Credential theft is one of the most common causes of security breaches today. Users reuse passwords, fall for phishing attacks, or unknowingly expose credentials through unsecured platforms. Once attackers gain access, they can move laterally across systems without much resistance.
This is why modern authentication methods rely on more than just passwords. One-Time Password (OTP) mechanisms were introduced to solve this exact problem. Instead of relying on something static, they generate temporary codes that expire quickly and cannot be reused.
Among these, OTP, TOTP, and HOTP are widely used authentication methods in cybersecurity today. Each of them follows the same principle of one-time usage, but the way they generate and validate codes is different. Understanding this difference is key to choosing the right method.
In this blog, we’ll break down the difference between OTP, TOTP, and HOTP so you can clearly understand how each one works and when to use them.
What is One-Time Password (OTP)?
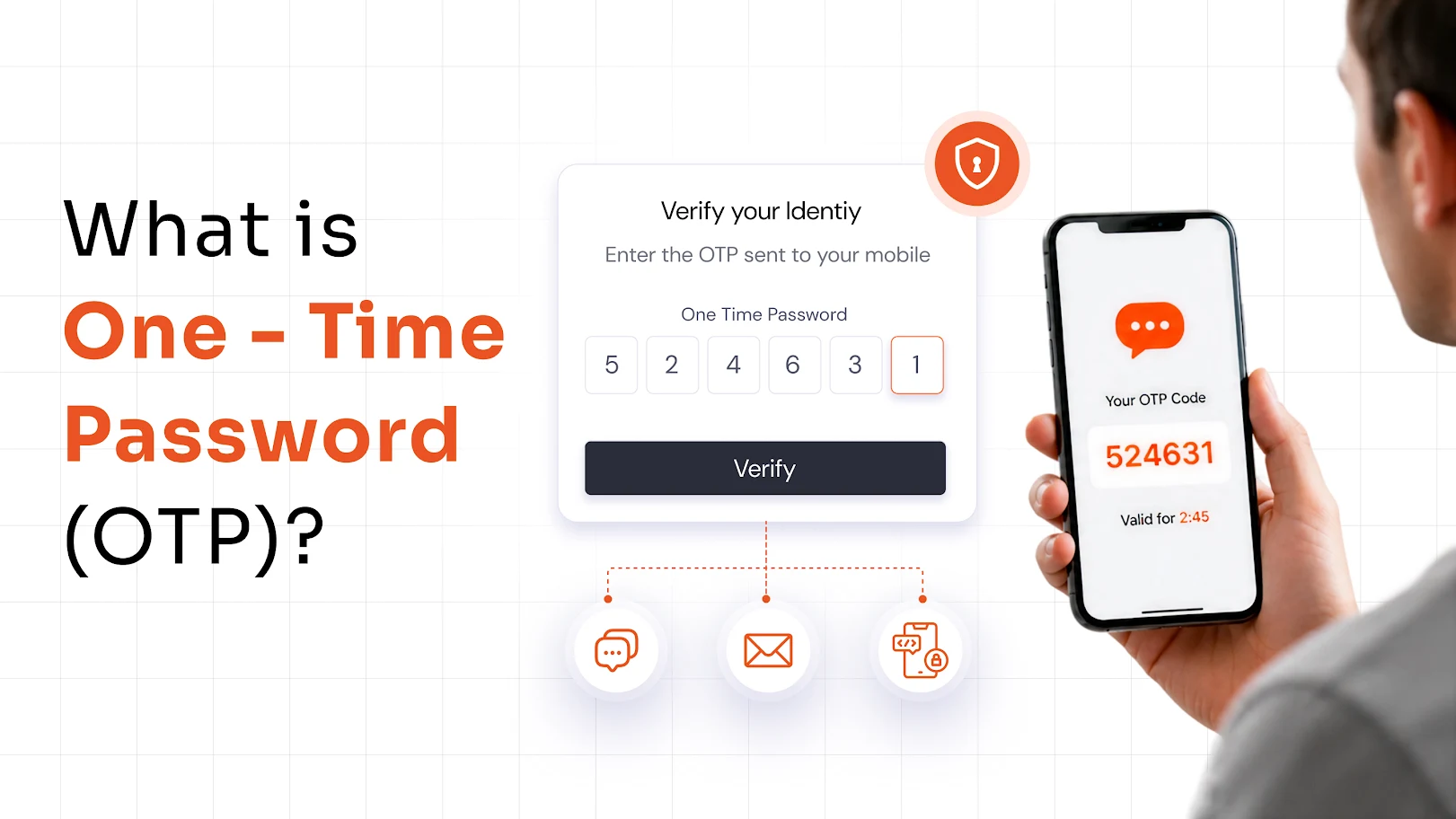
A One-Time Password (OTP) is a temporary code used to verify a user’s identity during login or a transaction. Unlike static passwords, it is valid for a single use and expires quickly, which makes it more secure against reuse and credential theft.
