Jira Using SCIM User and Group Provisioning for Microsoft Entra ID
User Sync & Group Sync app provisions user and group information from Microsoft Entra ID (Previously known as Azure AD) to Jira, Confluence and Bitbucket. Users, groups and directory details can by provisioned using SCIM and REST API. SCIM provisioning works based on events performed on IDP. This way the administrator only needs to manage user accounts in Microsoft Entra ID (Previously known as Azure AD). This reduces the administration time required to create users and groups in Atlassian modules such as Jira, Confluence and Bitbucket.
Video Setup Guide
Download and Installation
- Log into your atlassian instance as admin.
- Navigate to the settings menu and Click Manage Apps.
- Click on Find new apps .
- Locate miniOrange User and Group Sync app.
- Click Try free to begin a new trial or Buy now to purchase a license.
- Enter your information and click Generate license when redirected to MyAtlassian.
- Click Apply license.
Step 1: Get SCIM Client Details
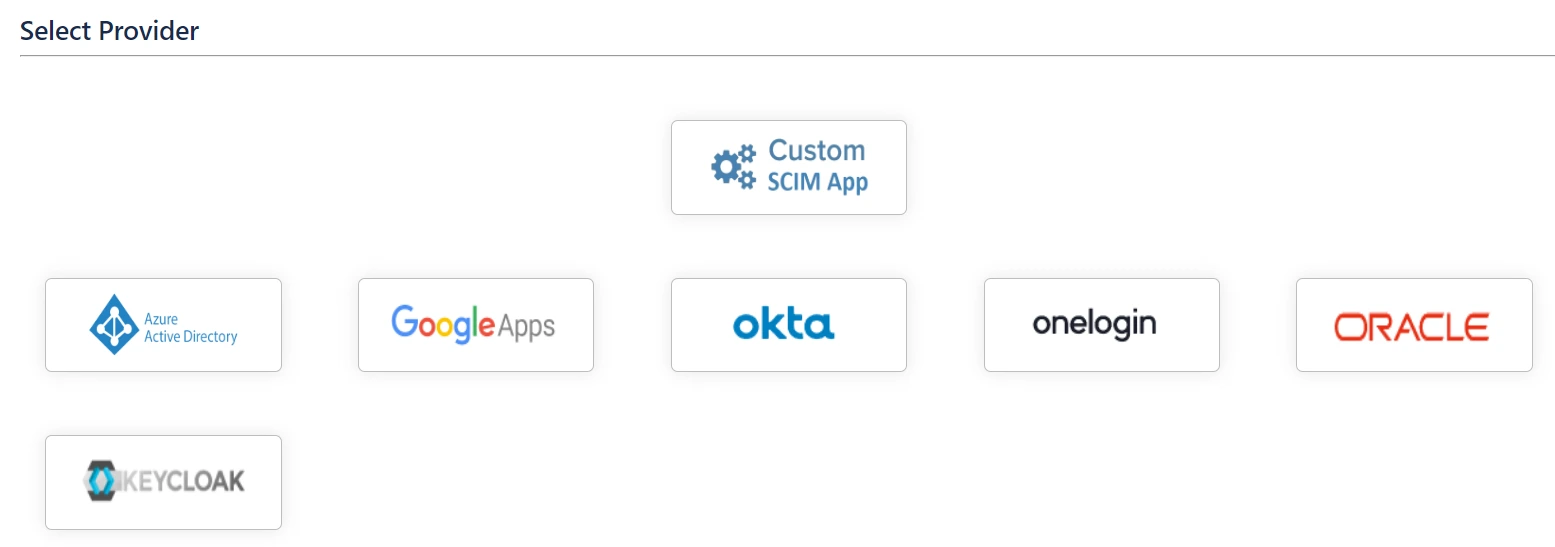
- In the Configuration tab, please select Microsoft Entra ID (Previously known as Azure AD) provider.
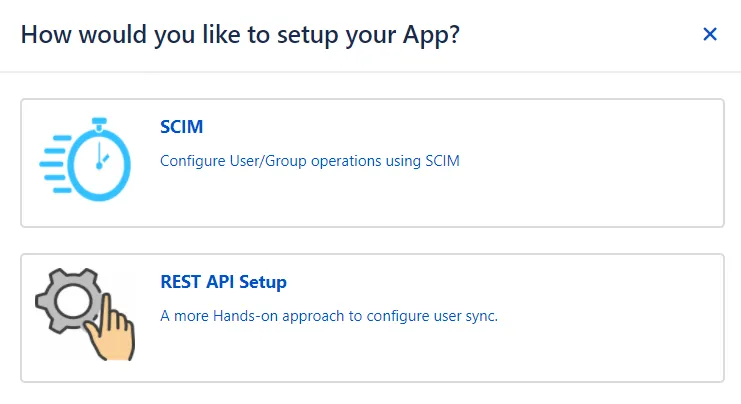
- In the popup, please select SCIM method to perform user and group synchronization.
