Need Help? We are right here!
Search Results:
×






Legacy access methods force teams to bypass security protocols for the sake of speed, creating critical security blind spots in your infrastructure.
Stop choosing between team productivity and Zero-Trust security. miniOrange PAM enables multiple authorized users to join a single, secure proxied session under centralized oversight and strict governance policies.
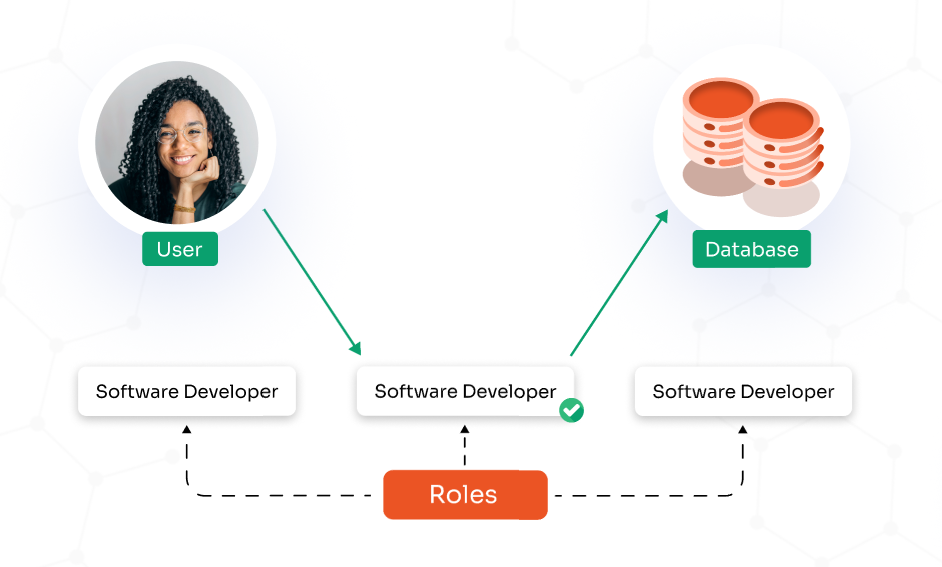
Define exactly who can initiate, join, and interact within a shared privileged session using granular, policy-based permissions.
Administrators can:
Allow multiple authorized users to securely work in the same live SSH or RDP session without creating separate connections to the target system.
miniOrange delivers:
Extend secure session collaboration across all critical infrastructure and platforms from a single PAM control plane.
Supported protocols include:
When a junior administrator encounters a critical issue, they can start a secure privileged session and generate a session-sharing link for a senior engineer. The expert joins instantly, diagnoses the problem in real time, and helps resolve it.
Outcome:

Instead of creating permanent accounts for third-party vendors, internal teams initiate a controlled session and provide temporary, monitored access through a secure link. The vendor performs the required task within the shared session, and access automatically ends when the session closes.
Outcome:
Senior engineers can demonstrate server configuration, database migrations, or deployment workflows in a real production-like environment while team members join the same session in view-only or interactive mode.
Outcome:
During a security incident, SOC analysts, infrastructure teams, and forensic specialists can collaborate within a single live session. All participants work from the same controlled connection, eliminating multiple direct logins.
Outcome:
Grant access through secure, time-bound session links instead of exposing passwords, and replace multiple direct logins with a single controlled connection.
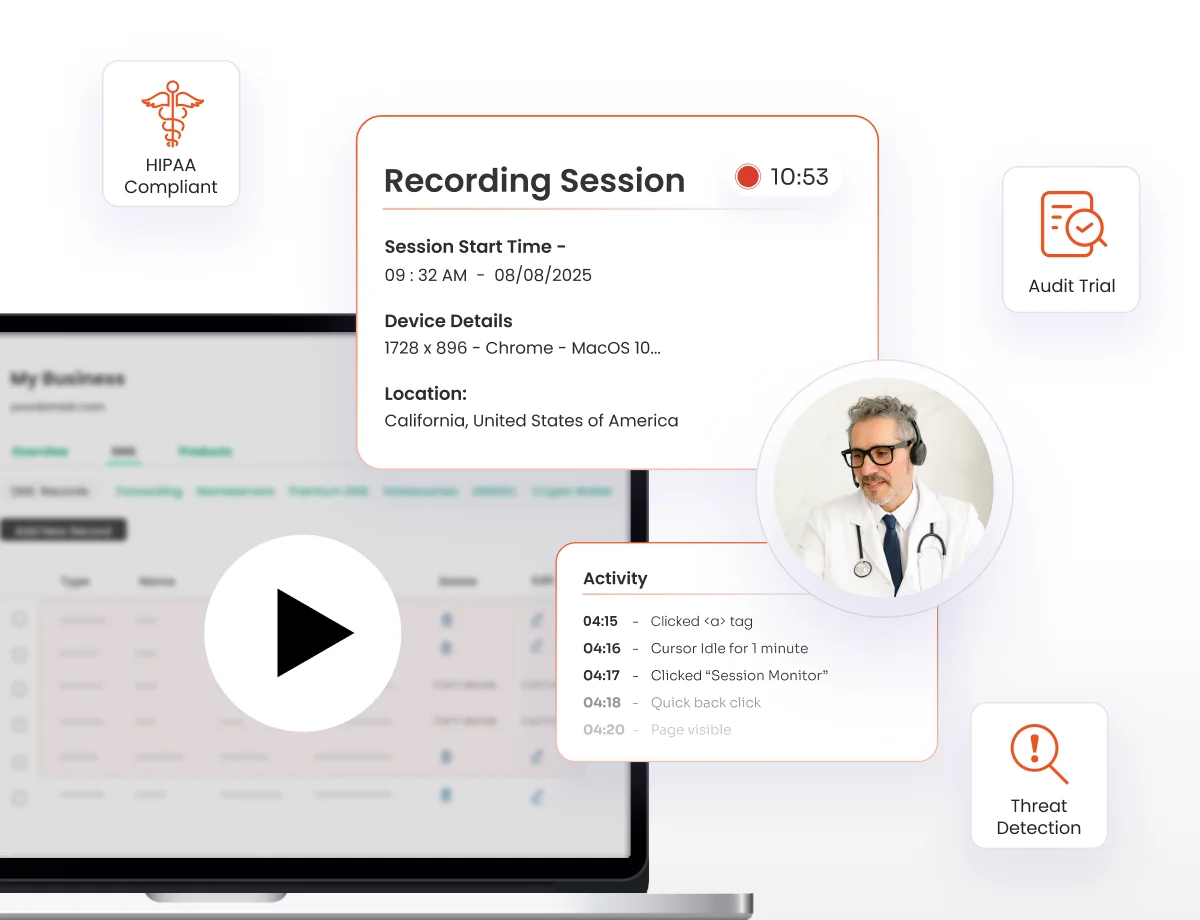
Apply role-based view or control permissions while monitoring every user action in real time through a centralized PAM proxy.
