying privileged configurations can automatically trigger stronger verification protocols, ensuring access aligns with risk sensitivity.
3. Zero Trust for Remote Work
Zero Trust security replaces implicit trust with continuous validation.
- Explicit Verification: Every request is authenticated and authorized based on all available data points, including user identity, location, and device security posture.
- Least Privilege Enforcement: Users are granted only the minimum level of access required to perform their specific job functions, significantly limiting lateral movement opportunities during a breach.
- Continuous Identity Validation: Identity verification does not end at the initial login. Sessions are monitored continuously to ensure that the security context hasn't changed (e.g., the device has not moved to an untrusted network).
How miniOrange enables Zero Trust for remote work:
miniOrange delivers a unified Zero Trust framework that protects workforce identities across cloud, on-premise, and hybrid environments by continuously validating access based on identity, device posture, and contextual risk.
Fine-grained, policy-driven controls evaluate user role, device trust, location, and behavioral signals before granting access. Micro-segmentation ensures users receive only the permissions required, limiting lateral movement during potential compromises.
miniOrange integrates with endpoint security and mobile device management solutions to validate device health alongside user authentication. This ensures access decisions reflect real-time endpoint posture across both SaaS and legacy environments.
Continuous monitoring powered by adaptive MFA and threat intelligence evaluates session risk beyond login. Suspicious behavior can automatically trigger step-up authentication, restricted access, or session termination, ensuring only verified users access sensitive resources regardless of network location.
Internal Link Opportunity: Zero Trust architecture page
4. User Identity Lifecycle Management (JML Automation)
One of the largest sources of organizational risk is not external attackers; it is outdated access permissions.
Employees change roles, contractors rotate through projects, and departments restructure frequently. Without automation, access rights quickly become misaligned with actual responsibilities.
User identity lifecycle management addresses this through structured Joiner-Mover-Leaver (JML) automation.
HRMS integrations enable automatic provisioning when employees join the organization. User accounts are provisioned across application & directories based on predefined role templates, allowing new hires to gain day-one access with appropriate permissions in place.
When employees change roles or departments, mover workflows adjust privileges automatically, preventing privilege creep caused by accumulated permissions.
Leaver workflows ensure rapid deprovisioning the moment employment ends or contracts expire, eliminating orphaned accounts that often become attack entry points.
SCIM-based automation synchronizes identity updates across SaaS and enterprise applications, removing the need for repetitive manual administration.
Access certification and review workflows further strengthen governance by enabling periodic audits of permissions. Managers and auditors can validate whether access remains appropriate, improving compliance posture while supporting scalable identity lifecycle management.
5. Privileged Access Management (PAM)
Administrative accounts represent some of the highest-risk workforce identities within any organization. Excessive or permanent privileged access dramatically increases breach impact when credentials are compromised.
Privileged Access Management (PAM) reduces this exposure by minimizing standing privileges and enforcing controlled elevation.
Just-in-time privileged access
JIT privileged access grants administrative permissions only when required and only for a limited duration. Users receive elevated access temporarily rather than maintaining permanent administrative rights.
Session recording and monitoring
Session recording and monitoring provide detailed visibility into privileged activity. Security teams can review commands executed during sensitive sessions, supporting forensic investigations and compliance reporting.
Role-based admin delegation
Role-based administrative delegation ensures responsibilities are distributed appropriately without granting excessive authority. Teams can manage specific systems without gaining unrestricted access across the environment.
Eliminating standing privileges
By eliminating always-on privileged accounts, organizations significantly reduce insider risk and credential abuse opportunities while maintaining operational efficiency.
Security Risks of Unmanaged Identities in Hybrid Workforces
Orphaned Accounts in SaaS Environments
SaaS adoption has accelerated faster than most organizations' ability to govern access consistently. Contractor accounts often remain active after project completion, temporary vendor permissions persist beyond engagement timelines, and shadow IT introduces applications outside IT visibility.
These orphaned identities create silent entry points into business systems. Beyond security exposure, they also introduce audit gaps when organizations cannot clearly demonstrate who retained access to sensitive resources and why.
