Contents
SAML Single Sign On (SSO) into Jenkins using ADFS as IDP
Jenkins SAML SSO app gives the ability to enable SAML Single Sign-On (SSO) for Jenkins. Here we will go through a guide to configure Single Sign On (SSO) between Jenkins and ADFS. By the end of this guide, ADFS users should be able to log in and register to Jenkins.
Pre-requisites
To integrate your Identity Provider (IDP) with Jenkins, you need the following items:
- Jenkins should be installed and configured.
- Jenkins Server is https enabled (optional).
- Admin credentials are set up in Jenkins.
Step 1: Setup ADFS as Identity Provider
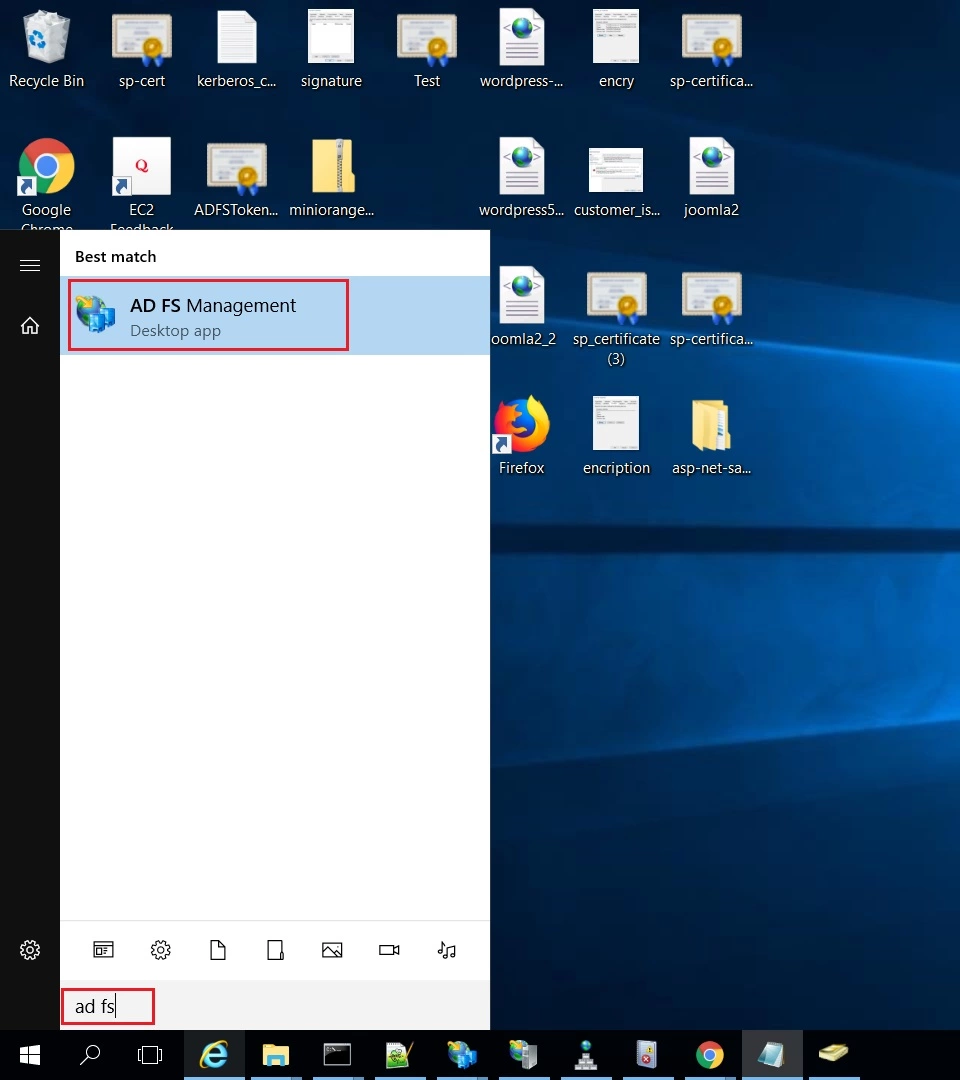
- On ADFS, search for ADFS Management application.
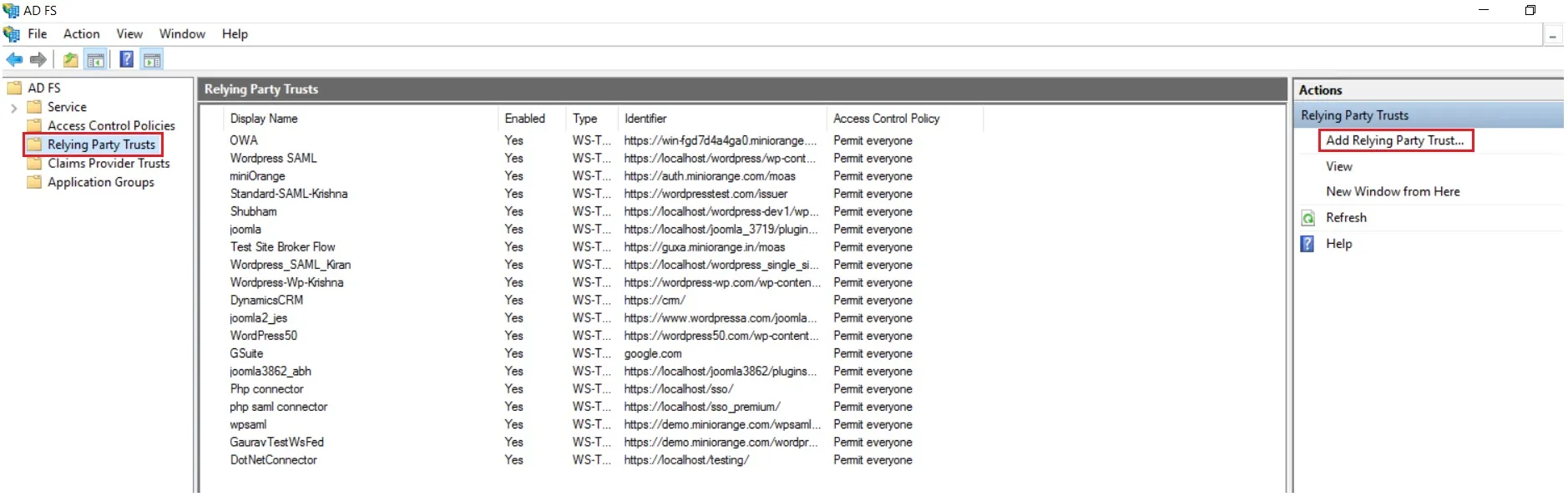
- After opening the AD FS Management, select Relying Party Trust & then click on Add Relying Party Trust.
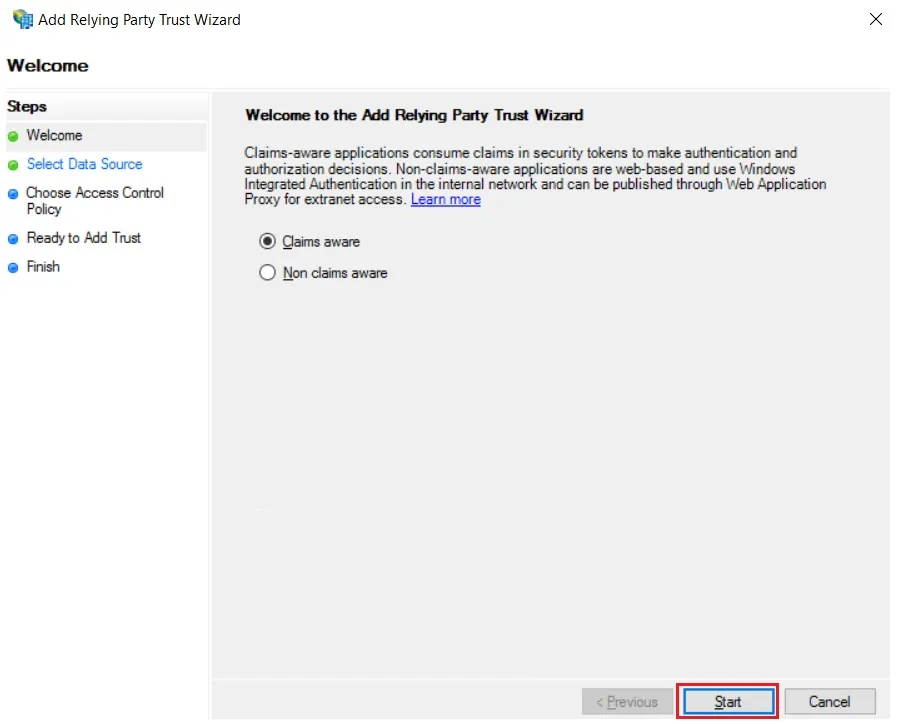
- Click the Start button from the Relying Party Trust Wizard pop up. But before that please make sure Claims Aware is selected.
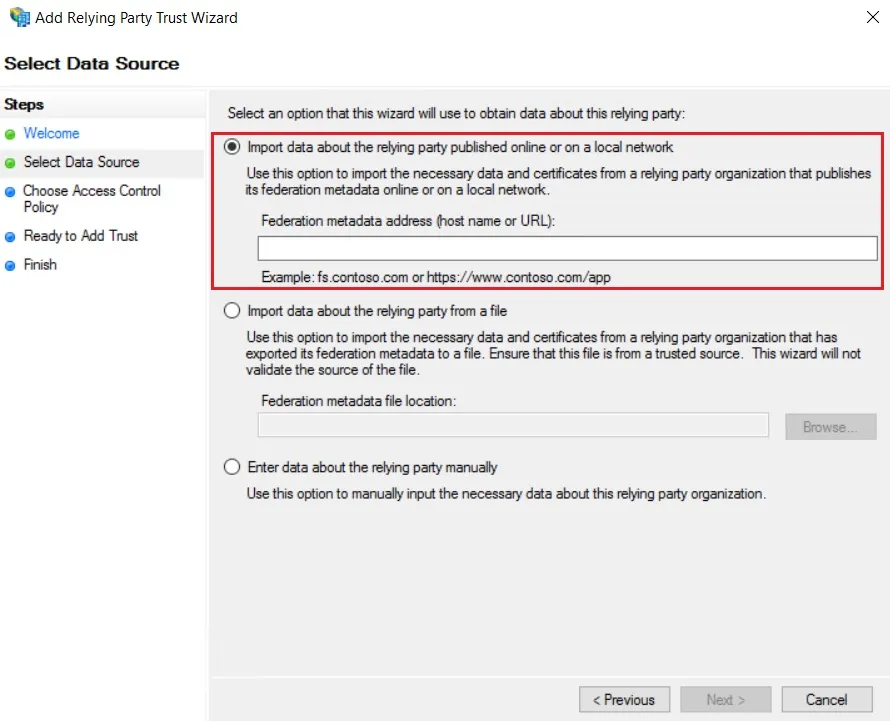
- Select the options for adding a relying party trust.
- In Select Data Source: Import data about the relying party published online or on the local network option & then add URL in Federation metadata address.
- Skip step-5 to step-8 & start configuring from step-9. Navigate to Service Provider Info tab from the plugin for getting SP Meatadata URL.
