Atlassian Cloud SSO for PingOne using SAML
Jira SAML Single-Sign On(SSO) for Atlassian Cloud allows you to securely login using PingOne credentials. Single Sign-on (SSO) into your Atlassian Access or Atlassian Jira Cloud Account with any of your existing Identity Provider credentials for enhanced security and features using our module.
Pre-requisites
- Atlassian Guard (Atlassian Access) Subscription:
Atlassian Guard is an additional subscription applied across the Atlassian Cloud products like Jira Software, Jira Service Management, Jira Work Management, Confluence, and Bitbucket. It is needed for Single Sign-On (SSO) or any Cloud Service that comes under Atlassian Guard. - Domain Verification:
The first step of Atlassian Guard starts with the Domain Verification process to enforce SSO on the managed user accounts. This process verifies that you own a valid domain for managing the user accounts and use the same domain name for the email addresses.
In this document, we will demonstrate the setup in two parts.
Part 1: Configure SAML SSO between Atlassian cloud as SP and miniOrange as IDP
Part 2: Configure SAML SSO between miniOrange as SP and PingOne as IDP
Part 1 + Part 2 : Testing SSO between Atlassian cloud as SP and PingOne as IDP using miniOrange Identity Broker.
Download and Installation
- Log into your Jira instance as an admin.
- Navigate to Apps → Explore more apps from the header menu.
- Next, search for the miniOrange OAuth/OpenID SSO app.
- Click on Try it free to begin a new trial of the app.
- On the menu bar click on Apps and locate the OAuth/OpenID SSO app and click .
Part 1: Setup miniOrange with Atlassian Access
Step 1. Setup miniOrange as an Identity Provider
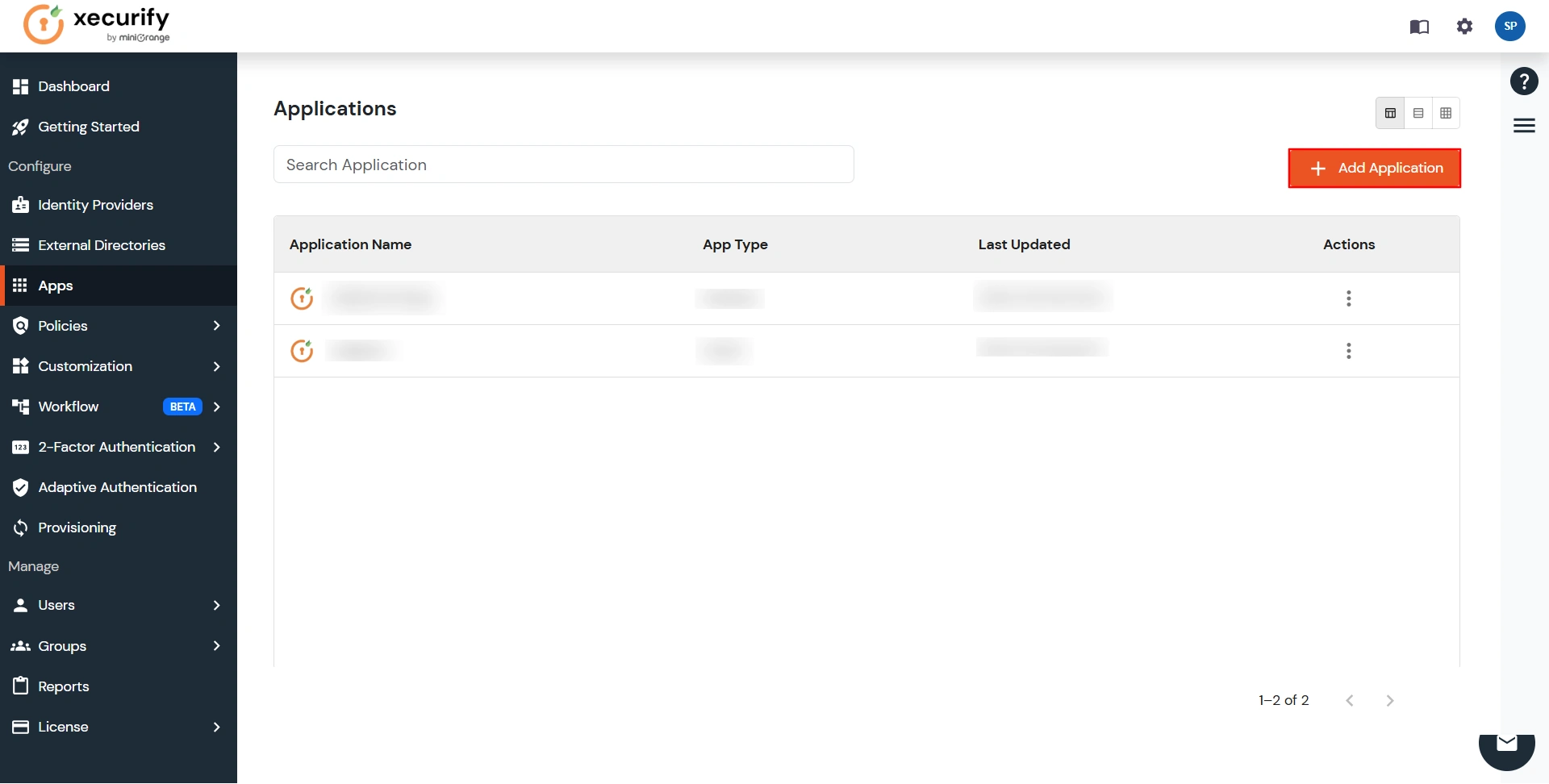
- Login into miniOrange Admin Console.
- Go to Apps and click on the Add Application button.
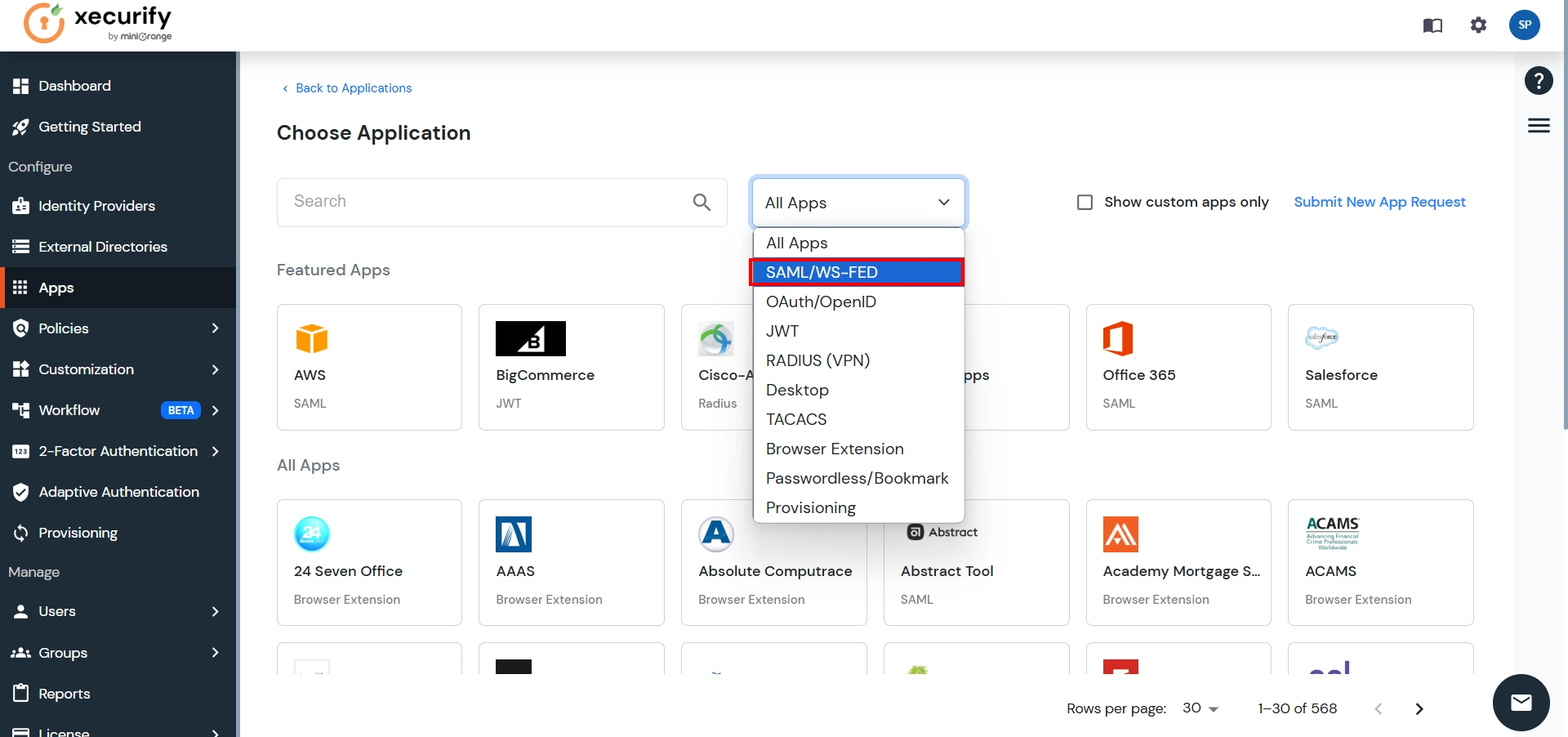
- In Choose Application Type click on All Apps dropdown and select SAML/WS-FED application type.
