A company spends months building trust with its customers. A single breach can erase it in hours.
In 2025, the average data breach in the United States cost businesses a record $10.22 million. Globally, 425.7 million accounts were breached, equating to roughly 810 breaches every single minute.
To the everyday operations of an organization, these numbers represent
- halted payrolls by ransomware
- Systems knocked offline
- Customer data sold on dark-web markets.
But what changed so dramatically coming into 2026?
Speed and automation.
AI-driven attacks now move faster than before, and attackers use the same machine-learning pipelines that defenders rely on, but with a head start. The traditional idea that a strong firewall keeps threats out is effectively obsolete. At miniOrange, we work with the fact that data lives in the cloud now, and every device is, potentially, an entry point.
So where do you start? With the fundamentals. Because the most expensive breaches in history often trace back to the most preventable mistakes.
Key Takeaways
- The average US data breach cost $10.22 million in 2025. Phishing, weak passwords, and unpatched systems remain the primary cause.
- Human-layer practices (MFA, phishing training, password hygiene) and technical controls (patching, UEM, DLP) must work together; neither alone is sufficient.
- Zero Trust Architecture in 2026 is baseline of cybersecurity practices: trust nothing, verify everything.
- Agentic AI & quantum risk are the emerging threats that forward-looking security programs must address.
4 Common but Critical Cybersecurity Best Practices for Employees (The Human Layer)
No matter how sophisticated your tech stack, humans remain the most targeted layer in any attack chain. Therefore, the following cybersecurity best practices address the human side.
1. Phishing Awareness & Social Engineering Defense
Phishing caused 16% of all 2025 data breaches, with an average cost of $4.8 million per incident. Attackers no longer send typo-filled emails from strange addresses. AI-generated phishing emails now mimic colleagues, clients, and even internal IT teams with near-perfect accuracy, & social engineering attacks have evolved alongside them, targeting human psychology as reliably as any technical vulnerability.
- Train employees to understand how phishing attacks are structured.
- Run simulated phishing campaigns to test and improve employee response.
- Establish a clear process for reporting suspicious emails, and make it easy enough that employees actually use it.
2. Strengthen Password Hygiene
In 2025, a single "mega-leak" exposed over 16 billion login credentials aggregated from infostealer malware datasets. Reusing passwords across platforms transforms one compromised credential into a skeleton key for dozens of accounts.
- Require unique, complex passwords (minimum 16 characters) for every account, never reuse across platforms.
- Deploy a password manager organization-wide, so employees have no excuse for weak or repeated passwords.
- Periodically audit accounts for dormant or default credentials that often go undetected and become attacker entry points.
3. Enforce Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is not an optional suggestion anymore. Passwords alone are insufficient in this era of phishing kits, credential stuffing, & large scale password leaks. MDA, with an additional verification layer, reduces the success rate of credential-based attacks.
- Mandate MFA Solution across all systems, especially email, VPN, cloud services, and financial platforms.
- Prefer hardware tokens or authenticator apps over SMS, which is susceptible to SIM-swapping attacks.
- Consider adopting passwordless authentication and biometric verification as MFA evolves toward identity-driven access controls.
4. Secure Remote Work & Wi-Fi Protection
Hybrid and remote work environments have permanently expanded the attack surface. Employees connecting from home networks, coffee shops, or airport lounges introduce risks that enterprise firewalls cannot address.
- Require VPN usage on all non-corporate networks, with split-tunneling disabled to prevent data leaks.
- Encourage employees to secure home routers with strong, unique passwords and WPA3 encryption where possible.
- Issue company-managed devices with pre-configured security policies rather than relying on personal devices for sensitive work.
6 Tech-Focused Cybersecurity Best Practices (The Infrastructure Layer)
If your underlying technology is misconfigured, unpatched, or poorly architected, strong human practice isn't going to make a difference. Therefore, the following cyber security best practices address the infrastructure side.
1. Patch Management & Automated Updates
The most exploited vulnerabilities in 2025 were not zero-days; they were known flaws with patches already available that organizations had not yet applied. Delayed patching is an open invitation.
- Automate OS, browser, and software updates across all endpoints.
- Establish a vulnerability management program that tracks, prioritizes, and remediates critical CVEs within defined SLAs.
- Don't forget that network devices, routers, switches, and firewalls are often overlooked in standard patch cycles.