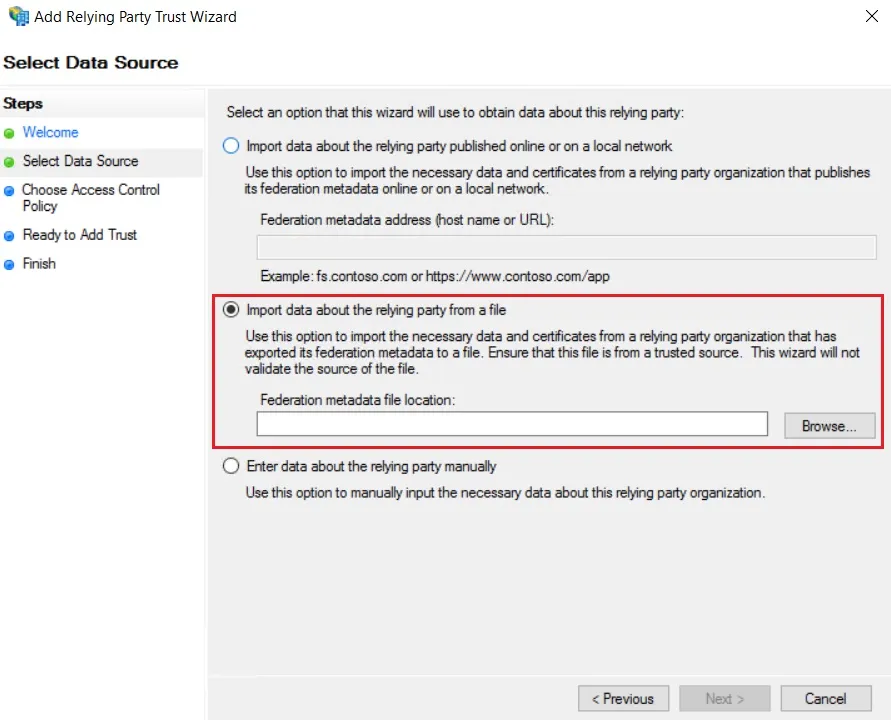
- In Select Data Source: Import data about the relying party from a file option & then browse the metadata file.
- Skip step-5 to step-8 & start configuring from step-9.
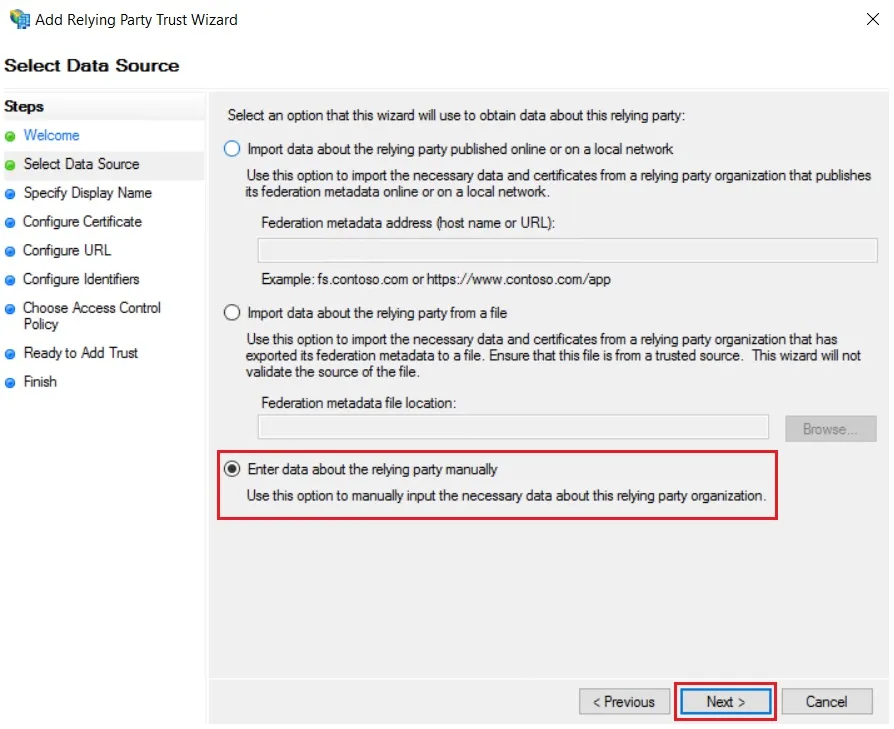
- In Select Data Source: Enter Data about the relying party manually & Click on Next.
- Enter Display Name & Click Next.
- Upload the certificate & click next. Download the certificate from plugin & use the same certificate to upload on ADFS.
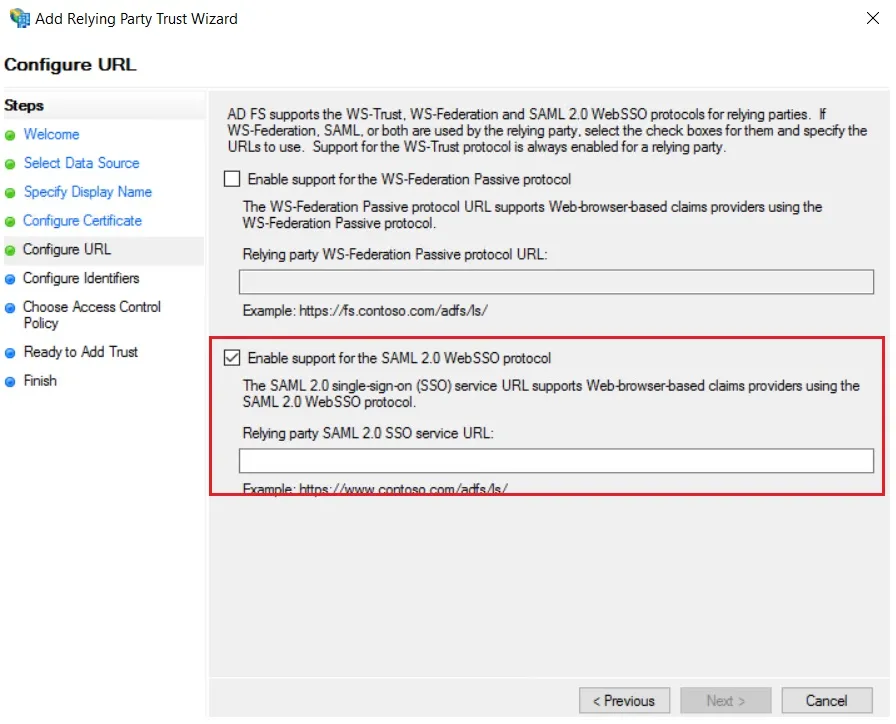
- Select Enable support for the SAML 2.0 WebSSO protocol & Enter ACS URL from the plugins Service Provider Info Tab. Click Next.
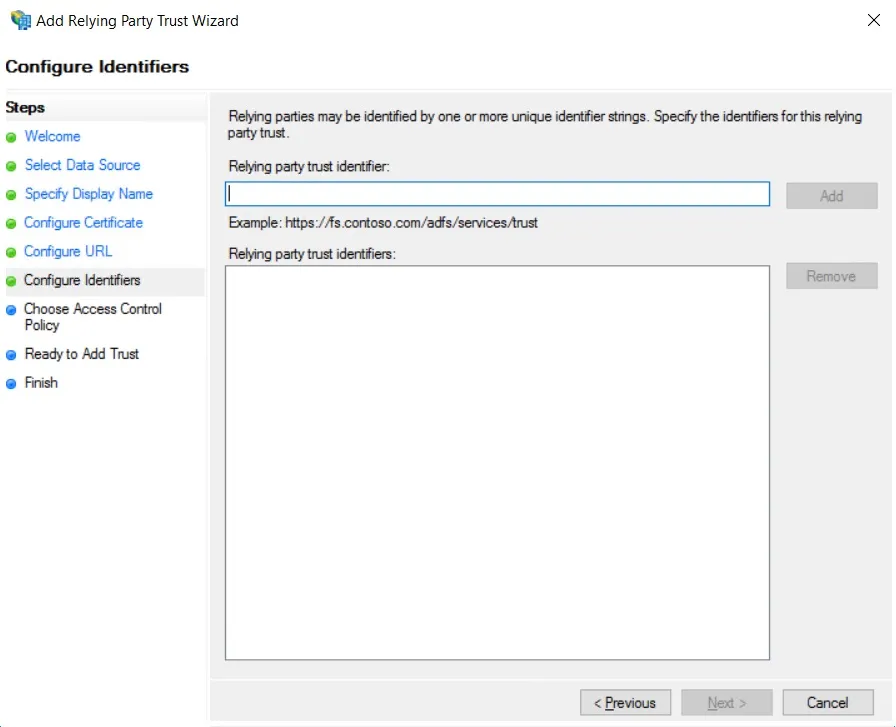
- Add Entity ID from plugins Service Provider Info Tab as Relying party trust identifier then click Add button & then click Next.
- Also download the Signing certificate from Service Provider Info Tab from the plugin.
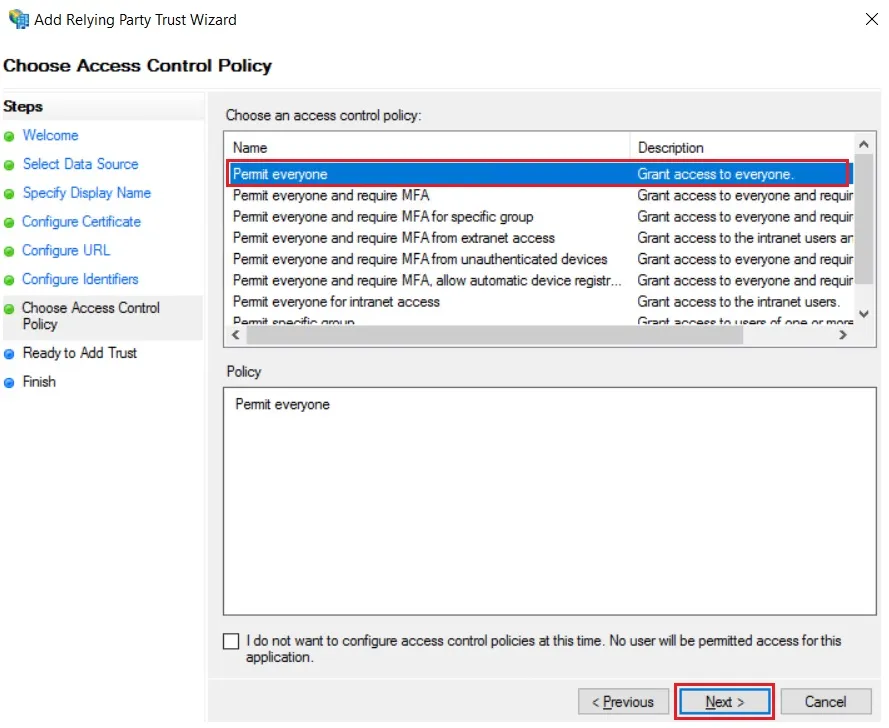
- Select Permit everyone as an Access Control Policy & click on Next.
- Click the Next button from Ready to Add Trust & click Close.