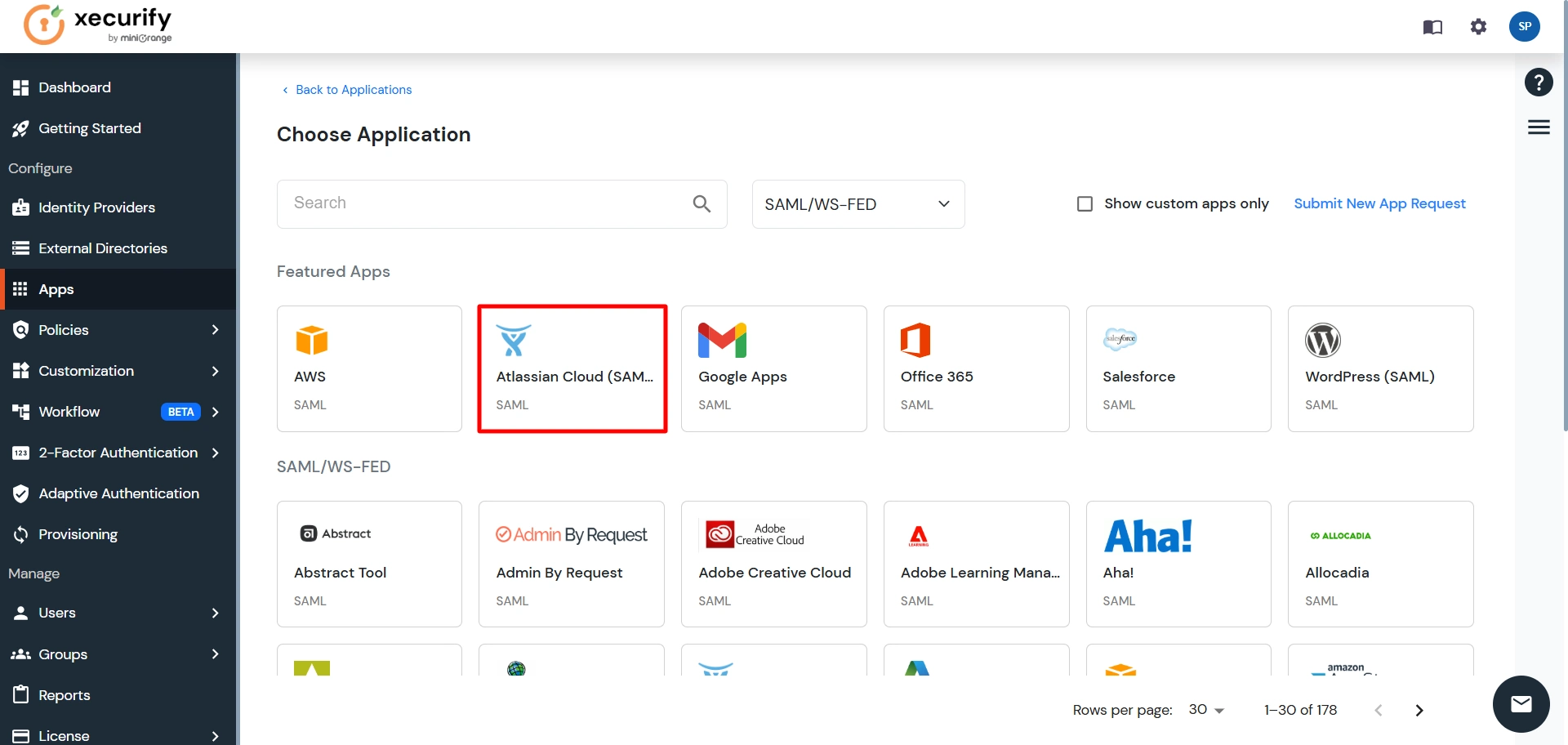
- Search for Atlassian Cloud (SAML) in the list.
- Enter the following values in the respective fields, you will receive these values after creating an app in Atlassian access. Refer this step.
- Also make sure that Sign Response & Sign Assertion both options are turned ON. Then click on the Save button.
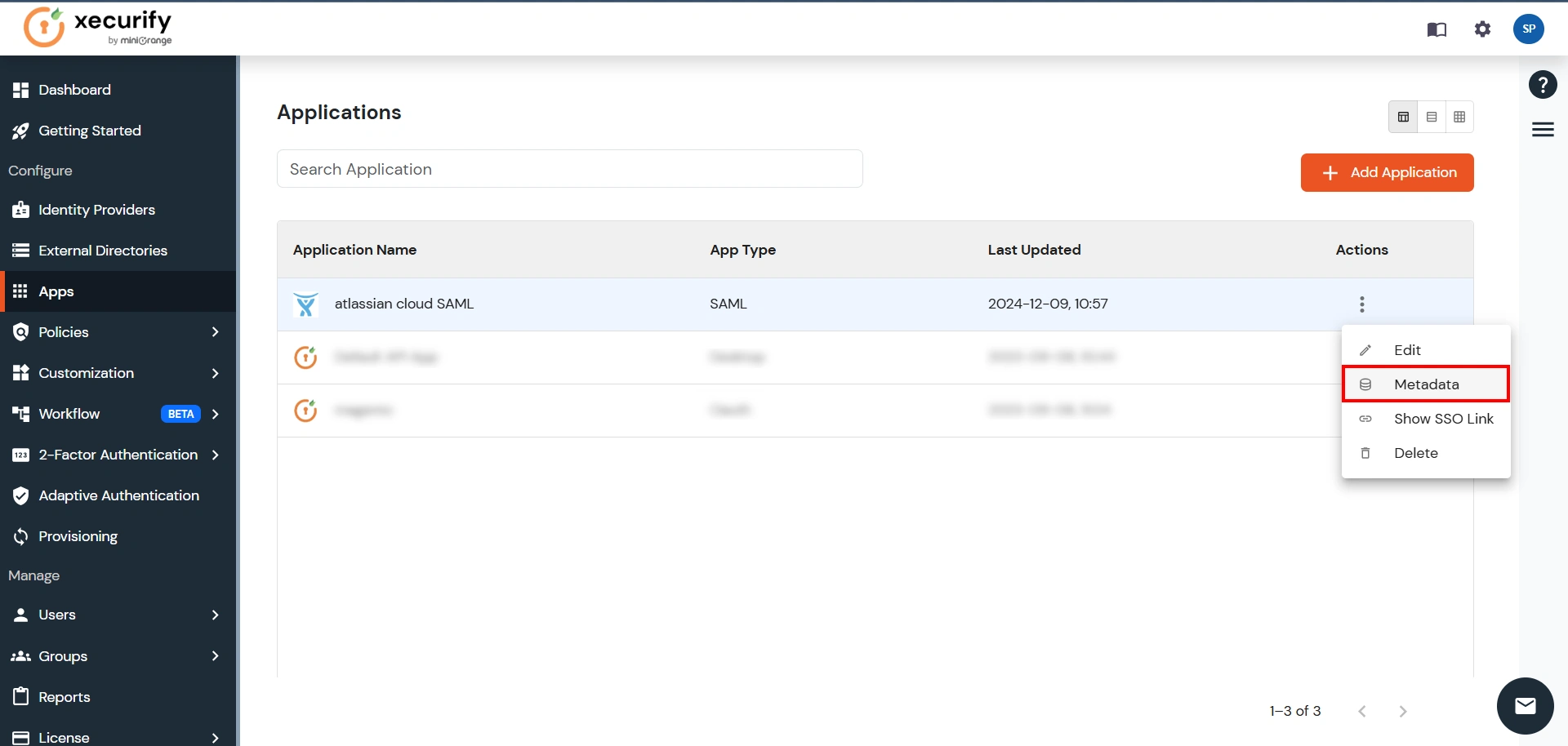
- Once the App is successfully Created, Select that App and then click on Metadata option to get app’s Metadata.
