Access issues don’t usually come from one big mistake. They build up over time through small decisions. Temporary access gets extended, roles change but permissions stay the same, and vendor accounts remain active longer than expected. Individually, these situations don’t seem urgent but over time, they make it difficult to track who has access to what, and whether that access is still required.
This is where access certification becomes important. It provides a structured way to review access regularly and correct it before it turns into a security or compliance issue. In this blog, we will explore what access certification is, how it works, why it matters, and how to implement it effectively.
What is Access Certification?
Access certification is the process of reviewing and validating user access to systems, applications, and data to ensure it is appropriate, necessary, and aligned with their role. It is also known as User Access Review or Account Attestation.
In simple terms, access certification helps answer: Does this user still need this level of access?
Within Identity and Access Management (IAM), access certification acts as a control mechanism. While IAM systems grant access, certification ensures that access remains accurate over time.
Without this step, access tends to accumulate, creating unnecessary permissions and increasing the risk of misuse or exposure.
Why Access Certification is Important?
Access certification is not just a checkbox for compliance. It directly improves how access is managed across the organization. Here are the key reasons why access certification is important:
- Prevents Privilege Creep: Over time, users accumulate access as they change roles or take on new responsibilities. Without regular reviews, old permissions remain active, leading to excessive access. Access certification helps identify and remove these permissions, ensuring users only have what they actually need.
- Reduces Insider Threats: When users have more access than required, the risk of misuse increases. This could be accidental or intentional. By regularly validating access, organizations reduce the chances of internal misuse and limit the impact of compromised accounts.
- Ensures Compliance: Regulatory frameworks like SOX, GDPR, HIPAA, and ISO 27001 require organizations to review access periodically. Access certification provides documented proof that access is being reviewed and controlled. This makes audits smoother and reduces compliance risks.
- Improves Visibility: In many setups, access data is spread across multiple systems. Access certification brings this information together, giving a clearer view of who has access to what and where inconsistencies exist.
How Does Access Certification Work?
Access certification follows a structured workflow that runs at regular intervals or is triggered by specific events. Each step ensures that access remains accurate, relevant, and aligned with current roles and responsibilities.
Here’s a step-by-step breakdown of how the process works:
1. Define Scope
The process begins by deciding what needs to be reviewed. This could include all users across the organization, specific departments, critical applications, or high-risk accounts such as administrators.
Defining the scope clearly helps keep the process focused and ensures that reviews are manageable. It also allows organizations to prioritize sensitive systems and avoid reviewing everything at once without context.
2. Collect Access Data
Once the scope is defined, access data is gathered from different systems. This includes user roles, permissions, application access, group memberships, and privileged entitlements.
Since this data is often distributed across multiple systems, collecting it manually can be time-consuming. This is why many organizations rely on integrations or automated tools to bring all access data into a single view.
3. Assign Reviewers
The next step is assigning the right reviewers. These are typically individuals who understand the purpose of access, such as managers, application owners, or security teams.
Choosing the right reviewers is important because they have the context needed to make accurate decisions. Without proper context, reviewers may approve access unnecessarily or revoke access that is still required.
4. Review and Decision
Reviewers evaluate each access entry and decide whether it should be approved, revoked, or modified based on the user’s current role and responsibilities.
For example, access may be retained if it is still relevant, removed if it is no longer needed, or adjusted if the user’s role has changed. This step requires clear visibility into what each permission means to avoid incorrect decisions.
5. Remediation
After decisions are made, the next step is to apply the necessary changes. Access that is no longer required should be removed, and any updates should be implemented without delay.
Timely remediation is critical. If changes are not enforced quickly, unnecessary access may continue to exist, which defeats the purpose of the review process.
6. Audit and Reporting
All actions taken during the process are recorded. This includes who performed the review, what decisions were made, and when changes were implemented.
These records are essential for audits and help organizations demonstrate compliance. They also provide long-term visibility into access patterns and how access is managed over time.