OTP is commonly used as a second layer of authentication, especially in scenarios where additional verification is required beyond a username and password. It is typically delivered through SMS, email, or authenticator apps, depending on the system.
How does OTP work?
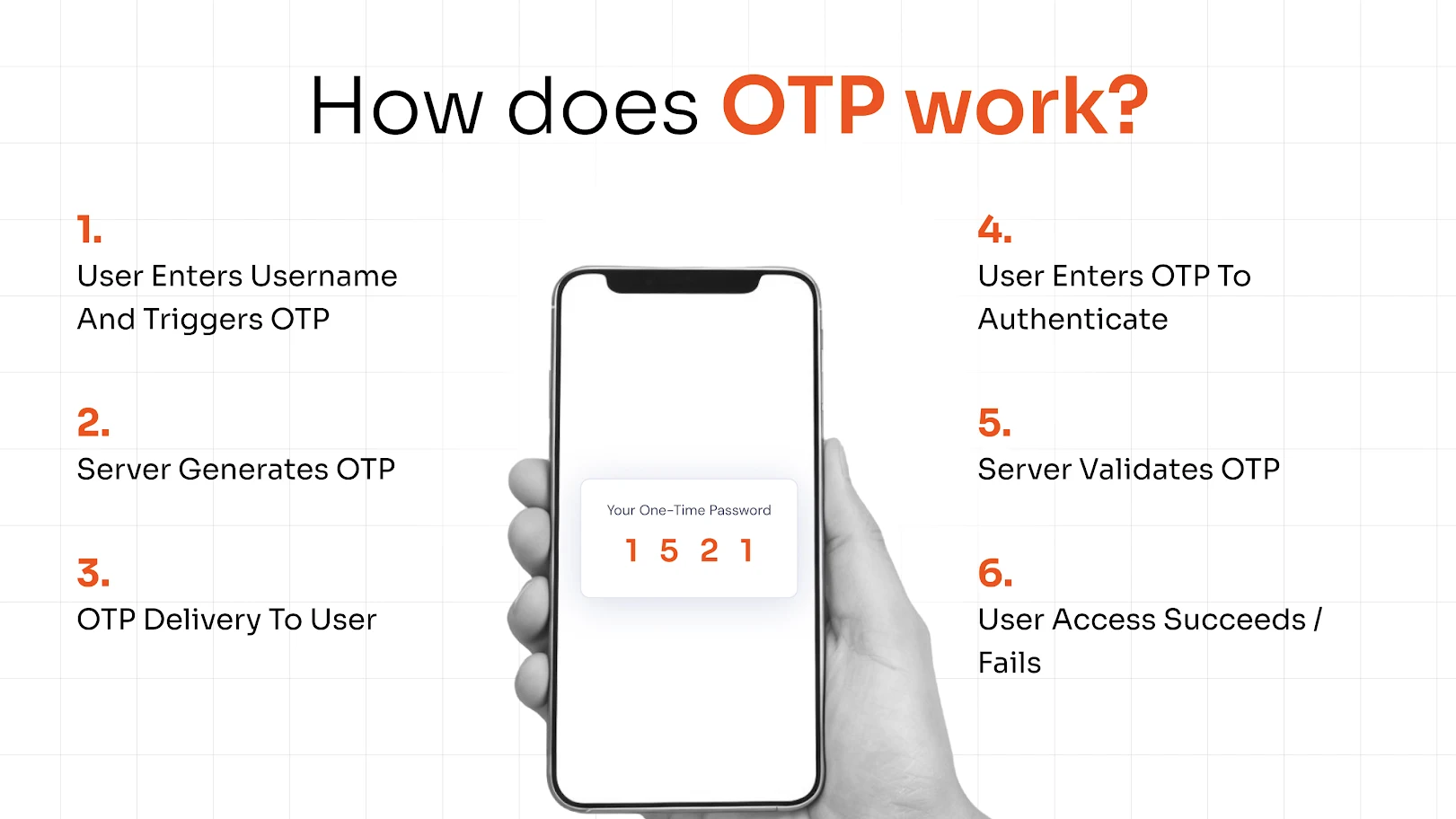
The process is simple and designed for quick verification. A user enters their login credentials, after which the system generates a one-time code. This code is sent to the user through a chosen delivery method such as SMS or email. The user then enters the code to complete authentication. Once used, the code becomes invalid and cannot be reused.