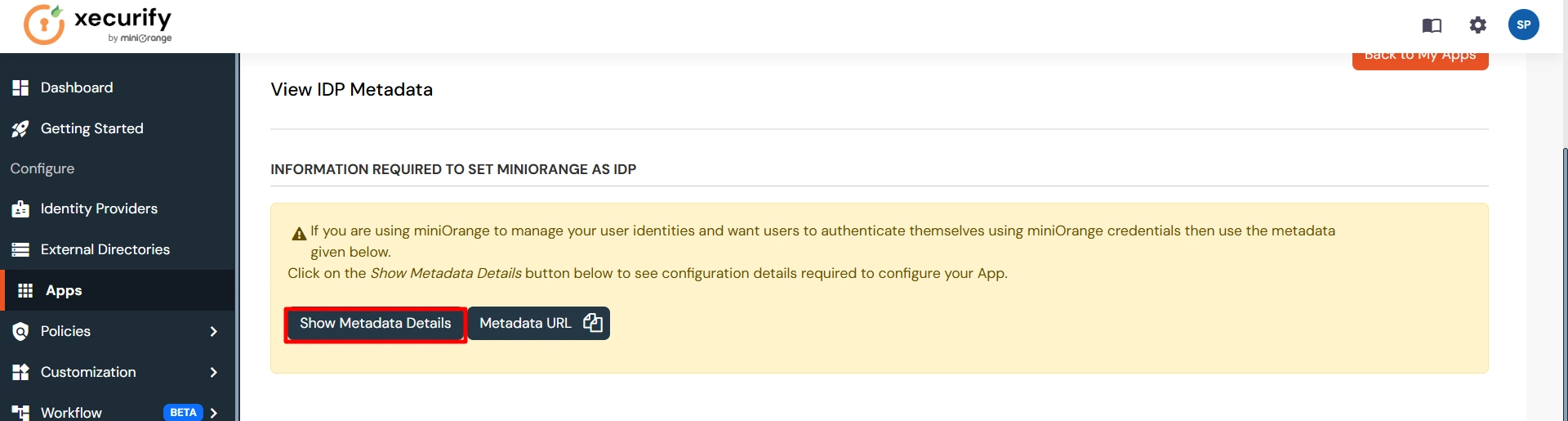
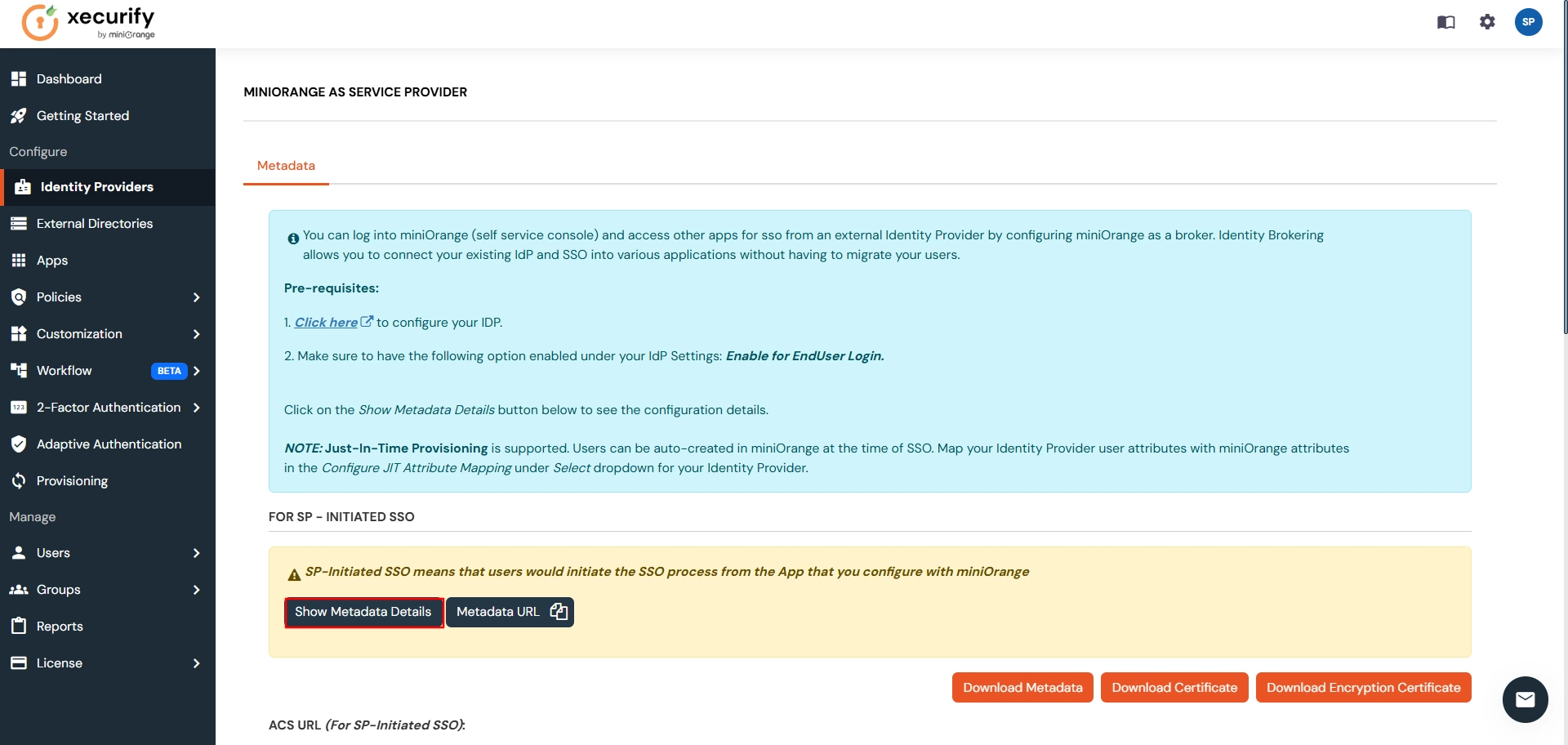
- Since we are using miniOrange as a Brokering Service in this solution, Go to Information required to authenticate via external idp section as highlighted, and Click on Show Metadata Details.
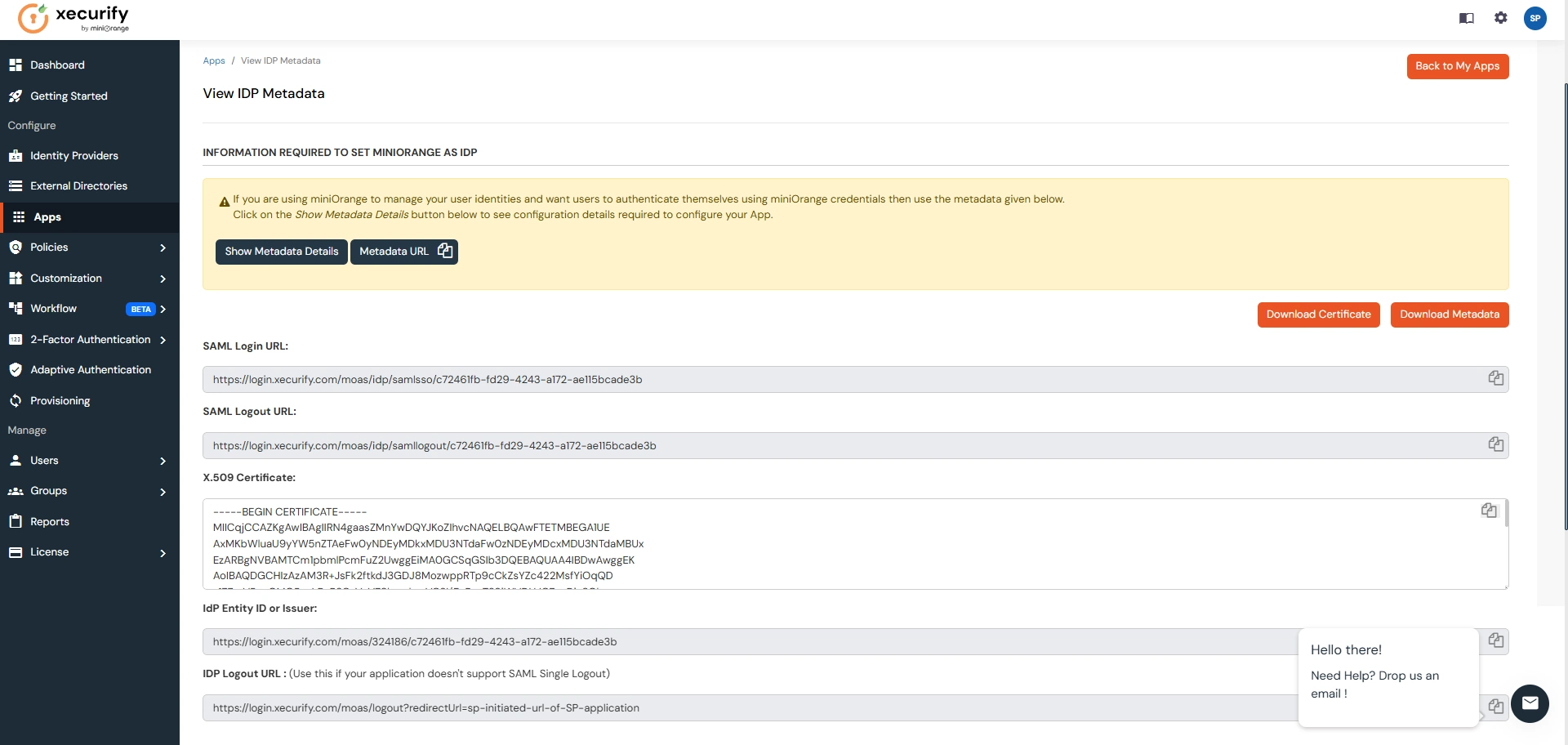
- After clicking on the Show Metadata Details button you can see the metadata details.
