Contents
Azure AD as IDP – Cloud SAML
Part 2: Setup miniOrange with Azure AD
Step 1. Setup Azure AD as IDP
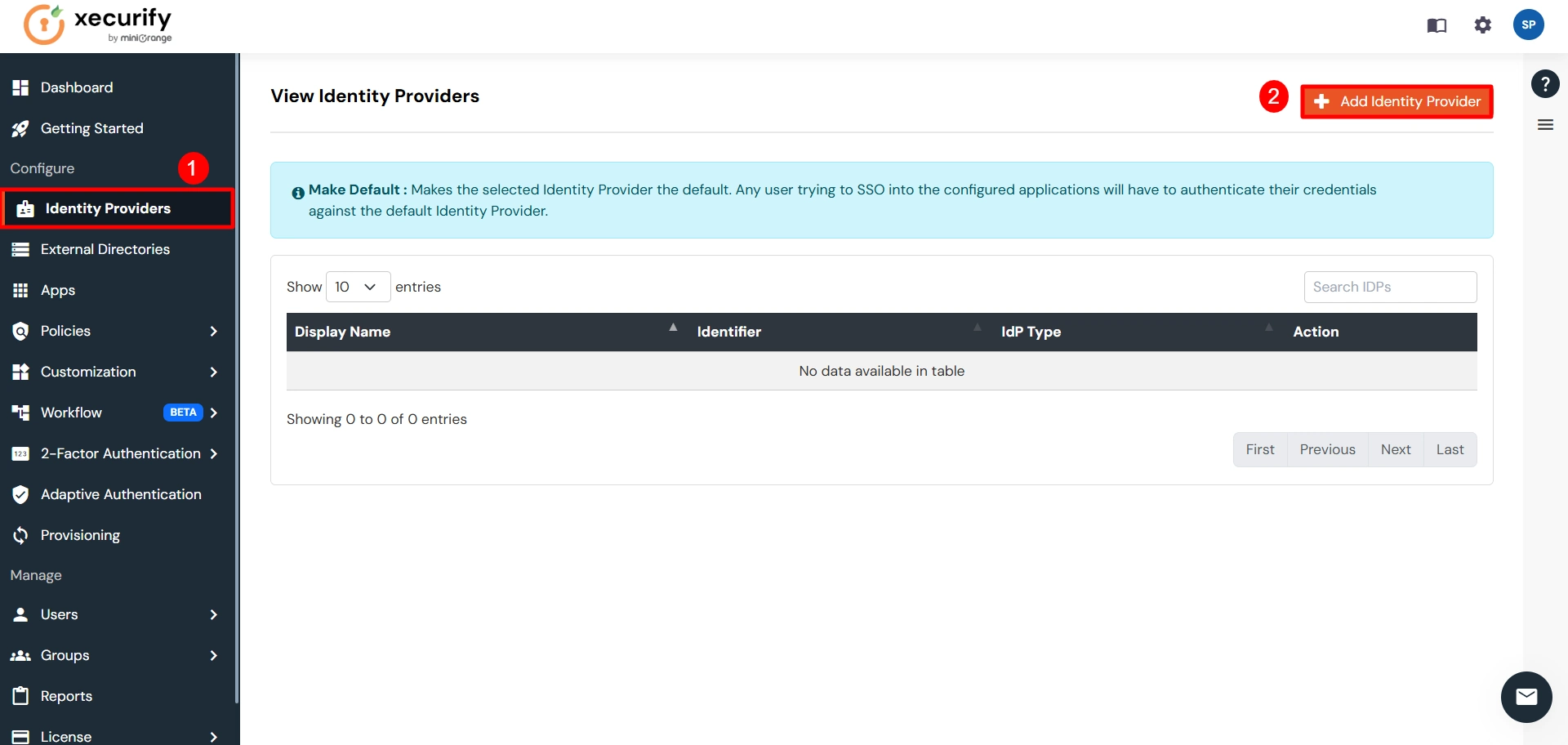
- Go to miniOrange Admin Console.
- From the left navigation bar select Identity Provider
- Click on Add Identity Provider button.
