What is Zero Standing Privileges (ZSP)?
Zero Standing Privileges is a security principle where human or machine identities and accounts have no persistent, always-on privileged access rights by default. Instead, privileges are granted only when needed, for a specific purpose, for a specific period of time, and are then automatically revoked afterward. ZSP is essentially an advancement of the Just-in-Time privileged access management system that goes a step further to achieve true least privilege.
A common example of ZSP is the difference between having a master key to every room in a building at all times versus having to request a specific room key, using it, and returning it immediately after.
Why is Zero Standing Privileges Important?
Many organizations operate by assigning "always-on" privileges for each system to individual users. These persistent, always-on access rights can lead to insider threats and data breaches.
ZSP ensures that authorized access is never pre-assigned but is instead automatically allocated for specific tasks and only for the necessary duration. This approach significantly reduces the attack surface by limiting opportunities for privilege abuse. By ensuring that privileges are securely scoped and short-lived, ZSP helps prevent the accumulation of access rights that could lead to data breaches, unauthorized data access, and other security violations. This approach strengthens security protocols and supports compliance by enforcing strict access control standards.
Risks of standing privileges
- Excessive Access Risk: Standing privileges allow for continuous, unmonitored access to IT resources, making them vulnerable if credentials are compromised, granting attackers unrestricted entry into the system.
- Security Issues with Permanent Access: The necessity to constantly monitor who has access to what, especially in growing IT environments with remote work, demands significant ongoing management and can lead to security oversights.
- Increased Risk of Lateral Movement: Withstanding privileges, attackers can use compromised credentials to move laterally within the network, accessing sensitive areas and escalating privileges, thus amplifying the potential damage from a breach.
- Resource Drain in Access Management: Continuous provisioning and de-provisioning of access for new or departing employees can overextend an organization's resources, increasing the chance of errors that lead to breaches.
- Inadequacy of Traditional PAM Solutions: Traditional Privileged Access Management solutions often fail to adequately prevent breaches from compromised credentials, underscoring the need for a Zero Standing Privileges approach to limit access to resources strictly as needed.
What is a Just-in-Time Access Model?
The Just-in-Time (JIT) access model is a real-time strategy for privileged access management (PAM) that limits privilege activation to only the precise moments they are needed. Rather than granting "always-on" access indefinitely, JIT enforces time-based restrictions driven by behavioral and contextual parameters; privileges come into existence when a legitimate need arises and expire immediately once that need is fulfilled.
How JIT Access Works
PAM programs implement JIT access through three primary mechanisms:
- JIT Group Membership: A user is temporarily added to a privileged group for the duration of a task, then removed automatically.
- JIT Account Creation: A privileged account or role is created on demand for a specific request and deleted afterward.
- JIT Account Enabling: An existing administrative account is activated for a user temporarily, then disabled once the task is complete.
Implementing a JIT model transforms how administrative privileges are handled. For example, in a standard environment, an administrator might have continuous access throughout the week, 24*7, 7 days a week, totaling 168 hours.
However, with JIT, this access could be restricted to as little as a few hours, or even minutes per week, based on specific tasks and operational requirements. This reduction ensures that access rights are provided dynamically and only as needed.
Zero Trust vs least privilege?
Zero Trust and the principle of least privilege are two fundamental concepts in cybersecurity that focus on minimizing access risks, but they differ in their approach and emphasis.
Zero Trust operates on the principle of "never trust, always verify." This means it doesn't automatically trust anything inside or outside its network. Instead, Zero Trust requires verification for every access request regardless of where the request originates or what resource it accesses. It involves continuous authentication and authorization checks to ensure security is maintained throughout a session, not just at the entry point.
Least Privilege, on the other hand, is about limiting user access rights to only what is strictly necessary to perform their job functions. It focuses on minimizing the potential damage that could occur if an account is compromised. By providing the minimum level of access required, it reduces the risk and impact of a security breach.
While Zero Trust encompasses a broader, more holistic approach to network security, constantly questioning the security status of assets and user access, least privilege is more specifically concerned with ensuring users don’t have more access than they need. Both approaches aim to enhance security by controlling access based on user identity and context, but they apply their principles in slightly different ways to protect digital environments.
How do you implement Zero Standing Privileges?
Implementing ZSP is a continuous journey, not a one-time setup. Organizations must build structured workflows, enforce strict access controls, and integrate the right tooling to achieve a true ZSP posture.
- Control Time, Entitlements, and Approvals (TEA) Define how long access lasts, what permissions are granted, and how requests get approved. Session durations should match the task — not be fixed blanket windows. Approvals should be automated through tools teams already use, like Slack or ServiceNow, to avoid workflow disruption.
- Build a Just-in-Time Access Workflow Every access request should be logged, policy-evaluated, and auto-provisioned without manual admin intervention. A reliable JIT solution like miniOrange JIT access management is the operational backbone of any ZSP implementation.
- Use Attribute-Based or Role-Based Access Controls Design policies that automatically grant access when a user meets defined criteria, role, device posture, location, etc. This reduces manual bottlenecks and ensures access decisions are consistent and auditable.
- Eliminate Static Credentials Replace long-lived, always-on credentials with ephemeral secrets that expire after each session. Store and rotate shared privileged account credentials through a secrets vault to limit exposure if credentials are ever compromised.