Enable teams like IT, DevOps, MSP, and SOC to collaborate in the same live session to resolve incidents faster and support critical operations without creating standing access.
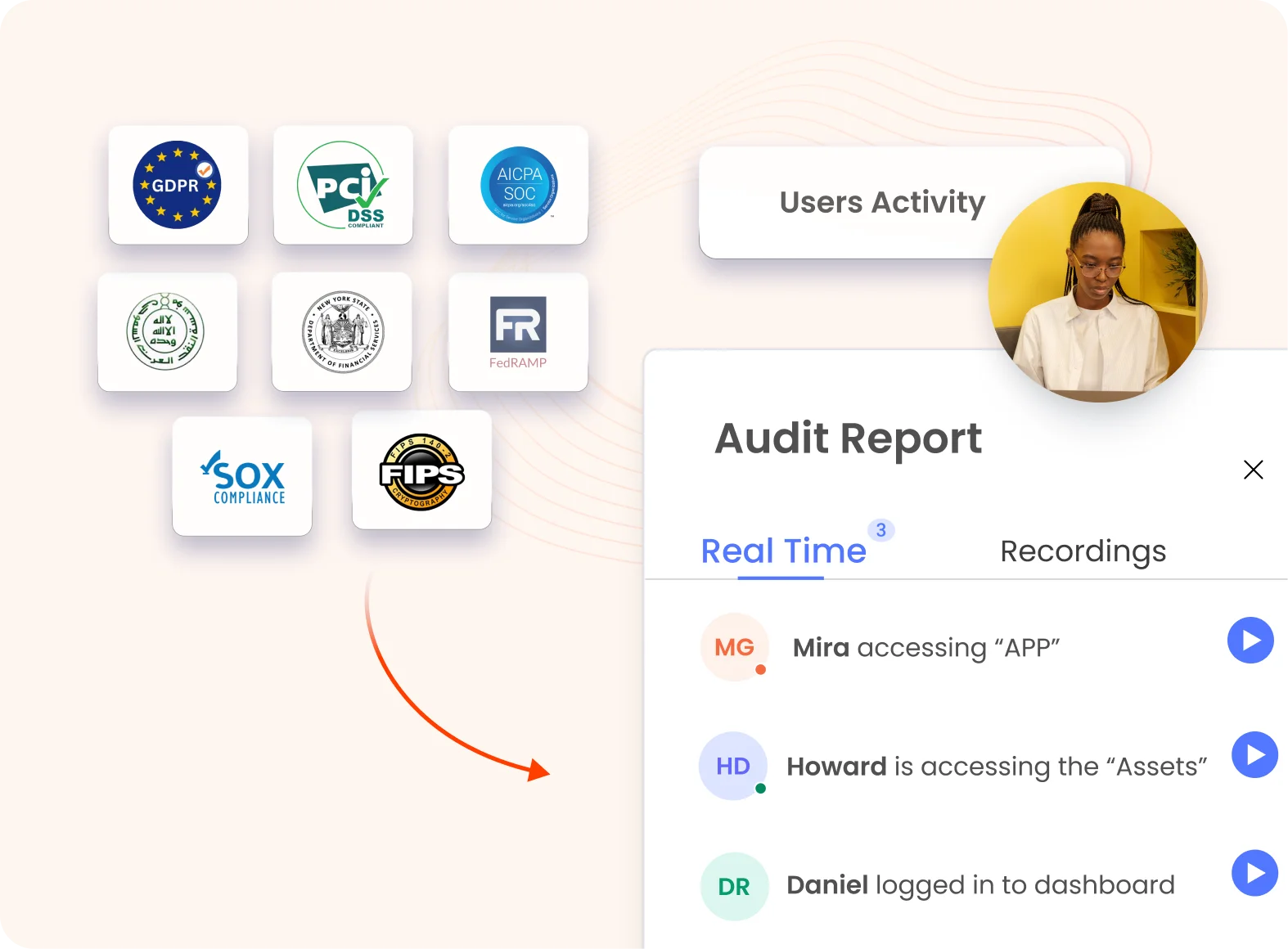
Maintain full session recordings, time-stamped activity logs, and policy-driven access to support ISO 27001, SOC 2, PCI DSS, and HIPAA requirements.