2. Endpoint Protection & Antivirus
Every laptop, mobile phone, and server that connects to your network is a potential entry point. Modern unified endpoint management solution (UEM) goes far beyond traditional antivirus by identifying behavioral anomalies before they escalate.
- Deploy UEM solutions on all company endpoints, not just desktops, but servers, mobile devices, and cloud workloads.
- Ensure real-time monitoring is active.
- Only download software and applications from official, verified sources.
3. Zero Trust & Least Privilege Access
Least privilege access means every user, system, and application gets the minimum permissions required to do their job, and nothing more. Combined with Zero Trust Architecture, this dramatically limits the blast radius of any successful intrusion.
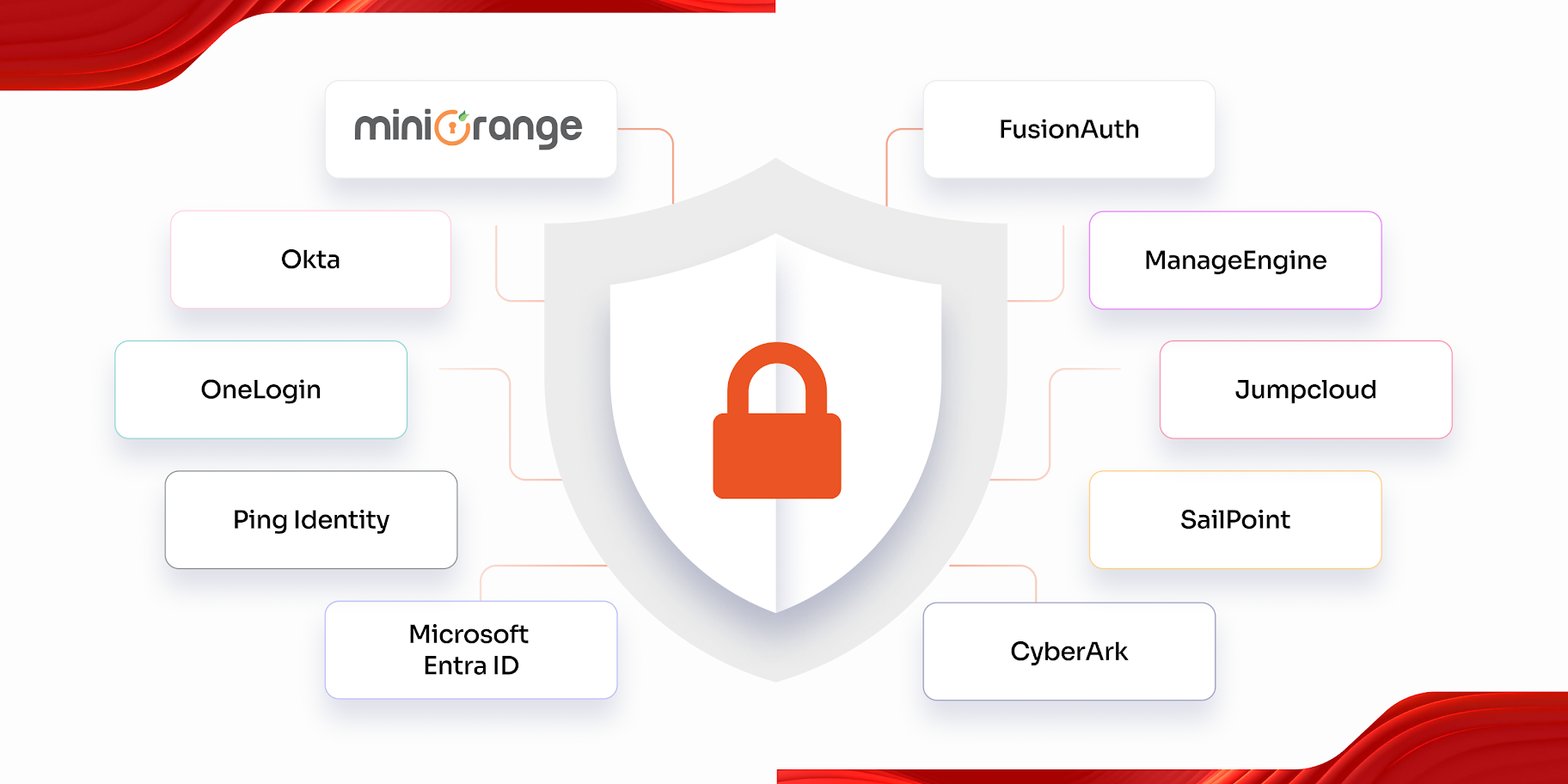
- Implement identity & access management (IAM) and review permissions regularly, especially when employees change roles or leave.
