Privileged accounts are the most powerful and most vulnerable identities in any organization.
System administrators, DevOps engineers, and IT teams have access to core systems, sensitive data, and critical infrastructure. This level of access is essential for daily operations, but it also makes these accounts highly attractive targets for attackers.
The real challenge is not just tracking activity, but understanding whether that activity is normal or not.
Traditional security tools can show what actions were performed, but they often lack the context to determine if those actions are expected.
This is where Privileged User Behavior Analytics (PUBA) becomes important. PUBA strengthens Privileged Access Management (PAM) and Zero Trust security by adding behavioral context to user activity.
In this blog, we will explore what PUBA is, how it works, and why it plays a critical role in modern identity and access security.
What Is Privileged User Behavior Analytics (PUBA)?
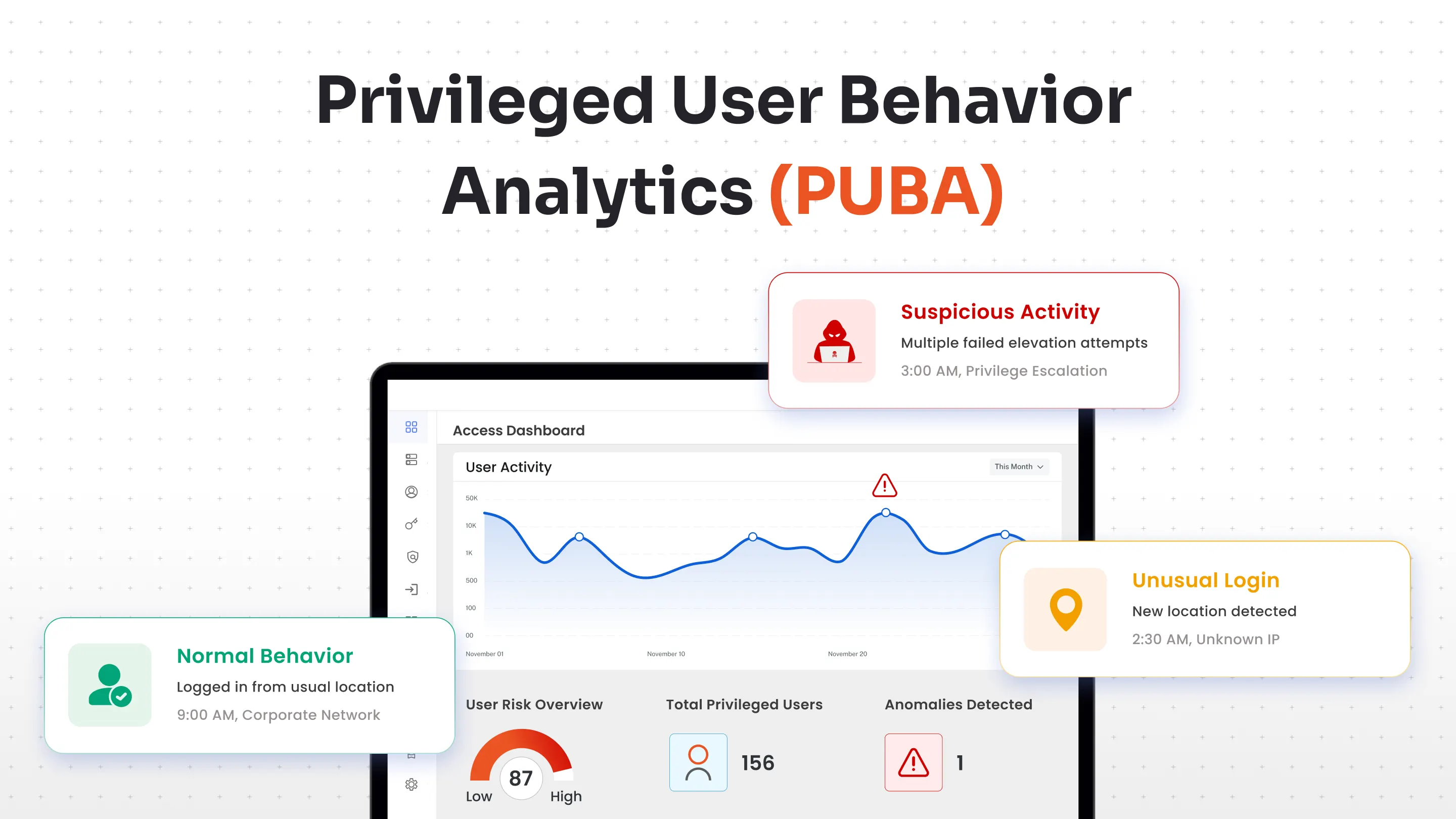
Privileged User Behavior Analytics (PUBA) is a security approach that monitors and analyzes the behavior of users with elevated access to detect unusual or suspicious activity.