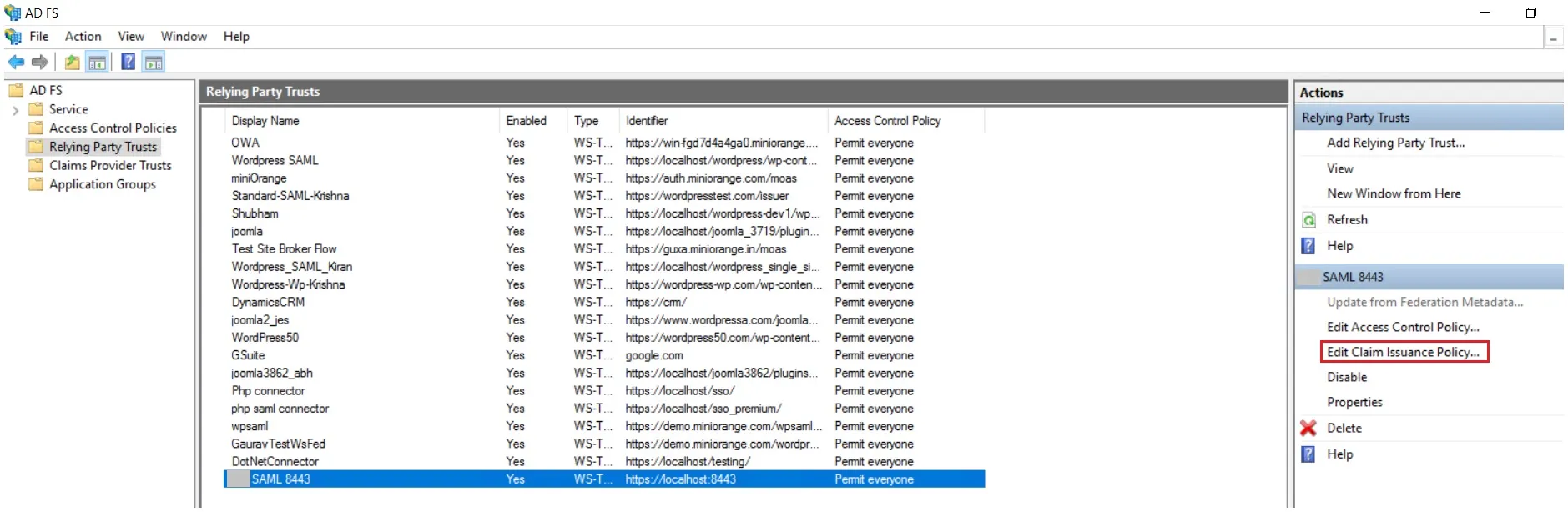
- It will show you the list of Relying Party Trusts. Select the respective application & click on Edit Claim Issuance Policy.
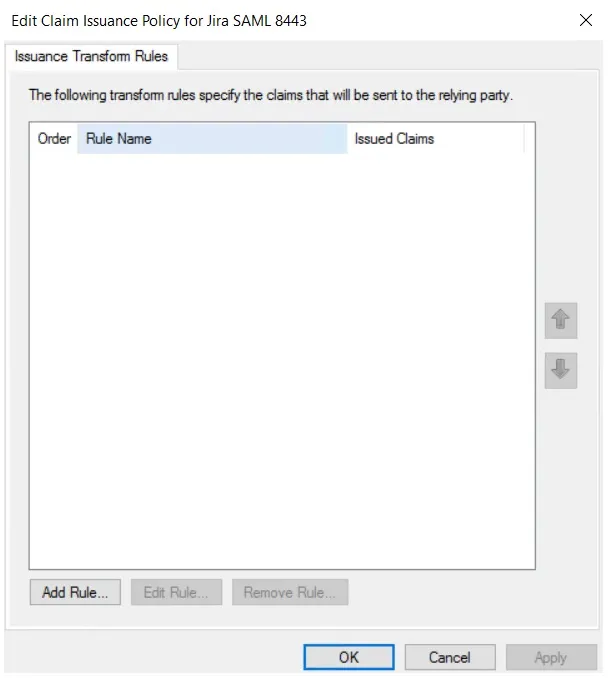
- Click on Add Rule button.
- Select Send LDAP Attributes as Claims & click on Next.
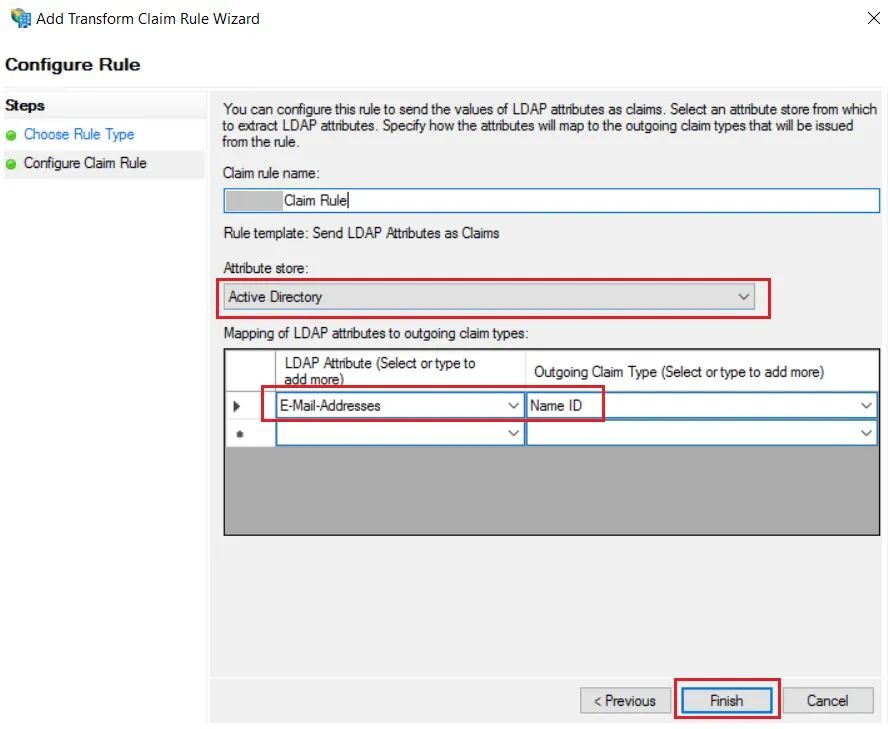
- Enter the following details & click on Finish.
- Click Apply Ok.
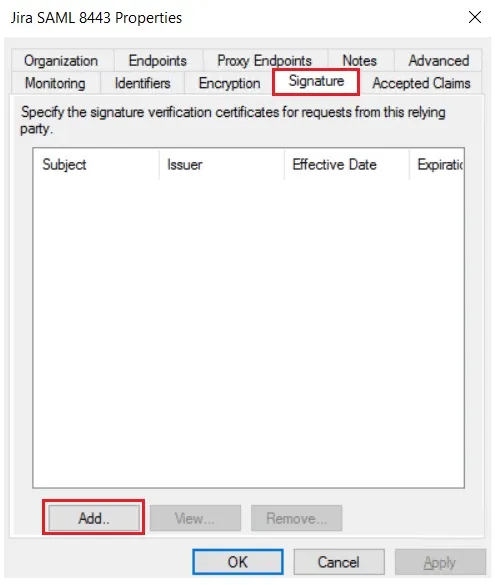
