For organizations that still rely on fragmented tools, identity fabric helps them to unify everything in one place.
What is identity fabric, and why is it gaining traction? The answer lies in the ability of identity fabric to unify identity systems without forcing a complete rip-and-replace. Identity fabric acts as a flexible, connective layer that brings together identity providers, applications, and security controls into a cohesive framework.
Instead of adding more tools to manage complexity, identity fabric reduces it. It aligns closely with zero trust identity principles, supports modern Identity and Access Management (IAM) architecture, and enables organizations to adapt quickly to evolving security demands.
What is Identity Fabric?
Identity fabric is an architectural approach that connects and orchestrates multiple identity systems, tools, and services into a unified framework. It does not replace existing identity solutions. Instead, it integrates them using APIs, connectors, and orchestration layers.
At its core, identity fabric enables seamless identity orchestration across environments such as cloud platforms, on-prem systems, SaaS applications, and APIs.
In simple terms, identity fabric creates a flexible identity layer that allows organizations to manage authentication, authorization, and identity governance consistently without being tied to a single vendor or system.
Why Identity Security Fabric Matters for Modern Enterprises
Here are five reasons why identity security fabric is essential for enterprises (large, medium, or small):
1. Eliminate Identity Fragmentation
Most enterprises operate with multiple identity providers, directories, and access tools. This fragmentation creates gaps in visibility and control. Identity fabric unifies these systems, allowing centralized policy enforcement.
2. Quicken Identity Initiatives
Deploying new identity solutions traditionally takes months due to integration challenges. With identity fabric, organizations can quickly connect new applications or services using pre-built connectors and APIs, significantly reducing deployment time.
3. Support Distributed and Multi-Cloud Environments
Modern businesses operate across AWS, Azure, GCP, and private data centers. Identity fabric provides a consistent identity layer across all these environments, ensuring secure access regardless of where resources are hosted.
Key Components of Identity Fabric

Identity fabric is powered by a set of core capabilities that work together to unify authentication, authorization, and identity governance across all your environments. The components that help to do so are:
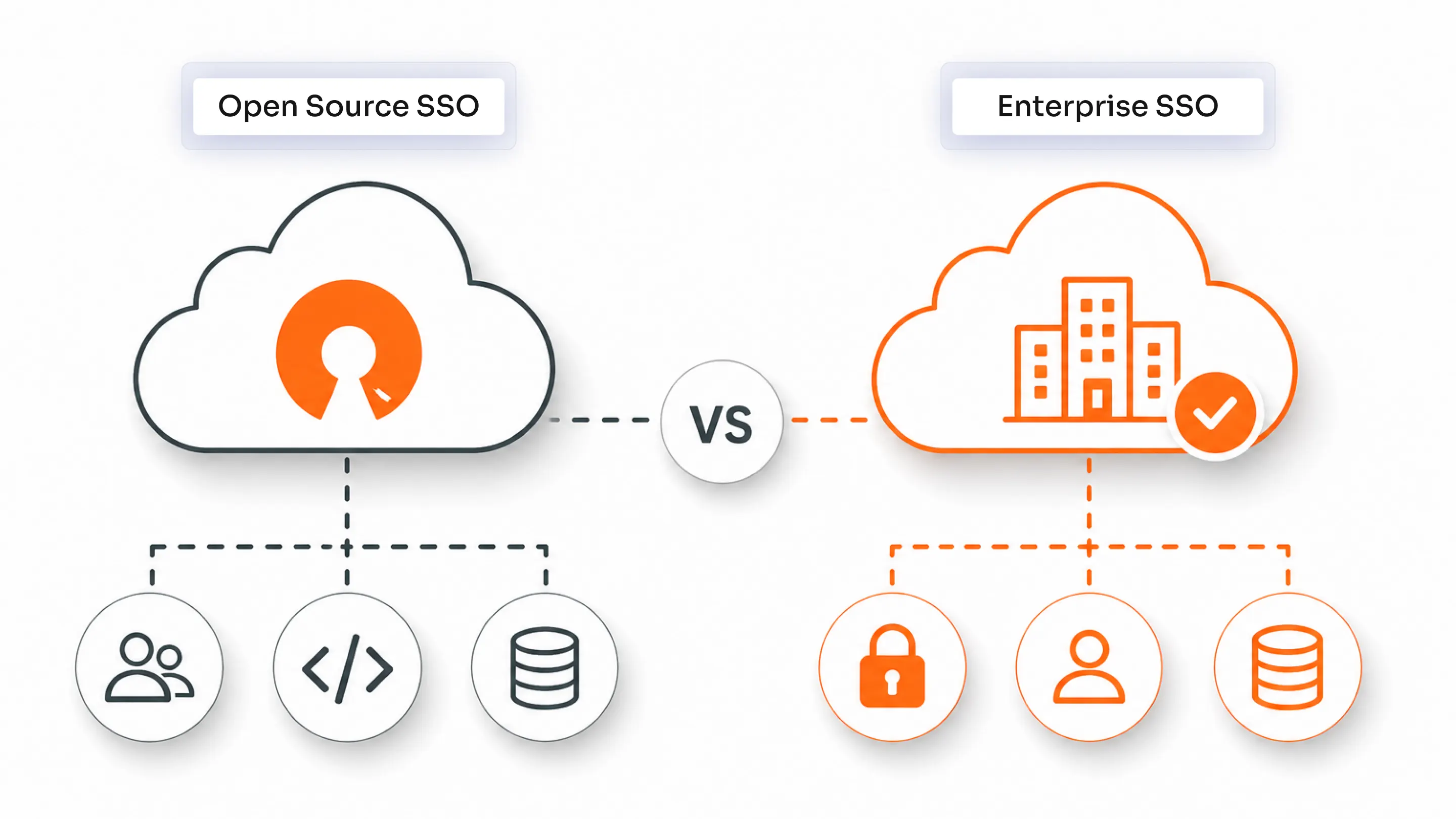
1. Single Sign-On (SSO)
An SSO solution allows users to access multiple applications with a single set of credentials. Within the identity fabric, SSO acts as a foundational layer that improves user experience while maintaining centralized authentication control.
2. Multi-Factor Authentication (MFA)
The MFA solution strengthens security by requiring additional verification factors such as hardware tokens, OTP, biometrics, etc., on top of passwords to reduce account takeover attacks.
3. Identity Directories
Directories store user identities and attributes. Identity fabric connects multiple directories, such as Active Directory and cloud-based directories, creating a unified identity view.
4. SCIM Provisioning
SCIM provisioning is an automated provisioning and deprovisioning that keeps access in sync across SaaS, on‑prem, and cloud apps as users/employees join, move, and leave. Identity fabric uses the SCIM protocol to ensure identities are consistently managed across applications.
5. APIs and Connectors
APIs and connectors are the backbone of the identity fabric. They enable communication between disparate systems, allowing integration without custom development.
6. Identity Orchestration Engine
A policy‑driven workflow layer that coordinates login flows, risk checks, step‑up MFA, and authorization decisions across all connected systems.
The Core Principles of Identity Fabric
The Tech Republic has highlighted 10 identity fabric principles that are used by Gartner to help clients with an identity fabric model. These principles are as follows:
- Scope for any human and machine
- Topology includes centralized control and decentralized enablement
- Architecture should be composable, orchestrated, and journey-oriented
- Adaptive, continuous, risk-aware, and resilient security levels
- Standards have to be pervasive
- Connectivity includes event-based integration
- Change is continuous and automated
- Threat detection and response must be prescriptive and remedial
- Privacy preservation is for everyone
- Maintain continuous observability
Identity Fabric Architecture: How It Works
At a high level, an identity fabric sits in the middle of your existing identity stack and your applications, connecting everything through an orchestration layer and open protocols.
The core levels of identity fabric that drive its working are:
1. Identity Sources
HR systems, Active Directory, LDAP, and cloud directories store the core identity attributes, group memberships, and lifecycle data that define who a user is.