Instead of only tracking activity, PUBA focuses on how privileged users typically behave and identifies patterns that do not match. It helps detect insider threats, compromised accounts, and unusual behavior early, before it turns into a serious security incident.
At its core, PUBA answers a simple question: “Is this activity normal for this user?”
Privileged accounts are considered high-risk because they can access sensitive data, modify system configurations, create or delete users, and bypass standard security controls. If one of these accounts is misused either by an insider or an attacker, the impact can be significant.
PUBA adds an additional layer of intelligence by analyzing behavior over time and identifying patterns that deviate from what is expected. It also works closely with identity security frameworks such as:
- Privileged Access Management (PAM)
- Identity and Access Management (IAM)
- Zero Trust security models
How Privileged User Behavior Analytics Works?
Privileged User Behavior Analytics (PUBA) goes beyond static rules by using behavioral analytics and machine learning to understand what normal activity looks like for each user. Instead of evaluating isolated events, it analyzes patterns over time to detect unusual behavior.
Here’s how the process works step by step:
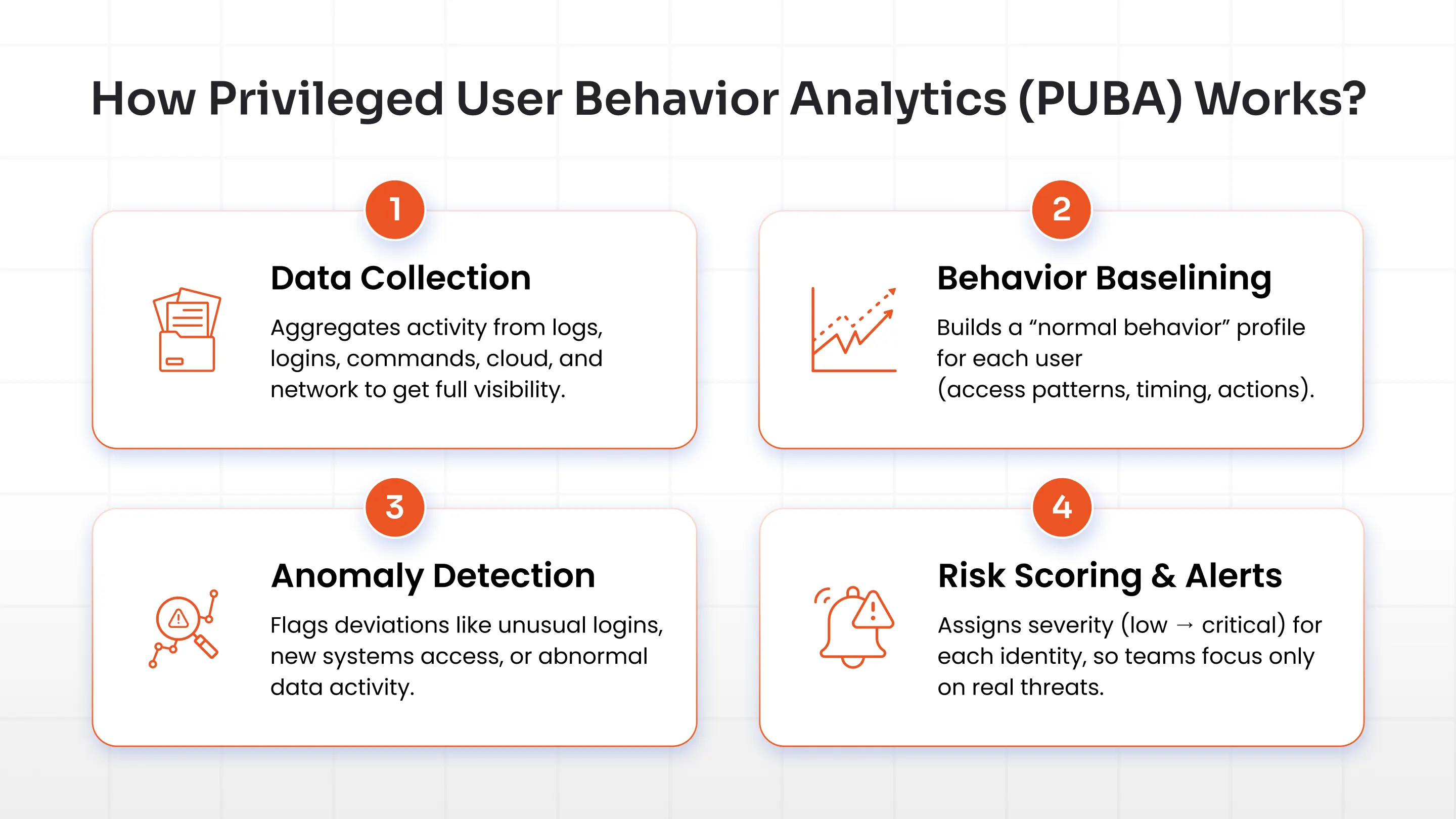
1. Data Collection
The process begins by collecting activity data from multiple sources across the environment. This includes system logs, authentication records, command history, cloud activity, and network logs. By combining data from different sources, PUBA builds a comprehensive view of how privileged users interact with systems rather than relying on individual events.
2. Behavioral Baselining
Once the data is collected, PUBA establishes a baseline of normal behavior for each privileged user. It analyzes patterns such as login times, frequently accessed systems, commands executed, and typical data transfer volumes. Over time, this baseline becomes more accurate, allowing the system to understand what is expected for each user based on their role and activity.
3. Anomaly Detection
After defining normal behavior, PUBA continuously compares real-time activity against the established baseline. Any deviation from expected patterns is flagged as a potential anomaly. For example, unusual login times, access to unfamiliar systems, large data downloads, or attempts to escalate privileges can indicate suspicious activity. This approach helps identify risks that traditional rule-based systems often miss.