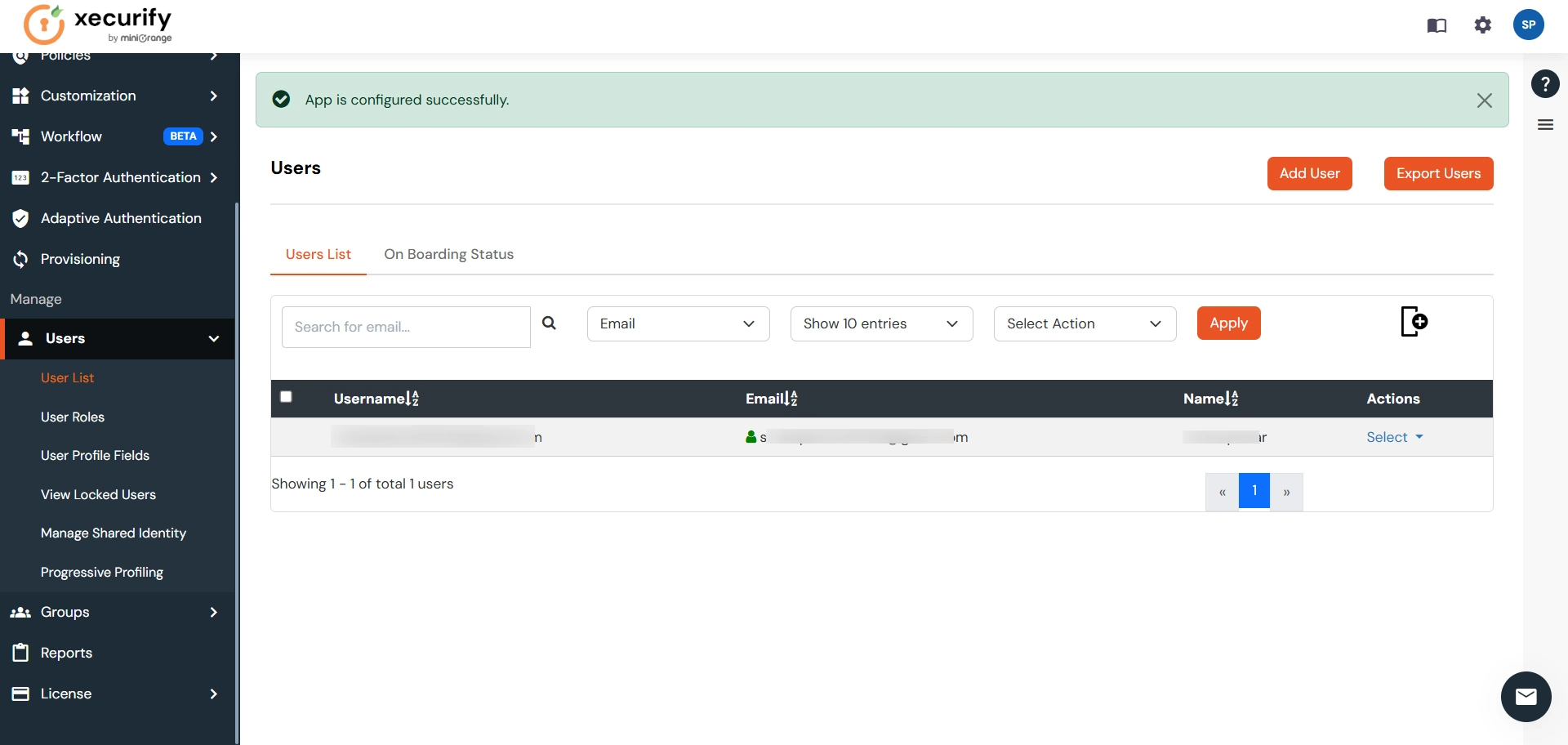
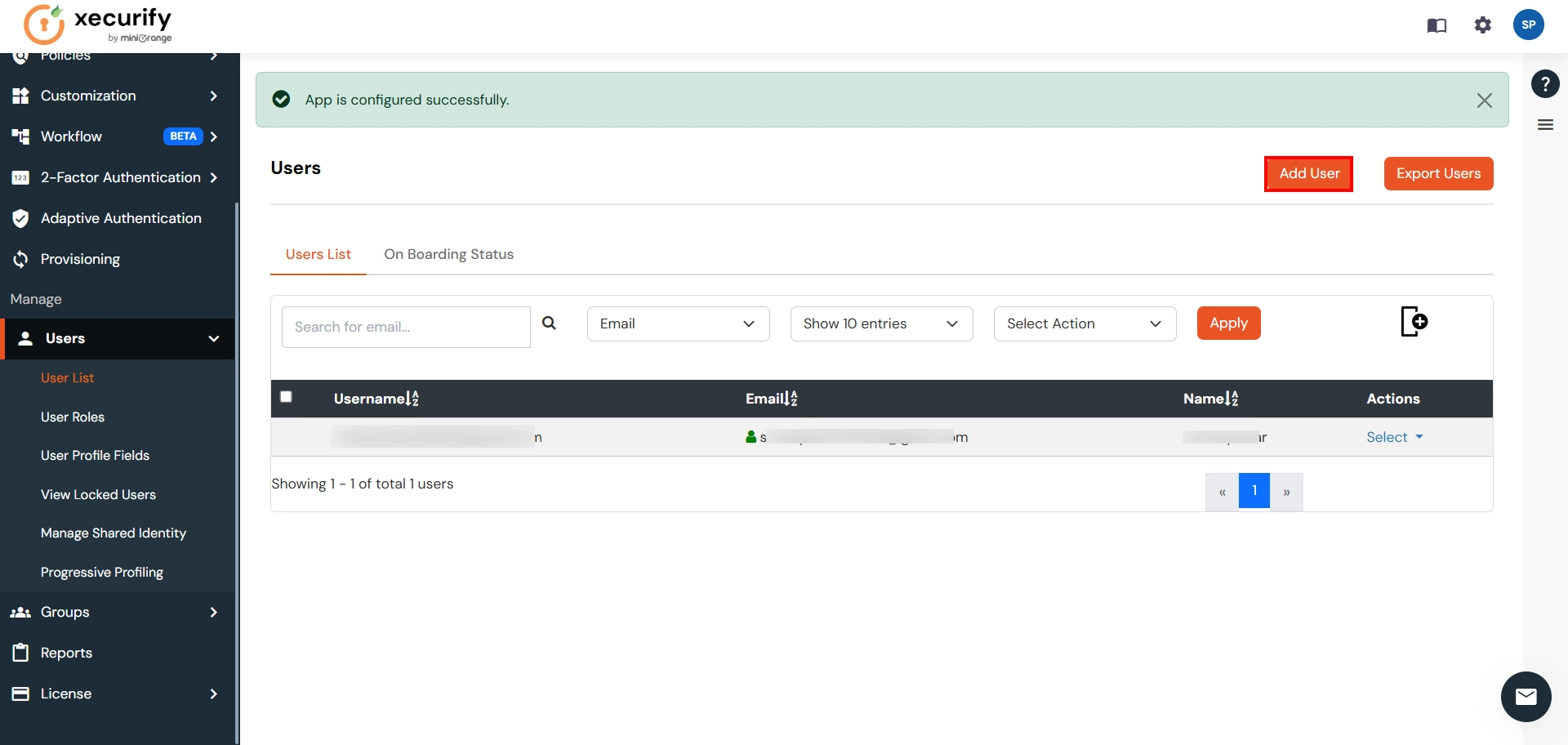
- In the left sidebar hover on Users then click on Users List
- Click on Add User and enter details to enforce Single Sign On(SSO) on that user.