- If the organization is big enough, go beyond IAM and implement a Privilege Access Management (PAM) solution to control, monitor & audit elevated access.
- Enforce identity-driven access regardless of network location.
- Segment networks so that a compromise in one area cannot cascade across your entire infrastructure.
4. Data Loss Prevention (DLP) & Secure Backups
Ransomware incidents surged 30–40% year-over-year in 2025, with nearly 4,700 reported cases in just the first nine months of 2025. A robust backup strategy is often the difference between a minor disruption and a business-ending crisis.
- Implement DLP solutions that detect and block unauthorized transfer of sensitive data.
- Follow the 3-2-1 backup rule: three copies of data, on two different media types, with one stored securely off-site or in an air-gapped environment.
- Test backup restoration regularly; a backup you've never tested is a backup you don't actually have.
5. Application Security
If you've ever wondered how to secure an application properly, the answer starts well before launch. Applications are one of the most attacked surfaces in modern organizations. Whether it's a customer-facing web app or an internal tool, insecure code and exposed APIs are persistent vulnerabilities that attackers actively probe.
- Embed security reviews into every stage of the software development lifecycle (Secure SDLC), not just at launch.
- Conduct regular penetration testing, both internal red teaming and 3rd-party assessments, to surface vulnerabilities before attackers do.
- Secure all API endpoints with authentication, rate limiting, and input validation.
6. Supply Chain Risk Management
Supply chain attacks have become one of the most effective vectors for large-scale compromise precisely because third-party software and services are often trusted implicitly.
- Conduct thorough security assessments before onboarding new vendors, and review them periodically, not just at contract signing.
- Maintain a software bill of materials (SBOM) for all applications, so you know exactly what third-party components you're running.
- Apply the same Zero Trust principles to vendor access, or implement PAM, as you do to internal users.
2026 Cybersecurity Best Practices at a Glance
The following table consolidates 10 cybersecurity best practices that we discussed above in a single reference. Each entry reflects current threat patterns, from AI-powered phishing to ransomware targeting unpatched systems. All of which helps understand exactly what you're defending against, not just what you do to defend your business.
| Sr. No. | Best Practices for Cyber Security | Why does it matter? |
|---|---|---|
| 1. | Phishing Awareness & Social Engineering Defense | AI-generated phishing emails & attacks now mimic colleagues, clients, & even internal IT teams with near-perfect accuracy. |
| 2. | Strengthen Password Hygiene | Reusing passwords across platforms transforms one compromised credential into a key for dozens of accounts. |
| 3. | Enforce Multi-Factor Authentication (MFA) | Nearly 1 in 3 users is exposed to credential theft |
| 4. | Secure Remote Work & Wi-Fi Protection | Employees connecting from home networks, coffee shops, or airport lounges introduce extra external risks. |
| 5. | Patch Management & Automated Updates | Delayed patching is an open invitation to non zero-day attacks. |
| 6. | Endpoint Protection & Antivirus | Every laptop, mobile phone, and server that connects to your network is a potential entry point for cyber attacks. |
| 7. | Zero Trust & Least Privilege Access | Convenience led to default logins, which led to open endpoints for cyber attacks. |
| 8. | Data Loss Prevention (DLP) & Secure Backups | There were nearly 4,700 ransomware cases reported in just the first nine months of 2025. |
| 9. | Application Security | Whether it's a customer-facing web app or an internal tool, insecure code & exposed APIs are persistent vulnerabilities that attackers actively probe. |
| 10. | Supply Chain Risk Management | Supply chain attacks have become one of the most effective vectors for large-scale compromise |
Why Do These Cybersecurity Best Practices Matter? 3 Cybersecurity Attacks from 2025
These best practices or cybersecurity advice are not theoretical guidelines. The following incidents from 2025 illustrate exactly what happens when they are skipped, and the scale of damage that follows.
1. Oracle Cloud Breach: 6 Million Records, 140,000 Tenants Affected
Over 140,000 tenants were compromised when a hacker gained access to about 6 million records due to a login flaw in Oracle Cloud's infrastructure. The hack brought to light the results of poorly secured cloud authentication systems & the ripple effect that occurs when a single provider is compromised.