Privilege Creep and Role Sprawl
As employees move across roles or teams, access permissions frequently accumulate rather than adjust. Without periodic certification reviews or automated role alignment, users retain privileges that no longer reflect their responsibilities.
Over time, this privilege creep expands the attack surface. A compromised account with excessive permissions can provide attackers immediate access to sensitive systems without requiring additional escalation.
MFA Fatigue and Identity-Based Attacks
Modern attackers increasingly target workforce authentication rather than infrastructure vulnerabilities.
Techniques such as push notification bombing attempt to overwhelm users into approving fraudulent login requests. MFA fatigue often leads the user to eventually hit "Approve" simply to stop the notifications.
Adversaries are also moving beyond credential theft to steal or hijack active session tokens. By bypassing the initial workforce authentication entirely, they can masquerade as a legitimate user within a validated session, rendering traditional, static MFA ineffective.
Example: A 2025 data exposure involving MagentaTV revealed session identifiers within an unsecured database, highlighting how stolen session tokens can allow attackers to impersonate authenticated users without triggering MFA challenges.
When authentication policies lack contextual risk evaluation or continuous monitoring, attackers can bypass traditional defenses using legitimate credentials.
Compliance and Governance Exposure
Regulatory compliance depends on demonstrating consistent access governance across the workforce. Regulatory bodies (SOC 2, ISO 27001) require proof of timely provisioning and deprovisioning. Delayed certification reviews, incomplete audit trails, or inconsistent deprovisioning workflows can, therefore, increase the likelihood of failed audits.
Beyond regulatory penalties, poor identity governance can raise cyber insurance premiums. Organizations that cannot demonstrate robust workforce access management are facing significantly higher premiums, or outright denial of coverage, due to their perceived volatility. Slow incident response investigations turn unmanaged identities into both a security and operational liability for hybrid enterprises.
Architecture Blueprint: Implementing Workforce IAM with miniOrange
Phase 1: Identity Discovery and Risk Assessment
Start with visibility into identities and access relationships before enforcing controls.
Identity inventory across SaaS and on-prem: Identify users, service accounts, and applications across SaaS and on-premise environments to establish a unified identity inventory.
Privilege mapping: Highlight excessive access, dormant accounts, and high-risk permission overlaps that can become entry points for attackers.
Phase 2: SSO and MFA Consolidation
Once identities are discovered, the next priority is to harden the workforce authentication process and reduce the overall attack surface by eliminating security gaps between different applications.
Eliminate redundant authentication systems: Implement Single Sign-On (SSO) as a single source of truth for all corporate access, reducing password reuse risks while enabling unified access logging and control.
Standardize MFA policies: Apply consistent MFA enforcement across applications to improve workforce identity protection without increasing user friction.
Phase 3: Automate Identity Lifecycle Management
Automation is essential for maintaining security at scale. This phase focuses on removing manual intervention from the "Joiner-Mover-Leaver" (JML) process to ensure access always reflects an employee's current status.
Integrate HRMS: Link the workforce identity management platform directly to the Human Resources Management System (HRMS). Trigger automatic access updates when employees join, change roles, or leave the organization.
Deploy SCIM provisioning: The System for Cross-domain Identity Management (SCIM) protocol allows for real-time synchronization between the central directory and cloud applications. This ensures that when an identity is modified centrally, the change is reflected across the entire SaaS ecosystem instantly.
Phase 4: Zero Trust Maturity
The final phase involves transitioning to a Zero Trust architecture, where trust is never assumed based on the network location but is continuously earned through contextual verification.
Context-based policy refinement: Continuously evaluate access using behavioral signals, device trust, IP risk, roles, or location.
Device trust enforcement: Perform device fingerprinting and health checks to ensure that only managed, encrypted, and familiar devices can access sensitive data.
Continuous access evaluation: Perform periodic assessments to detect session anomalies and dynamically revoke access if risk conditions change mid-session.