Types of Access Certification
Access certification can be applied in different ways depending on what needs to be reviewed. Each type focuses on a specific aspect of access, helping organizations maintain better control across users, systems, and roles.
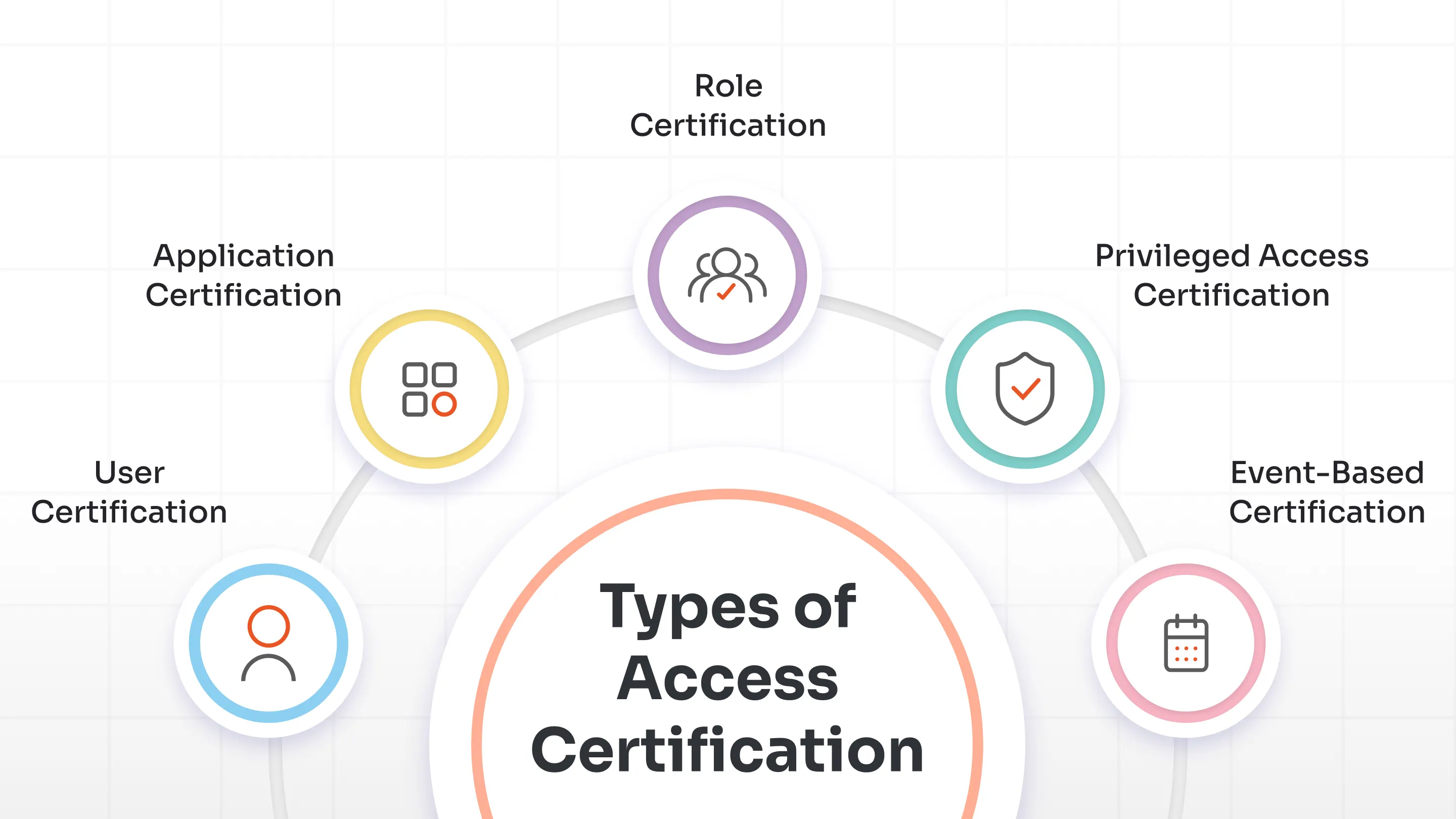
Below are the key types of access certification:
1. User Certification
User certification focuses on individual users and the access assigned to them across systems and applications.