| Custom Application Name | Any name would be fine |
| SP Entity ID or Issuer | You will receive after configuring Atlassian Access App |
| ACS URL | You will receive after configuring Atlassian Access App |
Step 2. Setup Atlassian Cloud
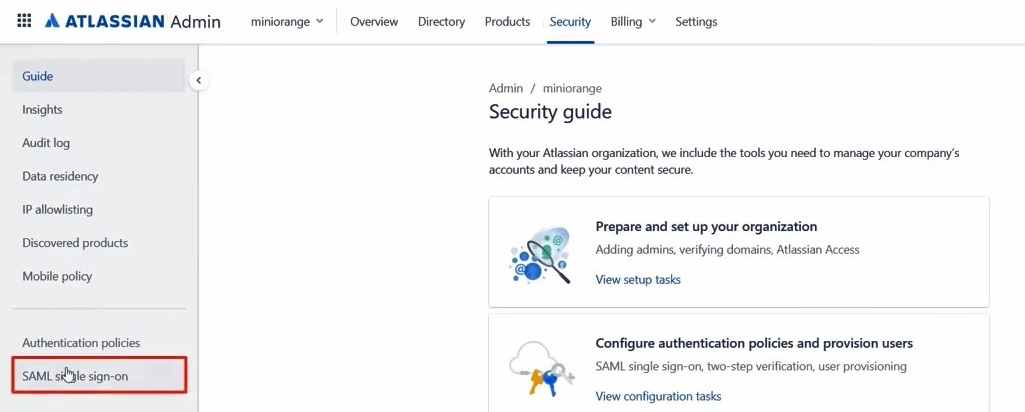
- Now login to Atlassian Cloud Admin Console.
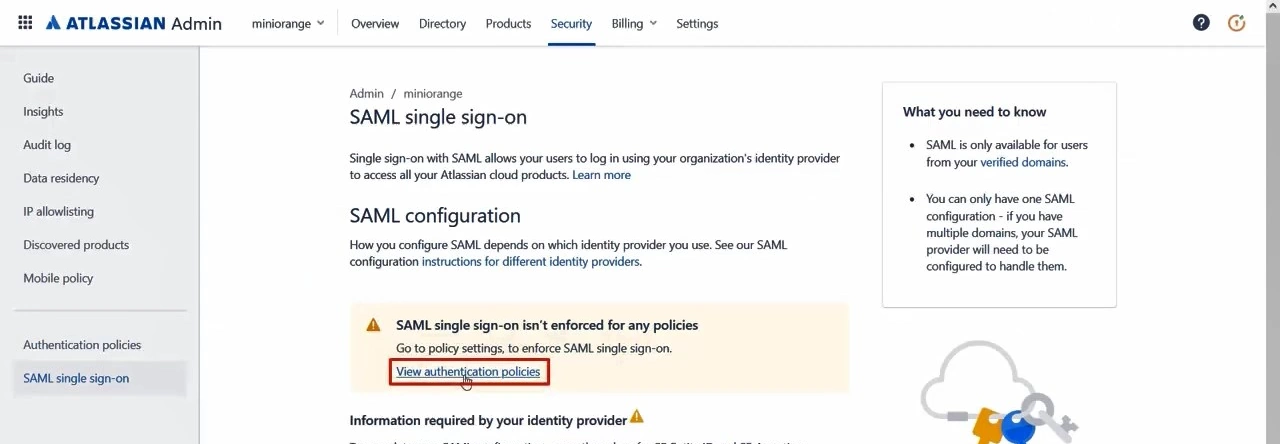
- Select your organization and then select the Security tab. Click on SAML Single Sign-On from the left sidebar.
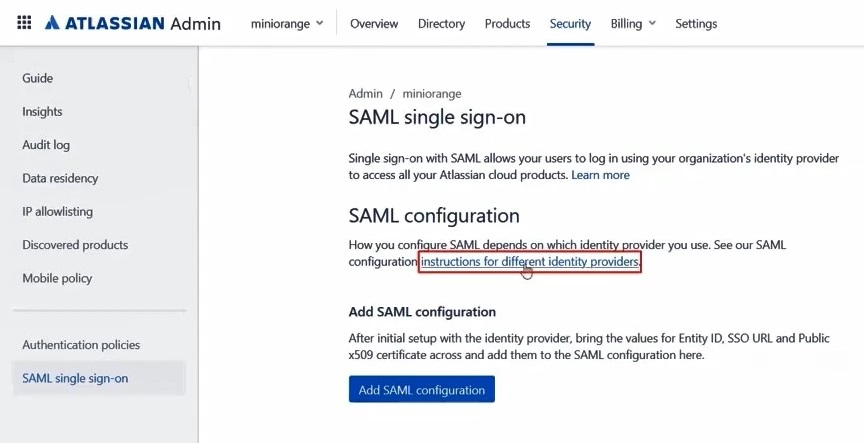
- You can click on Instructions for different Identity Providers. It provides a help page for specific IDP and Attribute Names for Attribute Mapping.
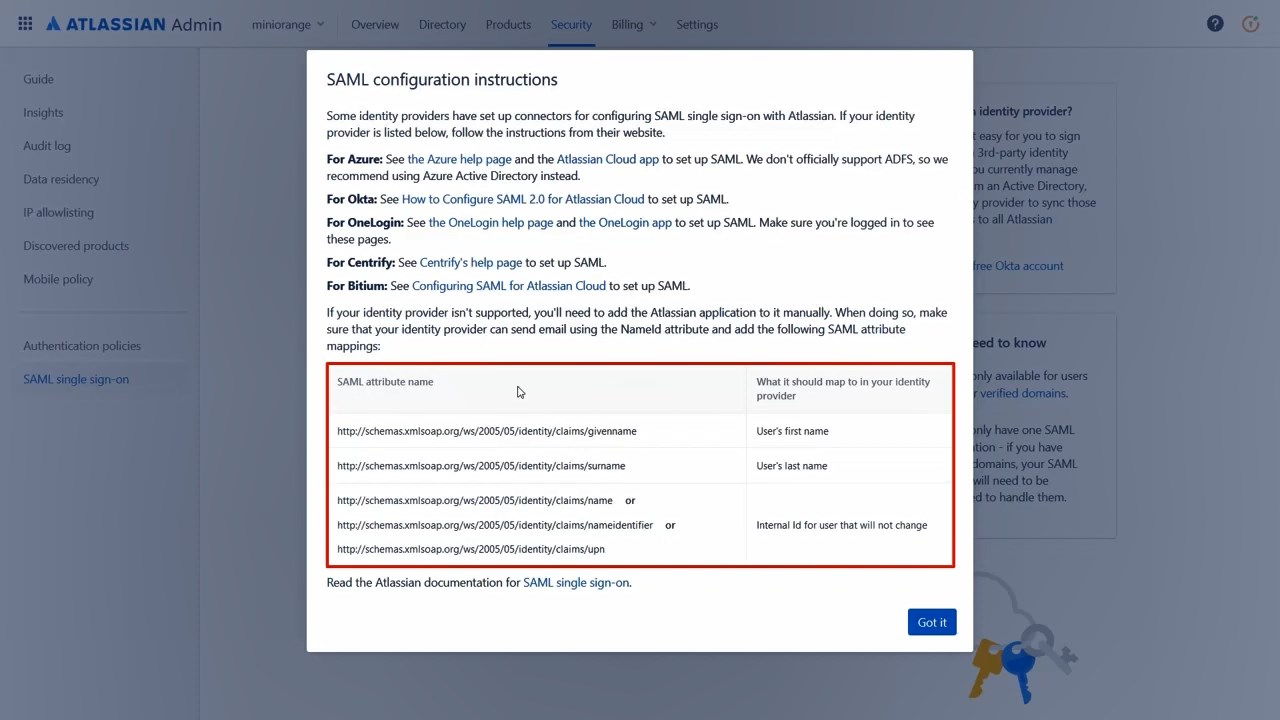
- Here you will get the SAML Configuration Instructions for different identity providers as listed. Click on Got it.