What is Time-Based One-Time Password (TOTP)?
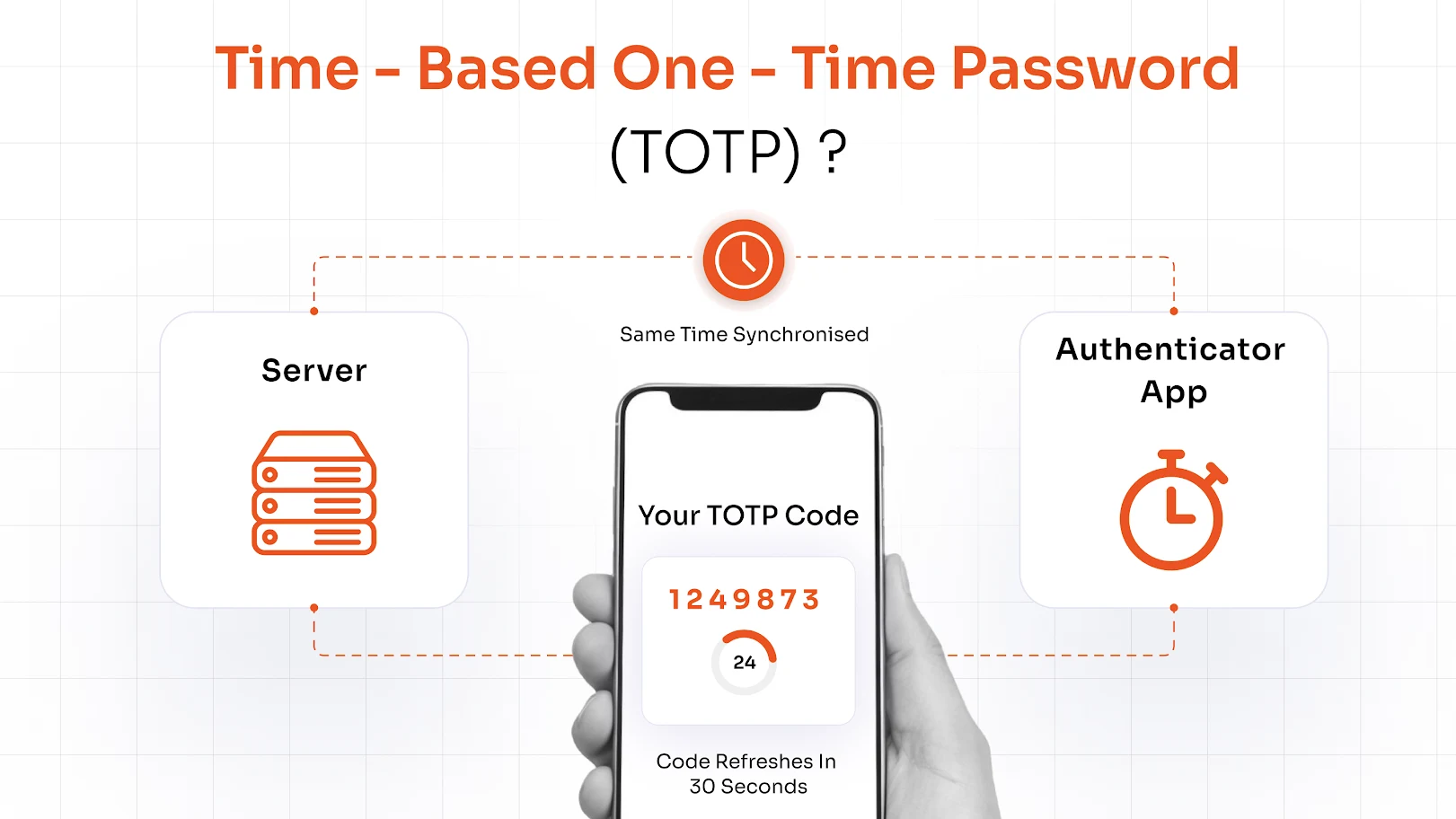
A Time-Based One-Time Password (TOTP) is a type of OTP that generates codes based on time. Instead of sending a code over a network, both the server and the user’s device generate the same code at the same time using a shared secret.