For example, a manager may be asked to review whether an employee still needs access to all the tools and systems they currently use.
This is the most commonly used type of certification because it provides a user-centric view. It helps ensure that access stays aligned with a person’s role and responsibilities as they change over time.
2. Application Certification
Application certification focuses on access to a specific application or system.
For example, an application owner may review who has access to a finance or HR system and decide whether that access is still required.
This type of certification is useful for maintaining control over critical systems. It ensures that only the right users have access to sensitive applications and reduces the risk of unauthorized usage.
3. Role Certification
Role certification focuses on roles and the permissions associated with them, rather than individual users.
For example, a team may review whether a particular role includes permissions that are no longer needed or are too broad.
This helps ensure that roles remain clean and well-defined. If roles are not reviewed regularly, they can become overly permissive, which can impact multiple users at once.
4. Privileged Access Certification
Privileged access certification focuses on high-risk accounts, such as administrators or users with elevated permissions.
For example, organizations may review who has admin access and whether that level of access is still justified.
This type of certification is critical because privileged accounts have the highest level of control. If misused or compromised, they can cause significant damage, making regular reviews essential.
5. Event-Based Certification
Event-based certification is triggered by specific changes instead of running on a fixed schedule.
Common triggers include role changes, employee exits, or the introduction of a new system.
This approach ensures that access is reviewed at the right time, especially when something changes. It helps close gaps that may exist between periodic review cycles.
Access Certification vs Access Review vs Provisioning
| Feature | Access Certification | Access Review | Provisioning |
|---|---|---|---|
| Purpose | Validate access | Review access | Grant access |
| Frequency | Periodic | Ad-hoc | On-demand |
| Compliance Impact | High | Medium | Low |
While Access Certification, Access Review, and Provisioning are often used interchangeably, they serve very different purposes in managing user access.
Access Certification is a structured and formal process designed for compliance and governance. It typically runs at defined intervals, follows a workflow, and requires reviewers to validate whether access is still appropriate. Every decision is tracked, creating an audit trail that organizations can use during compliance checks.
Access Review, on the other hand, is more flexible and less formal. It may happen on demand or as part of routine checks without a defined process or strict documentation. While it helps identify obvious issues, it does not always provide the level of accountability or audit readiness required for compliance.
Provisioning focuses on granting access rather than validating it. When a user joins, changes roles, or requests access as part of the JML (Joiner, Mover, Leaver) lifecycle, provisioning ensures they receive the required permissions. However, it does not check whether that access should continue over time, which is where certification becomes important.
To put it simply, each serves a different role in the access lifecycle. Provisioning gives users access, Access Certification ensures that access remains valid over time, and Access Review helps with ongoing monitoring and quick checks between certification cycles.
Together, these processes create a complete cycle:
Provisioning grants access → Access Certification validates it → Access Review supports continuous monitoring.
Key Benefits of Access Certification
Access certification helps organizations stay in control of who has access to what, while reducing risk and keeping permissions aligned with current roles and responsibilities.
Below are the key benefits of access certification:
- Enforces Least Privilege: Over time, users tend to accumulate access as their roles change. Access certification helps identify and remove permissions that are no longer needed, ensuring users retain only the minimum level of access required for their role. By enforcing the principle of least privilege, it reduces unnecessary exposure across systems and lowers the chances of misuse.
- Improves Compliance: Regulations require organizations to review access regularly and maintain clear records of those reviews. Access certification provides that documentation, making it easier to demonstrate compliance during audits. As a result, audit processes become smoother and compliance risks are reduced.
- Reduces Risk of Breaches: Outdated or excessive access increases the chances of misuse or compromise. Regular certification helps identify and remove such access before it turns into a security issue. By limiting unnecessary permissions, organizations reduce their overall attack surface.