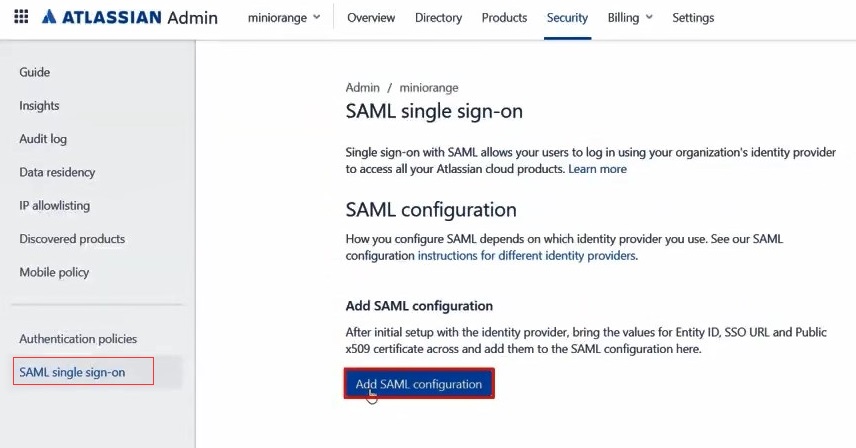
- Click on Add SAML Configuration.
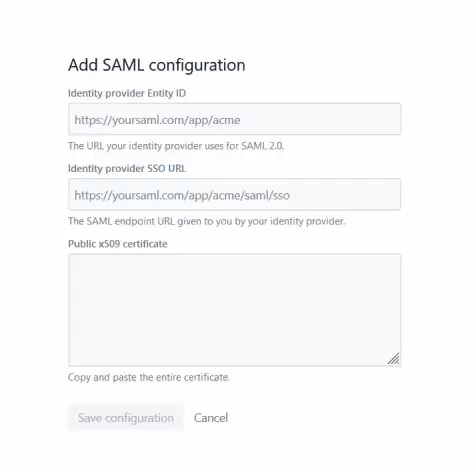
- You will be redirected to the Add SAML Configuration window. Enter IDP Entity ID, SSO URL and the public certificate. Click on the Save Configuration button.
- Now you will be shown SP Entity ID & SP ACS URL as shown below. These details will be needed in miniOrange app configuration. Now set up the Authentication Policies by clicking on the View Authentication Policies.
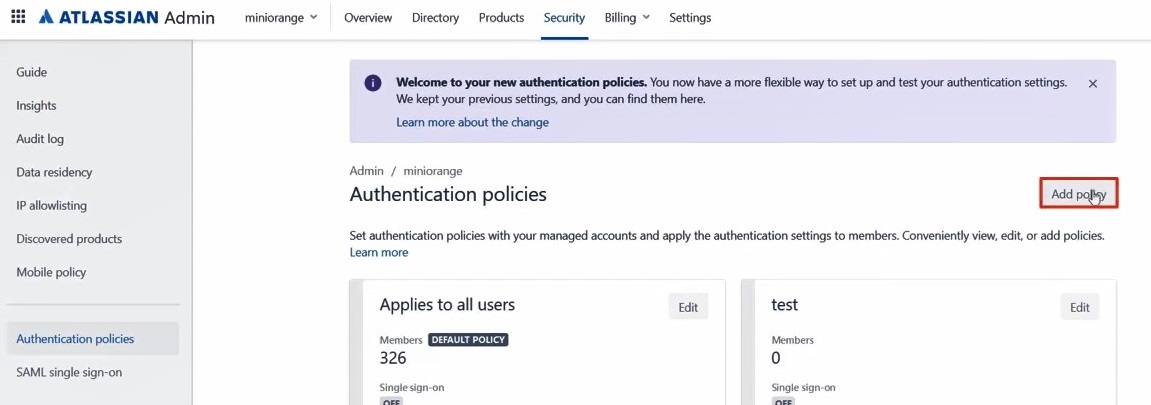
- Click on Add Policy.
- Enter the policy name and add the policy.
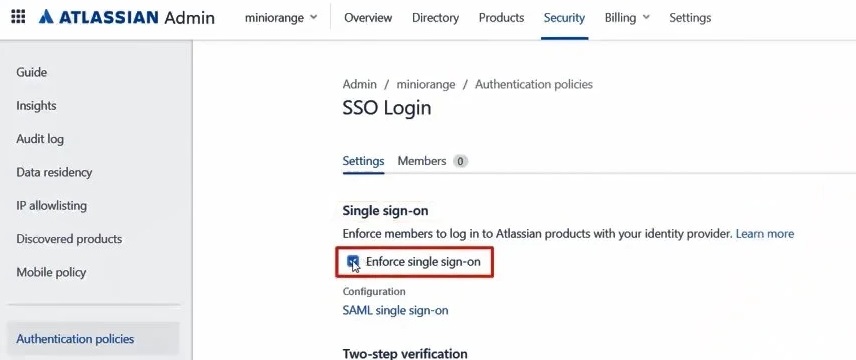
- Now under Single Sign-On, click on Enable Single Sign-On.
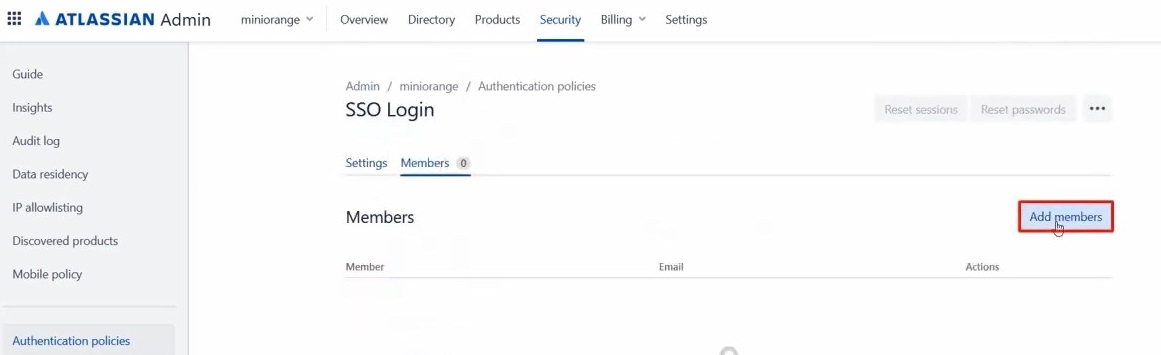
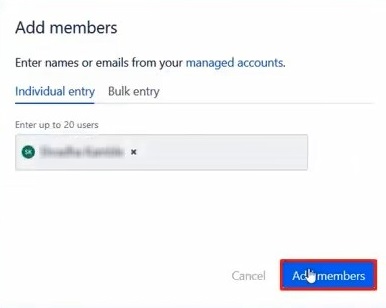
- Then click on the Members tab besides the settings tab and click on Add Members.
- Enter details and click on Add Members.
Step 3. Test Atlassian Cloud - miniOrange Configuration
- Go to Atlassian Login Page.
- Enter email and click on Continue. Then you will be redirected to miniOrange Login Page
- After logging into miniOrange, you will be successfully logged into Atlassian Cloud Dashboard
If you do not have any IDP, you can always go with miniOrange IDP.
Part 2 : Configuring SAML SSO between miniOrange as SP and PingOne as IDP
Step 1. Setup PingOne as IDP
- Login to your PingOne environment as the administrator. Click on your ProfileAdmin.
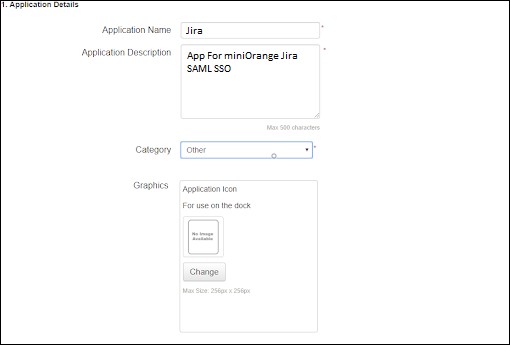
- Go to ApplicationsAdd ApplicationNew SAML Application.
- Enter the application details and click Continue. Application Name, Application Description, and Category are required fields. For logos and icons, PNG is the only supported graphics format.