Workforce IAM and Business Outcomes
Stronger Remote Workforce Security
Workforce IAM reduces exposure across distributed environments by enforcing consistent identity controls. Moving to an identity-first model directly impacts the two most critical metrics in cybersecurity:
Reduced Breach Probability: By enforcing workforce authentication standards like phishing-resistant MFA, organizations can virtually eliminate credential-based entry points.
Lower Lateral Movement Risk: A modern IAM platform enforcing Zero Trust ensures that even if one identity is compromised, the attacker is confined to a single, low-value resource rather than being able to traverse the entire infrastructure.
Improved Productivity and User Experience
The friction often associated with security is usually a byproduct of poor architecture. Modern workforce access management aims to make the secure path the easiest path for the employee.
Faster access: Automated provisioning ensures that new hires are productive from their first hour, with all necessary permissions pre-configured based on their role.
Reduced password resets: Implementing self-service password resets and passwordless authentication can reduce support desk overheads, allowing IT teams to refocus on high-value digital transformation projects.
Seamless SaaS access: With authentication solutions like SSO, employees log in once and gain instantaneous access to their entire application ecosystem. This eliminates the login fatigue that causes employees to seek insecure workarounds or shadow IT solutions.
Compliance and Audit Readiness
For organizations in regulated industries, identity is the primary evidence requested during audits. Modern IAM transforms compliance from a manual task into a continuous, automated state.
Centralized access logs: Every login, permission change, and access request is recorded in a centralized dashboard, making it simple to demonstrate which user has access to what, and why.
Automated certification campaigns: Periodic access reviews ensure permissions remain aligned with employee roles, preventing privilege accumulation over time.
Policy consistency across environments: Standardized identity policies enforce the same governance controls across hybrid infrastructure, reducing audit gaps and configuration inconsistencies.
The Future of Workforce Identity and Access Management (IAM)
Managing Non-Human Identities
Human users are no longer the majority identity type inside enterprise environments. Cloud workloads, DevOps pipelines, robotic process automation, AI agents, and API integrations now create millions of machine credentials operating continuously behind the scenes.
Industry analysts increasingly highlight non-human identities as one of the fastest-growing enterprise attack surfaces, largely because ownership and lifecycle governance remain unclear across departments. When service accounts persist without rotation policies or bots retain excessive permissions, they quietly accumulate privilege without visibility.
Future-ready workforce identity management must therefore treat non-human identities as first-class citizens by focusing on:
- Automated ownership tracking for service accounts
- Credential rotation and API token governance
- Least-privilege enforcement for automation workflows
Passwordless Authentication Adoption
Passwords are becoming increasingly incompatible with distributed work. Phishing automation, credential marketplaces, and AI-assisted social engineering have significantly reduced the effort required to compromise traditional authentication methods.
As a result, enterprises are accelerating the adoption of passwordless workforce authentication models built around cryptographic trust rather than shared secrets.
Passkeys and FIDO2 authentication introduce device-bound credentials that cannot be reused or replayed across environments. Biometrics further reduces dependency on memorized passwords while improving login speed for mobile and hybrid employees.
To maintain relevance in this evolving scenario, workforce access management solutions must prioritize:
- Seamless authentication across devices without password resets
- Login flows resistant to credential harvesting
- Strong authentication without increased user friction
AI and Risk-Adaptive Access Decisions
Security teams are no longer able to manually evaluate every login attempt across thousands of applications and endpoints. Workforce IAM is therefore shifting toward continuous risk evaluation powered by behavioral intelligence.
AI models increasingly analyze signals such as login timing patterns, device posture, geographic anomalies, entitlement usage, and access velocity to determine whether a request aligns with normal behavior. Instead of relying solely on static policies, access decisions are becoming contextual and dynamic.
Emerging workplace IAM capabilities must include:
- Detecting subtle account takeover attempts before privilege escalation
- Automatically triggering step-up authentication during abnormal behavior
- Recommending entitlement cleanup to reduce privilege creep
Note: This does not eliminate human oversight. Rather, AI functions as a decision accelerator, highlighting risk signals faster than manual monitoring ever could.
