Modern organizations frequently onboard new employees, manage internal role changes, and handle departures across multiple business applications. Without a structured identity lifecycle, access requests become manual, inconsistent, and difficult to track. This directly affects security, operational efficiency, and audit readiness.
A defined JML process in IAM ensures that the right users receive the right access at the right time while reducing administrative overhead. It also improves user productivity by enabling day-one access and timely updates when responsibilities change.
As digital ecosystems grow, organizations are adopting joiner-mover-leaver automation to standardize access control, maintain visibility, and support compliance with changing regulatory requirements.
Why the JML Process Is Needed
Eliminates Manual Access Management
In many environments, access is still provisioned through emails, tickets, or spreadsheets, leading to delays and errors. A structured JML process in IAM replaces these disconnected activities with a consistent, policy-driven approach. This ensures access is assigned and updated automatically based on verified identity data rather than ad hoc requests.
Prevents Access Misalignment
When employees move between departments or take on new responsibilities, their access often remains unchanged. Over time, this creates a buildup of outdated entitlements. A well-implemented JML process ensures access is updated in real time, keeping it aligned with current job functions and reducing security risks.
Enables Complete Offboarding
If access is not removed immediately after an employee leaves, organizations are left with active accounts that no longer have a valid business owner. Automated JML workflows trigger deprovisioning across connected systems as soon as the exit is recorded, maintaining control and protecting sensitive data.
Improves Audit Readiness
Auditors require clear evidence of who had access to what and when. A centralized integration for joiner, mover, and leaver events between HR systems and the IAM platform provides reliable access history, making it easier to demonstrate compliance and enforce governance policies.
Delivers Consistency Across Applications
As organizations adopt more cloud and on-premises applications, managing access individually for each system becomes unsustainable. A standardized JML lifecycle ensures users receive consistent access based on their role, regardless of the number of applications involved.
What Is the JML Process in IAM?
The joiner mover leaver (JML) process in IAM refers to the structured approach used to manage user access throughout their time in an organization. It begins when a new user joins and requires access to systems, continues as their role or department changes, and ends when they leave, and their access must be removed.
These lifecycle events ensure that access is always aligned with current job responsibilities, reducing manual intervention and improving consistency across applications. By standardizing how access is assigned and updated, the JML lifecycle becomes a core operational component for maintaining secure and efficient identity management.
How JML Fits into Identity Lifecycle Management
Within identity lifecycle management, JML acts as the execution layer that translates identity changes into access changes. When a trusted source, such as an HR system, records a hiring, transfer, or exit event, the IAM platform automatically updates the user's access across connected systems.
This makes the joiner mover leaver process essential for ensuring that identity data, access policies, and business roles remain continuously synchronized, enabling organizations to scale access control while maintaining visibility and compliance.
Relationship Between JML, Provisioning, and Deprovisioning
Provisioning and deprovisioning are the key technical actions that power the JML process. During the joiner stage, provisioning creates accounts and assigns role-based access. In the mover stage, it modifies access to reflect new responsibilities. In the leaver stage, deprovisioning removes access across all integrated applications in a timely manner. Together, these actions enable automated joiner-mover-leaver workflows that eliminate manual effort, enforce policy-driven access, and maintain a complete audit trail.