- Enhances Audit Readiness: Every review and decision is recorded as part of the certification process, creating a clear and traceable audit trail. This makes it easier to provide evidence during audits without last-minute effort. Consistent documentation also ensures that audit requirements are met over time.
- Supports Governance Automation: When integrated with IGA tools, access certification can be automated across systems, reducing the need for manual tracking and follow-ups. This makes reviews more consistent and easier to manage at scale. It also allows teams to focus on higher-priority tasks instead of repetitive administrative work.
Access Certification Use Cases
Access certification applies across multiple scenarios where access needs to be reviewed, validated, and controlled over time.
Below are the key use cases of access certification:
- Employee Lifecycle Management: As a part of user lifecycle management, Access certification ensures users receive the right access when they join and that it stays aligned as their roles change over time. It also helps remove access promptly during offboarding, reducing the risk of unused or lingering permissions. This keeps access consistent with job responsibilities at every stage of the employee lifecycle.
- Privileged Access Reviews: Admin and high-risk accounts require closer monitoring due to the level of control they provide. Regular certification helps verify whether such access is still justified and reduces the chances of misuse or over-privileged users. This is especially important for protecting critical systems and sensitive data.
- Third-Party Access Control: Vendors and contractors often need temporary access to systems and data to complete specific tasks. Access certification ensures that their access is reviewed regularly and removed once their work is complete. This prevents external users from retaining access longer than necessary.
- Cloud and SaaS Access: With multiple cloud applications in use, tracking access across platforms can become difficult. Access certification helps maintain visibility and ensures that only authorized users have access to these systems. It also helps identify unused or excessive access across SaaS environments.
- Regulatory Compliance: Many regulations require organizations to validate access on a regular basis and maintain proper records. Access certification supports compliance by ensuring access is reviewed, controlled, and documented consistently. This makes it easier to demonstrate accountability during audits.
Common Challenges in Access Certification
While access certification is essential for maintaining control and compliance, it is not always easy to implement in practice. As organizations grow and systems become more complex, managing access reviews can become time-consuming and difficult to scale.
Below are the common challenges in access certification:
1. Manual Processes
Many organizations still rely on spreadsheets or manual tracking methods to conduct access reviews. This approach is not only time-consuming but also increases the chances of errors and inconsistencies. As the number of users and systems grows, managing access manually becomes harder, making the process inefficient and difficult to maintain at scale.
2. Reviewer Fatigue
Access certification often involves reviewing large volumes of access data, which can overwhelm reviewers. When too many reviews are assigned without proper context, decisions may be rushed or made without thorough validation. Over time, this can lead to incorrect approvals, reducing the effectiveness of the entire certification process.
3. Delayed Remediation
Even when unnecessary access is identified, it is not always removed immediately. Delays in implementing changes can leave security gaps, allowing users to retain access longer than required. This reduces the effectiveness of access certification, as identified risks are not addressed in a timely manner.
4. Limited Visibility
Access data is often distributed across multiple systems, applications, and environments. This makes it difficult to get a complete and accurate view of who has access to what. Without centralized visibility, reviews can become incomplete or inconsistent, leading to missed risks.
5. Complex IT Environments
Modern organizations operate across a mix of on-premise, cloud, and hybrid systems. Managing access across these environments adds layers of complexity to the certification process. Different systems may have different access models, making it harder to standardize and manage access reviews effectively.
Access Certification Best Practices
Access certification works best when it is structured, consistent, and aligned with how access is actually used across the organization. Without the right approach, reviews can become inefficient, incomplete, or difficult to manage at scale.
Here are some best practices to follow for effective access certification:
1. Automate Certification Campaigns
Manual access reviews can quickly become time-consuming and difficult to manage as the number of users and systems grows. Automating certification campaigns helps streamline the process and ensures reviews are conducted consistently across the organization. It also reduces the chances of errors and allows teams to focus on decision-making instead of administrative tasks.