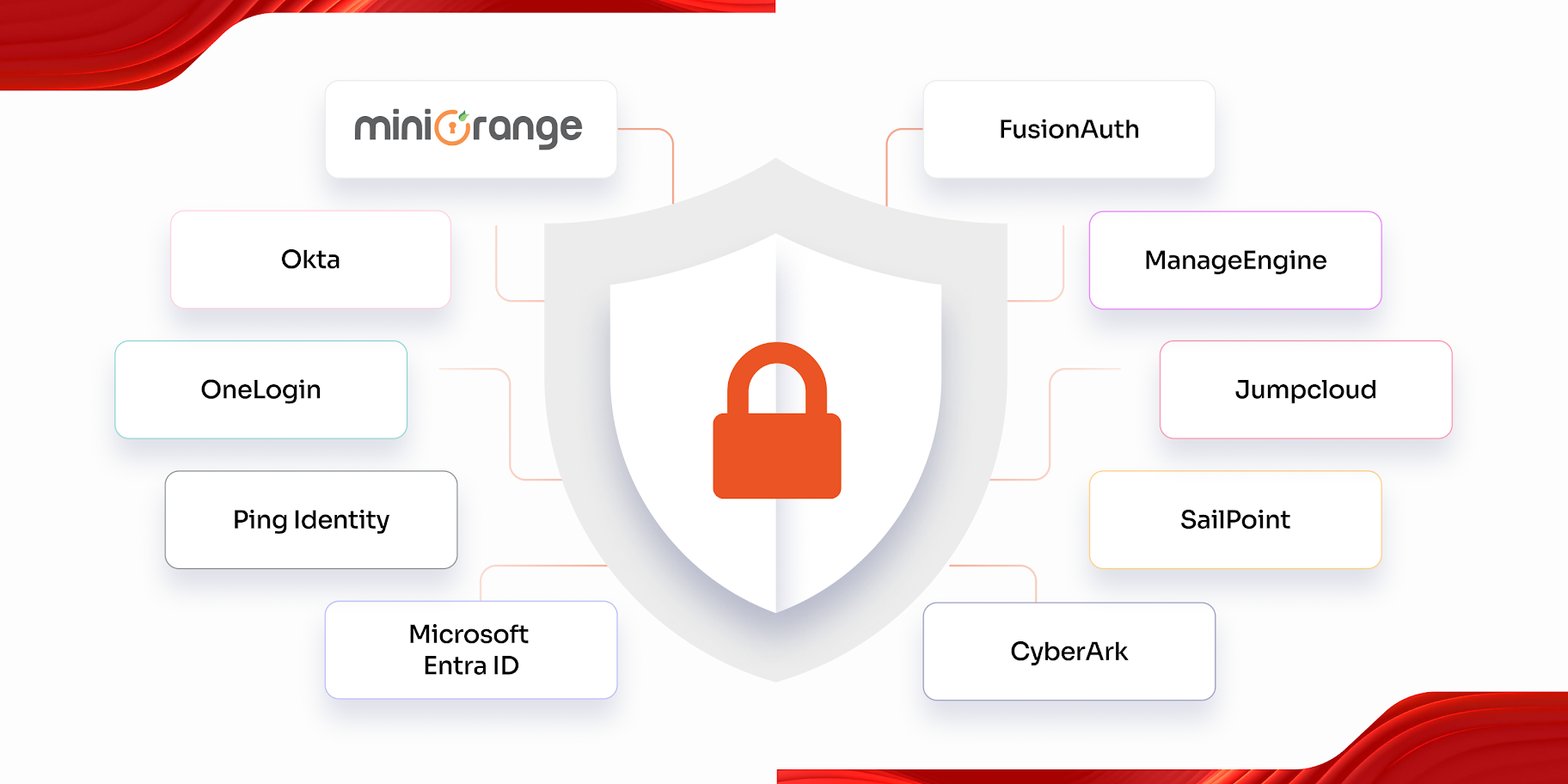
Why Enterprises Choose miniOrange for Workforce IAM Solutions
Selecting a workforce identity and access management provider is a strategic decision that impacts both the security posture and the operational velocity of an organization. As enterprises navigate the complexities of remote and hybrid work, they require a partner that can bridge the gap between legacy infrastructure and cloud-native innovation.