- Select property of the application & add the certificate downloaded from the add-on.
 Using Metadata URL
Using Metadata URL
 Using Metadata XML file
Using Metadata XML file
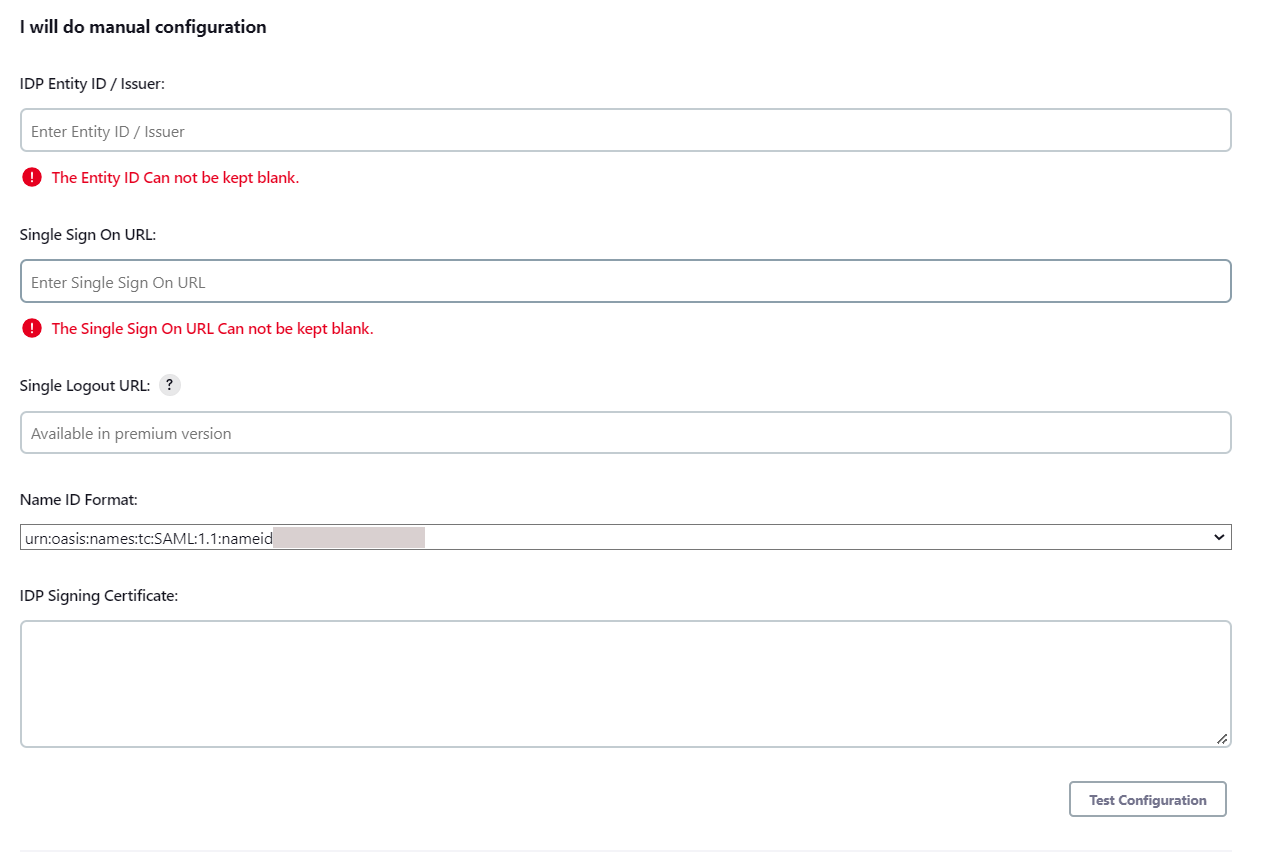
 Using Manual configuration
Using Manual configuration
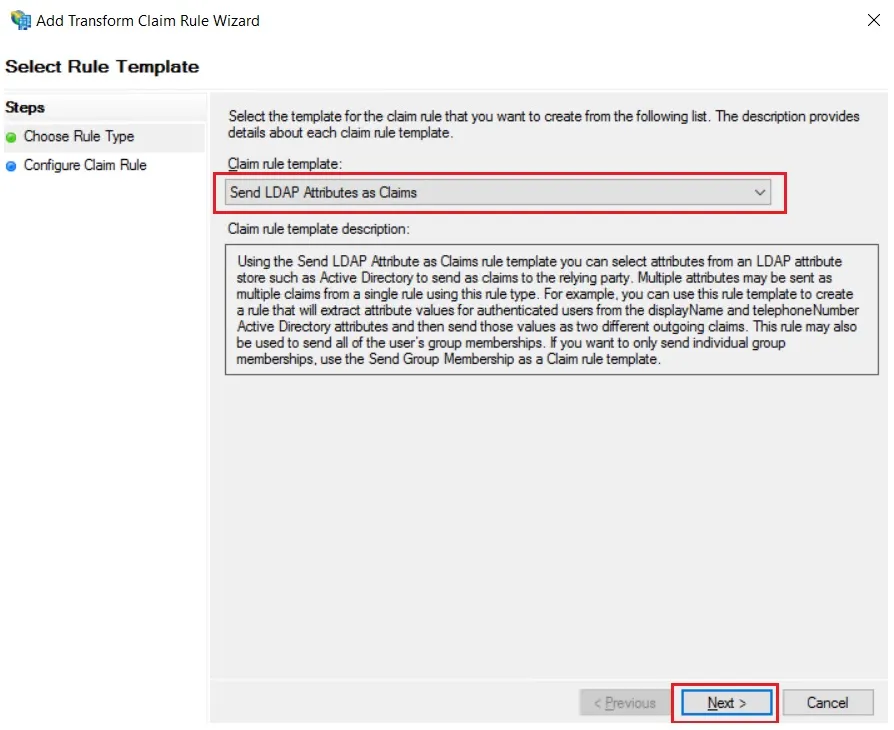
| Claim rule name: | Attributes |
| Attribute Store: | Active Directory |
| LDAP Attribute: | E-Mail-Addresses |
| Outgoing Claim Type: | Name ID |
×
![]()