2. Use Risk-Based Prioritization
Not all access carries the same level of risk, and treating everything equally can make the process inefficient. Focusing on high-risk users, sensitive systems, and critical permissions helps prioritize what matters most. This approach ensures that review efforts are directed where they have the greatest impact.
3. Include Non-Human Identities
Access is not limited to human users, as Non-Human Identities such as service accounts and machine identities also interact with systems and data. These identities often have persistent access, which can go unnoticed if not reviewed regularly. Including them in certification processes helps close potential gaps and improves overall security.
4. Combine Periodic and Event-Based Reviews
Relying only on scheduled reviews can leave gaps when changes occur between cycles. Combining periodic certification with event-based triggers ensures that access is reviewed both regularly and when important changes happen. This creates a more responsive and complete approach to access validation.
5. Maintain Detailed Audit Logs
Keeping accurate records of access reviews, decisions, and changes is essential for both visibility and compliance. Detailed audit logs provide a clear history of actions taken and help demonstrate accountability. They also make it easier to prepare for audits without last-minute effort.
Access Certification & Compliance
Access certification plays a critical role in helping organizations meet regulatory and compliance requirements. Most frameworks expect organizations to not only control access but also review it regularly and maintain clear records of those reviews.
Access certification supports this by providing a structured way to validate who has access to what, why that access exists, and whether it is still appropriate. It also creates an audit trail that proves access is being monitored and managed consistently.
Here’s how access certification aligns with key compliance frameworks:
SOX (Sarbanes-Oxley Act)
SOX focuses on protecting financial data and ensuring the integrity of financial reporting systems. It requires organizations to strictly control who can access financial systems and to regularly review those permissions. Access certification helps validate that only authorized users have access and that permissions are not excessive or outdated.