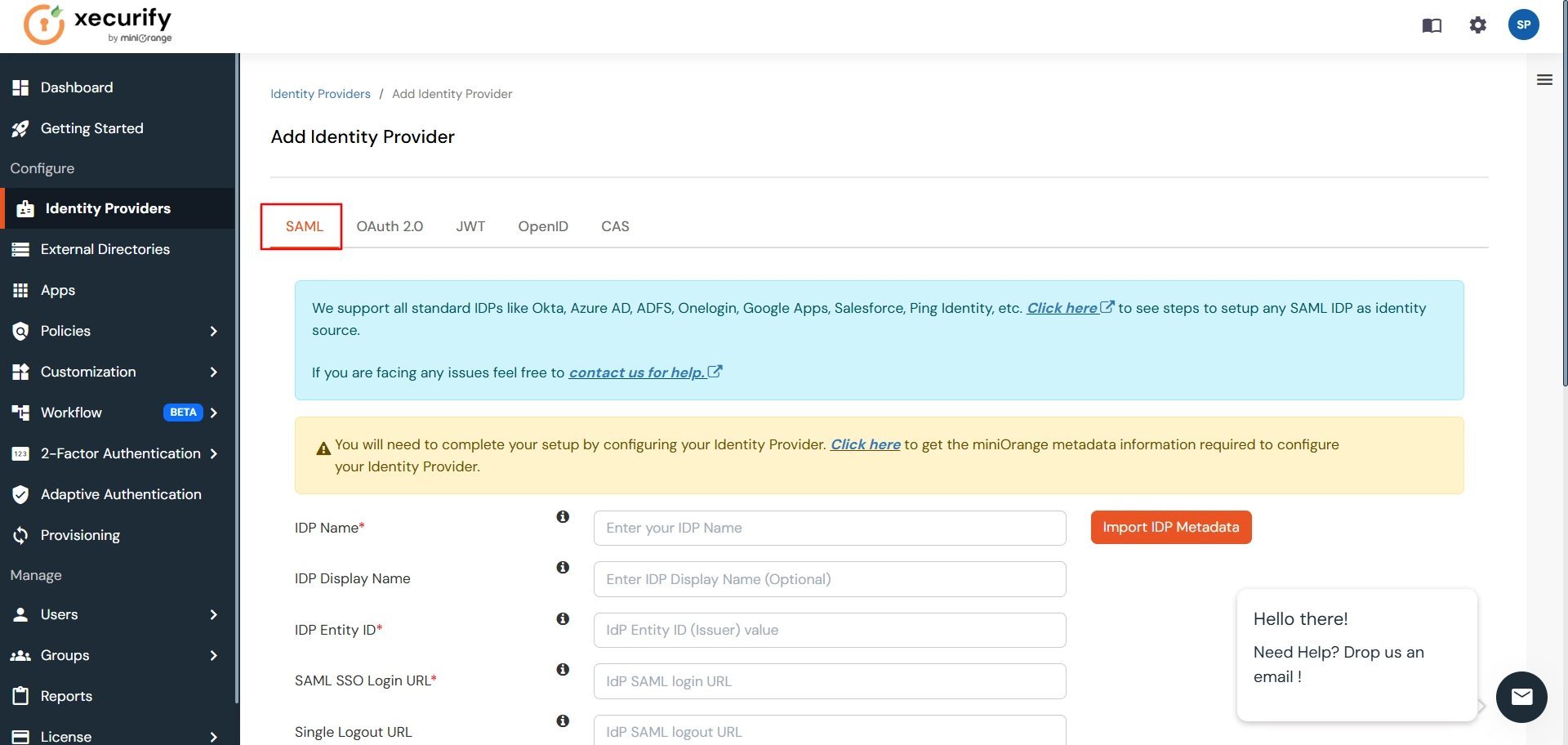
- Select SAML tab.
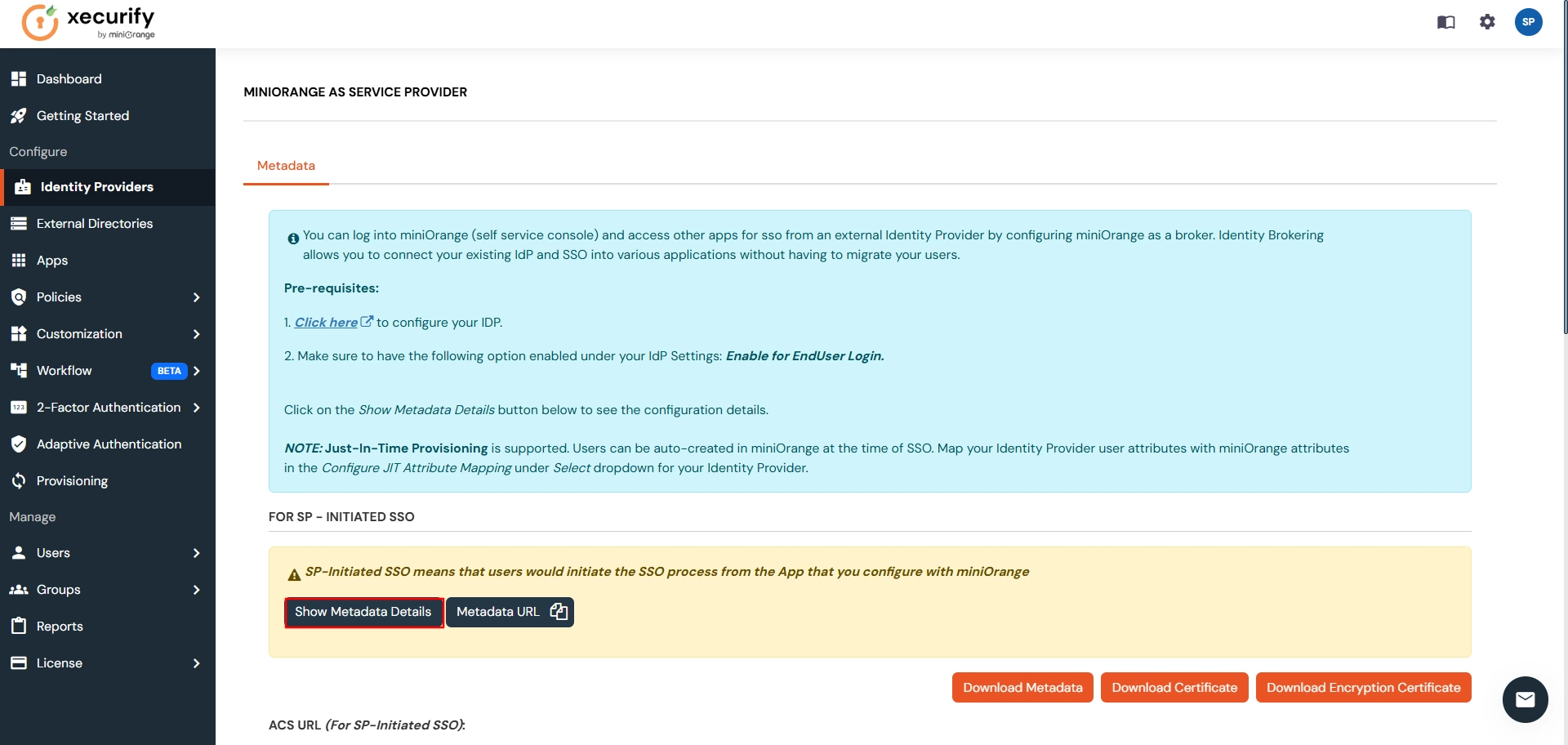
- Click on Show Metadata details under For SP - INITIATED SSO. You can either manually enter details or use Metadata URL or File
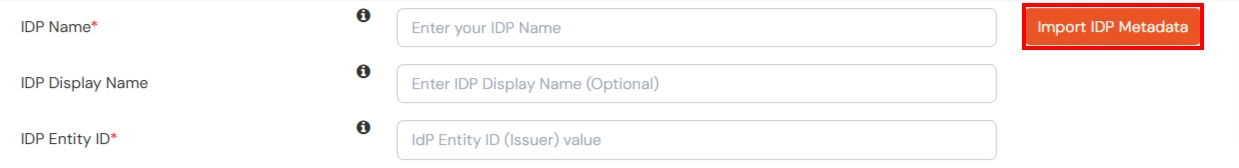
- Now to add SAML app for Azure AD, go to Add Identity Provider page and click on Import IDP Metadata. Import the metadata file that you will get from Azure AD. Refer this step.
- If you don't have a metadata file, you can also provide the details manually. You need to configure following endpoints:
You can get the metadata details of miniOrange app either by clicking on the link shown by
"Click here" in the yellow block, Or you can also get the details after creating the app.
Keep these details handy as we will need these in configuring Azure AD.
| IDP Entity ID | Entity ID of IDP |
| Single Login URL | Login Url from IDP |
| Single Logout URL | Logout Url from IDP |
| X.509 Certificate | The public key certificate of your IDP. |
- Few other optional features that can be added to the Identity Provider(IDP) are listed in the table below:
| Domain Mapping | Can be used to redirect specific domain user to specific IDP |
| Show IdP to Users | Enable this if you want to show this IDP to all users during Login |
| Send Configured Attributes | Enabling this would allow you to add attributes to be sent from IDP |
- Click on Save.