4. Risk Scoring and Alerts
Not every anomaly carries the same level of risk. PUBA assigns a risk score to each activity based on its severity and context. For instance, a login from an unusual location may be considered medium risk, while mass data export or deletion of security logs may be classified as high or critical. This prioritization helps security teams focus on the most important threats without being overwhelmed by excessive alerts.
Key Capabilities of Privileged User Behavior Analytics
PUBA platforms provide continuous visibility into privileged activity and help security teams detect threats more effectively. Instead of relying on static rules, they analyze behavior patterns to identify risks as they develop.
Here are some of the key capabilities of Privileged User Behavior Analytics:
- Behavioral Baselining: PUBA builds a profile of normal activity for each privileged user by analyzing patterns such as login behavior, system access, and command usage over time. A clear understanding of expected behavior makes it easier to identify deviations that may indicate potential risk.
- Real-Time Monitoring: Privileged user activity is continuously tracked across systems, applications, and environments without interruption. Suspicious actions are identified as they occur, enabling faster response instead of delayed reaction after an incident.
- Risk Scoring: Each activity is evaluated based on its context and assigned a risk level that reflects its potential impact. High-risk actions are prioritized, allowing security teams to focus on critical issues instead of reviewing every alert equally.
- Insider Threat Detection: Behavioral analysis helps identify unusual or risky actions from internal users, whether intentional or accidental. Early detection is important because insiders already have access, making misuse harder to detect through traditional methods.
- Compliance Reporting: All privileged activities are logged and organized to provide clear visibility into user actions. These records support audit requirements, improve accountability, and simplify compliance reporting.
Common Security Threats Detected by Privileged User Behavior Analytics
Privileged User Behavior Analytics is particularly effective at identifying threats that involve misuse of privileged access. By analyzing behavior patterns instead of relying only on rules, it can detect risks that are often missed by traditional security tools.