The miniOrange Workforce IAM Platform has emerged as a preferred choice for global organizations by prioritizing three critical pillars: security depth, deployment agility, and user-centric design.
Unified Platform Approach
One of the primary challenges in workforce identity management is the fragmentation of security when organizations use different vendors for different identity needs.
miniOrange eliminates this by providing a comprehensive ecosystem where SSO, MFA, PAM, and Identity Governance reside within a single, unified framework.
- Integrated Ecosystem: By consolidating these core capabilities, organizations gain a holistic view of their security posture. A single platform allows IT teams to manage workforce authentication, monitor privileged sessions, and automate user lifecycles without switching between separate consoles.
- Cohesive Security Context: A unified platform ensures that risk signals are shared across modules. For example, a suspicious login detected by the MFA engine can immediately trigger an alert within the PAM module to restrict administrative access, providing a layered defense that siloed tools cannot match.
Hybrid Deployment Flexibility
The miniOrange Workforce IAM platform is architected to support cloud, on-premise, or hybrid deployment models based on specific organizational requirements.
- Protecting Existing Investments: Enterprises can secure their on-premise legacy applications alongside modern SaaS tools using the same set of security protocols.
- Data Sovereignty: For organizations in highly regulated sectors, the ability to deploy the workforce IAM solution on-premise or in a private cloud ensures that sensitive identity data remains within their geographic or physical control, simplifying compliance with local data residency laws.
Enterprise-Grade Scalability
miniOrange Workforce Identity and Access Management (IAM) is built to handle the high-volume demands of large, global workforces without compromising on performance or latency.
- Global Reliability: The platform supports a large number of workforce identities and ensures that authentication requests are processed quickly, regardless of where the employee is located.
- Multi-Region Compliance Alignment: The platform's built-in compliance support allows for region-specific access controls, ensuring that a global workforce remains compliant with localized standards like GDPR, SOX, HIPAA or regional banking regulations.
Fast Implementation and Integration
The Workforce IAM platform is designed to minimize the deployment gap through an architecture that prioritizes ease of integration.
- Pre-built Connectors: With integration support for 5,000+ apps, organizations can connect their entire application portfolio, from Microsoft 365 and AWS to custom-built internal tools, in a fraction of the time required by traditional vendors.
- API-First Architecture: For unique or complex environments, the miniOrange API-first approach allows developers to extend the platform's capabilities and integrate workforce access management directly into existing business workflows.
FAQs
How does Workforce IAM improve remote workforce security?
Workforce IAM secures remote access by verifying identities instead of trusting networks. Features like SSO, adaptive MFA, and device- or behavior-based risk checks ensure only legitimate users access business applications. Centralized visibility also helps security teams quickly detect compromised accounts or abnormal activity.
What is the role of Zero Trust in hybrid workforce access management?
Zero Trust enables secure hybrid workforce access management by eliminating implicit trust based on network location. Employees are no longer automatically trusted because they connect from a corporate office or VPN. Instead, every access request is continuously verified based on identity, device health, geographic context, behavioral risk signals, and user privileges before granting or maintaining access. Least-privilege enforcement and micro-segmentation ensure users receive only the permissions required for their roles, limiting lateral movement during a breach.
Why is identity lifecycle management critical for compliance?
Identity lifecycle management is essential for compliance because most regulatory frameworks require organizations to demonstrate controlled access provisioning, timely deprovisioning, and ongoing permission governance. Automated Joiner-Mover-Leaver (JML) workflows ensure employees receive appropriate access when they join, privileges adjust automatically when roles change, and accounts are immediately revoked when employment ends. This prevents orphaned accounts and privilege creep, both of which create audit risks.


Leave a Comment