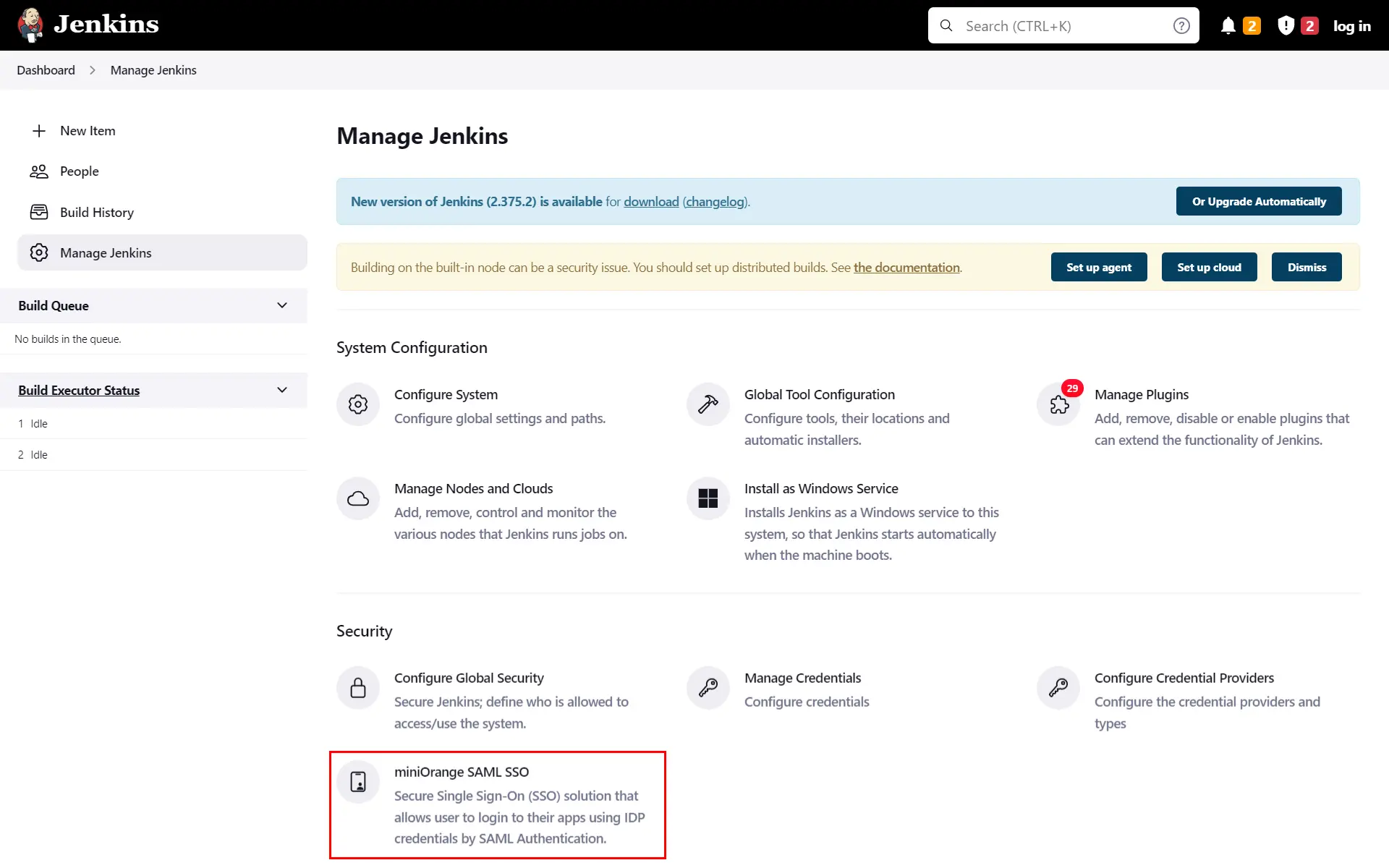
Step 2: Setup Jenkins as Service Provider
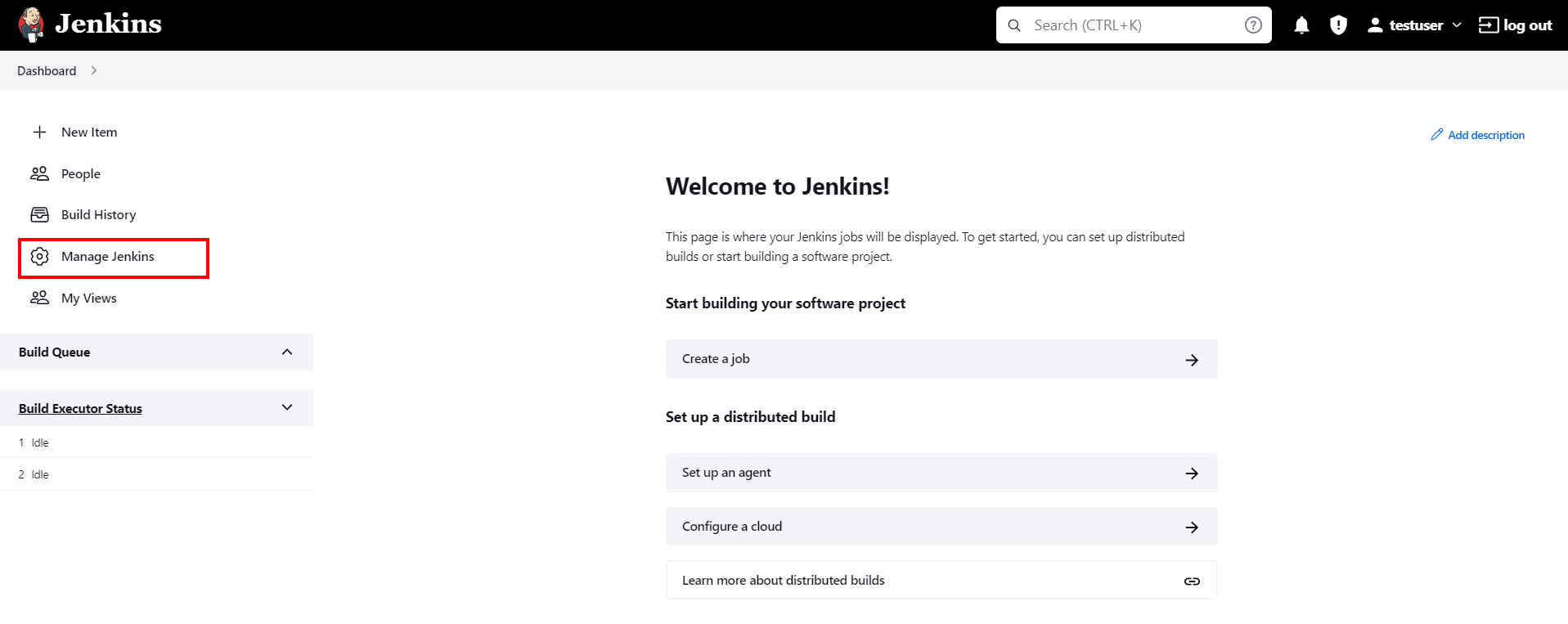
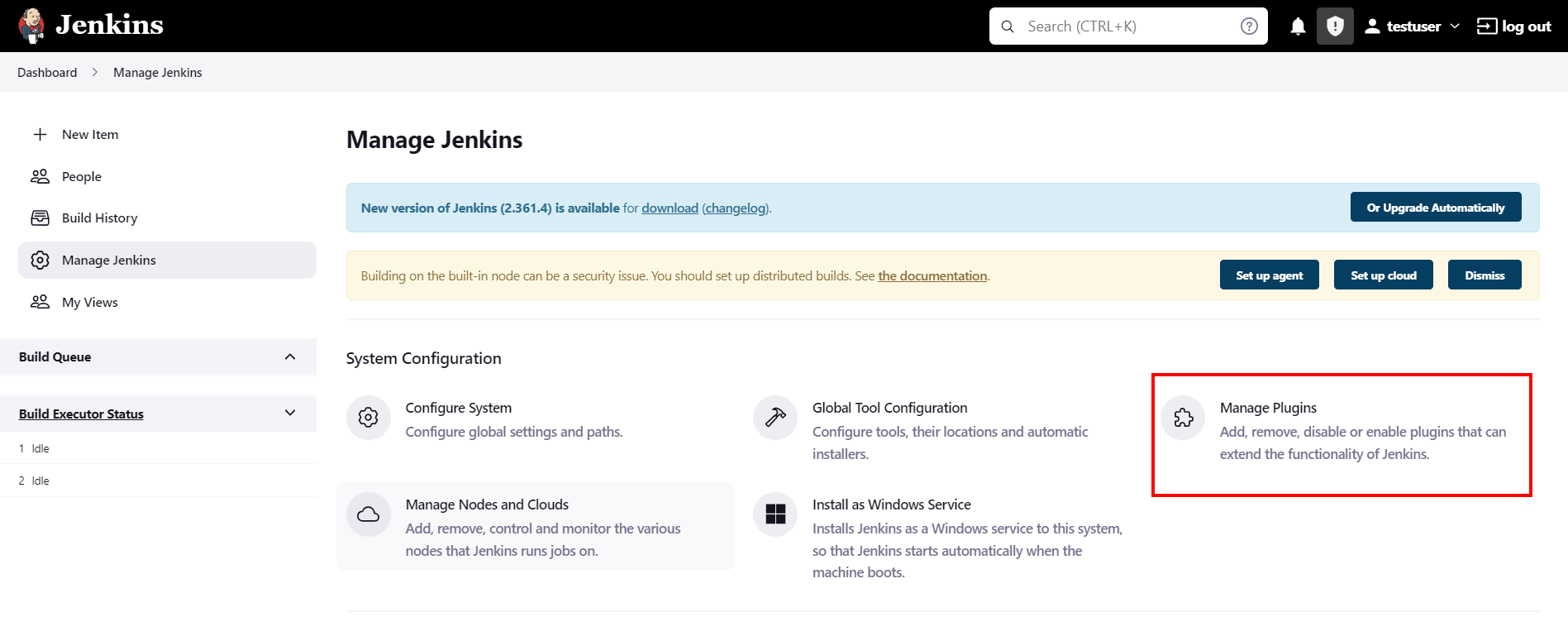
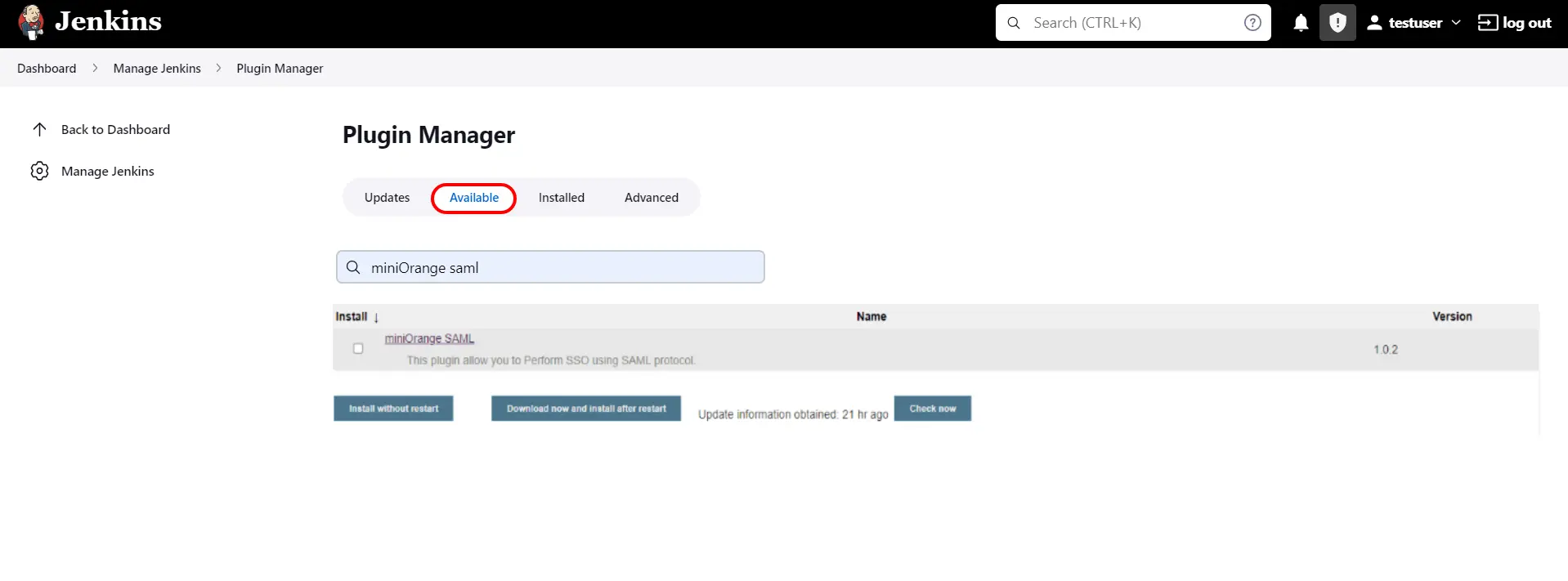
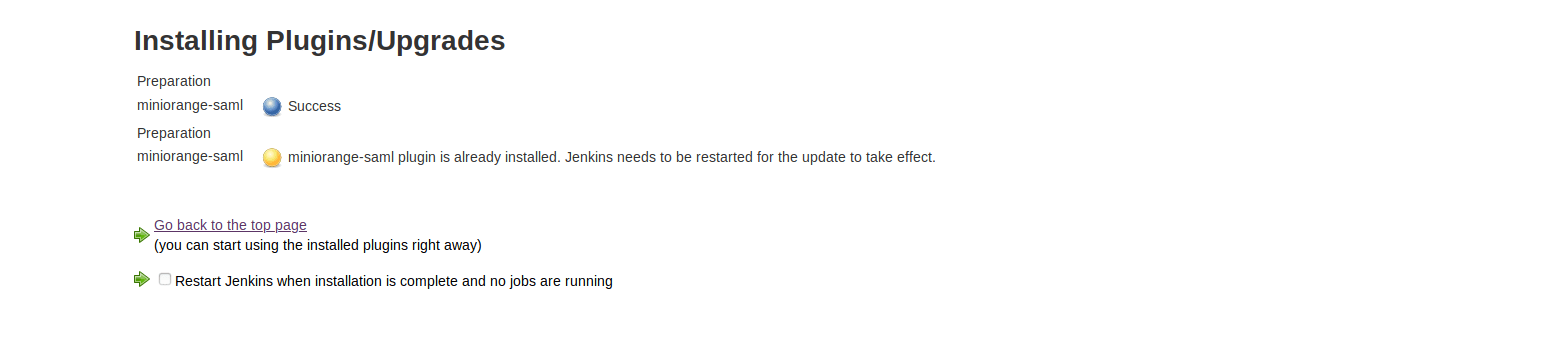
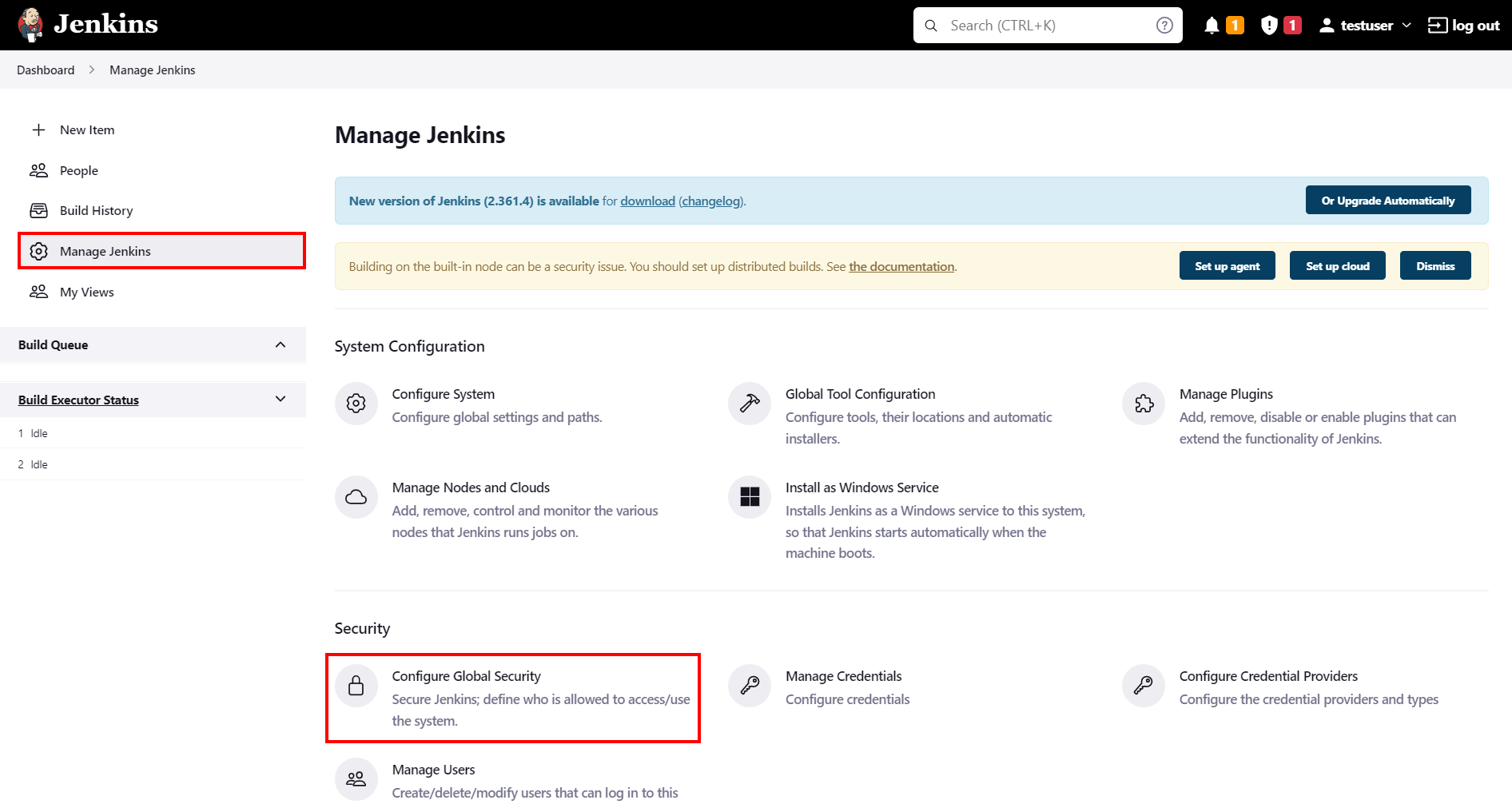
- Open Manage Jenkins and select Configure Global Security.
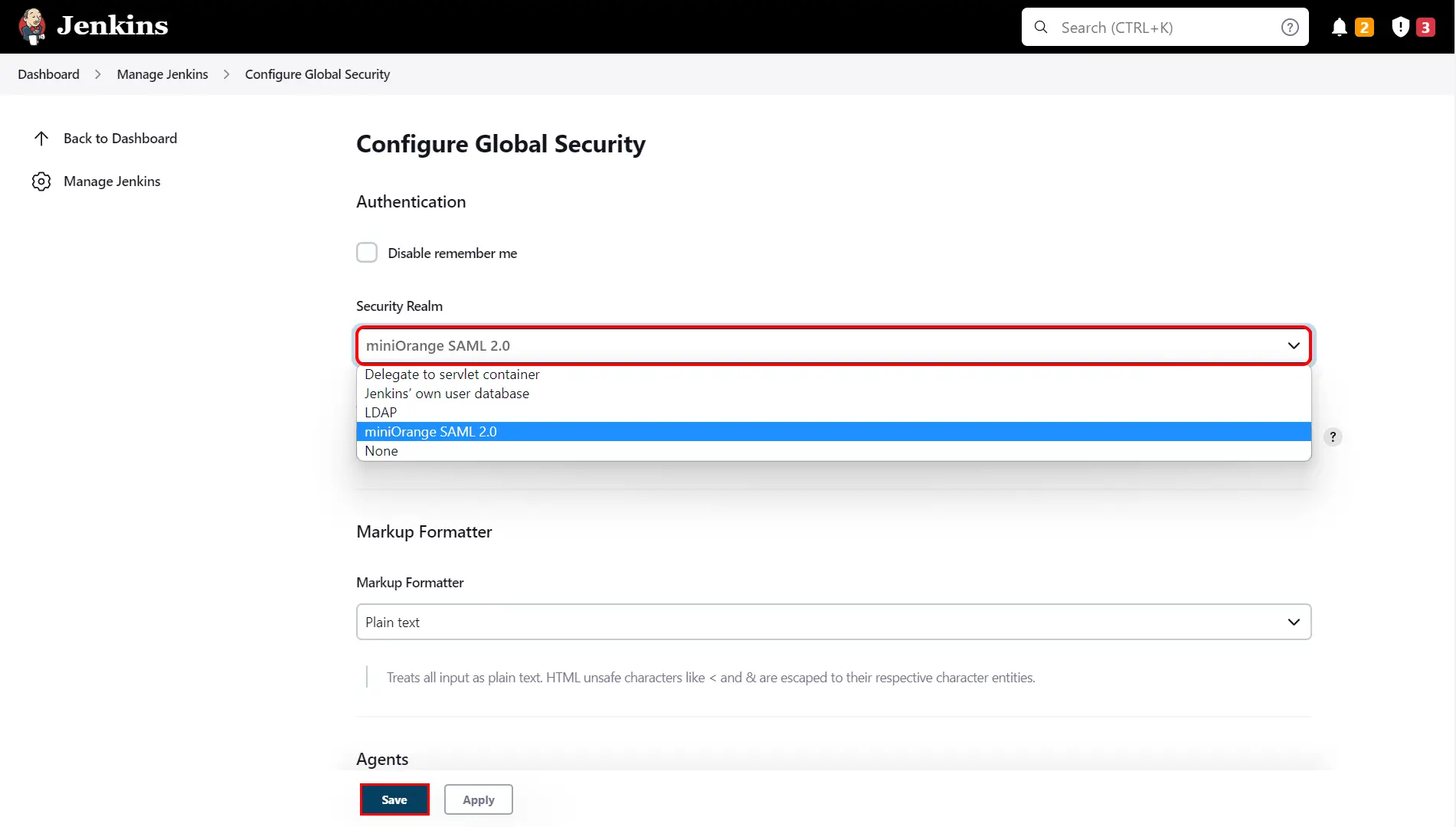
- Set the Security Realm as miniorange SAML 2.0 and click on save button.