2. The 2025 Ransomware Surge: 4,700 Incidents in Nine Months
Ransomware incidents surged 30-40% in 2025 compared to the previous year. A pattern that analysts at miniOrange recognized was that the attackers exploited unpatched systems and used stolen credentials to move laterally across networks before deploying encryption payloads. In cases like this, strong patch management and network segmentation help to recover faster or even avoid the attack entirely.
3. The 16 Billion Credential Mega-Leak: Infostealers at Scale
In 2025, a single aggregated dataset of 16 billion login credentials was made public. This dataset was compiled from infostealer malware that had been collecting credentials from compromised devices covertly for months. This incident made it clear that endpoint security, MFA, and password hygiene must cooperate; an attacker can succeed if just one of these layers fails.
5 Cybersecurity Trends to Observe for 2026 and Beyond
Executing the best practices above gets you to a defensible baseline. But to stay ahead of adversaries who are continuously evolving, these are the strategic trends that will define the cybersecurity landscape in 2026 and shape investments for years to come.
1. Agentic AI
Gartner identifies agentic AI as one of the top emerging technology trends of 2025–2026. In cybersecurity, agentic AI means the systems that can autonomously plan, decide, and act on both sides of the fence. Attackers are deploying agentic AI to automate, adapt phishing lures in real time, and pivot across compromised networks without human operators.
2. Shadow Agents
IBM defines Shadow AI as the use of AI tools and models by employees without the knowledge of IT teams. Just as Shadow IT created unmanaged data flows a decade ago, Shadow AI is creating invisible risk in 2026, employees feeding sensitive company data into unapproved AI tools, embedding AI-generated code without security review, or using personal AI assistants for work tasks that process confidential information.
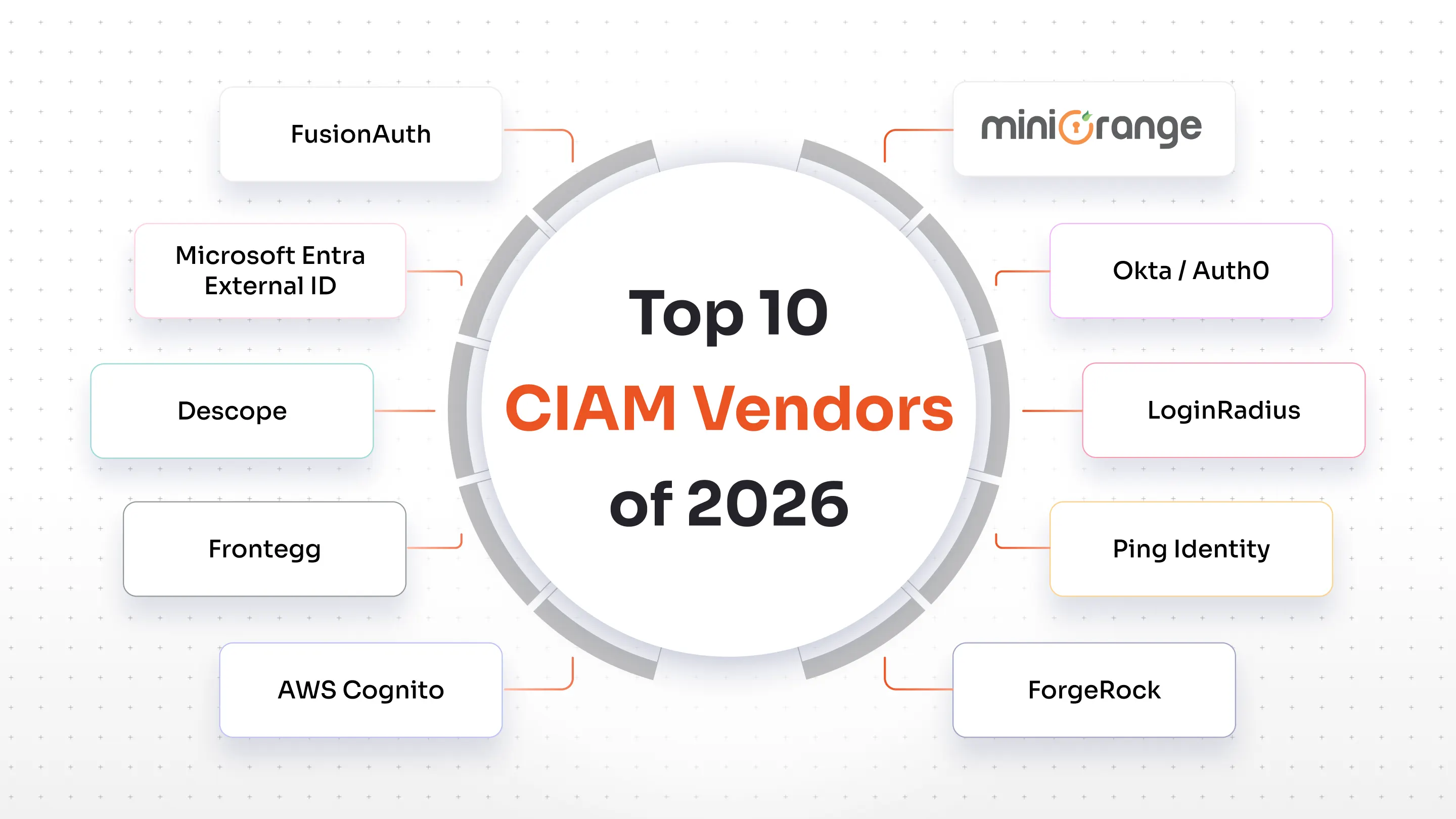
3. Identity Theft
Identity is rapidly becoming the primary battleground in cybersecurity. IBM predicts that there will be a surge in identity-focused attacks where adversaries exploit weaknesses in how organizations secure and manage digital identities. The traditional security frameworks are not yet built to entirely handle the identity theft methods we've seen so far, deepfakes, biometric spoofing, and model manipulations.
4. Quantum-Resistant Cryptography
IBM and NIST have been sounding the alarm for several years about this. Quantum computers are approaching the capability to break widely used encryption standards (RSA, ECC) that protect financial transactions, communications, and sensitive records. Attackers are already executing "store now, decrypt later" strategies, collecting encrypted data today to decrypt once quantum capability arrives.