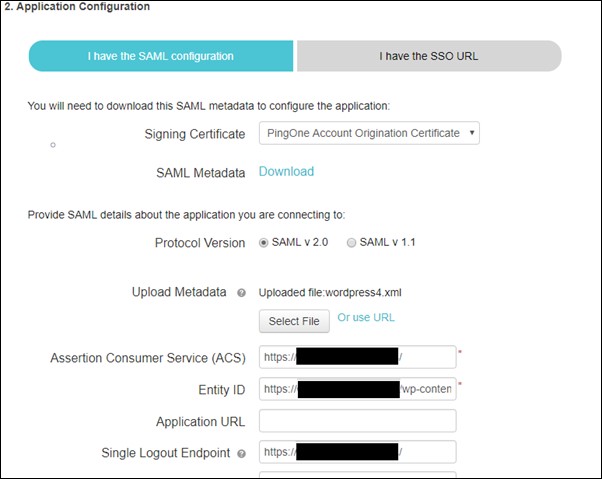
Provide the SAML configuration details for the application.
- Signing. In the dropdown list, select the signing certificate you want to use.
- SAML Metadata. Click Download to retrieve the SAML metadata for Ping One. This supplies the PingOne connection information to the application.
- Protocol Version. Select the SAML protocol version appropriate for your application.
- Upload Metadata. Click Choose File to upload the application’s metadata file. When you are manually assigning an Entity ID value, the Entity ID must be unique, unless you are assigning the Entity ID value for a private, managed app (an app that is supplied & configured by PingOne for Enterprise administrator, rather than an SP.
- Single Logout Endpoint. The URL to which our service will send the SAML Single Logout (SLO) request using the Single Logout Binding Type that you select.
- Single Logout Response Endpoint. The URL to which your service will send the SLO Response.
- Single Logout Binding Type. Select the binding type (Redirect or POST) to use for SLO.
- Primary Verification Certificate. Click Choose File to upload the primary public verification certificate to use for verifying the SP signatures on SLO requests and responses.
- Signing Algorithm. Use the default value or select the algorithm to use from the dropdown list.
You can also provide following optional attributes.
- Encrypt Assertion. If selected, the assertions PingOne sends to the SP for the application will be encrypted.
- Encryption Certificate: Upload the certificate from miniOrange plugin to use to encrypt the assertions.
- Encryption Algorithm: Choose the algorithm to use for encrypting the assertions. We recommend AES_256 (the default), but you can select AES_128 instead.
- Transport Algorithm: The algorithm used for securely transporting the encryption key. Currently, RSA-OAEP is the only transport algorithm supported.
- Force Re-authentication. If selected, users having a current, active SSO session will be re-authenticated by the identity bridge to establish a connection to this application.
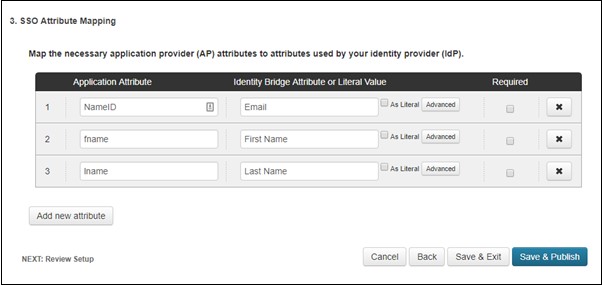
- Click Continue to Next Step. The SSO Attribute Mapping page is displayed.
- In the Attribute Mapping, Modify or add any attribute mappings as necessary for the application.
- The summary information for the application configuration is then displayed on a new page and the new SAML application is added to your My Applications list.
Step 2. Setup miniOrange as Service Provider
- Go to miniOrange Admin Console.
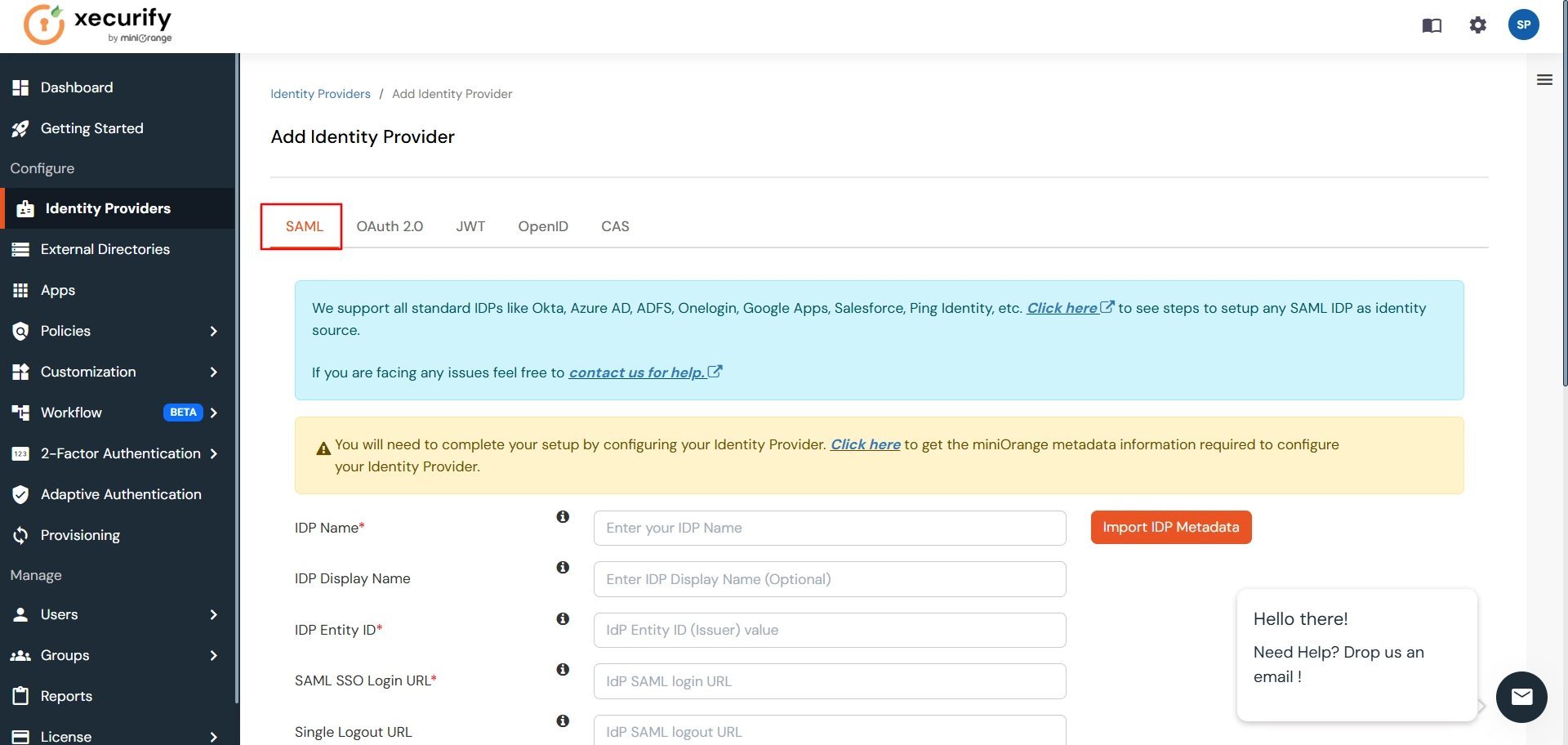
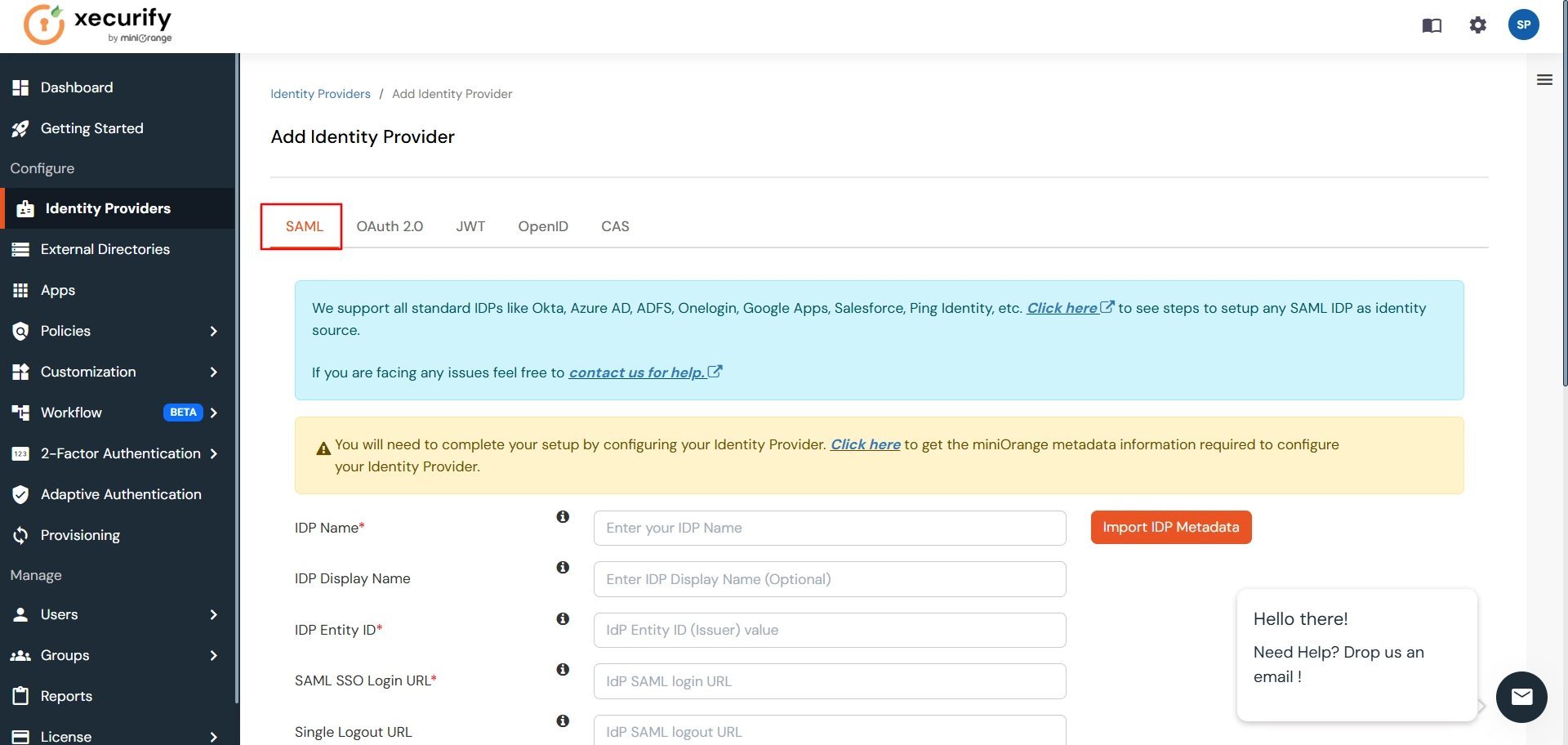
- From the left navigation bar select Identity Provider. Then click on Add Identity Provider
- Select SAML tab.