2. Identity Providers (IdPs and SSO Services)
Workforce IdPs and CIAM platforms handle authentication and token issuance, turning raw identity data into verifiable credentials your apps can trust.
3. Orchestration Layer (Identity Fabric Core)
The identity fabric’s orchestration layer sits on top of multiple IdPs and directories to apply policies, route traffic, perform identity orchestration, and enforce zero-trust identity decisions in a consistent way.
4. APIs and Connectors
Standards‑based APIs and connectors (SAML, OIDC, OAuth, SCIM, LDAP) plug the fabric into both identity systems and applications, so you can evolve vendors and platforms without changing application code.
5. Applications and Services
SaaS, on‑prem, mobile, and API‑based services integrate once with the identity fabric and rely on it for Single Sign-On, MFA, authorization, and identity governance, instead of managing that logic themselves.
Identity Fabric vs. Traditional IAM
Traditional IAM systems are often centralized and rigid, while identity fabric is distributed and flexible. For a detailed view, we’ve brought together a comprehensive comparison table:
| Feature | Traditional IAM | Identity Fabric |
|---|---|---|
| Architecture | Monolithic structure | Modular, API-driven approach |
| Flexibility | Limited | Adapts |
| Integration | Needs custom integration | Uses pre-built connectors |
| Scalability | Moderate | High |
| Deployment | Complex | Agile |
| User Experience | Fragmented | Unified |
| Vendor Dependency | Locks-in the organization | Promotes vendor neutrality |
The modern IAM solution is increasingly shifting toward identity fabric because it aligns better with cloud-native and zero-trust requirements.
Identity Fabric and Zero Trust Security
Zero-trust identity is built on the principle: never trust, always verify.
Identity fabric enables this by supporting:
- Continuous authentication, where the user's identity is verified throughout the session
- Context-aware access, using signals like device posture and location
- Policy enforcement across systems, ensuring consistent access control
Instead of relying on a single authentication event, identity fabric continuously evaluates trust, making it ideal for zero-trust deployments.
Identity Fabric vs. Identity Infrastructure
Identity infrastructure refers to the underlying systems, such as directories, identity providers, and authentication services.
Identity fabric sits above this infrastructure and connects it. While infrastructure provides the building blocks, identity fabric provides the intelligence and orchestration needed to unify them.
Identity Fabric vs. Converged Identity
Converged identity, or converged IAM, is a security approach that brings together several identity solutions, such as access management, Identity Governance and Administration (IGA), and Privileged Access Management (PAM), into a single, unified platform. It also aims to unify customer, workforce, and partner identities into a single system.
Identity fabric takes a different approach. It connects multiple identity systems rather than forcing consolidation. This makes it more flexible and easier to implement in complex environments.
What are the Principles of Identity Fabric Immunity?
The principles are listed as:
- Continuous Verification: Access decisions are not static. Identity fabric continuously evaluates user behavior and context to ensure ongoing trust.
- Zero Trust: Identity fabric enforces zero trust identity principles by verifying every access request regardless of origin.
- Least Privilege: Users are granted only the access they need. Identity fabric dynamically adjusts permissions based on roles and context.
Identity fabric immunity is about continuously verifying identities, enforcing zero trust by default, and tightly limiting privileges so breaches are contained before they spread.
Use Cases of Identity Fabric
Here’s where you can see Identity Fabric in action:
- Multi-Cloud Identity Management: Organizations can manage identities consistently across multiple cloud providers without duplicating policies.
- NHIs and Agentic AI: Non-human identities such as service accounts and AI agents require secure access. Identity fabric provides visibility and control over these identities.
- Mergers and Acquisitions: During M&A, integrating identity systems is complex. Identity fabric allows organizations to connect systems quickly without full consolidation.
- Hybrid and On-premise Environments: Identity fabric bridges the gap between legacy systems and modern cloud applications, ensuring better access control.