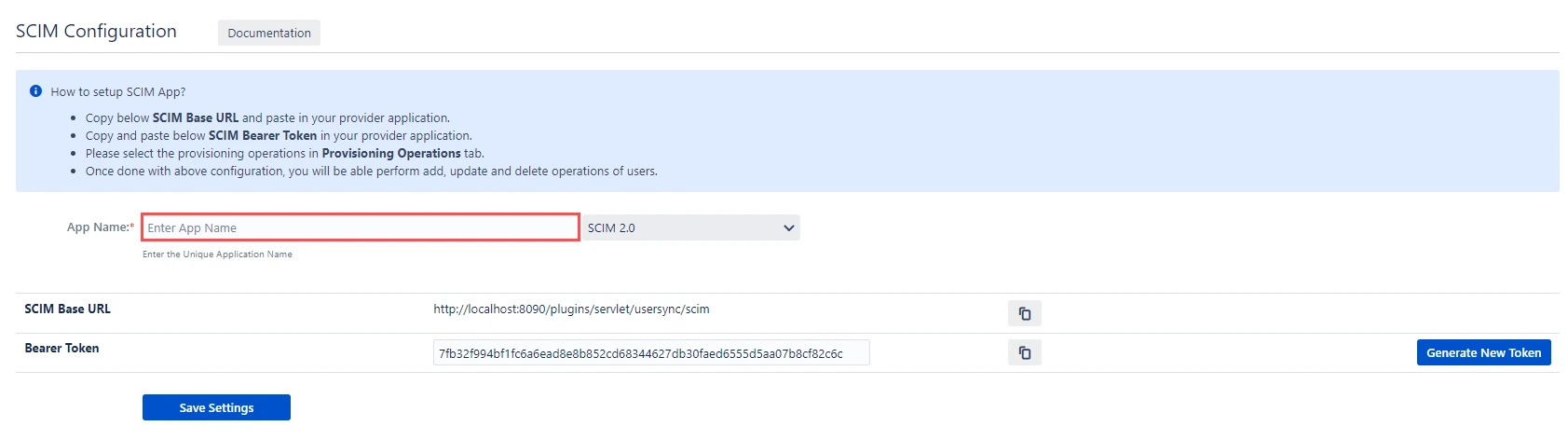
- In SCIM configuration, Please enter App Name and click on Save Settings button. Copy the SCIM Base URL and SCIM Bearer Token, these will be used later to configure SCIM application on Microsoft Entra ID (Previously known as Azure AD).
Step 2: Setup Microsoft Entra ID (Previously known as Azure AD) SCIM Configurations
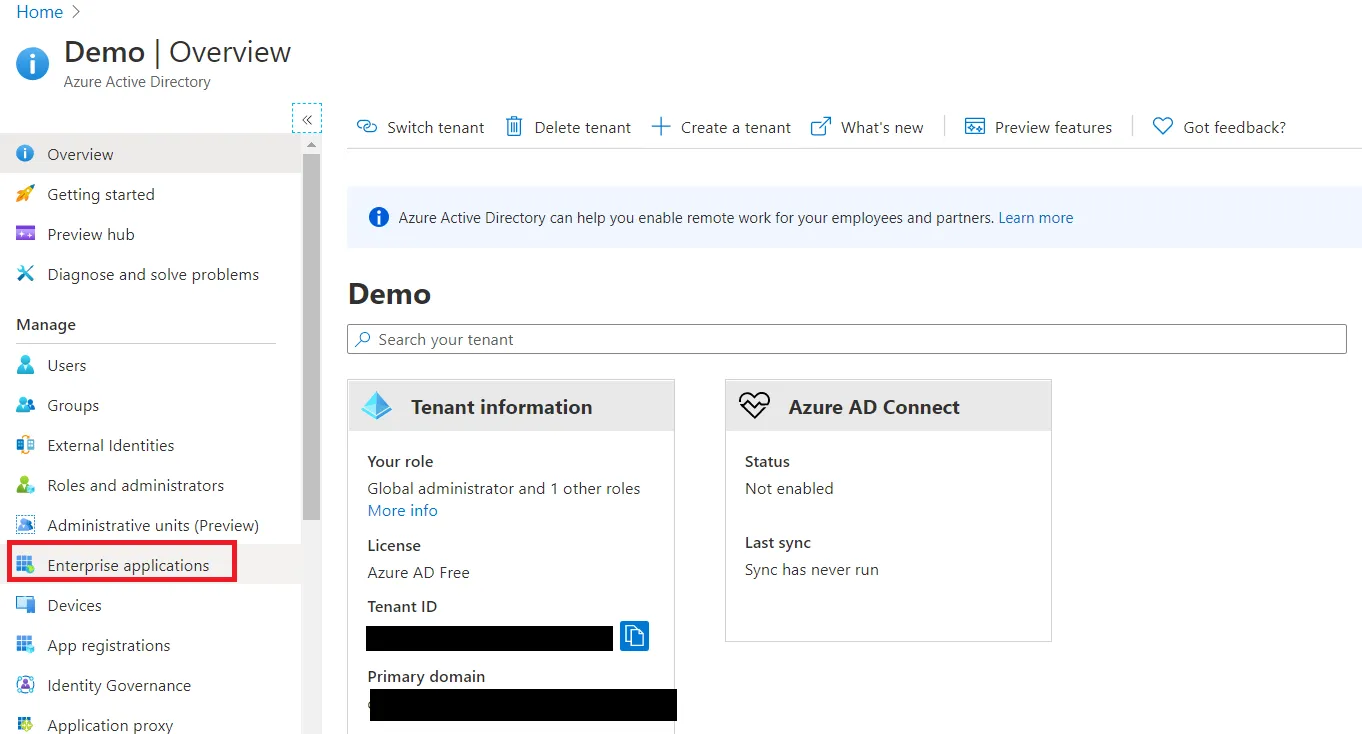
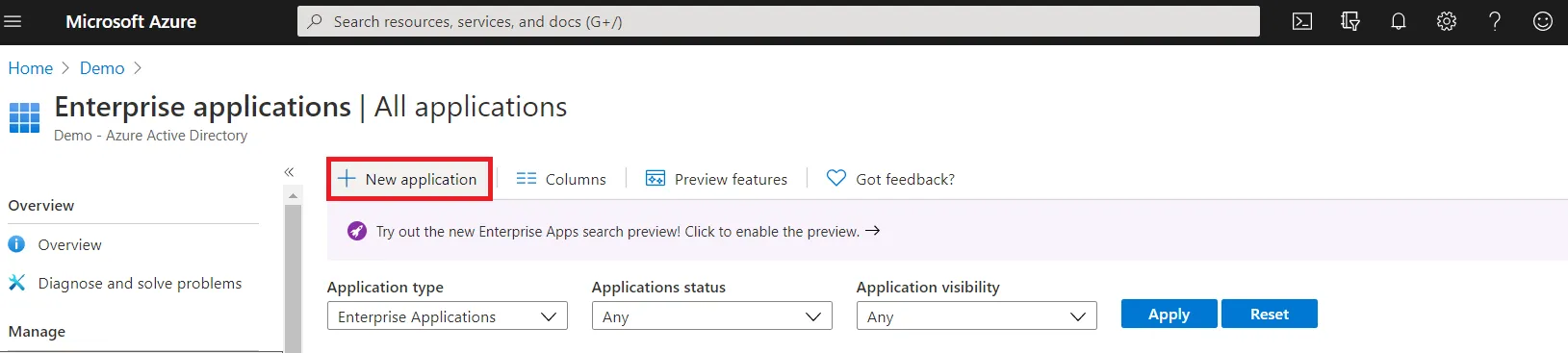
- Log in to your Microsoft Entra ID (Previously known as Azure AD) portal and select the Microsoft Entra ID. Then create an Enterprise application.
