Workforce identity has become far more complex than it used to be. Employees now access dozens of SaaS applications, often from different locations and devices, while organizations continue to adopt hybrid and remote work models. This shift has made manual access management inefficient and risky, leading to over-permissioned users and inconsistent access controls.
Without a structured approach, organizations struggle to maintain visibility over who has access to what. Role-Based Access Control (RBAC), when implemented within a Workforce IAM framework, helps standardize access, reduce risk, and bring much-needed control to modern identity environments.
Quick Summary: What is RBAC?
- RBAC is an access control model where permissions are assigned to roles, not individual users
- Users receive access based on their job function or responsibilities
- Roles act as a bridge between users and permissions
- It reduces manual access decisions and enforces consistency
- Supports least privilege by limiting access to only what is required
What is Workforce IAM?
Workforce Identity and Access Management (IAM) refers to the systems and processes used to manage digital identities of employees, contractors, and partners within an organization. It ensures that the right individuals can access the right resources at the right time, while maintaining security and compliance. Workforce IAM acts as a centralized layer that connects identity sources, applications, and access policies across the organization.
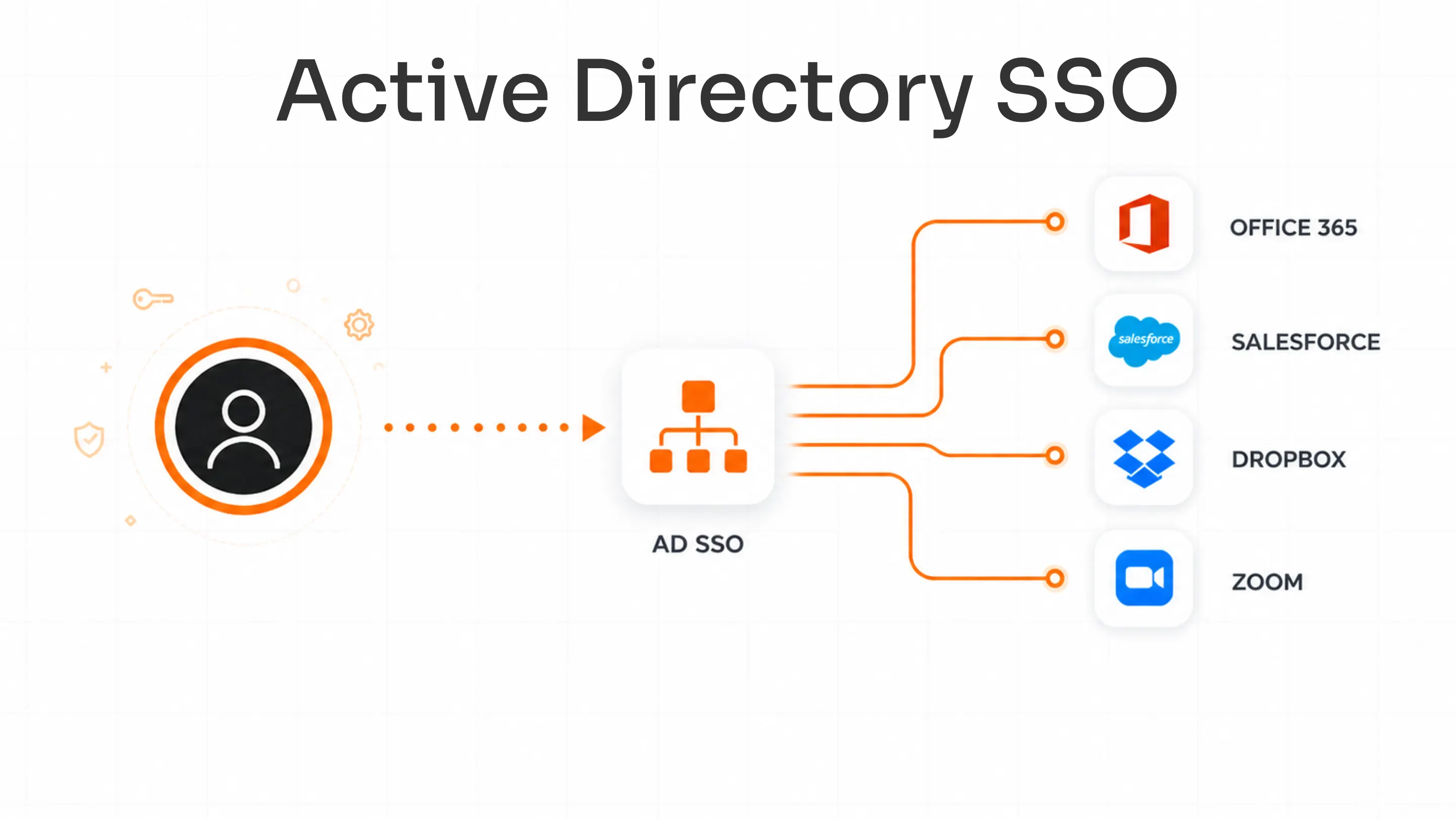
It typically includes authentication mechanisms such as Single Sign-On (SSO) and Multi-Factor Authentication (MFA), along with authorization models like RBAC. In addition, it automates provisioning and deprovisioning of access as users join, move within, or leave the organization, reducing manual effort and minimizing the risk of unauthorized access.