These codes typically refresh every 30 to 60 seconds, making them short-lived and difficult to exploit. Because TOTP does not rely on SMS or email delivery, it is considered more secure and is widely used in modern authentication systems.
How does TOTP work?
TOTP works by using a shared secret key stored on both the server and the user’s device, usually within an authenticator app. The system combines this secret with the current time to generate a unique code. Since both sides use the same inputs, they produce the same code simultaneously. The user simply enters the code displayed in their app, and the server verifies it within the valid time window.
What is HMAC-Based One-Time Password (HOTP)?
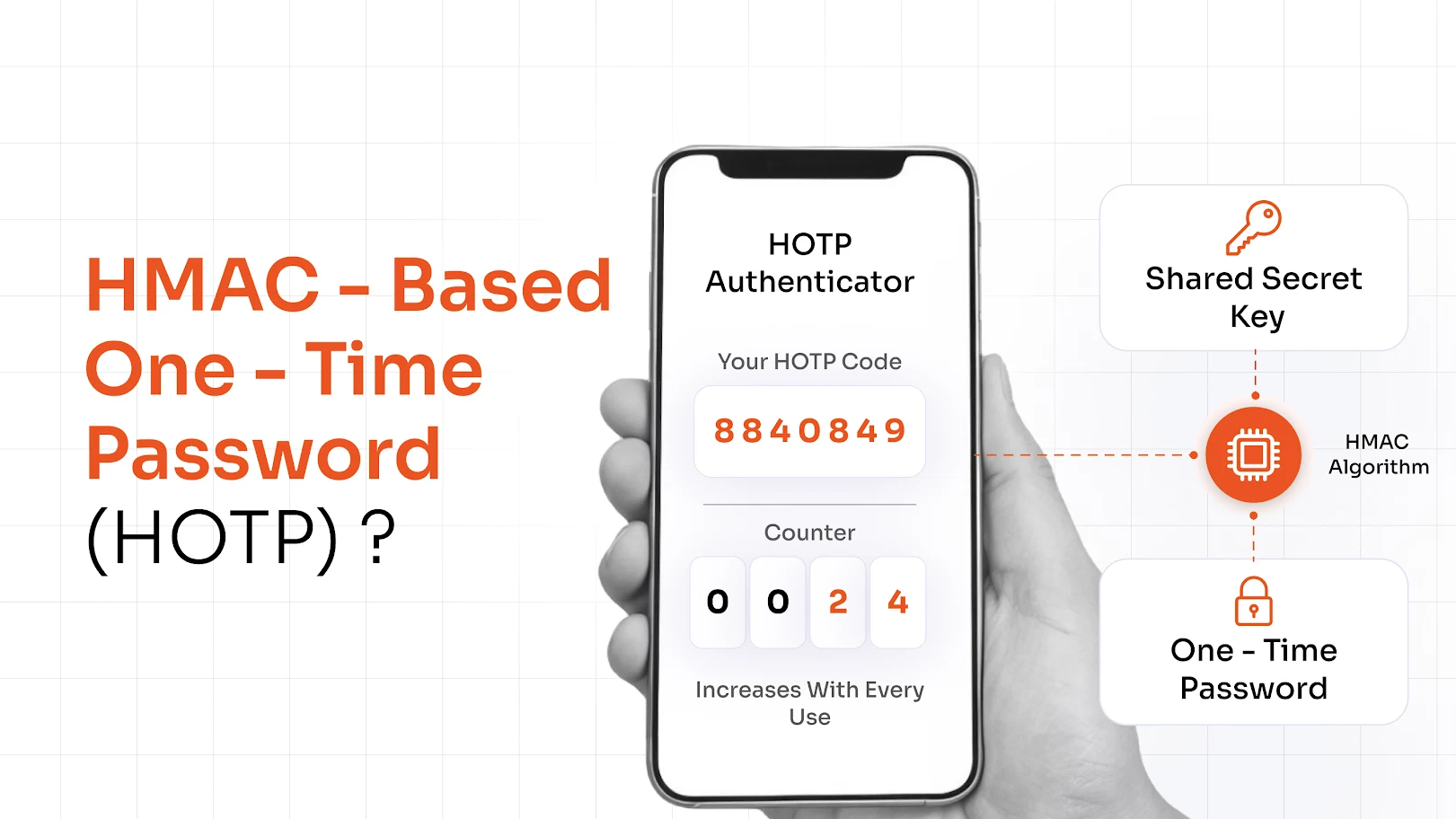
HOTP (HMAC-Based One-Time Password) is another type of OTP that generates codes based on a counter instead of time. Each time a new code is requested, the counter increases, and a new OTP is generated using a cryptographic algorithm.