- Click on New Application and select non-gallery application.
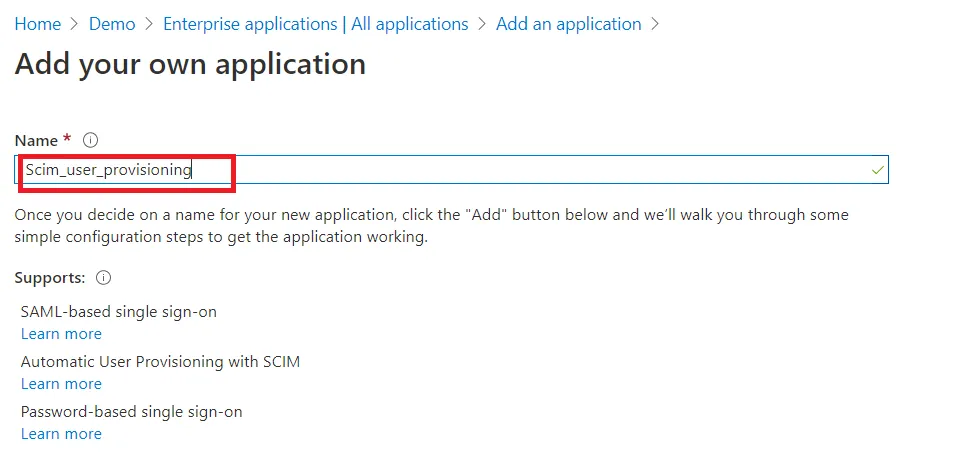
- Give suitable name to your user provisioning application.
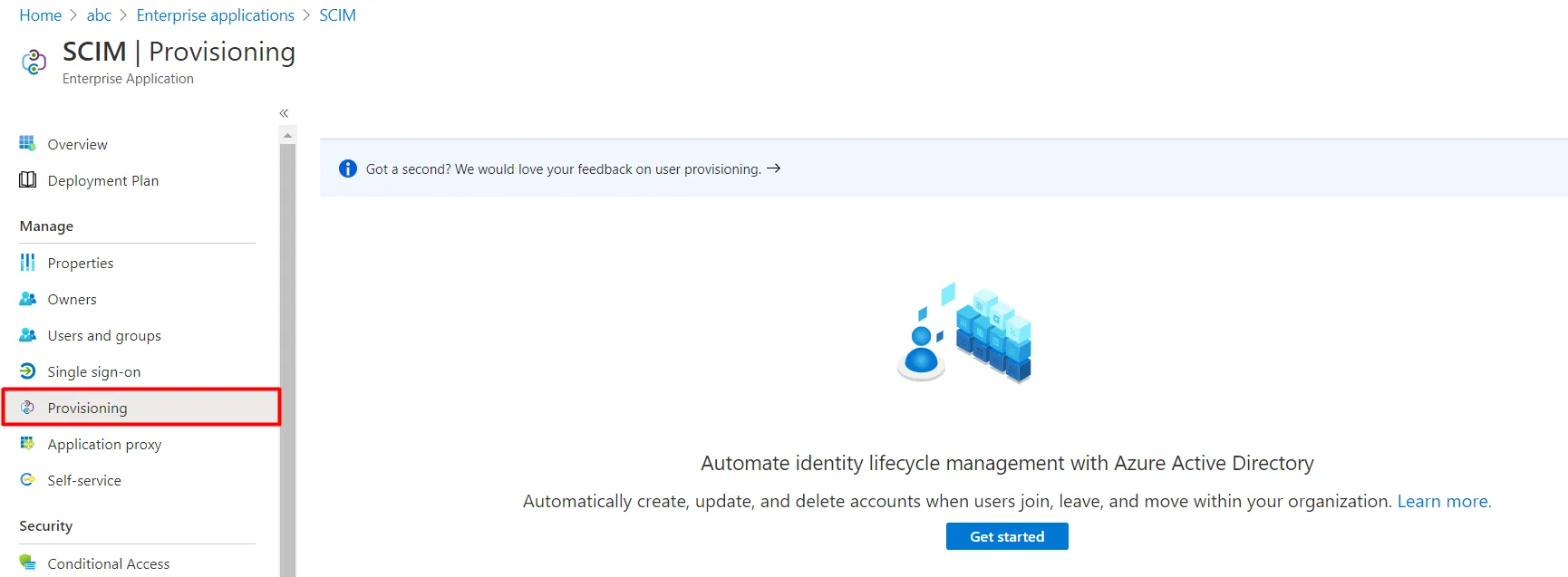
- Click on Provisioning in left menu and click on Get started.