Step 2. Setup Atlassian Cloud
- Log in to Azure AD Portal
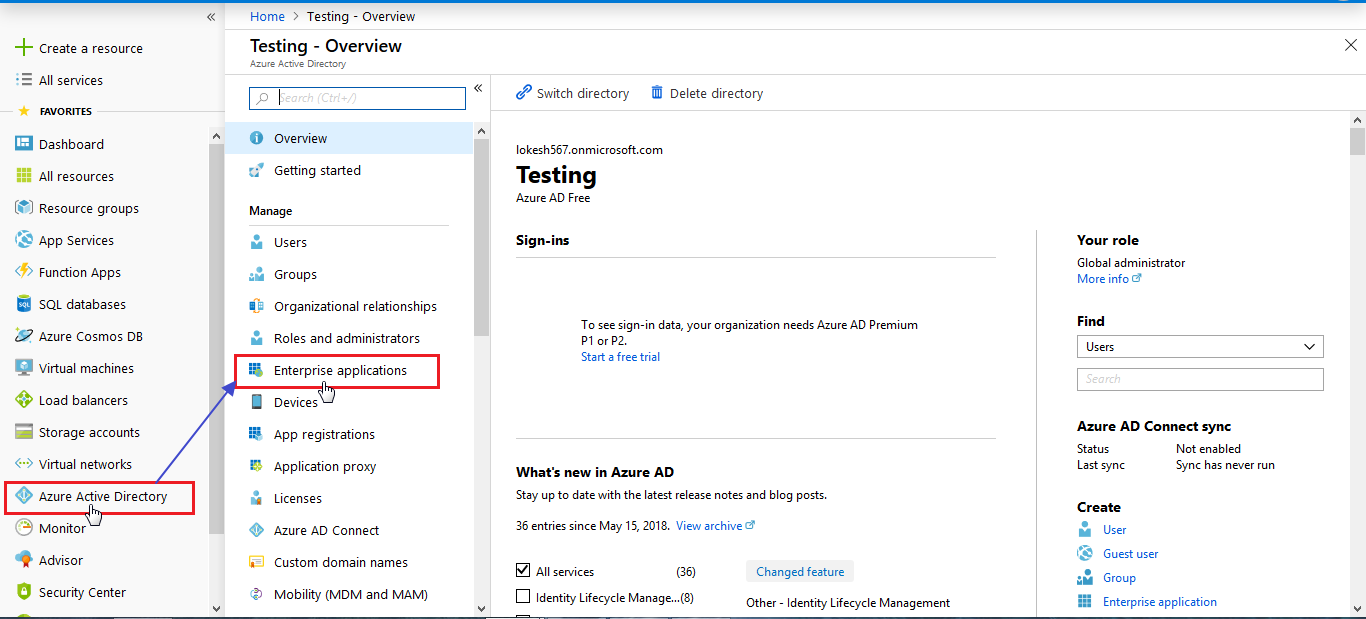
- Select Azure Active Directory ⇒ Enterprise Applications.
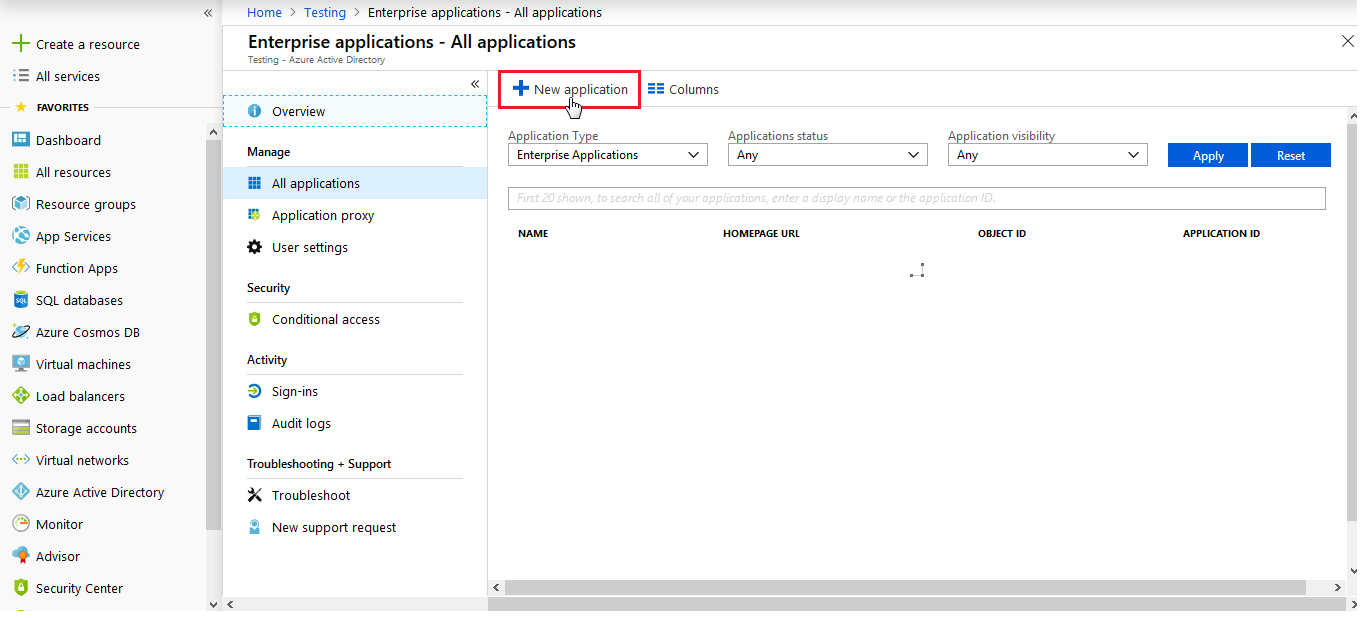
- Click on New Application.
