Agent-based security gives you deep visibility and real-time control. Agentless security gives you speed, scale, and easier coverage.
Most organizations don’t choose one over the other. They use both. That’s because different devices require different levels of control. Some systems need direct control, while others require a lighter approach that works without installation.
So the real question isn’t agent vs agentless security. It’s about knowing when to use each approach and how to combine them. In this blog, we will break down agent-based vs agentless security, how they work, where each one is useful, and why many teams combine both for better coverage.
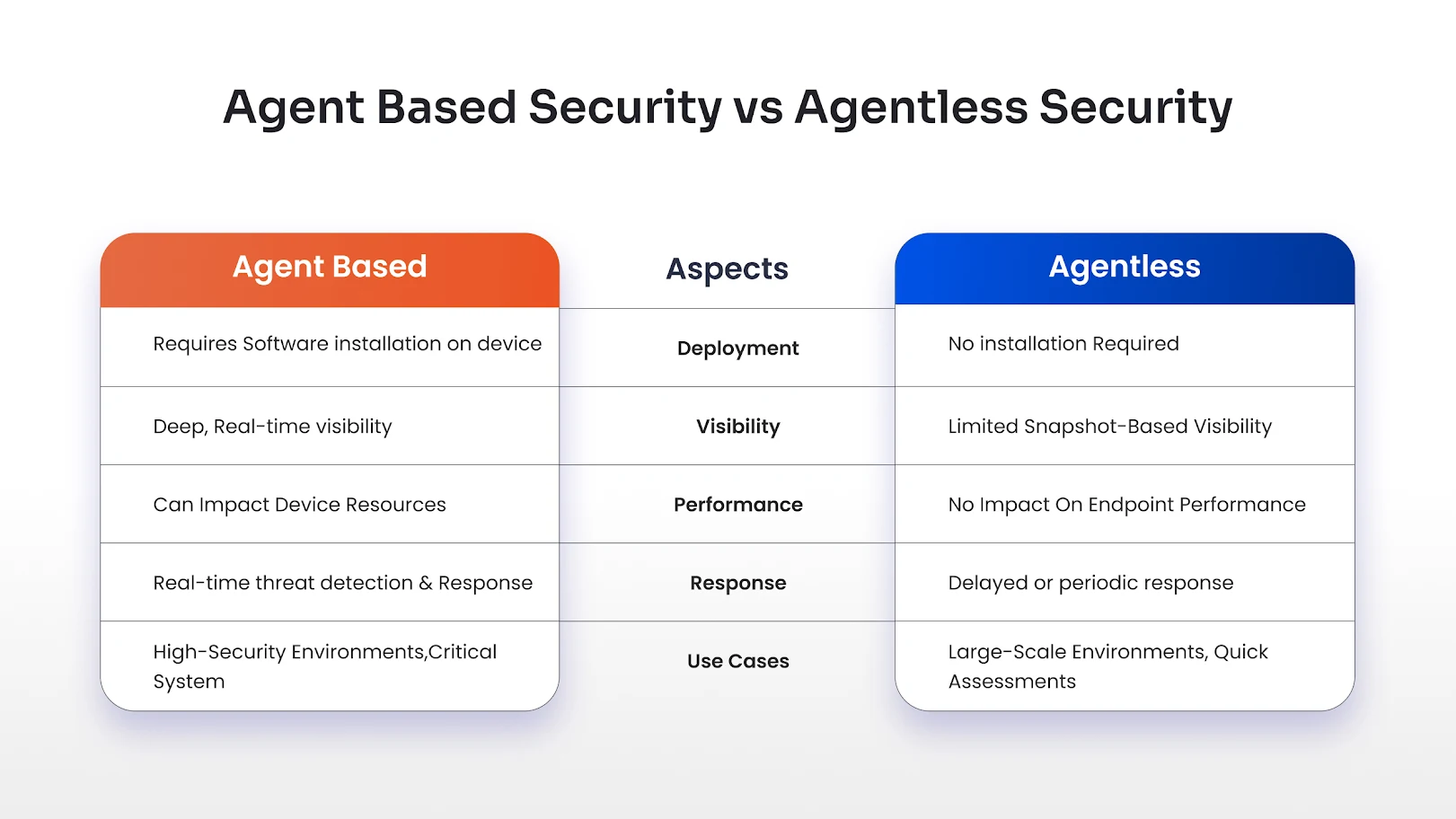
Agent-Based vs. Agentless Security at a Glance
What Is Agent-Based Security?
Agent-based security relies on installing a small software component, called an agent, directly on endpoint devices.
This agent continuously monitors activity, enforces policies, and reports data back to a central system.
How does it work?