GDPR (General Data Protection Regulation)
GDPR emphasizes the protection of personal data and requires organizations to limit access to only those who need it. Access certification ensures that personal data is only accessible to authorized users and that access is reviewed regularly. This helps reduce the risk of data exposure and supports accountability in handling sensitive information.
HIPAA (Health Insurance Portability and Accountability Act)
HIPAA requires organizations in the healthcare sector to protect patient data through strict access controls. Access certification helps ensure that only authorized personnel can access sensitive health information and that access is reviewed periodically to prevent misuse or overexposure.
ISO 27001
ISO 27001 is an information security standard that requires organizations to implement strong access control policies and regularly review user access. Access certification supports this by validating access rights, ensuring they align with business roles, and maintaining documentation for audits.
Without access certification, it becomes difficult for organizations to demonstrate that access is being properly managed and controlled. This not only increases compliance risk but also weakens overall security by allowing unnecessary or outdated access to remain active.
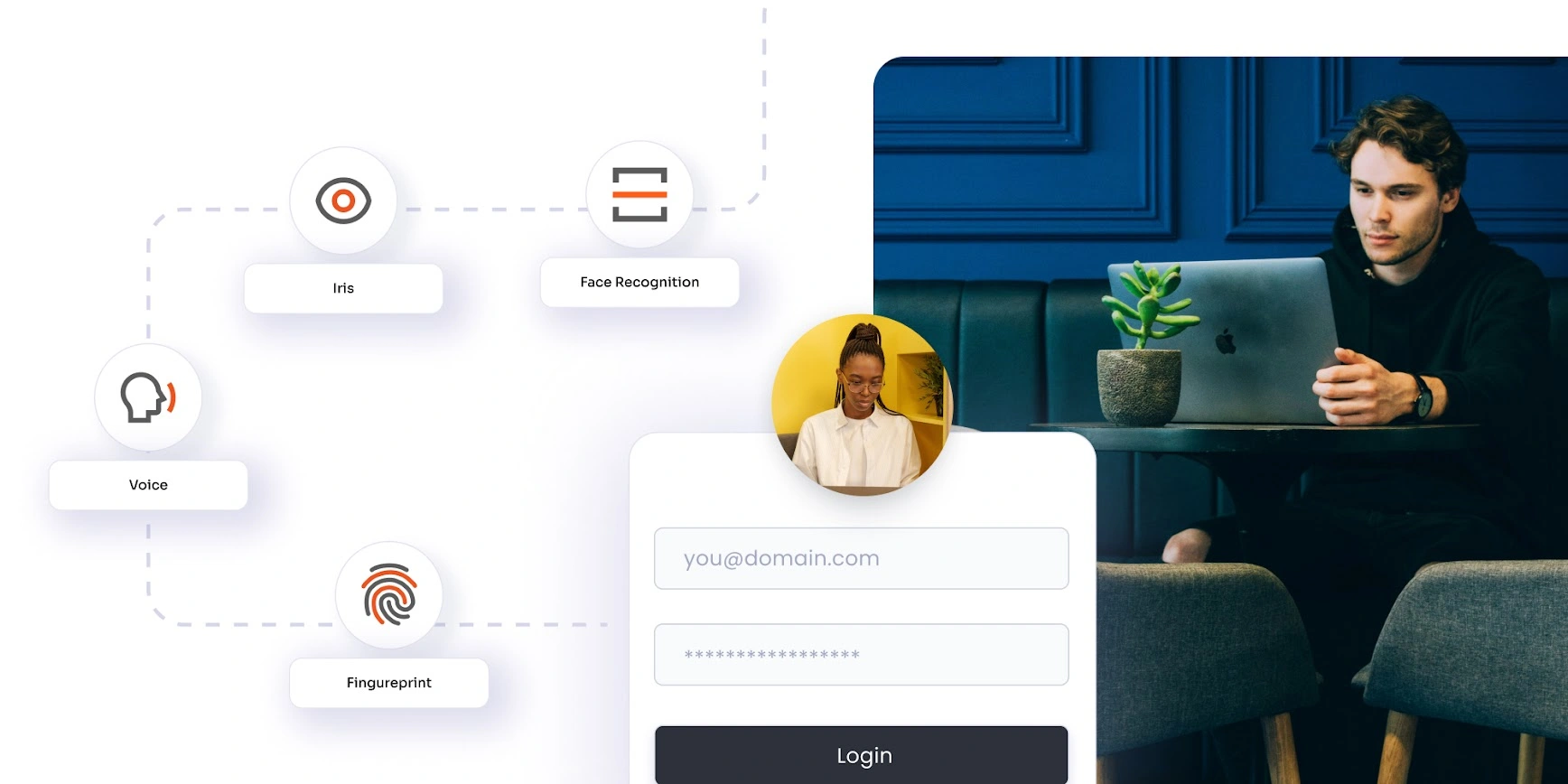
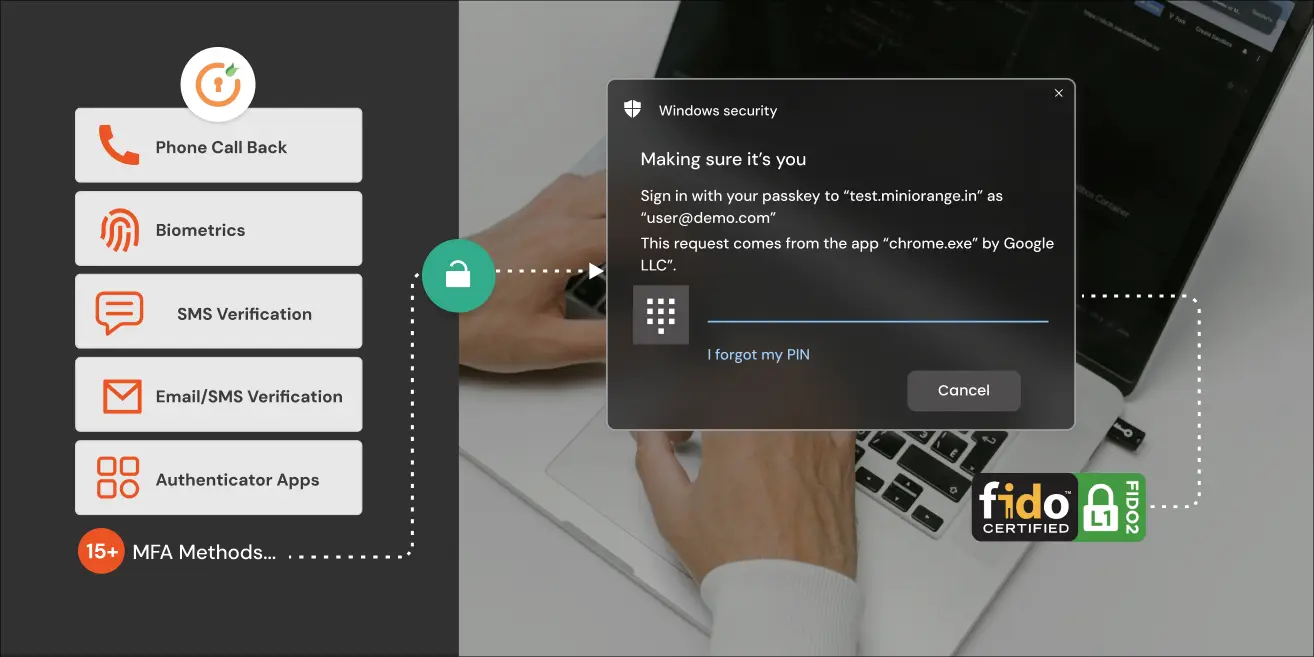
Streamline Compliance with miniOrange IGA Solution
As organizations grow, managing access manually becomes increasingly difficult. More users, more applications, and more systems mean access data is spread across multiple places. Tracking who has access to what, and keeping it updated, turns into a time-consuming and error-prone process.
This is where Identity Governance and Administration (IGA) comes in.
IGA provides a structured way to manage the entire access lifecycle, from provisioning to certification and compliance. Instead of relying on manual reviews and disconnected systems, organizations can centralize access management, automate reviews, and maintain consistent control across environments.
miniOrange Identity Governance and Administration (IGA) builds on this approach by offering a unified platform to manage identities, access, and compliance from a single place.