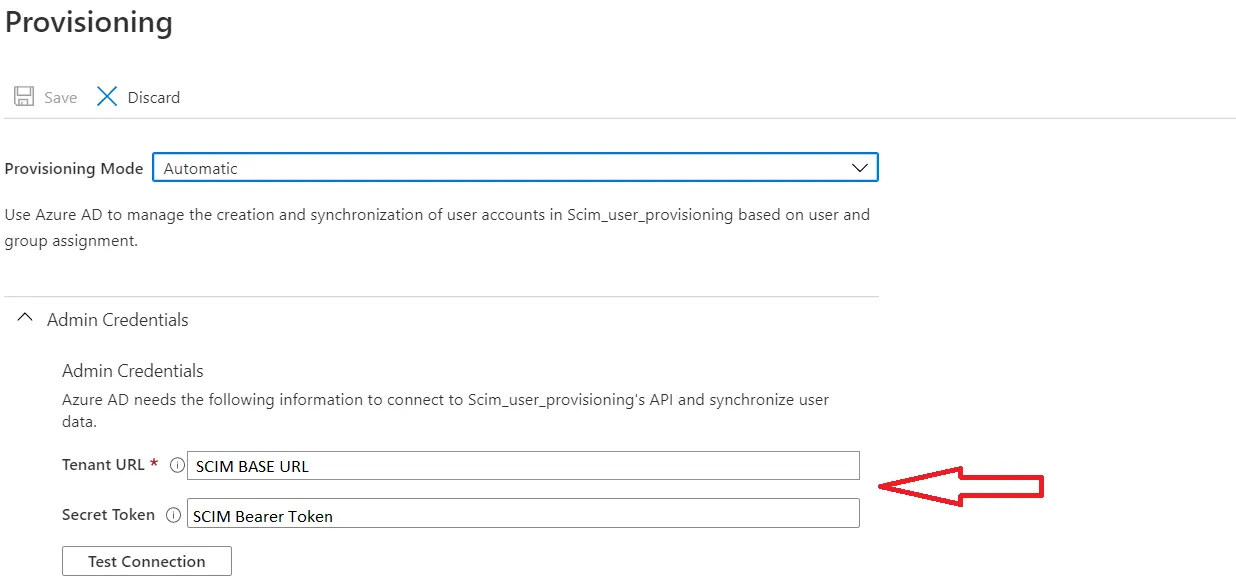
- Select Automatic in Provisioning Mode and Enter SCIM Base URL, SCIM Bearer Token (which you will find in step 1) .
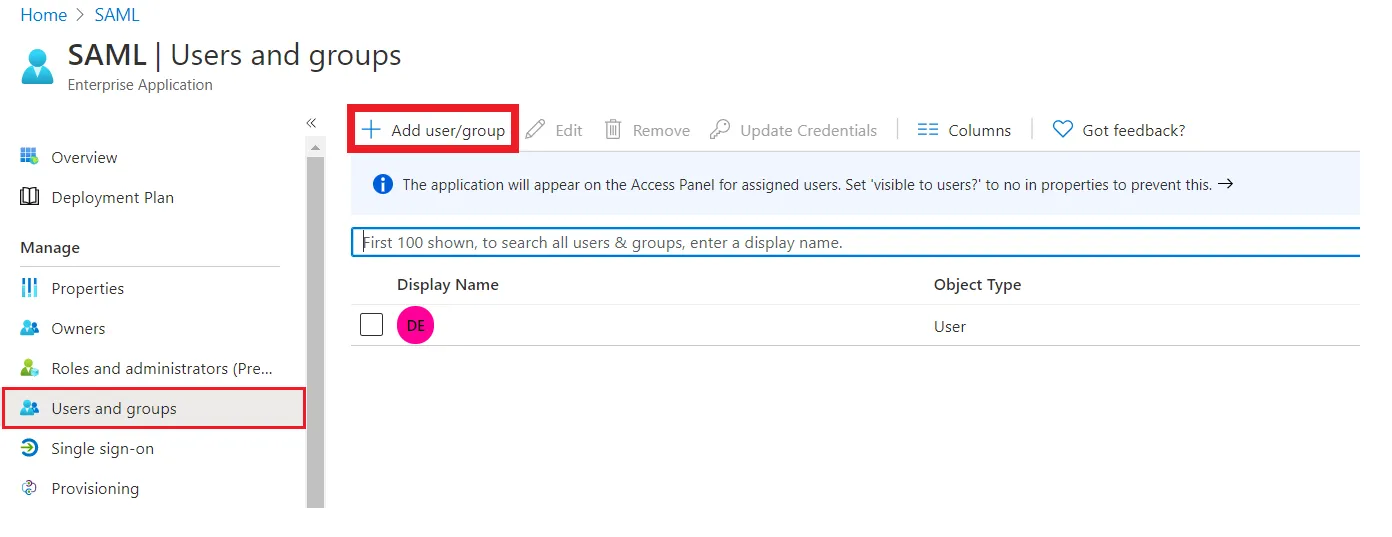
- Assign users to your applicartion. Assigned users will be created in your Atlassian module if they are not already present. You can also assign groups. Member of assigned groups will be provisioned for Atlassian module.