Unlike time-based methods, HOTP does not rely on time synchronization. This makes it suitable for environments where devices may not have accurate or consistent time settings.
How does HOTP work?
HOTP works by using a shared secret key along with a counter value. Every time a user requests a new OTP, the counter increments, and a new code is generated. The server performs the same calculation using its own counter and verifies the code entered by the user. As long as both counters remain aligned, authentication is successful.
OTP vs TOTP vs HOTP: Key Differences
Here’s a clear comparison to understand how they differ:
| Aspect | OTP | TOTP | HOTP |
|---|---|---|---|
| Type | General one-time password | Time-based OTP | Counter-based OTP |
| Generation Method | Random or server-generated | Based on current time (e.g., 30 sec window) | Based on incrementing counter |
| Validity | Valid for a single use or short duration | Expires every 30–60 seconds | Valid until used |
| Dependency | Delivery channel (SMS/email/app) | Time synchronization | Counter synchronization |
| Security Strength | Moderate | High | High |
| Common Use Case | SMS/email verification | Authenticator apps | Hardware tokens |
| Replay Risk | Possible if intercepted | Very low due to expiry | Possible if not synced properly |
At a high level, all three methods are designed to generate one-time codes, but the way they create and validate those codes is what sets them apart.
OTP is the most basic form. It is usually generated by a server and sent to the user via SMS or email. The system verifies the code once the user enters it, and the code becomes invalid after use or after a short time. While it is simple and widely used, its security largely depends on how the code is delivered.
TOTP improves on this by removing the need for delivery altogether. Instead of sending the code, both the server and the user’s device generate the same code using the current time and a shared secret. Because the code changes every few seconds and expires automatically, it reduces the chances of interception and reuse, making it more secure.
HOTP takes a different approach by using a counter instead of time. Each new code is generated based on an incrementing value. This means the code does not expire automatically and remains valid until used. While this can be useful in certain environments, it requires proper synchronization between the server and the user’s device to work correctly.
The key difference comes down to how codes are generated and validated:
- OTP depends on delivery and one-time usage
- TOTP depends on time-based generation and expiry
- HOTP depends on counter-based generation and synchronization
Why OTP, TOTP, and HOTP are Important for Multi-Factor Authentication (MFA) in Enterprise Security?
In enterprise settings, relying on passwords alone is not sufficient to protect systems and sensitive data. Organizations use Multi-Factor Authentication (MFA) to add an additional layer of security and reduce the risk of unauthorized access.
MFA works by combining different factors such as something you know (password), something you have (OTP), or something you are (biometrics). Among these, OTP-based methods are one of the most widely used and practical second factors.
Each type of OTP plays a specific role. Basic OTPs are commonly used for quick verification through SMS or email. Time-Based One-Time Passwords (TOTP) are widely adopted in enterprise environments because they generate short-lived codes that expire quickly. HMAC-Based One-Time Passwords (HOTP) are used in controlled scenarios where counter-based generation is more suitable.
By adding this second layer, OTP, TOTP, and HOTP ensure that even if a password is compromised, access cannot be granted without additional verification. This significantly strengthens access security across enterprise systems and applications.
Advantages and Limitations of OTP, TOTP, and HOTP
Not all OTP methods offer the same level of security or usability. While they all add a second layer of authentication, the way codes are generated, delivered, and validated makes a real difference.
For enterprises, this difference is important. Each method has its own strengths and limitations, which affect how authentication works across systems and users.
OTP (One-Time Password)
A One-Time Password (OTP) is a temporary code used once to verify a user’s identity during login or a transaction. It is typically delivered via SMS, email, or sometimes through an app, making it one of the most commonly used authentication methods.
