Need Help? We are right here!
Search Results:
×






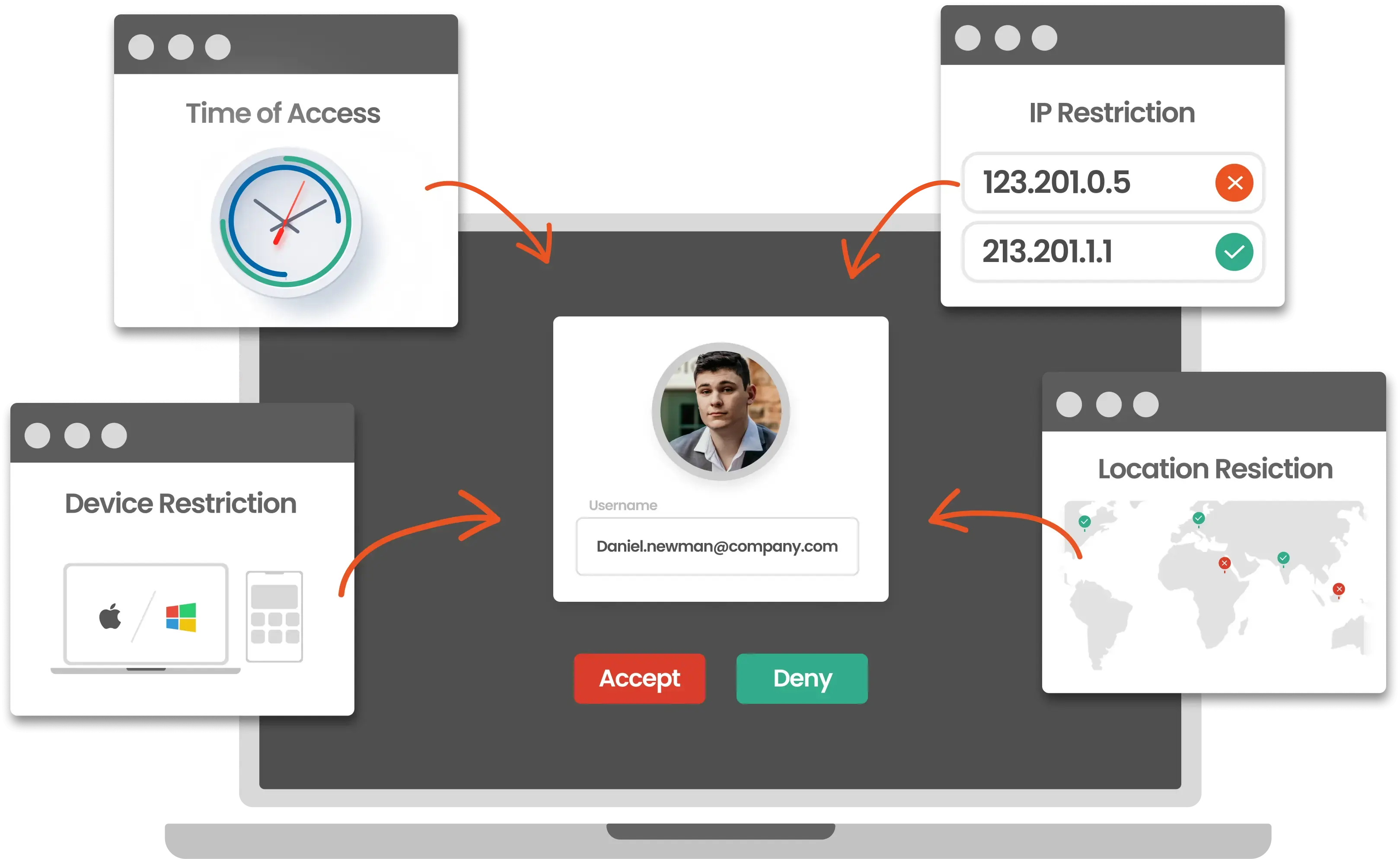
Secure user access with advanced Device Restriction, MFA, and Adaptive authentication tailored for your business needs.
Organizations limit access to apps and data by allowing only trusted devices. Here's how key sectors apply device restriction in practice.
Control access to learning platforms using trusted student and staff devices. Prevent unauthorized usage while ensuring secure access to academic data.
Secure POS systems and retail applications by allowing access only from authorized devices. Protect customer data and transactions from unauthorized access.
Ensure only approved devices access patient records and healthcare applications. Maintain data protection and comply with healthcare regulations.
Restrict access to financial systems based on trusted devices and user roles. Prevent fraud and unauthorized transactions with device-level controls.
Secure access to critical systems and confidential data using trusted devices. Enforce strict policies to prevent unauthorized access.
Control access to operational systems and production data using authorized devices. Ensure secure usage across factory and enterprise environments.
Ensure users can access business and SaaS applications only from trusted and authorized devices. Strengthen identity assurance with device-level authentication aligned to Zero Trust security.
Control access to cloud applications by verifying device trust and login context before granting access.
Enforce device-level controls on mobile devices to secure access to business applications. Ensure only approved and managed devices can access corporate resources.
Enable secure access for personal devices while maintaining strict control over corporate data. Apply Device Restriction policies to ensure only compliant devices can access business applications.
Secure access for external users such as vendors, partners, and contractors. Ensure third-party access is limited to trusted devices and controlled environments.
Device Restriction strengthens your Zero Trust security posture by ensuring only trusted devices can access
sensitive business resources while enabling real-time threat detection and response.
Allow access to critical business applications only from trusted and compliant devices. Prevent unauthorized access from unknown locations or unmanaged personal devices to reduce data leakage risks.
Grant role-based access to users and groups with precise control over device usage. Simplify access management while enforcing strict Device Restriction policies across applications.
Restrict access to approved devices to support regulatory compliance requirements. Align with global standards such as GDPR, HIPAA, PCI DSS, SOX, and other industry regulations.
Centralize access control with unified Device Restriction policies. Reduce security overhead, minimize manual interventions, and lower operational costs while improving overall security effectiveness.
Define Device Restriction policies tailored to your organization's risk posture. Adapt access decisions dynamically based on user context, device trust, and real-time risk signals.
Enable Device Restriction security policies across a fleet of Cloud and On-Premise SaaS applications like Google Workspace, MS Office 365, Atlassian, Slack, Dropbox, Oracle and more to secure your data by allowing access from authorized user devices only.
Explore Our App Integration Catalog