What is Role-Based Access Control (RBAC)?
Role-Based Access Control (RBAC) is a structured authorization model that simplifies how access is granted and managed across systems. Instead of assigning permissions directly to each user, RBAC groups permissions into roles that reflect job responsibilities. Users are then assigned one or more roles, and each role determines what resources they can access.
This approach creates a clear separation between users and permissions, making access management more scalable and consistent. For example, a finance analyst role may include access to accounting software and reporting tools, while an IT administrator role may include system-level permissions.
RBAC also supports governance by enabling organizations to enforce least privilege, standardize access policies, and audit permissions more effectively across the workforce.
Why RBAC is Critical in Workforce IAM
Enforces Least Privilege
RBAC ensures that users only receive access necessary for their job roles, reducing the risk of over-permissioning. By aligning access with defined responsibilities, organizations can minimize unnecessary exposure to sensitive systems and data, which is a key requirement for maintaining a secure workforce environment.
Simplifies Access Management at Scale
Managing access individually becomes unmanageable as organizations grow. RBAC streamlines this by assigning permissions to roles instead of users, allowing administrators to manage access for large groups efficiently. This way, access management reduces operational complexity and improves consistency across systems.
Reduces Insider and Accidental Risks
Excessive or incorrect access is a common cause of security incidents. RBAC limits this risk by ensuring users only have relevant permissions. It also reduces the chances of accidental misuse of systems, especially in environments with multiple applications and sensitive data.
Supports Compliance and Audit Readiness
Regulatory frameworks require organizations to demonstrate controlled and auditable access. RBAC provides a structured way to enforce policies, maintain access records, and support audits. It simplifies compliance by making it easier to track who has access to what and why.
Types of RBAC Roles in Workforce IAM
Functional Roles
Functional roles are based on job responsibilities within the organization. The group permissions required to perform specific tasks, such as HR Manager, Developer, or Finance Analyst. These roles are the most commonly used in RBAC and provide a clear mapping between business functions and system access.
Organizational Roles
Organizational roles are defined based on hierarchy, department, or position within the company. Examples include Manager, Director, or Intern. These roles help align access with organizational structure and are often combined with functional roles to provide more precise access control.
System Roles
System roles are application-specific and define access within individual systems or platforms. Common examples include Admin, Editor, and Viewer. These roles are typically predefined within applications and are mapped to broader workforce roles within IAM systems to maintain consistency across tools.
Temporary / Time-Bound Roles
Temporary roles provide access for a limited duration or for a specific task. They are commonly used for contractors, external collaborators, or short-term projects. This approach helps reduce standing access and improves security by ensuring that permissions are revoked automatically when no longer needed.
Composite Roles
Composite roles combine multiple roles into a single package to support users with complex responsibilities. For example, a team lead may require both functional and managerial access. While useful, composite roles must be carefully managed to avoid unnecessary access accumulation.
Types of RBAC Models
Core RBAC
Core RBAC is the foundational model where users are assigned to roles, and roles are linked to permissions. It establishes a simple and structured relationship between identities and access. This model is easy to implement and works well for organizations with clearly defined job functions, forming the base for more advanced RBAC models.
Hierarchical RBAC
Hierarchical RBAC introduces role inheritance, where higher-level roles automatically inherit permissions from lower-level roles. For example, a manager role may include all permissions of an employee role along with additional privileges. This reduces duplication in role design and helps organizations scale access control efficiently across departments and hierarchies.
Constrained RBAC
Constrained RBAC adds restrictions to enforce security policies such as Separation of Duties (SoD). It ensures that conflicting roles are not assigned to the same user, such as preventing a user from both initiating and approving financial transactions. This model is particularly important for compliance and risk mitigation in regulated environments.
Symmetric RBAC
Symmetric RBAC focuses on governance and visibility by allowing organizations to analyze both user-to-role and role-to-permission relationships. It supports better auditing and review processes by enabling administrators to evaluate how access is assigned and whether it aligns with organizational policies, improving overall access control maturity.