- Make sure that Enable Security checkbox is checked.
- Choose miniorange SAML SSO from the manage Jenkins tab.
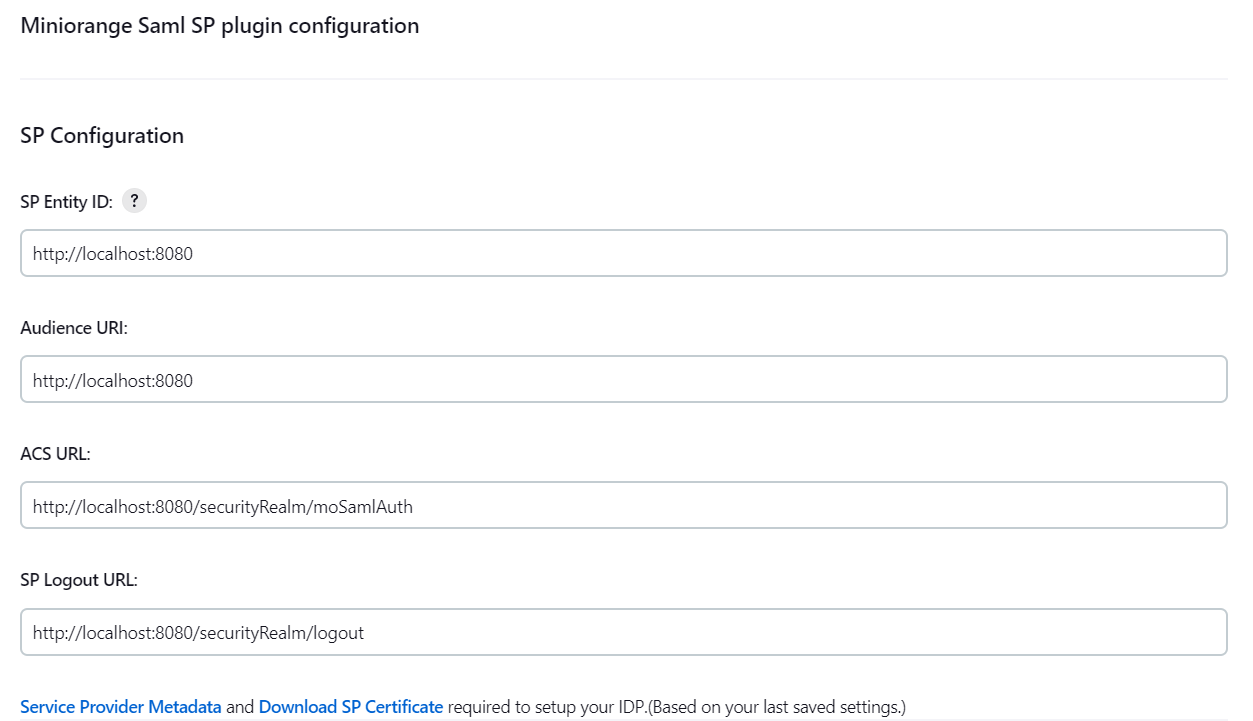
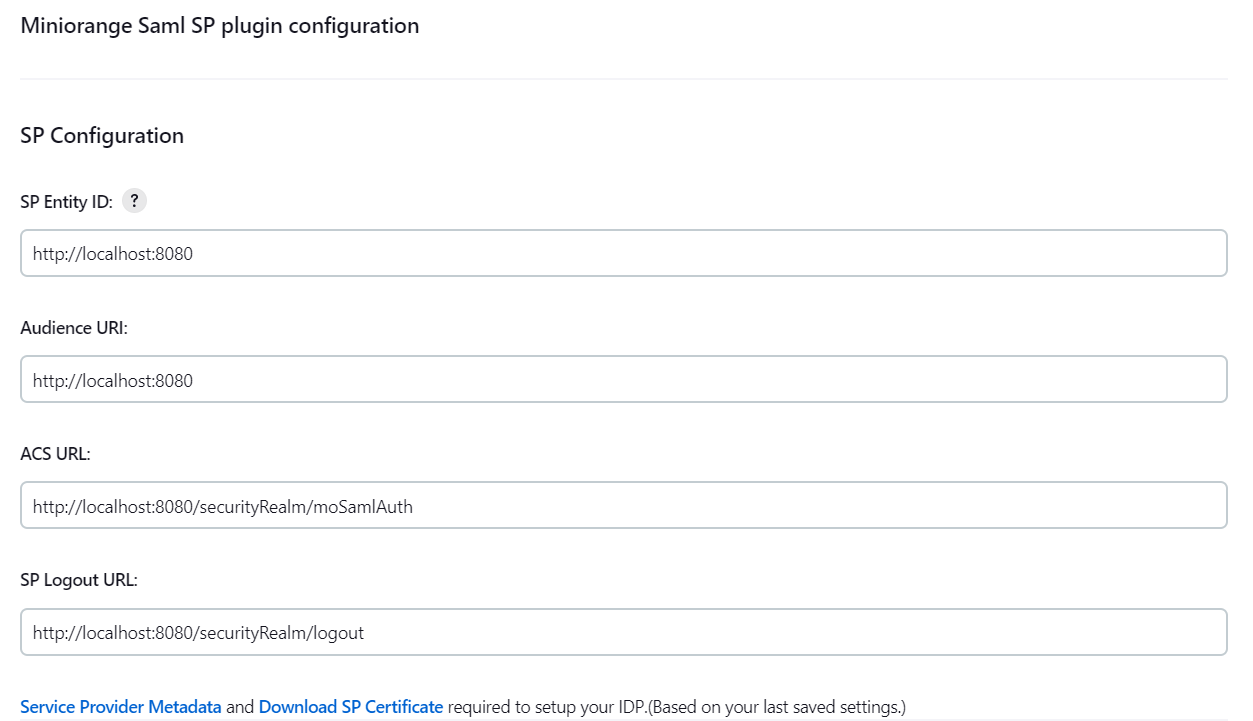
SP Configurations
You can configure SP settings in IDP in 2 ways:
A. By uploading Metadata XML file
To Configure IDP enter the following details and pressapply and save the settings.
User Profile Configuration
Advanced Configurations
You can configure SP settings in IDP in 2 ways:
A. By uploading Metadata XML file
- Click on Service Provider Metadata in SP Configuration section.
- Metadata xml file will be downloaded.
- Use this file to setup IDP.
- To Configure SP Settings at IDP copy below URL and paste in respective fields at IDP end.
- SP Entity ID: https://your-jenkins-domain
- Audience URI: https://your-jenkins-domain
- ACS URL: https://your-jenkins-domain/securityRealm/moSamlAuth
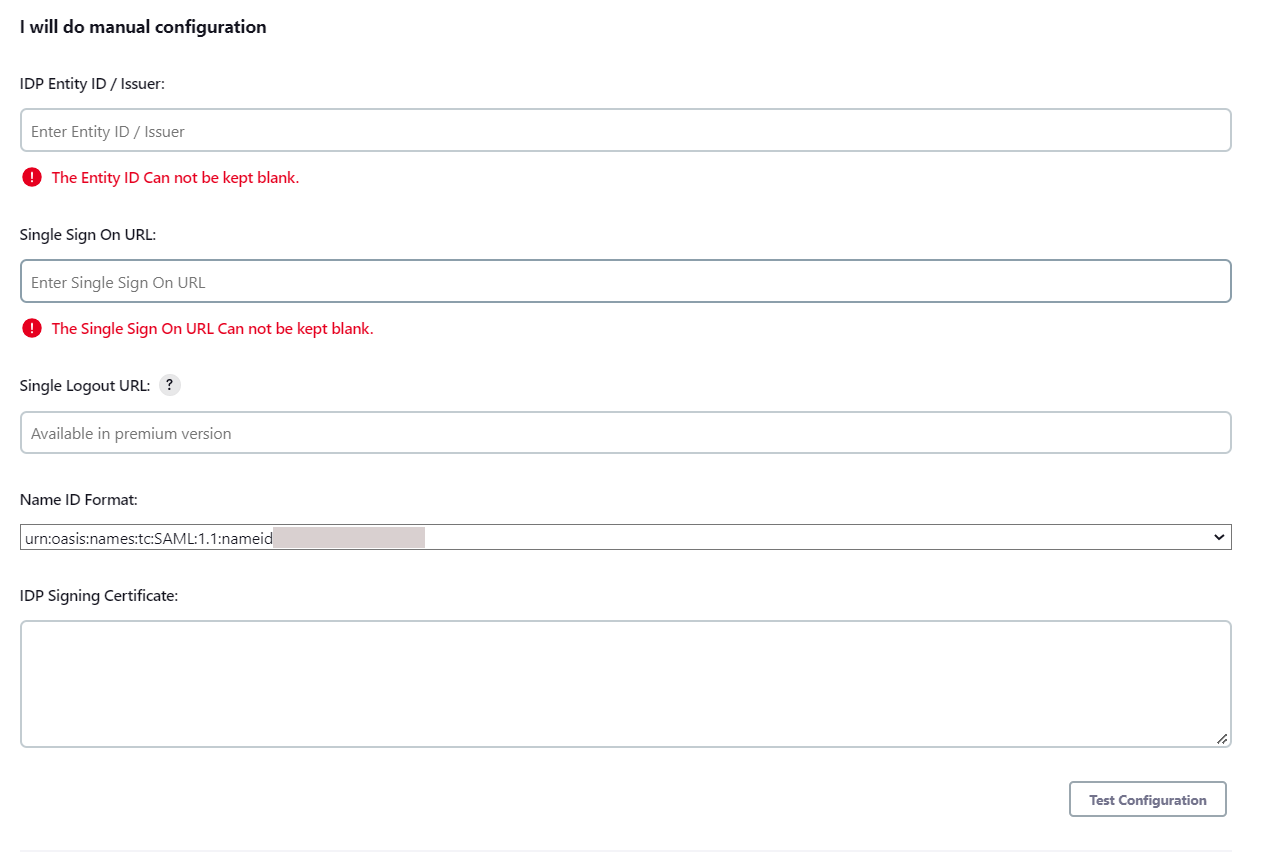
To Configure IDP enter the following details and press