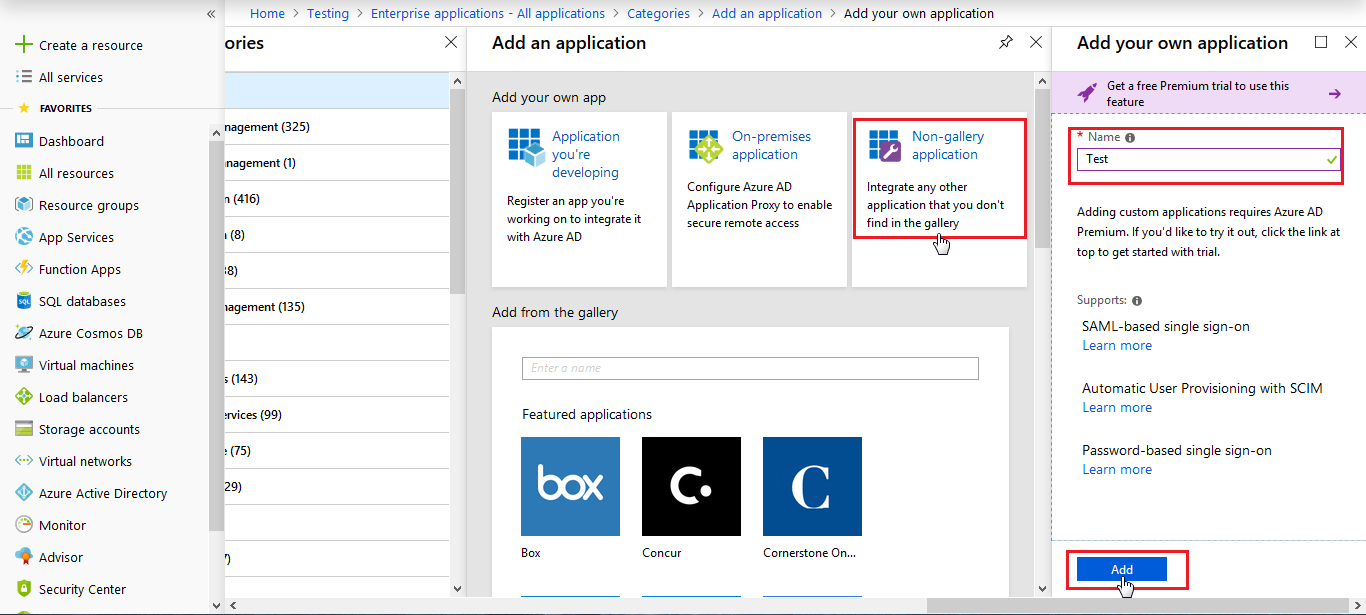
- Click on Non-gallery application section and enter the name for your app and click on Add button.
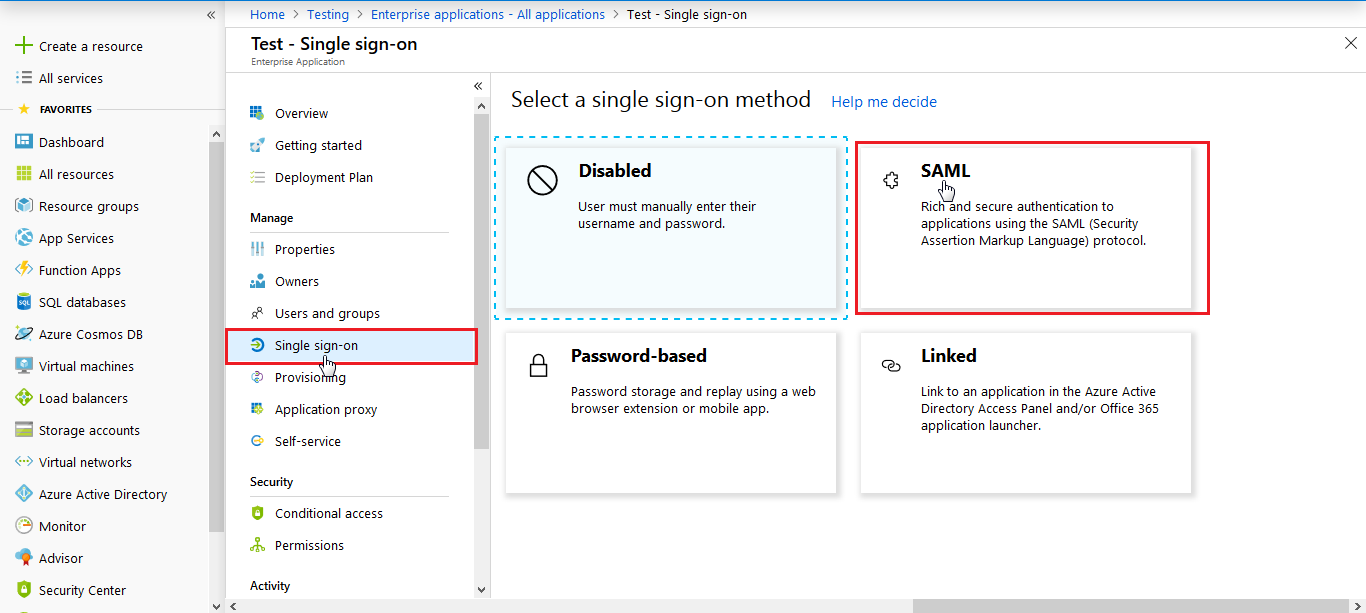
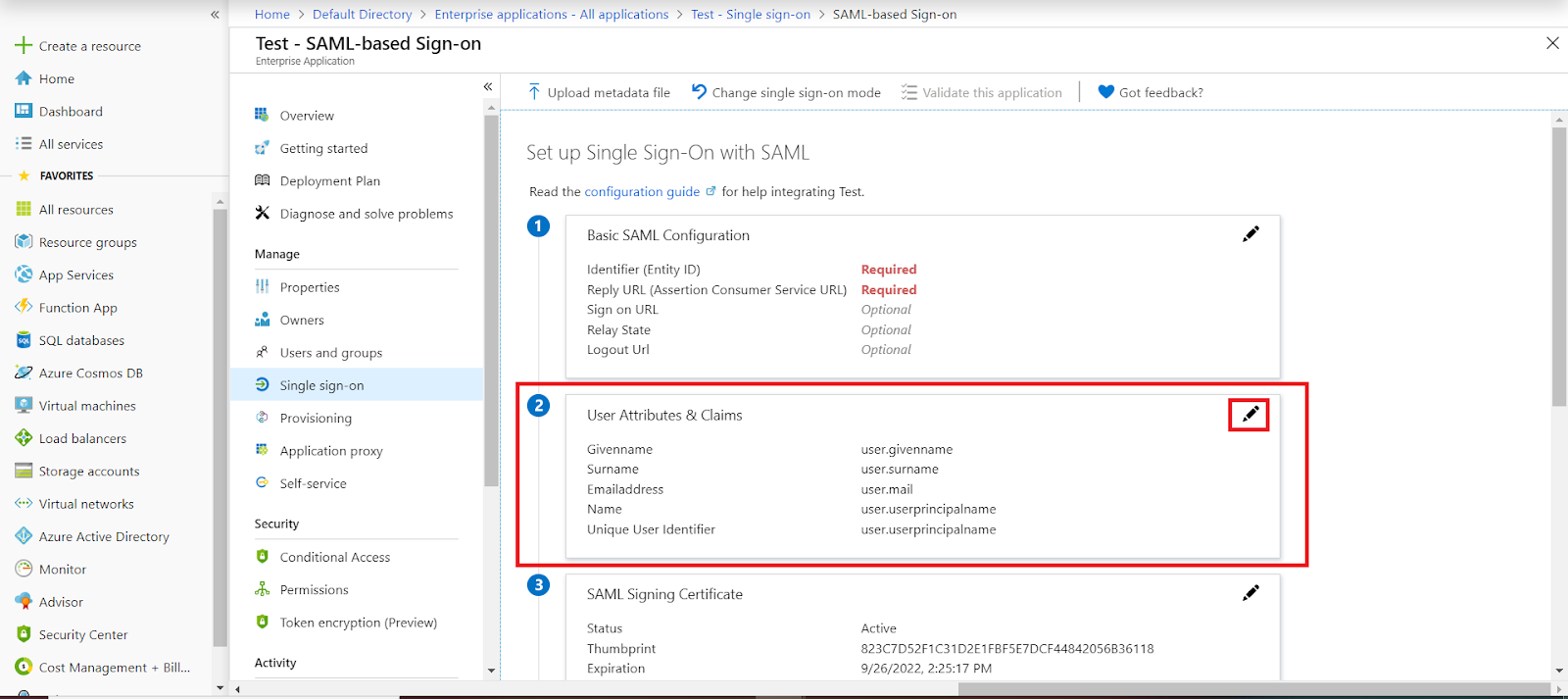
- Click on Single sign-on from the application's left-hand navigation menu. The next screen presents the options for configuring single sign-on. Click on SAML.
- Click on the edit icon to edit SAML Configuration Details
- For Basic SAML configuration you need to get the Entity ID, ACS URL, and the Single Logout URL from miniOrange. Refer this step.