Joiners: Day-One Access
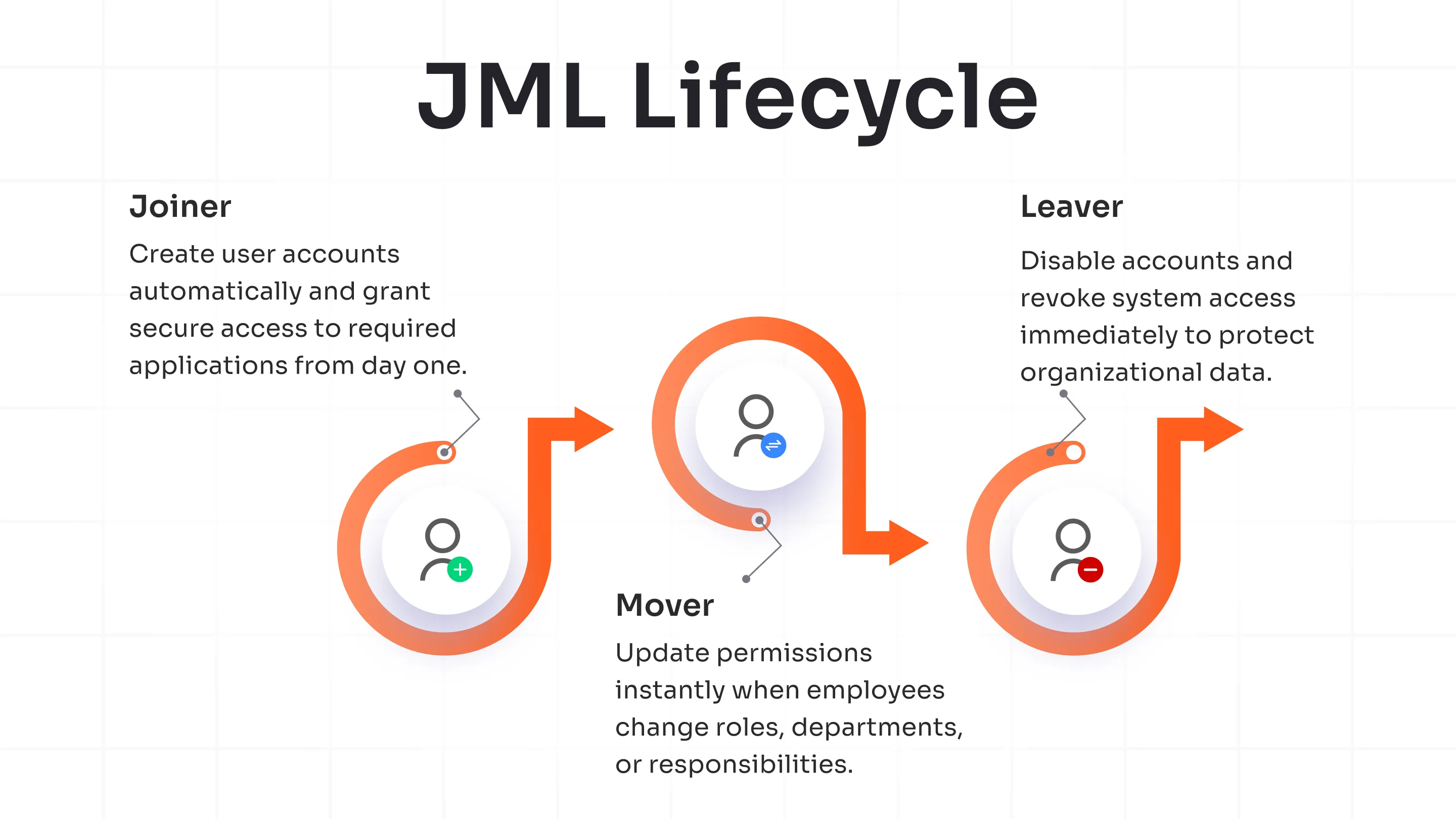
The joiner stage focuses on giving new users the right access as soon as they enter the organization. A well-defined joiner process in IAM ensures onboarding is fast, accurate, and consistent by using identity data from the HR system to automatically create accounts and assign role-based access.
With joiner-mover-leaver automation, organizations can:
- Trigger identity creation directly from the HR record
- Provision access across required applications in a single workflow
- Assign access based on predefined business roles
- Eliminate manual tickets and approval delays
- Ensure a consistent onboarding experience for every new user
This structured approach reduces the operational effort for IT teams while enabling day-one productivity for employees. It also improves accuracy by standardizing how access is granted, making the JML process in IAM scalable as the organization grows.
Movers: Access Aligned with Role Changes
The mover stage ensures that access evolves as employees transition between roles, departments, or projects. In a mature mover process in IAM, any change in the authoritative source automatically updates user access, preventing misalignment between job responsibilities and system access.
With joiner-mover-leaver automation, organizations can:
- Update access instantly when a role or department changes
- Grant new application access based on the updated business role
- Remove access that is no longer required
- Avoid repeated manual access requests during internal transitions
- Maintain continuity without disrupting user productivity
By continuously aligning access with current responsibilities, the joiner, mover, and leaver lifecycle reduces governance gaps, improves operational efficiency, and ensures access remains accurate as the organization evolves.
Leavers: Timely Offboarding
The leaver stage focuses on removing access quickly and consistently when a user exits the organization. A disconnected offboarding process often leaves active accounts behind, but a well-integrated joiner mover leaver integration ensures that access removal is automatically triggered from the exit event in the HR system.