Advantages of OTP
- Easy to implement: Requires minimal setup and can be integrated quickly into existing systems
- Widely supported: Works across multiple platforms and is commonly used in banking, SaaS, and consumer applications
- User-friendly: Familiar process that users can easily understand without additional training
Limitations of OTP
- Delivery risks: SMS and email OTPs can be intercepted, phished, or exposed through SIM-swapping attacks
- Network dependency: Delays or failures in message delivery can impact login experience
- Lower security compared to app-based methods: More vulnerable than TOTP due to reliance on external channels
TOTP (Time-Based One-Time Password)
TOTP generates a one-time code based on time, usually refreshing every 30 to 60 seconds. Instead of sending the code, both the server and the user’s authenticator app generate the same code simultaneously using a shared secret.
Advantages of TOTP
- Stronger security: Codes expire quickly, reducing the risk of reuse or interception
- No dependency on delivery channels: Eliminates risks associated with SMS or email-based attacks
- Widely adopted in enterprises: Standard method used in modern MFA solutions and authenticator apps
Limitations of TOTP
- Device dependency: Requires access to a registered device, typically a smartphone
- Time synchronization requirement: Even small time mismatches can lead to authentication failures
- Recovery challenges: Losing access to the device can make account recovery more complex
HOTP (HMAC-Based One-Time Password)
HOTP generates codes using a counter instead of time. Each time a new code is requested, the counter increments, and a new OTP is generated using a shared secret.
Advantages of HOTP
- No reliance on time synchronization: Works effectively in environments where time sync is unreliable
- Suitable for hardware tokens: Commonly used in controlled enterprise environments with physical devices
- Consistent generation mechanism: Not affected by timing issues or delays
Limitations of HOTP
- Counter synchronization issues: If the server and device counters go out of sync, authentication can fail
- No automatic expiry: Codes remain valid until used, increasing potential risk if exposed
- Less convenient for users: Not as seamless as TOTP for everyday authentication scenarios
OTP vs TOTP vs HOTP: Which One Should You Choose?
The right authentication method depends on your requirements, including ease of use, security needs, and how your systems operate.
- For basic verification and ease of use: OTP works well, especially for SMS or email-based authentication. It is simple to implement and familiar to users, making it suitable for login verification and transaction approvals.
- For modern applications and stronger security: TOTP is the preferred choice. Its time-based codes expire quickly, reducing the risk of misuse and making it ideal for enterprise systems and authenticator apps.
- For specialized or controlled environments: HOTP can be useful where counter-based generation is more suitable, such as in hardware tokens or environments where time synchronization is not reliable.
In most enterprise environments today, TOTP is the standard because it offers a strong balance between security and usability. However, enterprise requirements differ. What works for one organization may not work for another.
This is why adopting a Multi-Factor Authentication (MFA) solution is important. It allows organizations to choose and configure authentication methods based on their specific requirements, instead of relying on a single approach.
Strengthen Your Enterprise Security with miniOrange MFA Solution
Passwords alone are no longer enough to secure modern enterprise environments. With increasing threats like credential theft, phishing, and account takeover attacks, organizations need stronger and more reliable authentication methods.
This is where Multi-Factor Authentication (MFA) becomes essential.
By combining multiple authentication factors, MFA ensures that access is not granted based on a password alone. Methods like OTP, TOTP, and HOTP add an extra layer of verification, making it significantly harder for unauthorized users to gain access to systems and sensitive data.
However, managing different authentication methods across users, devices, and applications can quickly become complex.
miniOrange MFA solution simplifies this by providing a unified platform to manage multiple authentication methods from a single place. It supports a wide range of MFA methods, including OTP, TOTP, push notifications, biometrics, and more, allowing organizations to choose the right approach based on their security and usability requirements.
With miniOrange MFA, enterprises can:
- Secure access across cloud, on-premise, and hybrid environments
- Enable flexible authentication methods for different user groups
- Reduce dependency on passwords and minimize identity-based risks
- Ensure a consistent and scalable authentication experience
Instead of relying on a single method, organizations can adapt authentication strategies based on risk, use case, and user behavior.
FAQs
What is the difference between OTP, TOTP, and HOTP?
OTP is a general one-time password, TOTP is time-based, and HOTP is counter-based. The difference lies in how the codes are generated and validated.
Is TOTP more secure than HOTP?
Yes, TOTP is generally more secure because codes expire quickly, reducing the risk of reuse or replay attacks.
Where is HOTP used in cybersecurity?
HOTP is commonly used in hardware tokens and systems where time synchronization is not reliable.
What is TOTP authentication and how does it work?
TOTP authentication generates time-based codes that change every few seconds. Both the server and user device generate the same code using a shared secret.
Leave a Comment