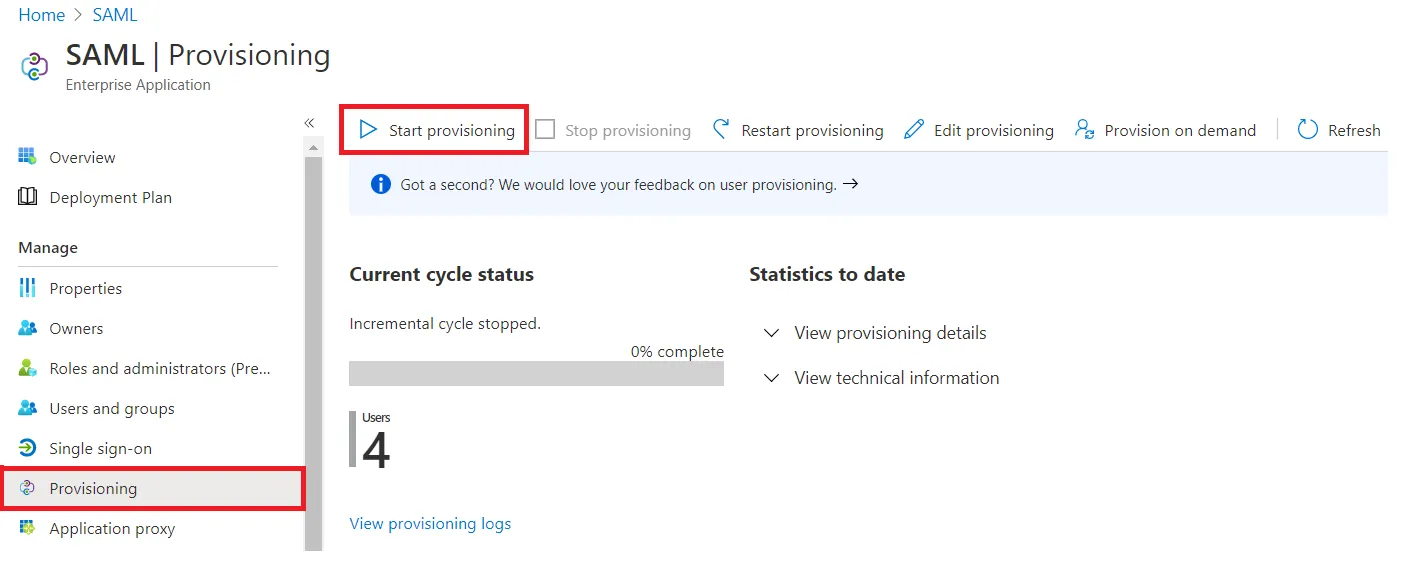
- Once done with configuration, Go back to application and click on Start provisioning.
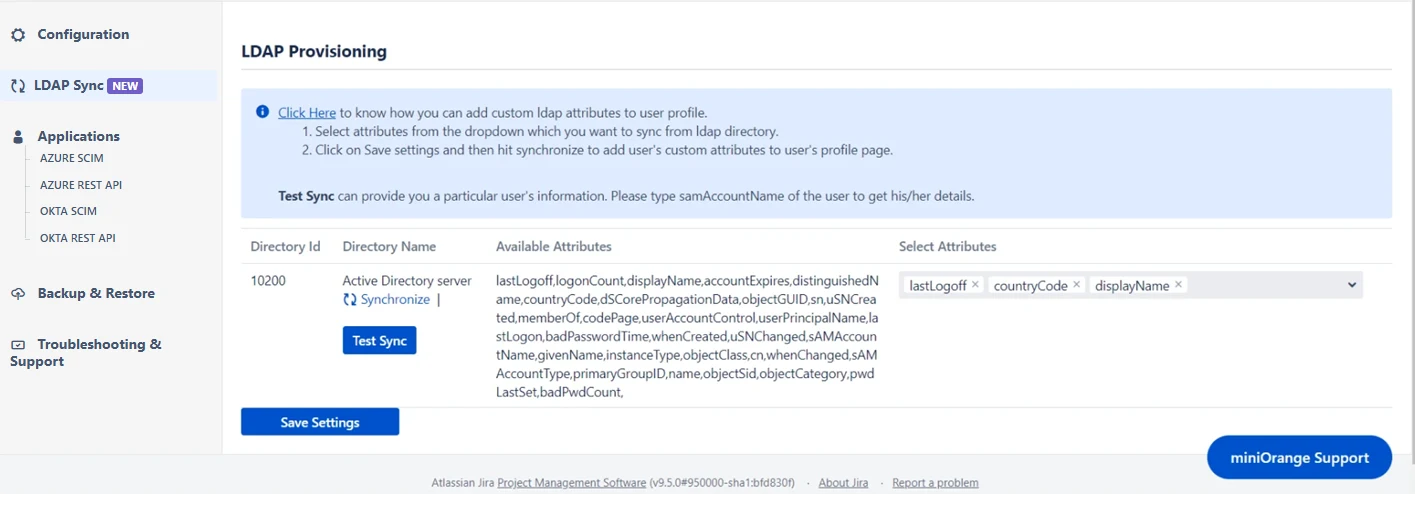
Step 3: LDAP Sync Settings
- The miniOrange user sync app now provides support for LDAP Sync. Follow the instructions to configure the LDAP directory. By configuring the LDAP directory, you can synchronize all attributes from your LDAP directory and choose the attributes you wish to include in Jira.
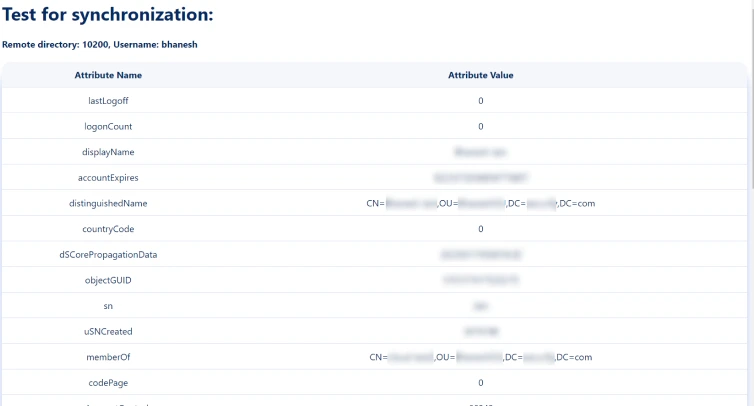
- Once you have successfully configured the LDAP directory in Jira/Confluence, you can test the specific user’s attributes by using the Test Sync button.