- IDP Entity ID
- Single Sign On URL
- Name ID Format
- X.509 Certificate
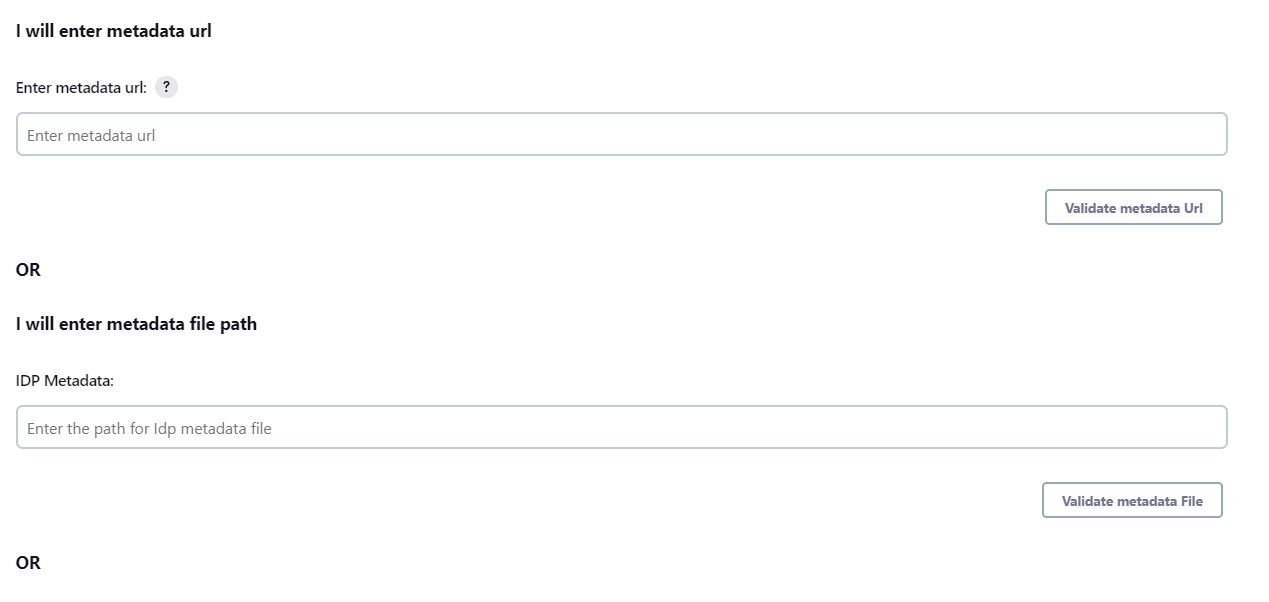
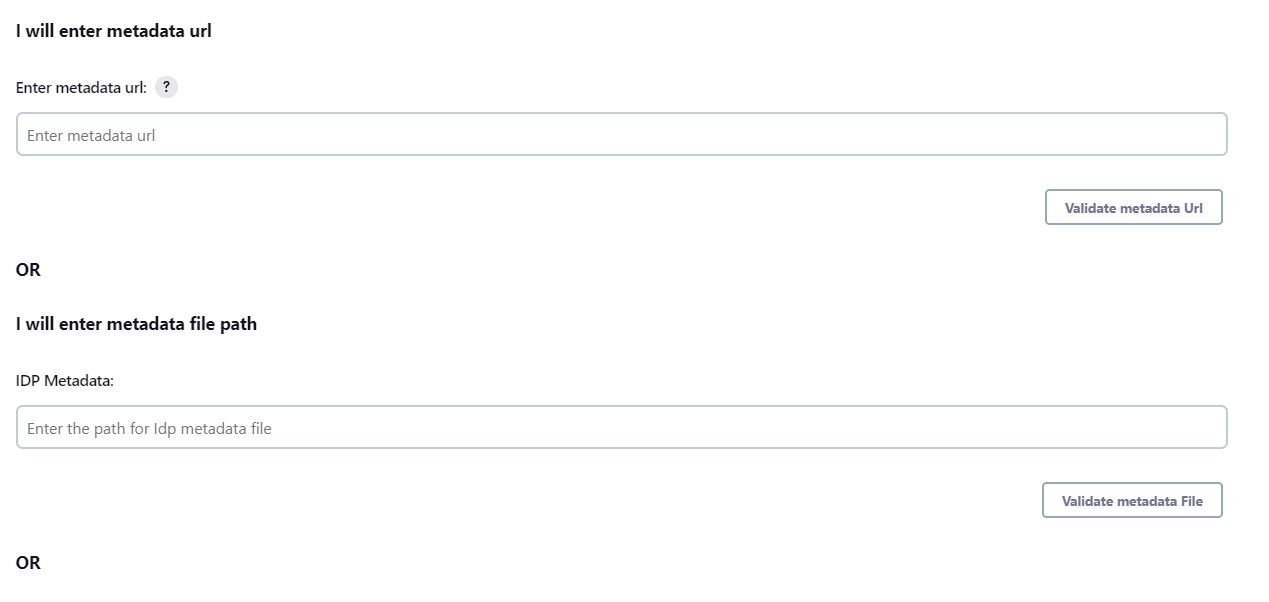
- You can either enter the metadata URL or the metadata file path.
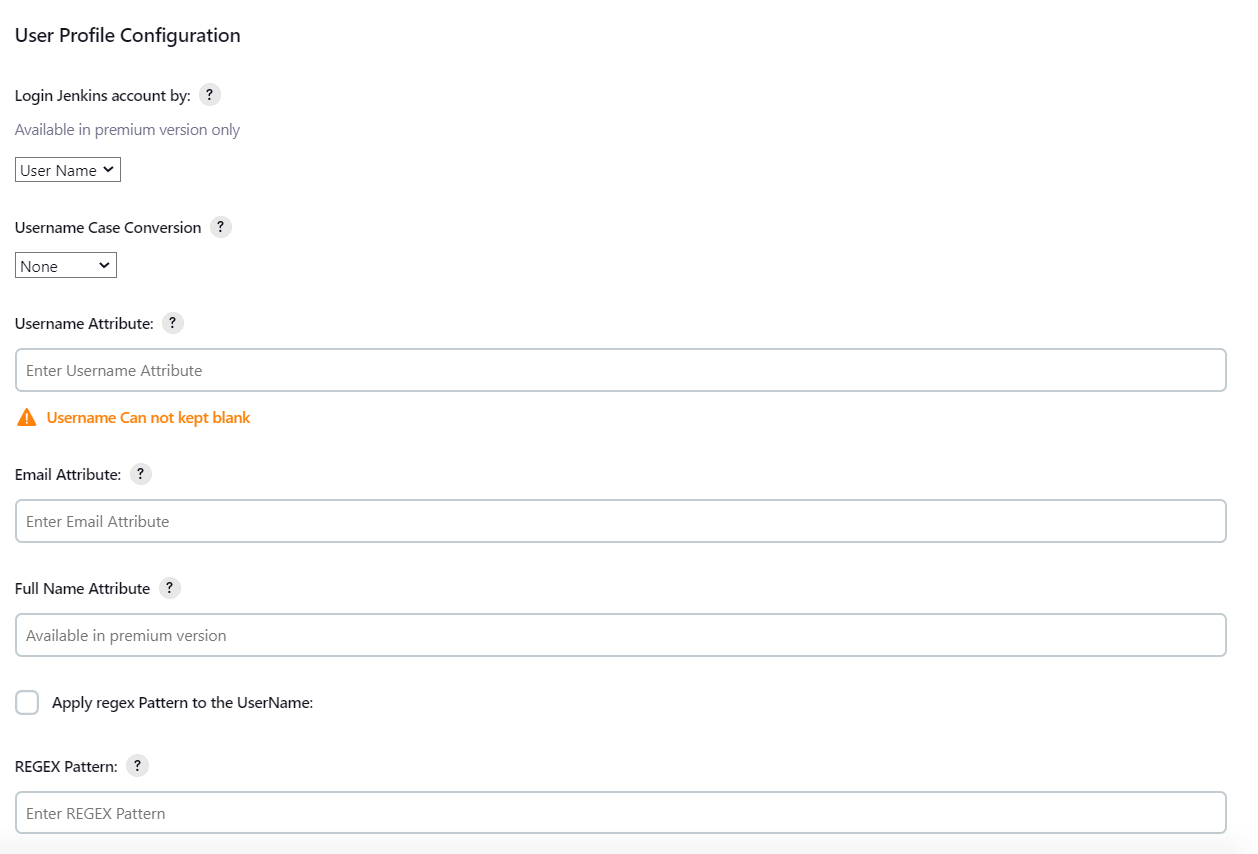
User Profile Configuration
- Select Username Case Conversion.
- Enter the attribute name from IDP which corresponds to Username in Username Attribute textbox.
- Enter the attribute name from IDP which corresponds to Email in Email Attribute textbox.
- Select the checkbox Apply regex Pattern to the UserNameif the userID returned from SAML is not same as username of Jenkins.
- Enter the regular expression in REGEX Pattern textbox. It will be applied on user ID from SAML Response and will convert it into the username same as Jenkins. For example, you can use regular expression ^.*?(?=@) to extract demo from username demo@example.com
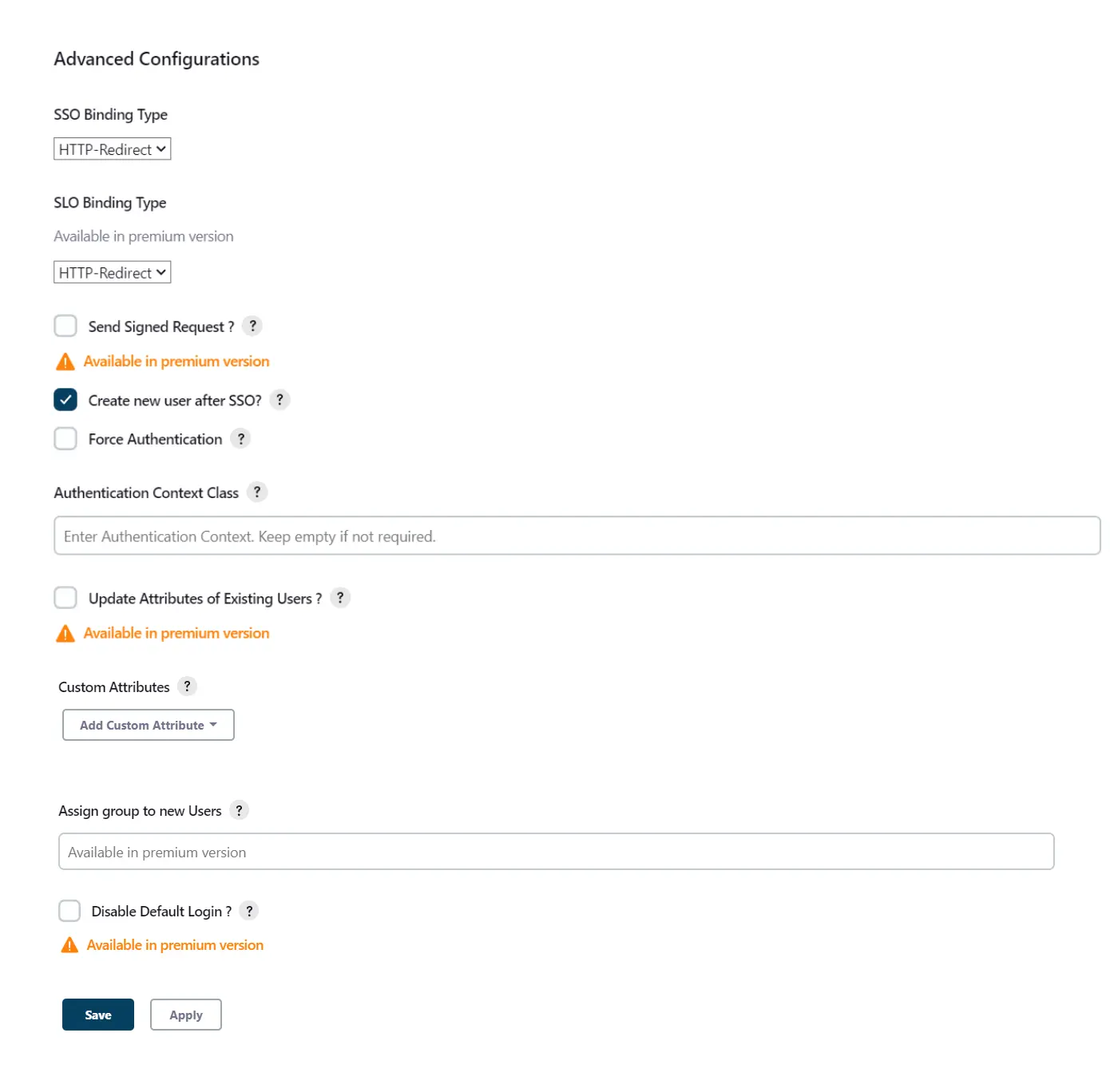
Advanced Configurations
- Select the SSO Binding Type.