- Enter the values in basic SAML configuration as shown in below screen
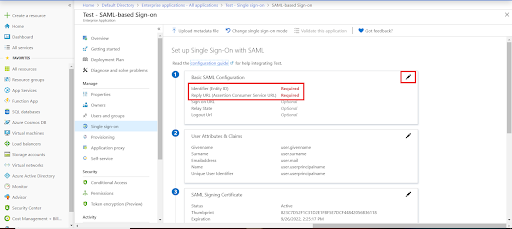
| Identifier (Entity ID) | Entity ID or Issuer |
| Reply URL (Assertion Consumer Service URL) | ACS URL |
| Sign on URL (optional required during IDP-initiated SSO) | SSO Login URL |
| Logout URL | Single Logout URL |
- By default, the following Attributes will be sent in the SAML token...
- Download Federation Metadata xml, and copy the Logout URL as well.
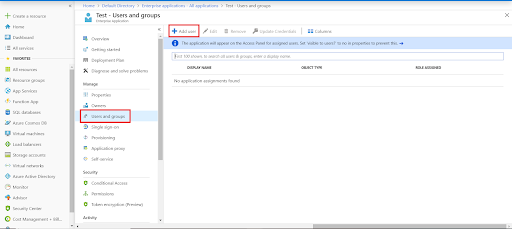
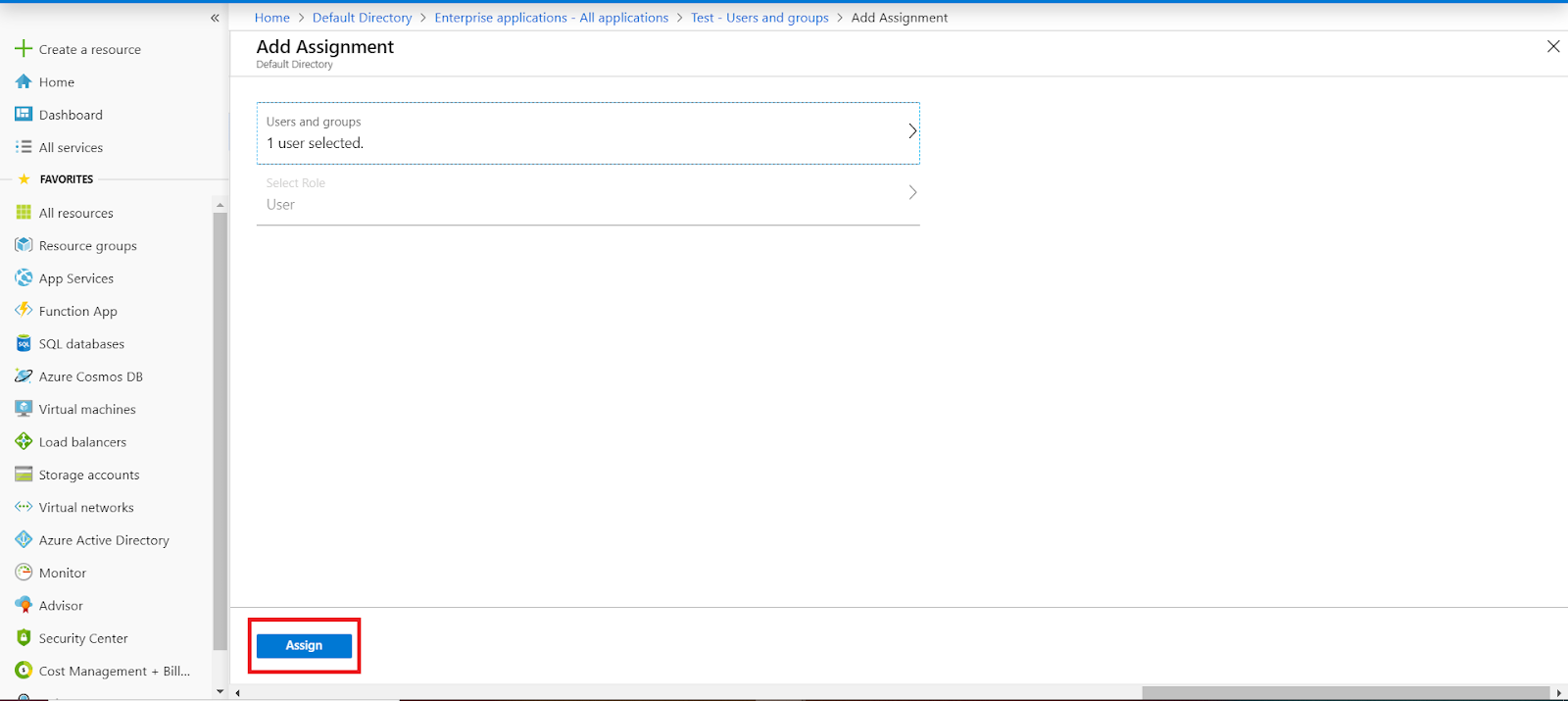
- Assign users and groups to your SAML application.
- Azure AD will not issue a token unless access is granted.