It integrates seamlessly with:
- Role-Based Access Control (RBAC)
- Privileged Access Management (PAM)
- Identity lifecycle management
With features like automated access certification campaigns and continuous access reviews, organizations can ensure that access stays aligned with roles and policies without relying on manual processes.
This not only reduces operational effort but also improves visibility, consistency, and decision accuracy across access reviews.
FAQs
How often should access certification be done?
Access certification is usually performed quarterly or bi-annually, depending on the organization and compliance requirements. High-risk systems or privileged accounts may require more frequent reviews.
Who performs access certification?
Access certification is typically performed by managers, application owners, or security teams. These reviewers understand the context of access and decide whether it should be approved, modified, or removed.
What is the difference between access review and access certification?
Access certification is a formal, structured process with defined workflows and audit trails, mainly used for compliance. Access reviews are more informal and may not always include strict tracking or documentation.
Is access certification required for compliance?
Yes, most regulatory frameworks such as SOX, GDPR, HIPAA, and ISO 27001 require organizations to regularly review and validate user access as part of compliance.
What is identity governance certification?
Identity governance certification refers to the use of Identity Governance and Administration (IGA) solutions to automate and manage access certification processes. It helps organizations enforce policies, run certification campaigns, and maintain audit-ready records.
Access review vs certification: what’s the difference?
Access reviews are general checks to verify access, while access certification is a formal process designed for governance and compliance. Certification includes structured workflows, approvals, and audit logs.
What are access certification tools?
Access certification tools are part of IAM or IGA solutions that help automate access reviews, assign reviewers, track decisions, and generate audit reports. These tools simplify large-scale access management and improve accuracy.


Leave a Comment