Once installed, the agent runs in the background on the device. It tracks processes, monitors behavior, detects anomalies, and can take action instantly if something suspicious happens.
It also enables strict device control. For example, you can restrict USB access, block unauthorized apps, or enforce system-level policies directly on the device.
This is especially useful for environments where devices are managed closely and need consistent enforcement.
Pros
- Provides deep visibility into device behavior
- Enables real-time threat detection and response
- Supports strict device-level restrictions and controls
- Works well for compliance-heavy industries
Cons
- Requires installation and maintenance of agents
- Can impact device performance if not optimized
- Deployment can be slower at scale
- May face resistance from users or unmanaged devices
What Is Agentless Security?
Agentless security works without installing any software on endpoint devices.
Instead, it connects to systems remotely using APIs, network access, or identity-based controls to monitor and enforce security policies.
How does it work?
Agentless solutions pull data from existing systems such as cloud platforms, directories, or network layers.
Instead of sitting on the device, they observe from the outside. They analyze configurations, user behavior, and access patterns.
This is where device restriction and identity-based controls become important.
For example, using miniOrange device restriction capabilities, you can allow or block access based on:
- Device type
- Device fingerprint
- Browser or OS
- Trusted vs untrusted devices
This means even without an agent, you can still control which devices can access your systems.
Pros
- Quick to deploy with no installation required
- Scales easily across large environments
- No performance impact on devices
- Ideal for BYOD and remote work scenarios
Cons
- Limited visibility into real-time device activity
- Cannot enforce deep system-level controls
- Relies on external data sources
- Slower response to certain threats
Key Differences: Agent-Based vs Agentless
Agent-based and agentless security approaches are designed to solve different security challenges and are used in different situations. Here are the key differences between agent-based and agentless security, based on how they operate in practice.
Visibility
Agent-based security gives you continuous, real-time visibility because it runs directly on the device and tracks activity as it happens. It can monitor processes, user actions, and system behavior in detail, making it easier to detect and respond to threats immediately.
Agentless security provides a broader view across systems by pulling data from external sources like APIs, cloud platforms, or network layers. While this helps cover more systems quickly, it is limited to what can be accessed externally and usually relies on periodic data instead of constant monitoring.
Deployment
Agent-based solutions require software to be installed on each device, followed by setup, configuration, and ongoing maintenance. This makes deployment more time-consuming, especially in large or distributed setups where managing agents across devices can be challenging.
Agentless solutions are much quicker to roll out since they don’t require installation on endpoints. They can be deployed across systems in a shorter time, making them a better fit when speed and scalability are priorities.
Performance
Agent-based security uses device resources such as CPU and memory to monitor activity and enforce controls. Depending on how it is configured, this can impact device performance, especially on lower-powered systems.
Agentless security operates outside the device, so it does not consume endpoint resources. This makes it a better option in cases where performance needs to remain unaffected.
Response
Agent-based systems can detect and respond to threats in real time because they operate directly on the device. They can block suspicious actions, isolate compromised systems, or trigger alerts instantly.
Agentless systems focus more on visibility and analysis across systems rather than direct control. While they can identify risks and misconfigurations, their response is not always immediate and often depends on integrations or follow-up actions.
When to Use Agent-Based Security?
Agent-based security makes sense when you need tight control over devices.
It is ideal for:
- Corporate-owned devices
- High-security environments
- Systems handling sensitive data
- Compliance-driven industries
If you need real-time monitoring, deep visibility, and strict enforcement, agent-based is the better choice.
When to Use Agentless Security?
Agentless security is better suited for flexibility and scale.
It works well for:
- Remote and hybrid work setups
- BYOD environments
- Cloud-first organizations
- Quick security assessments
If you need fast deployment and wide coverage without touching devices, agentless is the way to go.
Why Does Hybrid Approach Work Best?
Most organizations don’t operate in a single, controlled setup. Some devices are fully managed, while others are personal or unmanaged. Some users work internally, while others connect remotely.
Because of this, relying on just one approach creates gaps.
Agent-based security works well for managed devices where control and real-time monitoring are critical. But it doesn’t extend easily to unmanaged or external environments.
Agentless security fills that gap by providing broader coverage without requiring installation, but it cannot offer the same level of control or real-time response.
A hybrid approach brings both together.
Agent-based security handles environments where deep control is needed, while agentless security extends visibility and coverage across devices that can’t be managed directly.