A structured JML process enables organizations to:
- Deprovision access across all connected applications from a single workflow
- Disable directory accounts immediately after exit confirmation
- Maintain a complete and verifiable record of access removal
- Eliminate orphaned accounts and manual follow-ups
- Support audit and compliance requirements with accurate lifecycle data
This automated and policy-driven approach strengthens security, reduces administrative effort, and makes the JML process reliable, consistent, and fully auditable.
How the JML Lifecycle Works
Step 1: Identify the Event from the Authoritative Source
The lifecycle begins when a trusted system, such as the HRMS, records a new hire, role change, or exit. This event acts as the single source of truth and initiates the JML process, ensuring all access decisions are based on verified user data.
Step 2: Identity Creation or Update
The IAM system creates a new digital identity for joiners or updates an existing identity for movers. Key attributes like department, role, and location are synchronized to enable accurate and policy-based access assignment.
Step 3: Role-Based Access Assignment
Access is determined using predefined roles and rules. This standardizes provisioning, ensures consistency across applications, and enables automated joiner-mover-leaver workflows without manual intervention.
Step 4: Provisioning and Access Modification
User accounts are created, updated, or adjusted across all connected applications and directories. When a user changes roles, the system grants new access and removes outdated access to keep the JML lifecycle aligned with current responsibilities.
Step 5: Timely Deprovisioning and Audit Trail
When a user leaves, access is removed across systems in a consistent and auditable manner. Every action is logged, providing complete visibility for compliance, reporting, and access reviews.
Key Stakeholders in the JML Process
A successful JML process depends on all stakeholders playing a distinct role in ensuring that identity data is accurate and lifecycle events are executed on time.
HRMS: HR systems initiate the lifecycle by recording hires, role changes, and exits. This makes HR the primary trigger for ensuring access decisions are based on verified user information.
IT and IAM Teams: They configure the policies, roles, and workflows that drive provisioning and deprovisioning.
Reporting Managers: Managers are responsible for confirming that users receive the access required for their job function.
Application Owners: They define what access is required for different roles within their systems and ensure that access provisioning is accurate with operational needs.
Security and Compliance Teams: Security teams monitor lifecycle activities, validate policy enforcement, and use JML reports during audits.
Tools and Technologies That Enable JML
Implementing an efficient joiner, mover, and leaver lifecycle requires a connected technology stack that can translate identity events into automated access changes.
Common tools used in JML implementations include:
- HRMS / HCM systems: Act as the authoritative identity source and trigger lifecycle events
- IAM/PAM platform: Manage identity creation, role assignment, and access workflows
- Identity Governance and Administration (IGA) solutions: Handle role models, access reviews, and lifecycle policies
- Directory services: Maintain user accounts and group-based access
- Single Sign-On (SSO): Provide seamless and consistent access across applications
- Workflow and ticketing systems: Manage approvals and exception handling
- Connectors and integration frameworks: Synchronize access changes across target systems
Together, these tools enable automated joiner-mover-leaver workflows that eliminate manual processing and maintain consistency across environments.
Best Practices for an Effective JML Process
Use HR as the Single Source of Truth
All lifecycle events should originate from a trusted HR system so that onboarding, role changes, and exits automatically trigger access updates. This eliminates conflicting data across systems and ensures the JML process always works with verified and current user information.
Design a Clear RBAC Model
Define access based on job functions rather than individual user requests. A well-structured RBAC model simplifies provisioning, reduces approval dependencies, and ensures users receive the correct access when they join or move within the organization.
Standardize JML Workflows
Create predefined workflows for each lifecycle event so that access is handled in a consistent and repeatable manner. Standardization reduces manual effort, shortens onboarding and offboarding timelines, and minimizes configuration errors across applications.
Enable Real-Time, Event-Driven Offboarding
Access removal should begin immediately when an exit is recorded in the authoritative system. Automated deprovisioning across directories and business applications prevents active accounts from remaining and ensures that the joiner mover leaver integration supports audit and security requirements.
Implement Policy-Based Provisioning
Access decisions should be driven by policies that evaluate user attributes such as department, location, and employment type. This reduces the need for manual approvals and ensures consistent access assignment across systems.
Perform Periodic Access Reviews
Regular access certifications help confirm that users still require their assigned access. These reviews also highlight outdated roles, unused access, and opportunities to optimize the access model.
JML Automation: From Manual to Event-Driven Workflows
Many organizations begin with a manual onboarding and offboarding model driven by service desk tickets and email approvals. As the number of applications and users grows, this approach becomes slow, error-prone, and difficult to audit.