Here are some of the most common security threats it helps detect:
1. Credential Theft
Stolen admin credentials are often used to access systems from unusual locations, devices, or at unexpected times. Attackers may appear as legitimate users, making such activity difficult to detect using basic authentication checks. Privileged User Behavior Analytics identifies these anomalies by comparing login behavior against established patterns, helping flag access attempts that do not match normal usage.
2. Insider Threats
Employees with legitimate access may misuse it, either intentionally or due to negligence. This can include accessing sensitive data without a valid reason or downloading information beyond their role requirements. Behavioral analysis helps detect such patterns by identifying unusual actions, such as accessing unfamiliar systems or handling data in ways that differ from typical behavior.
3. Privilege Escalation
After gaining initial access, attackers often attempt to increase their privileges to gain deeper control over systems. This may involve accessing restricted resources or attempting unauthorized administrative actions. Such behavior is known as privileged escalation and can be identified by detecting deviations from normal access patterns, such as sudden changes in permissions or attempts to execute unfamiliar commands.
4. Data Exfiltration
Large or unusual data transfers can indicate an attempt to move sensitive information outside the organization. These actions may appear legitimate at first glance, especially when performed by privileged users. Behavioral analytics helps identify these risks by monitoring data movement patterns and flagging activity that exceeds normal thresholds, such as unusually large downloads or repeated access in a short period.
Benefits of Privileged User Behavior Analytics
Privileged User Behavior Analytics improves security by adding context to how user activity is analyzed. Instead of looking at isolated events, it evaluates behavior over time, making it easier to identify risks that would otherwise go unnoticed.
Here are some of the key benefits:
- Early Threat Detection: Unusual behavior can be identified at an early stage, before it develops into a larger issue or security incident. This allows security teams to respond quickly and take corrective action before any real damage is done.
- Insider Threat Prevention: Monitoring behavior patterns makes it easier to detect risks from users who already have legitimate access. Suspicious actions, whether intentional or accidental, can be identified early and addressed before they escalate.
- Reduced Alert Fatigue: Instead of generating a large number of alerts, activities are evaluated based on context and risk level. This helps security teams focus on what matters most without being overwhelmed by low-priority alerts.
- Compliance Readiness: Tracking privileged activity in a structured way provides clear visibility into access and actions across systems. These records make it easier to demonstrate compliance and simplify audit processes.
- Stronger Identity Security: Continuous monitoring of privileged access ensures that user activity remains aligned with expected behavior. This strengthens overall identity security and reduces the chances of misuse or unauthorized access.
Privileged User Behavior Analytics in miniOrange PAM
Static policies and basic access controls can only go so far. To stay ahead of threats, organizations need clear visibility into how privileged access is actually being used across systems. This is where Privileged User Behavior Analytics becomes essential.
miniOrange PAM integrates behavior analytics directly into privileged access management, allowing organizations to monitor, analyze, and control privileged activity from a single platform. It brings together privileged access management, identity analytics, Anomaly detection and continuous monitoring to provide a more complete view of user behavior.
Capabilities such as real-time activity tracking, behavioral analysis of privileged users, risk-based alerting, and audit-ready reporting give security teams the visibility needed to identify and respond to suspicious activity quickly.
With miniOrange Privileged Access Management solution’s User Behavior Analytics capabilities, organizations can detect risks early and take proactive steps to reduce potential impact instead of reacting after an incident.
FAQs
What is privileged user behavior analytics?
Privileged User Behavior Analytics (PUBA) is a security approach that monitors and analyzes the behavior of users with elevated access to detect anomalies and potential threats.
How does user behavior analytics work?
It collects user activity data, builds a baseline of normal behavior, and identifies deviations using anomaly detection and risk scoring.
What is the difference between UEBA and EDR?
UEBA focuses on analyzing user behavior to detect anomalies, while EDR monitors endpoints to detect and respond to threats at the device level.
What is the difference between SIEM and UEBA?
SIEM collects and correlates logs, while UEBA adds behavioral analysis to detect anomalies and insider threats.
Is Splunk a UEBA tool?
Splunk is primarily a SIEM platform but can support UEBA capabilities through additional integrations and modules.


Leave a Comment