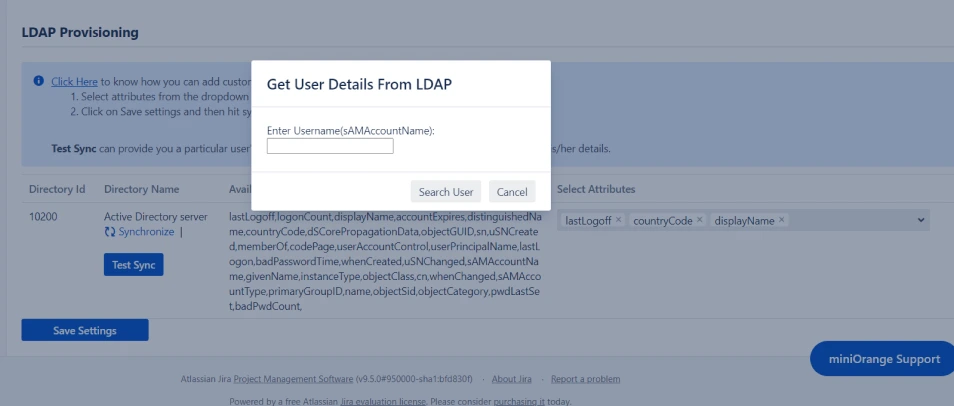
- To test your configuration, enter an username(sAMAccountName) from your directory's user data and click on the Search User button. You will then be able to view the details of the searched user.
Step 4: User Sync Settings
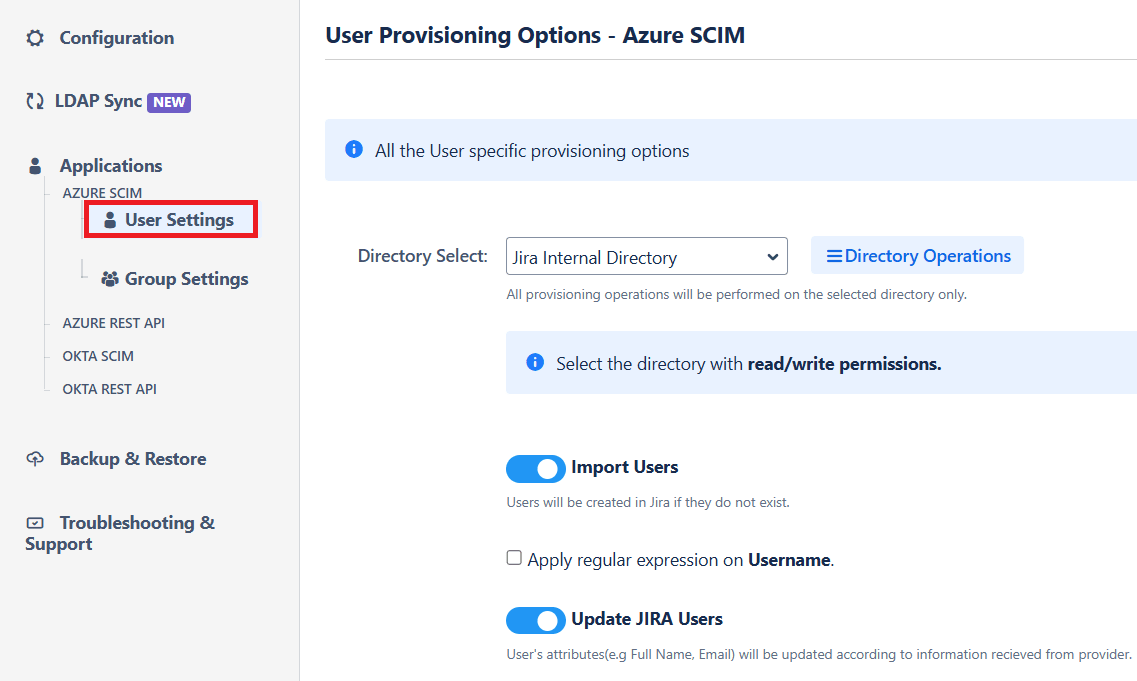
- Select the User Sync Settings tab from the left sidebar. Here you can configure different settings about user creation and updation.
- You can select the directory, enable or disable user import, update process.
- The user can be automatically enabled or disabled here based on IDP configuration.
- You also have an option to set Default Project Lead and Default Component Lead.
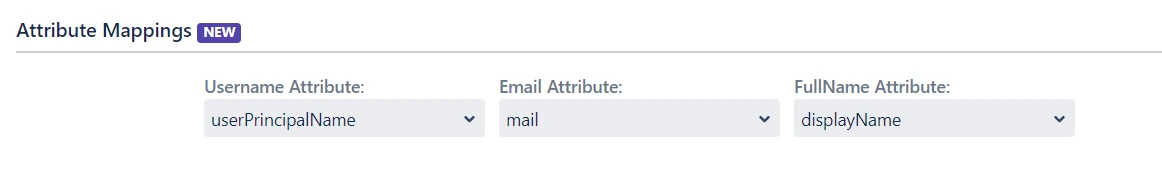
- Attribute mapping enables you to map your attributes sourced from the IDP to Jira attributes. Through this section you can map your jira attributes to the attributes coming from IDP. By default, username attribute corresponds to the username/userPrincipalName attribute, email corresponds to the email/mail attribute, and displayName corresponds to the full name attribute. However, if you want to map these jira attributes with other attributes coming from IDP, you can use this feature to change the attribute mapping configurations.