Joiner-mover-leaver automation replaces these disconnected tasks with event-driven workflows where identity changes automatically trigger access updates.
Moving to an automated JML model allows organizations to:
- Provision and update access in real time
- Enforce consistent, policy-based access decisions
- Reduce onboarding and offboarding time
- Minimize manual effort for IT teams
- Maintain complete lifecycle visibility for audits
The JML process becomes scalable, predictable, and aligned with business operations by integrating HR systems with IAM platforms.
Real-World JML Use Cases
Enterprise Onboarding at Scale
Large organizations use automated JML workflows to provide consistent day-one access for thousands of new hires across multiple applications and locations.
Internal Role Transitions
When employees move between teams, access is updated automatically based on their new responsibilities, eliminating delays and manual access requests.
Contractor Lifecycle Management
Time-based access is provisioned at the start of the engagement and automatically removed when the contract ends, ensuring accurate lifecycle control.
Audit Remediation Programs
Organizations use the joiner mover leaver lifecycle to close audit findings related to delayed offboarding, inconsistent access, and lack of access history.
Key Metrics to Analyze JML Success
Time to Onboard New Users
Measures how quickly new joiners receive required access after HR entry. Faster onboarding through an automated JML process improves productivity and reduces service desk workload.
Time to Update Access After Role Changes
Tracks how rapidly access is modified when employees change roles. A responsive JML process in IAM keeps access aligned with responsibilities and avoids repeated manual access requests.
Time to Remove Access After Exit
Indicates how quickly access is revoked after departure. Automated joiner-mover-leaver workflows ensure timely deprovisioning across systems, preventing active accounts and strengthening audit and security outcomes.
Reduction in Manual Access Requests
Shows how effectively role-based provisioning replaces ticket-driven access. A mature joiner mover leaver lifecycle minimizes approvals, reduces IT effort, and delivers consistent access across applications.
Number of Orphaned or Inactive Accounts
Highlights gaps in offboarding execution. Fewer orphaned accounts confirm that the JML joiner mover leaver process removes access completely and maintains accurate identity lifecycle control.
miniOrange for Automated User Provisioning
miniOrange provides a centralized platform to execute the joiner-mover-leaver process in IAM through automated, policy-driven workflows that keep access aligned with user roles and organizational changes.
With miniOrange, organizations can:
- Enable HR-driven provisioning for accurate day-one onboarding and role-based access assignment
- Implement end-to-end user lifecycle management from a single, unified identity platform
- Automate access creation through consistent user provisioning across connected applications
- Ensure timely and complete access removal with real-time user deprovisioning
- Orchestrate the entire joiner-mover-leaver automation workflow with full audit visibility
Building a Scalable Identity Lifecycle in 2026
The joiner-mover-leaver process in IAM brings structure and consistency to how user access is managed from onboarding to offboarding. Organizations can ensure access always reflects current roles and business needs by connecting HR-driven identity events with automated provisioning and deprovisioning.
This reduces manual effort, improves user productivity, and creates a reliable audit trail for compliance. As application environments continue to grow, adopting joiner-mover-leaver automation enables organizations to scale access management, maintain visibility across systems, and enforce policy-driven control without operational delays.
Frequently Asked Questions
What is the difference between JML and IAM?
IAM is the foundational framework for managing digital identities and controlling access to systems. The joiner mover leaver (JML) process in IAM is the lifecycle workflow that executes access changes when a user joins, changes roles, or leaves.
How do you automate JML?
Joiner-mover-leaver automation is achieved by integrating the HR system with an IAM or IGA platform. Identity events automatically trigger role-based provisioning, access updates, and deprovisioning across all connected applications without manual tickets.
Why is JML important for compliance?
A structured JML process ensures access is granted and removed in a timely, consistent, and traceable manner. This helps organizations demonstrate control effectiveness, maintain access history, and meet audit requirements across regulatory frameworks.
What challenges do organizations face when implementing JML?
Common challenges include inconsistent HR data, lack of role definitions, disconnected applications, and manual approval workflows. Addressing these gaps is essential for building a scalable and fully automated JML lifecycle.
What are the key benefits of an automated JML process?
An automated joiner, mover, and leaver lifecycle reduces onboarding time, keeps access aligned with job roles, removes access promptly after exit, minimizes IT workload, and improves visibility for audits and governance.

Leave a Comment