- Click on Show Metadata details under For SP - INITIATED SSO. You can either manually enter details or use Metadata URL or File
- Now to create SAML app for PingOne, go to the Add Identity Provider page and click on Import IDP Metadata. Import the metadata file that you will get from the SAML Login Information section of PingOne.
- If you don't have a metadata file, you can also provide the details manually. You need to configure following endpoints:
- Few other optional features that can be added to the Identity Provider(IDP) are listed in the table below:
- Click on Save.
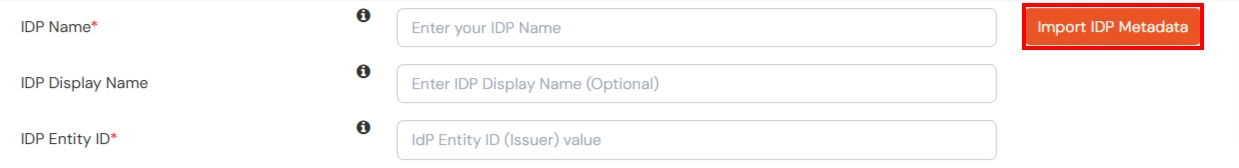
| IDP Entity ID | Entity ID of IDP |
| Single Login URL | Login Url from IDP |
| Single Logout URL | Logout Url from IDP |
| X.509 Certificate | The public key certificate of your IDP. |
| Domain Mapping | Can be used to redirect specific domain user to specific IDP |
| Show IdP to Users | Enable this if you want to show this IDP to all users during Login |
| Send Configured Attributes | Enabling this would allow you to add attributes to be sent from IDP |
Step 3. Test Connection between miniOrange and PingOne
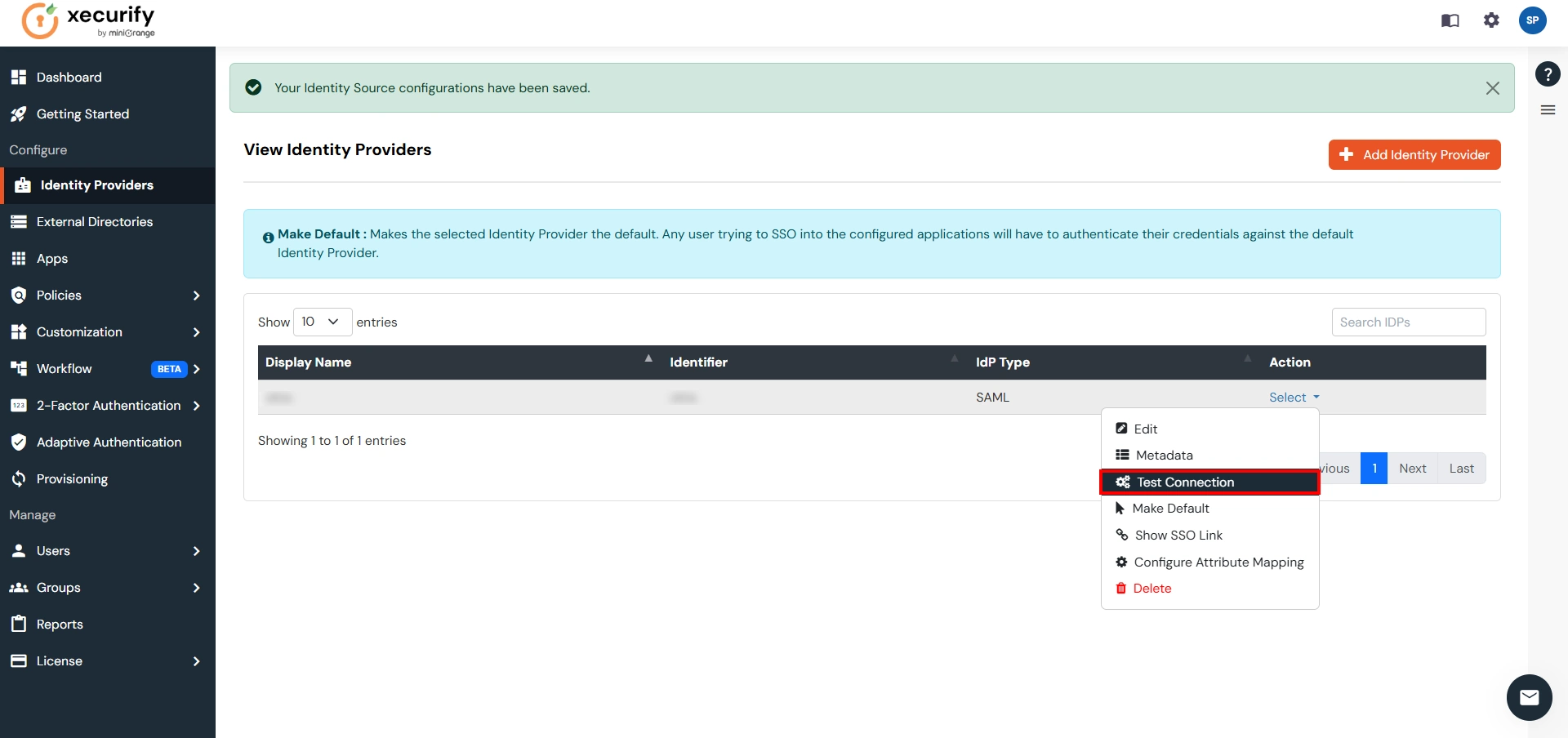
- Go to the miniOrange Admin Dashboard.
- Go to Identity Providers tab. Then click on select button under the app you just created. Then click on Test Connection.
- A new popup login window will open. Enter your credentials and login.
- Now you will see TEST SUCCESSFUL in a new popup window. If not, then check if you have missed any of the above step.
Part 3: Testing Connection between Atlassian and PingOne with miniOrange
- Go to Atlassian Login Portal.
- Enter email and click on Continue. Then you will be redirected to PingOne Login Page.
- After logging into PingOne Login Page, you will be successfully logged into Atlassian Cloud Dashboard.

Additional Resources
Did this page help you?

 Try it for free
Try it for free