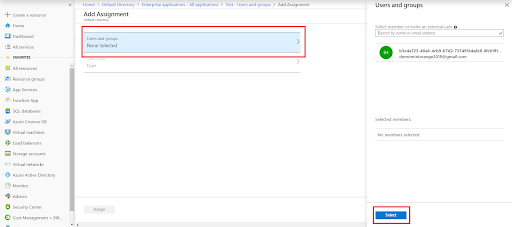
- Click on Users and groups → assign user/group.
- Click Add user → Select user/group → Select.
- Assign role under Select Role → click Assign.
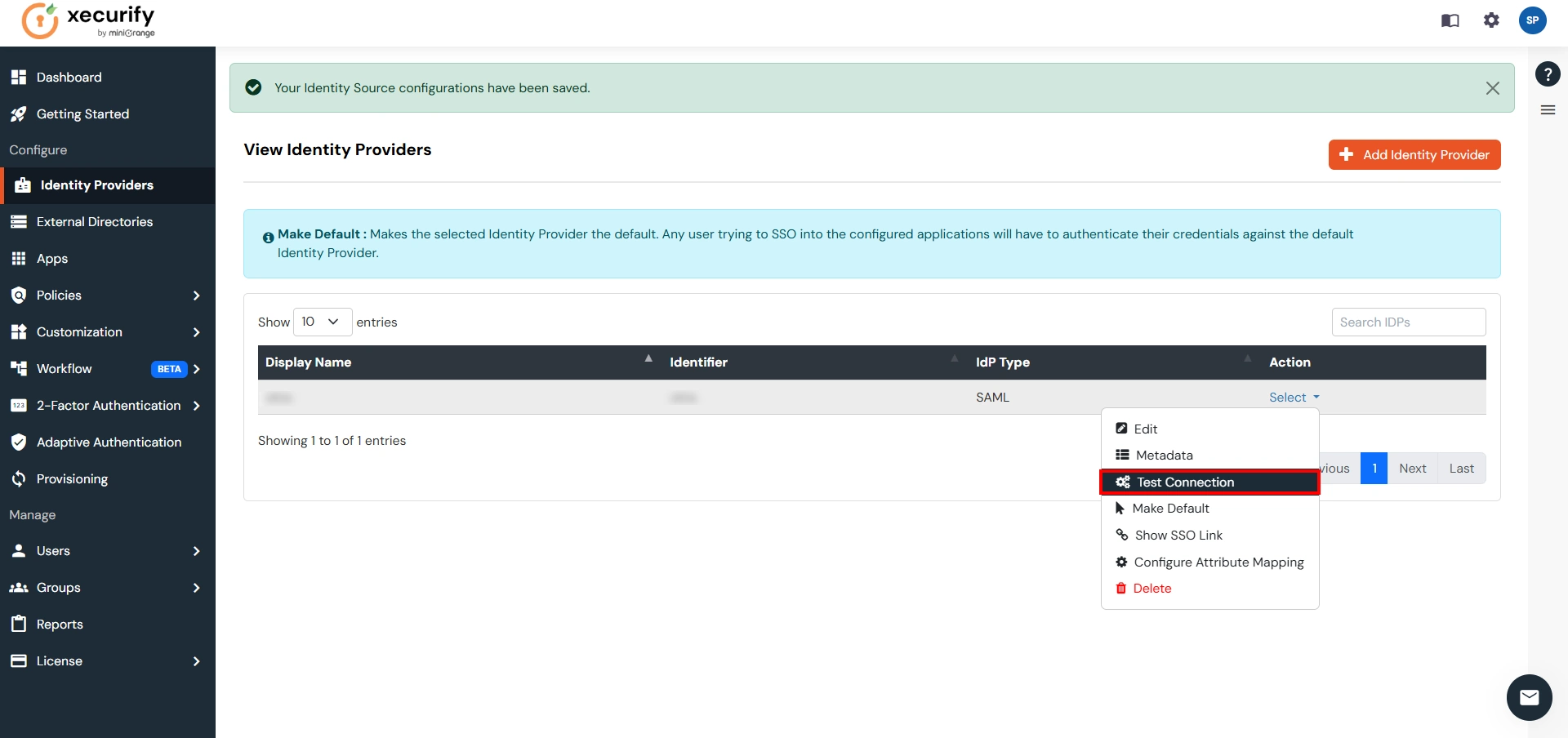
Step 3. Test Connection between miniOrange and Azure AD
- Go to Identity Providers tab → click Select → Test Connection.
- Login in popup window with credentials.
- You will see TEST SUCCESSFUL. If not, verify previous steps.
Part 3: Test Atlassian - Azure AD Configuration
- Go to Atlassian Login Portal.
- Enter email and click on Continue. Then redirected to Azure AD Login Page.
- Login to Azure AD → logged into Atlassian Cloud Dashboard.
×
![ADFS_sso]()