RBAC vs ABAC vs Rules-Based Access
| Factor | RBAC | ABAC | Rules-Based Access |
|---|---|---|---|
| Definition | Access is assigned based on predefined roles | Access is determined dynamically using multiple attributes | Access is controlled using predefined conditions |
| Access Basis | Job roles and responsibilities | User, resource, and environmental attributes | Rules like time, location, IP, or device |
| How It Works | Users are assigned roles, and roles carry permissions | Policies evaluate attributes in real time to allow or deny access | Access is granted or denied when specific conditions are met |
| Flexibility | Moderate | High | Moderate |
| Complexity | Low | High | Low to Moderate |
| Best Use Case | Organizations with stable roles and structured access | Dynamic environments needing fine-grained, real-time control | Adding contextual restrictions to existing access models |
How RBAC Works in Workforce IAM Systems
1. Identity Source Integration
Workforce IAM connects with a central identity source such as HRMS or Active Directory. This system acts as the single source of truth for user data like job title, department, and employment status, ensuring all access decisions start with accurate identity information.
2. Role Definition & Mapping
Roles are created based on business functions and organizational structure. Users are automatically mapped to roles using attributes like department, designation, or location, eliminating manual access assignment and ensuring consistency across the workforce.
3. Permission Assignment
Each role is linked to a defined set of permissions, including access to applications, systems, and data. This standardization ensures that every user within a role gets the exact access required to perform their responsibilities, without unnecessary privileges.
4. Automated Provisioning
Once roles are assigned, access is automatically provisioned to relevant SaaS and internal applications. This reduces onboarding time, eliminates manual errors, and ensures users can start working with the right tools from day one.
5. Monitoring & Lifecycle Management
The system continuously monitors access and user activity for visibility and security. When a user’s role changes, access is updated automatically, and when they leave the organization, all access is revoked immediately, maintaining compliance and reducing risk.
RBAC in Employee Lifecycle Management
RBAC plays a central role in managing access throughout the employee lifecycle (Joiner-mover-leaver). By tying access directly to roles, organizations can automate how access is granted, updated, and revoked as users move through different stages.
Joiner (Onboarding)
When a new employee joins, RBAC ensures they are automatically assigned a role based on their job function. This triggers immediate provisioning of required applications and systems, reducing onboarding delays and ensuring users have the right access from day one without manual intervention.
Mover (Role Change)
As employees change roles, RBAC updates their access dynamically by assigning a new role and removing outdated permissions. This prevents privilege accumulation over time and ensures access always aligns with current responsibilities, which is critical for maintaining security and operational efficiency.
Leaver (Offboarding)
When an employee exits the organization, RBAC enables immediate revocation of all access by removing role assignments. This eliminates the risk of orphaned accounts and unauthorized access, which are common security gaps in manual access management processes.
Building a Complete Workforce IAM Security Stack
RBAC alone defines what users can access, but it becomes significantly more effective when combined with authentication and verification mechanisms within Workforce IAM.
- RBAC (Authorization): Determines what resources a user can access based on their role
- SSO (Authentication): Simplifies login by allowing users to access multiple applications with a single set of credentials
- MFA (Verification): Adds an additional security layer by requiring multiple forms of authentication
Together, these components create a unified identity framework where access is not only controlled but also securely verified. This integration improves user experience while strengthening security across all workforce applications.
Common RBAC Challenges in Workforce IAM
Role Explosion
As organizations try to accommodate every edge case, they often create too many roles, leading to role explosion. This makes RBAC difficult to manage and undermines its purpose. Instead of simplifying access, it creates confusion, increases administrative overhead, and makes audits more complex and time-consuming.
Poor Role Design
If roles are not designed around actual business functions, they can either grant excessive permissions or restrict necessary access. Poorly defined roles lead to inconsistencies across systems and require frequent manual adjustments, reducing the efficiency and reliability of the RBAC model.
SaaS Sprawl
Modern organizations rely on multiple SaaS applications, each with its own access model. Maintaining consistent role mapping across these systems becomes challenging, especially without centralized IAM. This can result in fragmented access control and increased risk due to inconsistent permission assignments.
Shadow IT Access
Employees often adopt unauthorized tools outside official IT control, creating gaps in RBAC enforcement. These unmanaged applications operate outside visibility, making it difficult to track access or enforce policies, ultimately increasing the organization’s exposure to security risks.