5. Regulatory Compliance & Security Frameworks

Regulatory pressure on cybersecurity is accelerating. From the EU's NIS2 Directive to SEC disclosure requirements in the US, organizations face increasing legal obligations around breach reporting, data protection, and security governance. Using established frameworks, CIS Controls for tactical implementation, GDPR, PCI-DSS, and ISO 27001 for governance, is no longer just best practice; it's a baseline.
Explore the Top Cybersecurity Threats You Should Know
Stay Secure with miniOrange
Cybersecurity in 2026 is not a product you buy once; it's a program you continuously build, test, and improve. The organizations that stay protected are those that treat security as an operational discipline, not an IT checkbox.
At miniOrange, we help businesses move from reactive incident response to proactive, layered security. From MFA and Single-Sign On (SSO) to conditional access and identity management, our solutions are built to work together, not bolted on as an afterthought. Whether you're building your first security program or hardening an existing one, our team brings the expertise to keep you ahead of threats.
FAQs
What is the single most important cybersecurity best practice for a small business in 2026?
Multi-factor authentication. If you can only implement one thing, MFA/2FA dramatically reduces your exposure to credential-based attacks, which account for the majority of small business breaches. Combine it with a password manager, and you've addressed the most common attack vector with minimal cost.
Why is MFA critical for Cybersecurity?
MFA is critical for Cybersecurity as it adds a second verification step before giving access. With 16 billion credentials exposed in 2025 alone, even strong passwords are at risk, but with MFA, attackers need both the password and a second factor (hardware token, authenticator app, or biometrics) to gain entry.
What is the 3-2-1 backup rule?
The 3-2-1 backup rule is a proven standard: maintain 3 copies of your data, stored on 2 different media types, with 1 copy secured off-site or in an air-gapped environment. Given that ransomware surged 30–40% in 2025, this rule is no longer optional; it's essential.
How can employees improve cybersecurity?
The most practical cybersecurity advice for employees comes down to 3 habits: verify unexpected requests for credentials or sensitive data (even from seemingly trusted senders), use a password manager to maintain unique, complex passwords across all accounts, and enable MFA wherever available. Additionally, reporting suspicious emails, unusual login attempts, or anomalous behavior, rather than ignoring them, gives security teams the early warning needed to stop attacks before they spread.
Leave a Comment