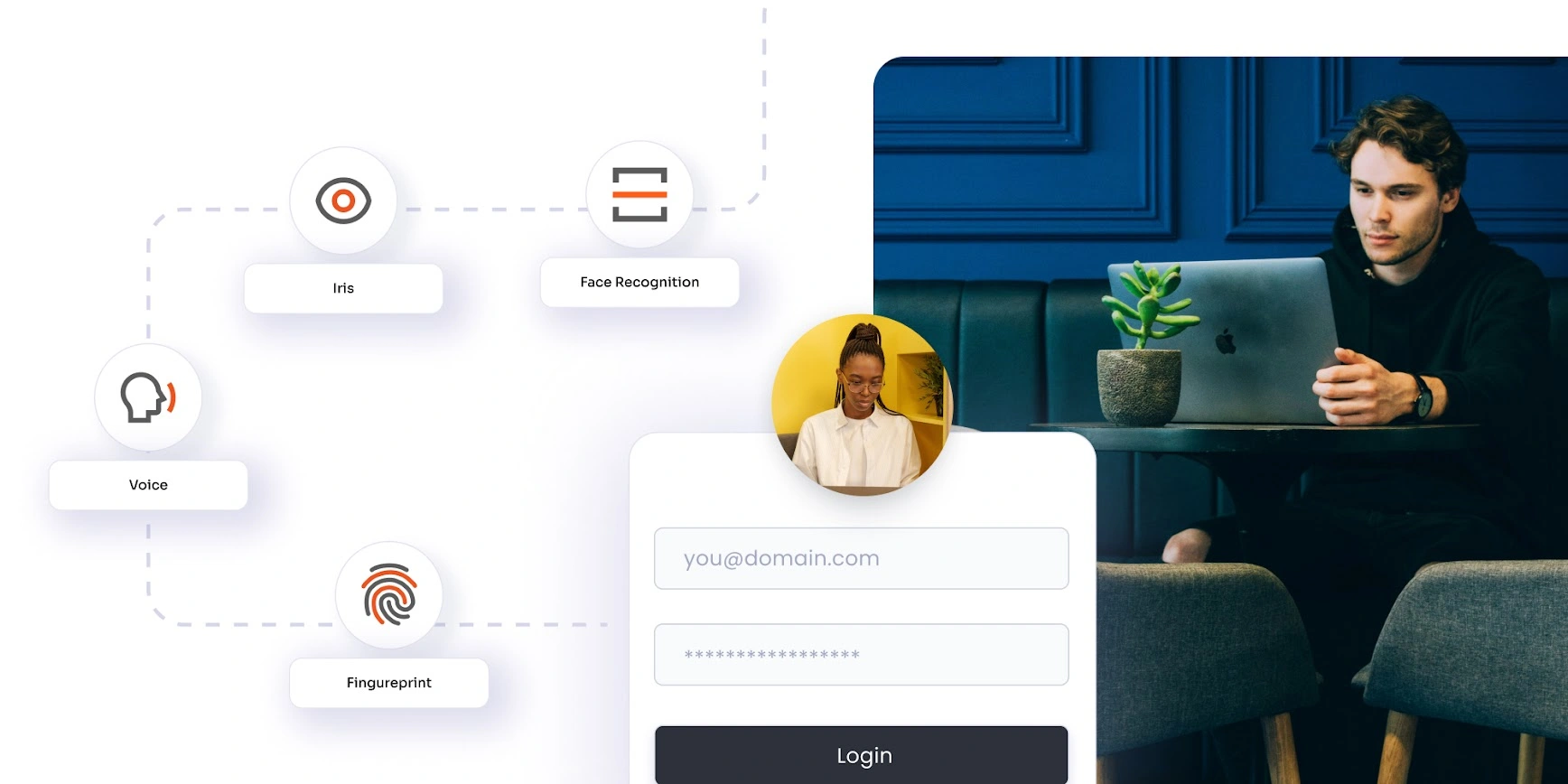
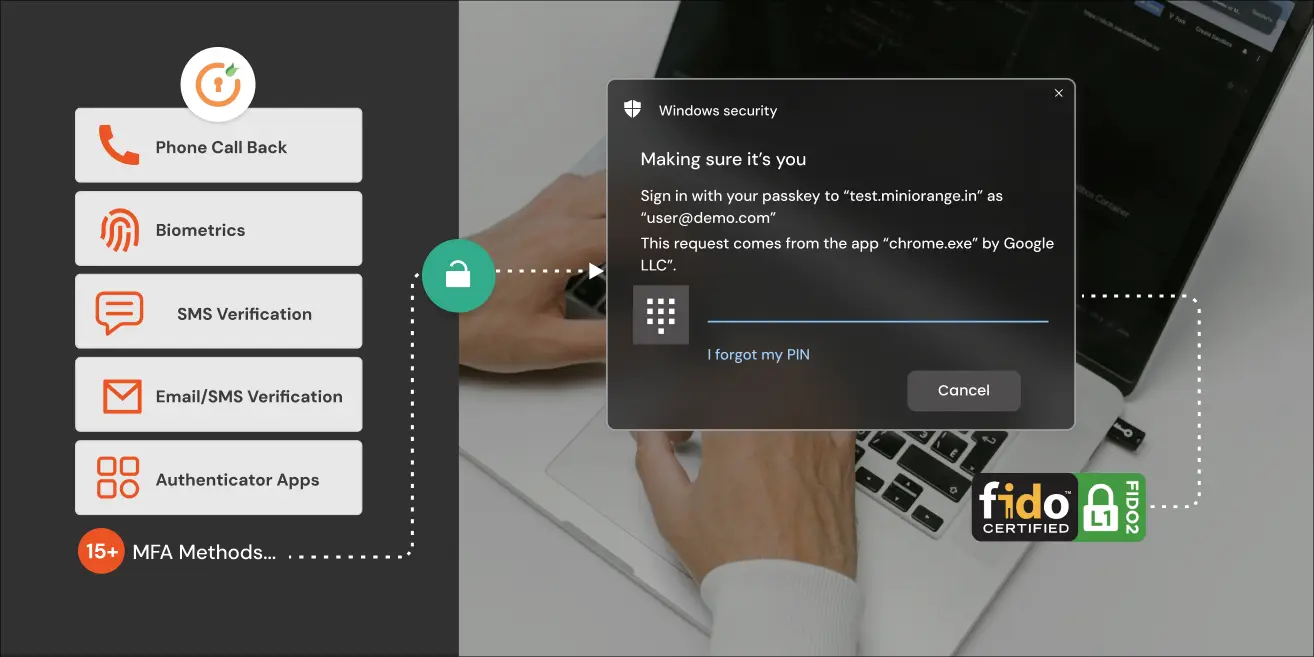
When you layer identity-based controls like adaptive MFA and device-aware access on top of this, security becomes much more context-driven.
This is where solutions like miniOrange add value. Instead of relying only on device-level controls, they factor in identity, device trust, and user context to make access decisions more secure and practical.
How to Choose the Right Approach?
The right choice depends on how your devices and users are set up, not just the technology itself.
If most of your devices are company-owned and centrally managed, agent-based security should be your starting point. It gives you stronger control, deeper visibility, and real-time response where it matters most.
If users are accessing systems from personal devices or different locations, agentless security becomes important. It helps extend coverage without needing software on every device.
In most cases, using both makes more sense.
Agent-based security works well for devices you control directly. Agentless security helps cover everything outside that, especially where installation isn’t practical.
But device-level security alone isn’t enough.
Access decisions should also consider factors like device trust, location, and user behavior. Adaptive MFA helps do that by adjusting authentication based on risk, while phishing-resistant MFA reduces the chances of attackers getting in even if credentials are exposed.
When these controls work together, you get a more balanced and reliable security approach.
Strengthen Your Security Strategy with miniOrange
Agent-based and agentless security are not competing approaches. They solve different parts of the same problem. Agent-based security provides depth, control, and real-time visibility where devices are managed.
Agentless security extends coverage across devices and access points that cannot be controlled directly. Most organizations today operate somewhere in between. That’s why combining both approaches is often more effective than relying on just one.