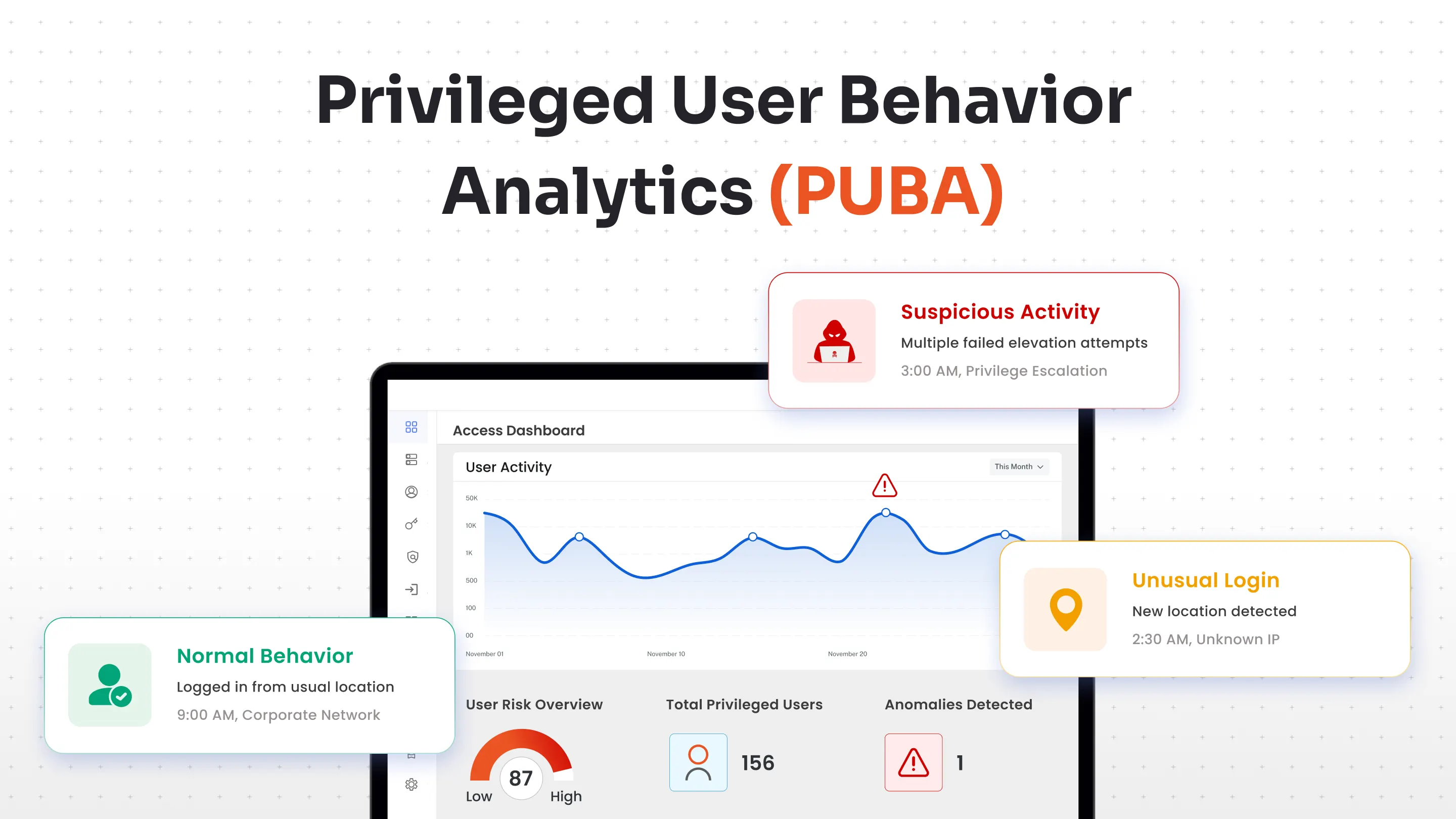
- Monitor, Log, and Audit Every Access Event Record every session, flag anomalies in real time, and maintain complete audit trails. This supports fast incident response and simplifies compliance reporting for frameworks like SOC 2, HIPAA, and PCI-DSS.
- Embed ZSP Within a Zero Trust Strategy ZSP works best as part of a broader Zero Trust posture, layered with MFA, network segmentation, and identity governance. No single control is enough; defense-in-depth ensures breaches are contained even when individual layers are bypassed.
miniOrange PAM for Implementing Zero Standing Privileges
miniOrange PAM comes with a modern Privileged Access Management solution, offering identity-based, cloud-first access control over your organization's critical resources. miniOrange PAM recognised as a leading access control system supporting ZSP architecture. With that, you empower your team to grant access precisely when it is needed, enhancing security without compromising productivity. All access is monitored and granted on the basis of user identity, utilizing the principles of Zero Standing Privileges and Just-in-Time access, minimizing the overall risk of unauthorized access and significantly reducing the threat of data breaches.
Start a free 30-day trial of miniOrange PAM today and experience firsthand how straightforward and effective implementing Zero Standing Privileges and Just-in-Time access can be.

Leave a Comment