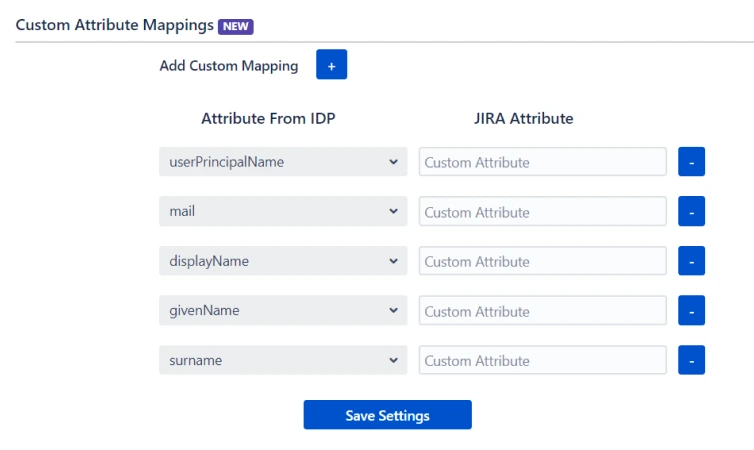
- User sync also supports mapping of custom attributes. Here, you can create custom attributes and automatically assign values to them from the IDP (Identity Provider). Select the desired attributes from the IDP that you want to display in Jira and provide a name for the custom attributes to be shown in Jira.
- Custom fields will be displayed in the user profile section as shown below
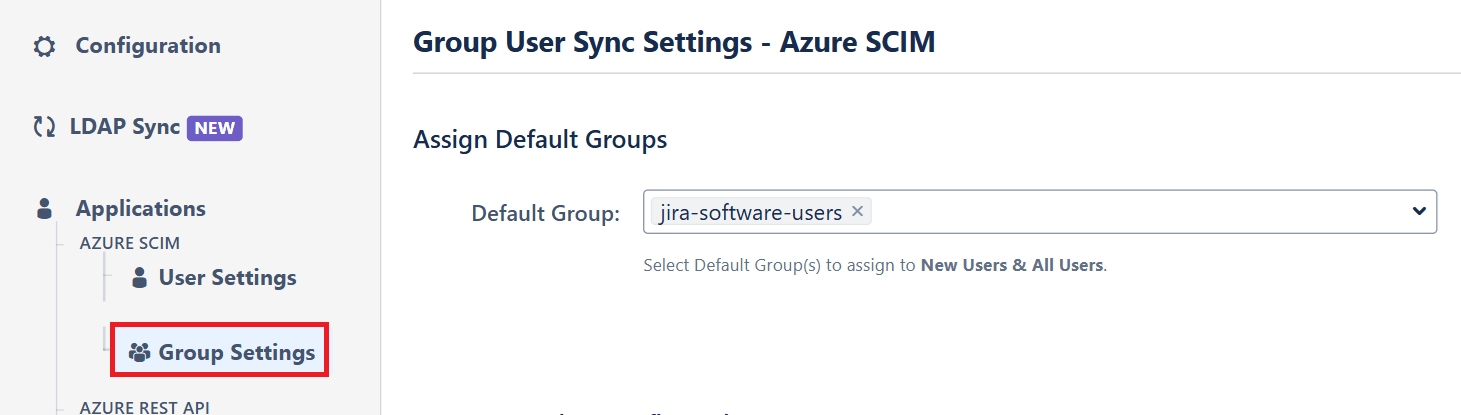
Step 5: Group Sync Settings
- Select the Group Sync Settings tab from the left sidebar. Here you can configure different settings about group creation and group mapping.
- Here you can configure Default groups for new and all users.
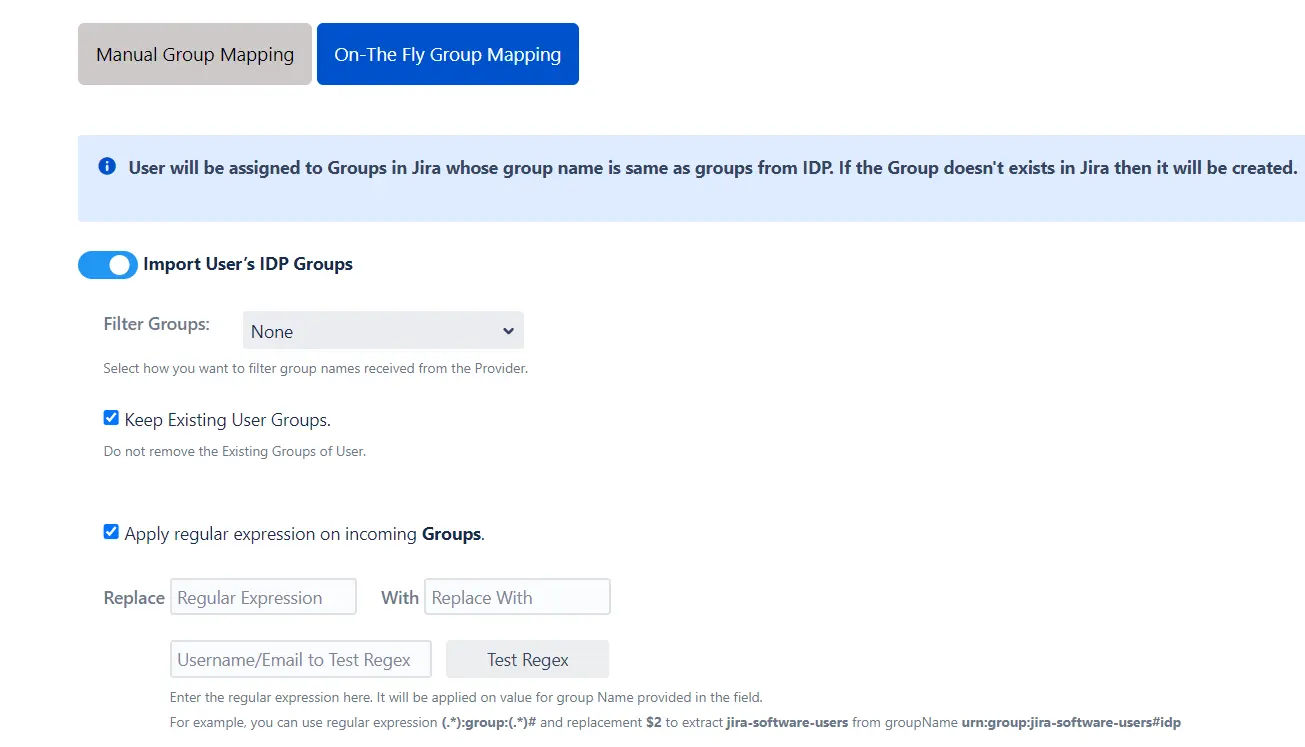
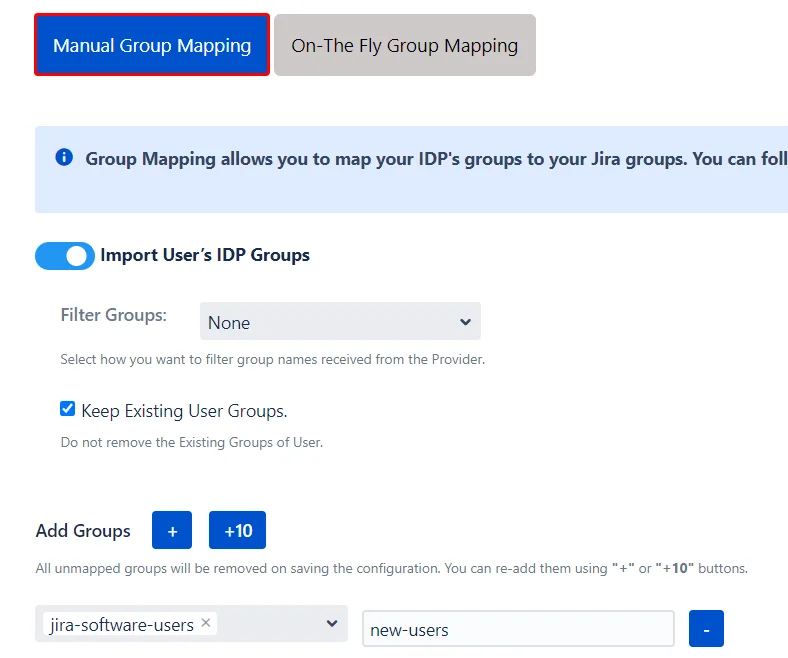
- You can set Manual Group Mapping or On-The Fly Group Mapping.