- Select the Create new user after SSO? to allow user creation through SAML.
- Select Force Authentication.
- To Add custom Attributes select Add option.
- Set Attribute Name as the one set in IDP eg. lname
- Set display name in user proprties as one you want it appear in jenkins user's config.xml file and in user's configure tab.
SP Configurations
You can configure SP settings in IDP in 2 ways:
A. By uploading Metadata XML file
To Configure IDP enter the following details and pressapply and save the settings.
User Profile Configuration
Advanced Configurations
You can configure SP settings in IDP in 2 ways:
A. By uploading Metadata XML file
- Click on Service Provider Metadata in SP Configuration section.
- Metadata xml file will be downloaded.
- Use this file to setup IDP.
- To Configure SP Settings at IDP copy below URL and paste in respective fields at IDP end.
- SP Entity ID: https://your-jenkins-domain
- Audience URI: https://your-jenkins-domain
- ACS URL: https://your-jenkins-domain/securityRealm/moSamlAuth
To Configure IDP enter the following details and press
- IDP Entity ID
- Single Sign On URL
- Single Logout URL
- Name ID Format
- X.509 Certificate
- You can either enter the metadata URL or the metadata file path.
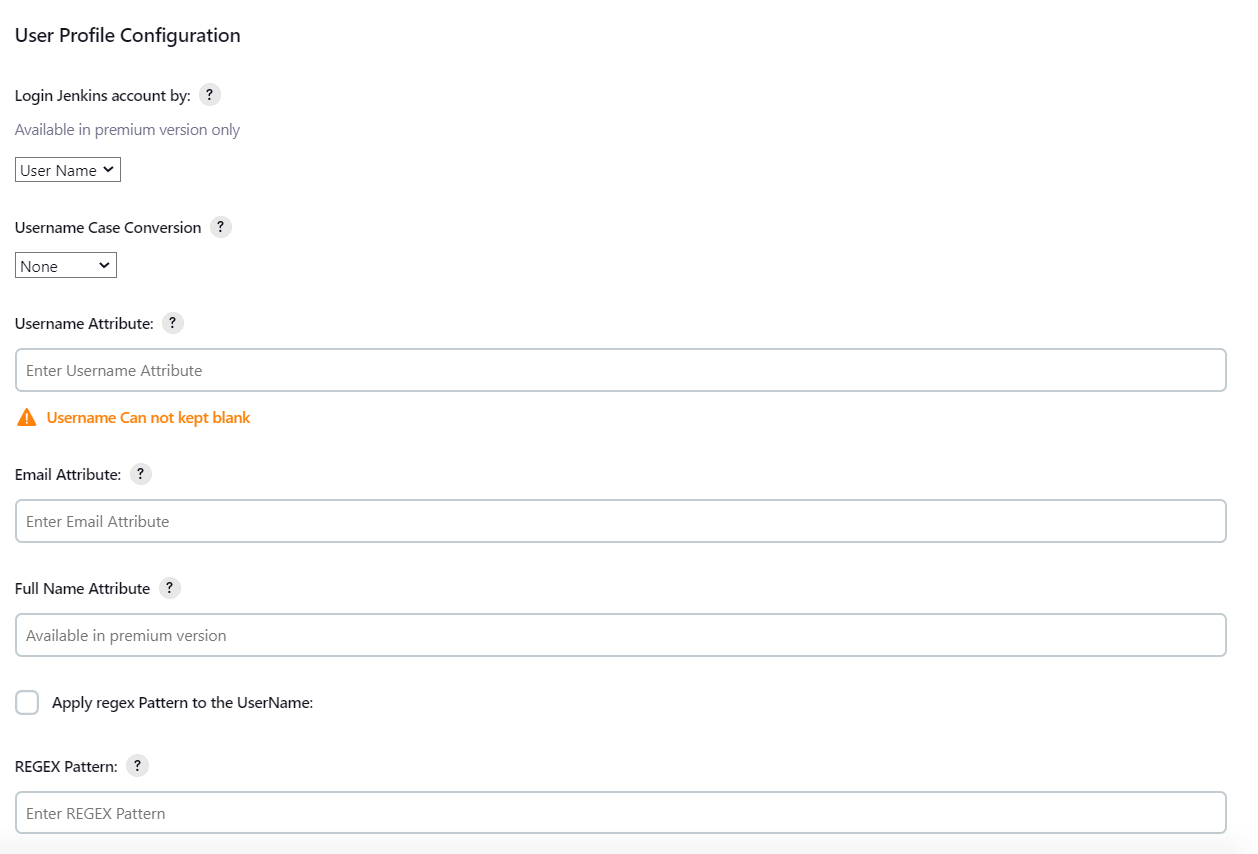
User Profile Configuration
- Select Username or Email for Login Jenkins account by:
- Select Username Case Conversion.
- Enter the attribute name from IDP which corresponds to Username in Username Attribute textbox.
- Enter the attribute name from IDP which corresponds to Email in Email Attribute textbox.
- Enter the attribute name from IDP which corresponds to full name in Full Name Attribute.
- Select the checkbox Apply regex Pattern to the UserNameif the userID returned from SAML is not same as username of Jenkins.
- Enter the regular expression in REGEX Pattern textbox. It will be applied on user ID from SAML Response and will convert it into the username same as Jenkins. For example, you can use regular expression ^.*?(?=@) to extract demo from username demo@example.com
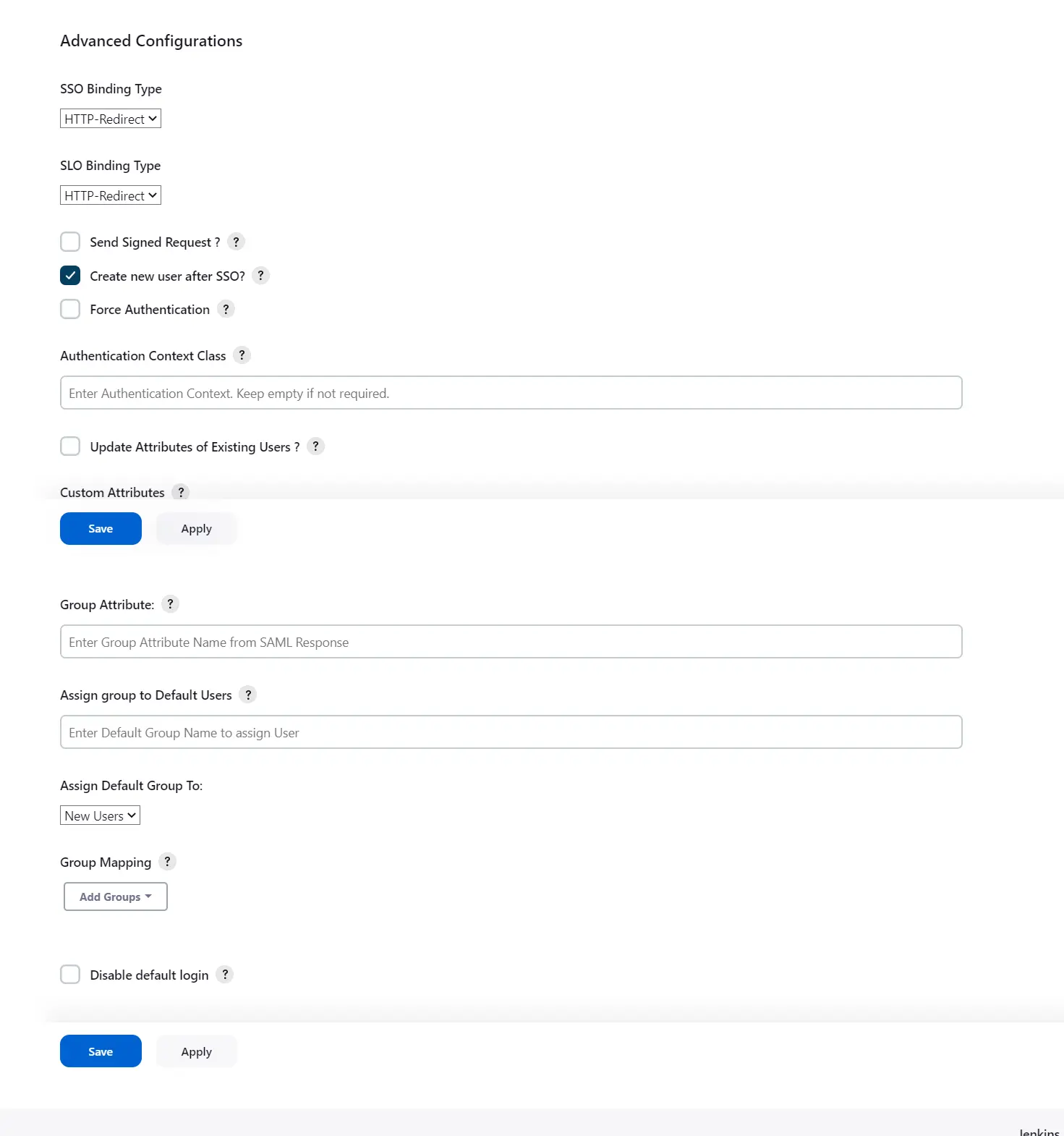
Advanced Configurations
- Select the SSO Binding Type.
- Select the SLO Binding Type.
- Select the Send Signed Request ? to send signed login and logout requests. Requests will be signed using public certificate from option Download SP Certificate in SP Configuration section.
- Select the Create new user after SSO? to allow user creation through SAML.
- Select Force Authentication.
- Select the Update Attributes of Existing Users ? to update attributes of existing user's each time they sign in Jenkins through SSO.
- To Add custom Attributes select Add option.
- Set Attribute Name as the one set in IDP eg. lname
- Set display name in user proprties as one you want it appear in jenkins user's config.xml file and in user's configure tab.
- To assign default group to users created through SSO add group name in Assign group to new Users option. Multiple groups can be added using ,(Comma) separater
- You can assign groups from IDP to users created through SSO by adding the name of the group attribute that contains the IDP groups in the SAML response in the Group Attribute field in the plugin configuration. You can find out the group attribute name by performing the test configuration from the test configuration button under the I will do manual configuration tab.
- If Disable Default login option is enabled, any unauthenticated user trying to access the default Jenkins login page will get redirected to the IDP login page for authentication. After successful authentication, they will be redirected back to the Jenkins base URL.
- Copy backdoor URL and save it for emergency.
Our Other Apps:
SAML SSO Apps
|
OAuth Apps
|
Crowd Apps
|
2FA Apps
|
REST API Apps
|
User Sync Apps
|
Bulk User Management
|
Secure Share
|
Bitbucket Git Authentication App | Kerberos/NTLM Apps | Word/PDF Exporter | WebAuthn | SonarQube SSO | Jenkins SSO
Bitbucket Git Authentication App | Kerberos/NTLM Apps | Word/PDF Exporter | WebAuthn | SonarQube SSO | Jenkins SSO
If you don't find what you are looking for, please contact us at support-atlassian@miniorange.atlassian.net or raise a support ticket here.
×
![ADFS_sso]()