Lack of Audits and Reviews
Without regular access reviews, users may retain permissions that are no longer relevant to their roles. Over time, this leads to access creep and increased security risks. A lack of auditing also makes it harder to demonstrate compliance and identify potential access-related vulnerabilities.
Best Practices for RBAC Implementation in Workforce IAM
To get the most value from RBAC, organizations need a structured and strategic implementation approach.
- Define Roles Based on Business Functions Align roles with actual job responsibilities instead of individuals to ensure scalability and consistency
- Follow the Least Privilege Principle Grant only the access required for a role, reducing unnecessary exposure to sensitive systems
- Integrate with HRMS as Source of Truth Use HR systems to drive role assignments and lifecycle changes automatically
- Automate Provisioning (SCIM Where Possible) Enable automated access provisioning and deprovisioning to reduce manual effort and errors
- Conduct Regular Access Reviews Periodically review roles and permissions to eliminate outdated access and maintain compliance
How to Implement RBAC in Workforce IAM
Identify Workforce Roles
Begin by analyzing how work actually gets done across teams. Define roles around real job functions, responsibilities, and access needs rather than titles alone. This ensures roles remain stable even as individuals change, creating a scalable structure that reduces rework and keeps access aligned with business operations.
Map Applications and Permissions
Create a complete inventory of applications, systems, and data resources. Then map the exact permissions each role requires. This step is critical for eliminating guesswork and over-provisioning, ensuring that every role has just enough access to function without introducing unnecessary risk.
Integrate an IAM Solution
Adopt a Workforce IAM platform that centralizes identities and supports role-based access enforcement. Integration with HRMS and directory services ensures that role assignments are consistent, automated, and driven by a reliable source of truth across all environments.
Enable SSO and MFA
Strengthen the access layer by combining RBAC with Single Sign-On for seamless user experience and Multi-Factor Authentication for added security. This ensures that access decisions are not only accurate but also securely verified at every login.
Automate Provisioning and Deprovisioning
Use automation to grant and revoke access as users join, change roles, or leave. Automated provisioning reduces onboarding delays, while immediate deprovisioning eliminates lingering access risks, making access control both efficient and secure.
How miniOrange Enables RBAC in Workforce IAM
Unified Access Management Platform
miniOrange brings RBAC, SSO, MFA, and provisioning together in a single platform, eliminating fragmented identity systems. This unified approach ensures consistent policy enforcement and simplifies how access is managed across the workforce.
Seamless Integration with Existing Systems
It integrates smoothly with Active Directory, HRMS, and a wide range of SaaS applications. This allows organizations to implement RBAC without disrupting existing workflows while maintaining centralized identity control.
Automated Identity Lifecycle Management
miniOrange automates joiner, mover, and leaver processes, ensuring access is always aligned with user roles. This reduces manual effort, minimizes errors, and keeps access up to date throughout the employee lifecycle.
Scalable and Fast Deployment
The platform is designed for quick implementation and easy scalability. Organizations can roll out RBAC across teams and applications without the delays and complexity associated with traditional IAM systems.
Centralized Visibility and Control
A unified dashboard provides complete visibility into users, roles, and permissions. This makes it easier to monitor access, enforce policies, and conduct audits with confidence.
Making RBAC Work for the Modern Workforce
Role-Based Access Control remains one of the most effective ways to bring structure to access management, but its real impact depends on how well it is implemented within a Workforce IAM framework. When roles are thoughtfully designed and backed by automation, RBAC shifts access management from a reactive task to a controlled, scalable process.
As organizations continue to expand across applications, environments, and user types, combining RBAC with lifecycle automation and adaptive controls becomes essential. This approach not only reduces risk and operational overhead but also ensures that access remains aligned with real business needs. The result is a system that is easier to manage, more secure by design, and better equipped to support modern workforce demands.
FAQs
What is RBAC in workforce IAM?
RBAC in workforce IAM is an access control approach where permissions are assigned based on user roles, ensuring consistent and secure access across systems.
How is RBAC used in employee access management?
RBAC automates access provisioning by assigning permissions based on roles, reducing manual effort and ensuring users have appropriate access throughout their lifecycle.
What is the difference between RBAC and ABAC in IAM?
RBAC assigns access based on roles, while ABAC uses attributes such as location, device, and time to make dynamic access decisions.
What are the types of RBAC?
RBAC includes core RBAC, hierarchical RBAC, constrained RBAC, and symmetric RBAC. These models define how roles, permissions, and constraints are structured within an identity and access management system.
How do you implement RBAC in workforce IAM?
Implementing RBAC involves defining roles, mapping permissions, integrating an IAM solution, automating provisioning, and continuously monitoring access.
Leave a Comment