- Here users will be assigned to groups in Jira whose group name is the same as groups from IDP. If the group doesn't exist in Jira then it will be created.
- You can configure to keep the existing user groups, filter groups and apply regular expressions on the groups.
- Here you can manually map Jira groups with the groups from IDP.
- You can also configure to import IDP groups, filter groups and whether to keep existing users or not.
1. On-The Fly Group Mapping -
2. Manual Group Mapping -
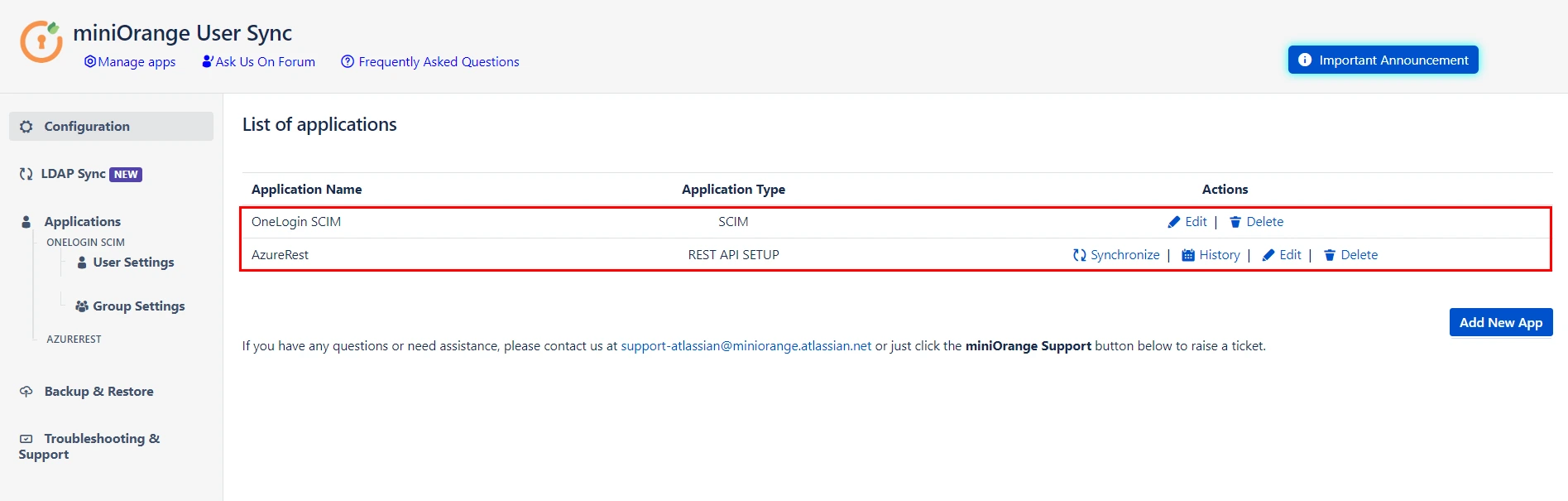
Step 6: Multiple IDPs
- The plugin allows for configuring SCIM provisioning on your SP (Service Provider) to accommodate your specific use case. To add another IDP, simply navigate to the "Configured IDPs" section. Select on Add new App to configure multiple provisioning connections.
Did this page help you?
×
![]()

 Try it for free
Try it for free