miniOrange OAuth/OIDC App
Single Sign On and User Identity that’s easy to use
100%
Secure Authentication
54+
Integrated Add-Ons
The Challenge
Trigger 2FA on identity provider with help of ACR value
Mercedes is a German automotive industry known for producing luxury vehicles and commercial vehicles. Mercedes was looking for a work around to add an extra level of authentication on their in house OpenID provider(aka provider) for the users using SSO. They were already using our miniOrange OAuth/OIDC SSO plugin to allow their users to login into the Atlassian(Jira/Confluence) applications from their identity provider. They further wanted to configure 2FA on their provider side for these users. So, whenever an authorization request is made from any Atlassian application to the provider for SSO, the provider prompts for 2FA.
Solutions we provided to Mercedes

OAuth/OIDC SSO
Two Factor Authentication
The provider would prompt for 2FA if the OpenID client sent any additional parameter in the authorization request. To achieve this we sent an additional parameter called acr value. A custom acr value is sent in the authorization request which the provider evaluates and enforces 2FA based upon. The administrator can configure this value in the plugin. There are various methods used in configuring the 2FA. This increases the security during SSO. Once the user is authenticated against the provider, it sends back the response to the OAuth/OIDC SSO plugin and the user is logged in.
By fulfilling the requirements of Mercedes we were able to include them in our journey of innovations. Being a software security company, we know the importance of organization security and hence build quality products for our clients along with world-class support.
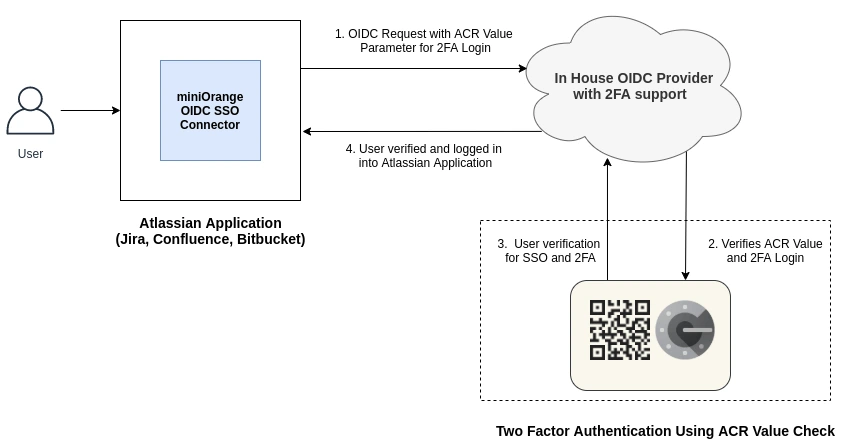
How It Works
The system administrator sets up Single Sign-On for all users and configures a custom acr value in the miniOrange OAuth/OIDC SSO plugin. The value is sent in the authorization request as an extra parameter. Depending on the acr parameter, the OpenID provider prompts 2FA to the user.
Our OAuth/OIDC SSO provides the best SSO features add-on that works with all Identity Providers. It enables users to sign in to the application with their Identity Provider. We support all known providers such as Google Apps, ADFS, Azure AD, Okta, Facebook, Salesforce, GitHub, GitLab, Keycloak, Discord, meetup, AWS Cognito, Azure B2C, Slack, and miniOrange.
Key Benefits
- Easy to integrate: Easily moved user authentication form Atlassian apps(Jira/Confluence) to Identity Provider.
- Ease Of Access: Users have to remember only one set of credentials.
- Force Redirection: User are forced to use their identity provider for authentication for incresed security.
- Secure Access: Made their environmental setup easy to enforce additional security layers like 2FA on top of user authentication on identity provider side which was not possible while using Jira/Confluence application login.
In conclusion, marketplaces have many products according to business needs. For Mercedes, our product proved to be the best. What about you? Which product is best for you?