- Customer Identity (CIAM): Identity fabric enhances the Customer Identity and Access Management (CIAM) solution by connecting customer identity systems with backend services, improving user experience and security.
- Workforce IAM Integration: Employees often use multiple tools. Identity fabric ensures consistent access policies across all workforce applications.
- API Security: APIs are critical attack surfaces. Identity fabric secures API access by enforcing authentication and authorization policies.
- Governance and Compliance: Identity fabric provides centralized visibility, making it easier to enforce governance policies, track access, meet regulations, and be audit-ready.
For enterprises that are looking to inculcate an identity fabric, the above are some of the most sought-after places where you can apply and see visible results.
Identity Fabric for Compliance and Security
Identity fabric security plays a key role in meeting regulatory requirements such as SAMA, PCI DSS, ISO 27001, GDPR, and more.
It supports compliance by:
- Centralizing policy enforcement across systems
- Generating audit-ready logs for all identity activities
- Ensuring consistent access control across environments
This reduces the risk of compliance gaps and simplifies audit processes.
Challenges in Implementing Identity Fabric
Challenges in implementing an identity fabric are very real. Framing them clearly helps you set expectations with stakeholders and secure the time, budget, and skills you actually need.
- Integration Complexity: Connecting multiple legacy and modern systems, each with its own protocols, can be challenging without a clear integration strategy, reference architecture, and phased rollout plan.
- Legacy Systems: Older or custom applications may lack modern API or standards support, forcing teams to rely on proxies, adapters, or custom connectors.
- Skill Requirements: Successful deployments require people who understand identity orchestration, protocols like SAML, OIDC, and SCIM, and API‑based integration, which may mean upskilling your existing IAM team or bringing in specialists.
- Initial Setup Effort: Designing the fabric architecture, selecting tooling, building reusable patterns, and onboarding the first wave of applications demands significant upfront time and investment before visible business value appears.
Overcome these challenges by ensuring support for open standards and protocols (OIDC, SAML, SCIM, OAuth) and getting the right skillset. Also, adhering to the right skillset, such as monitoring audit flows, centralizing policies, and API-driven integration.
How to Choose the Right Identity Fabric Solution
Selecting the right identity fabric solution requires evaluating several factors. Look for strong integration capabilities that support both legacy and modern systems. Ensure the platform can scale with your business and handle increasing identity workloads.
Security features should include advanced authentication, risk-based access, and support for zero-trust identity. Compliance support is equally important, especially for regulated industries.
Finally, consider the vendor ecosystem. A solution with a broad partner network and pre-built connectors will significantly reduce implementation time.
Why Identity Fabric is the Future of IAM
Identity fabric represents the evolution of modern IAM architecture. It addresses the limitations of traditional systems by providing flexibility, scalability, and interoperability.
It supports multi-cloud environments, enables zero trust deployments, reduces operational complexity, and improves organizational agility. As businesses continue to adopt distributed architectures, identity fabric will become a foundational component of identity strategy.
The Shift Toward Unified Control
Identity fabric is not just another security trend. It is a practical response to the growing complexity of identity management. By unifying fragmented systems and enabling consistent policy enforcement, it helps organizations achieve secure and scalable identity management.
For enterprises navigating multi-cloud environments, regulatory requirements, and evolving threats, identity fabric offers a clear path forward.
If identity is now your security perimeter, your next step is clear. Evaluate identity fabric options and pilot them on one high‑value, low‑risk application set to prove out the model. Contact us today, and we will guide you through.
FAQs
What is identity fabric?
Identity fabric is an architectural framework that connects and orchestrates multiple identity systems to provide unified identity management.
How is identity fabric different from IAM?
IAM is a broader concept that manages identities and access, while identity fabric is a modern architecture that enhances IAM by connecting multiple systems.
Is identity fabric a product or architecture?
Identity fabric is primarily an architecture, though many vendors offer platforms that implement its principles.
Why is identity fabric important for Zero Trust?
Identity fabric enables continuous verification, context-aware access, and consistent policy enforcement, which are essential for zero-trust identity.

Leave a Comment