But device-level security alone isn’t enough. Security today depends on more than just what’s happening on a device. It also involves integrating MFA services to verify who is accessing your systems, which device they’re using, and whether the access looks legitimate.
miniOrange brings this layer of control through capabilities like adaptive MFA, phishing-resistant authentication, device-based access control, and identity management. These controls work alongside your existing setup to strengthen security without adding unnecessary complexity.
Instead of treating devices as the only point of control, this approach connects users, devices, and access into a more complete security model.
FAQs
What is agent vs agentless security?
Agent-based security uses software installed on devices for monitoring and control, while agentless security works remotely without installing anything on endpoints.
Is agentless security better than agent-based?
Not necessarily. Agentless is faster and easier to deploy, while agent-based provides deeper visibility and control. The right choice depends on your needs.
What are the benefits of agent-based security?
Agent-based security offers real-time monitoring, deep visibility, and strong control over device behavior, making it ideal for high-security environments.
What are the benefits of agentless security?
Agentless security is easy to deploy, scalable, and does not impact device performance. It works well in remote and BYOD environments.
Can agentless security detect real-time threats?
Agentless security can detect threats, but it may not always provide real-time response like agent-based solutions.
Should organizations use both approaches?
Yes, most organizations benefit from a hybrid approach that combines agent-based and agentless security for better coverage and flexibility.


Leave a Comment