Contents
SSO for Externally Shared Confluence Links using Azure AD(Entra ID) as IDP
Make sharing Confluence Pages/Spaces easy and secure for external users. Just set up single sign-on (SSO) on your links. SSO ensures that only authorized users access shared content. Follow the simple instructions below to explore our setup guide for sharing SSO-enabled links with your external users.
Download And Installation
- Log into your Confluence instance as an admin.
- Click on Apps from the header then navigate to Find new apps.
- Locate Share Confluence with External Users (Secure Share).
- Click on Try it free to begin a new trial of Share confluence with external users.
Pre-requisite
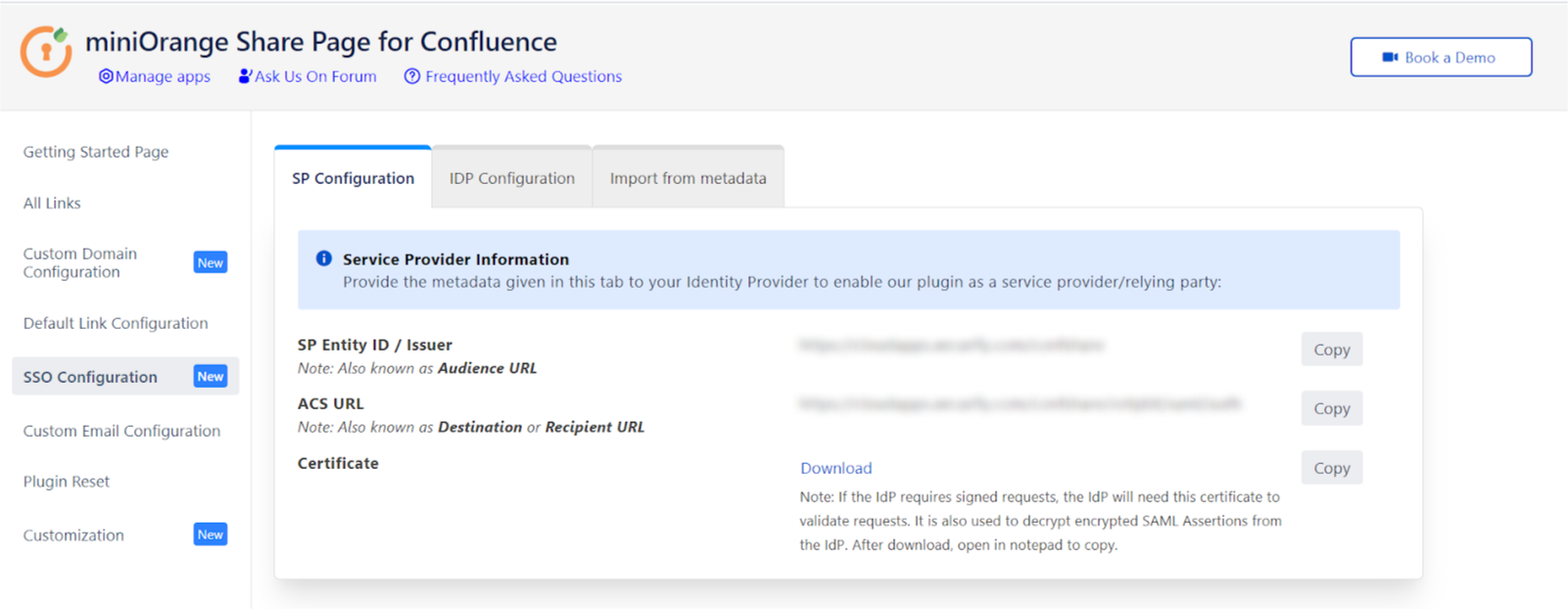
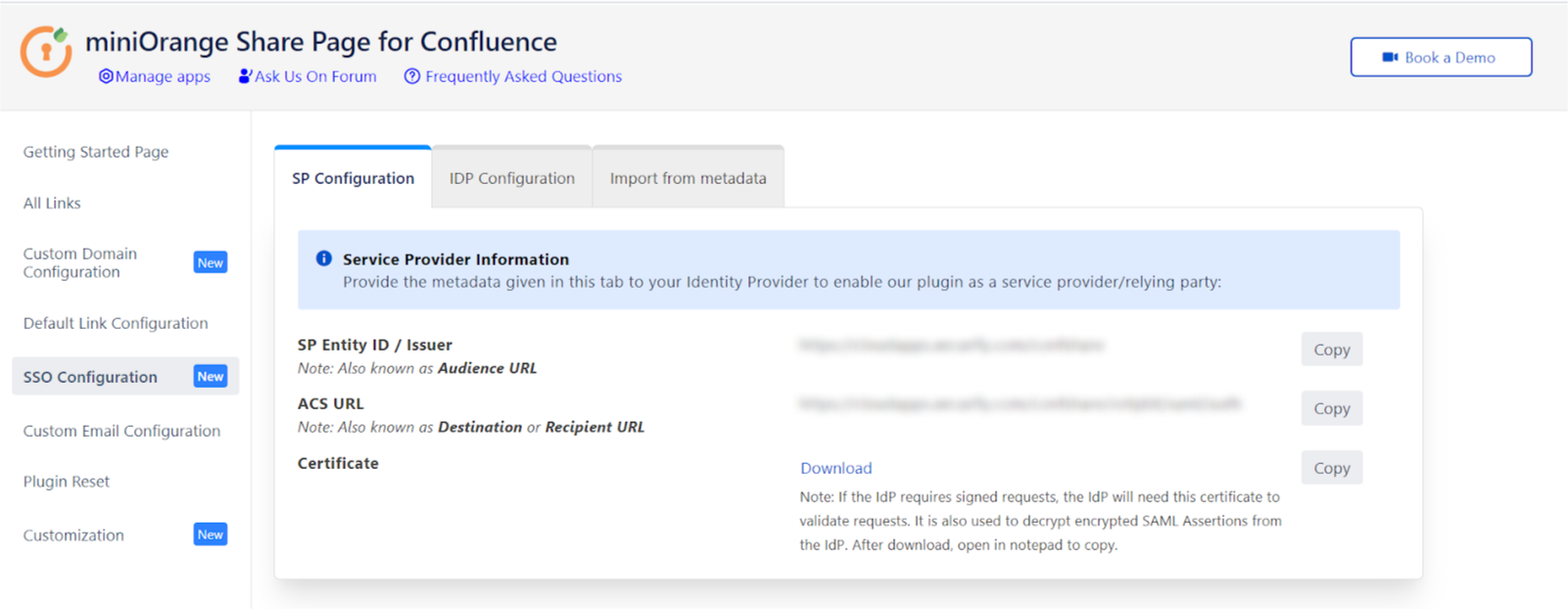
- We will need the SP entity id and ACS URL from the plugin.
- To get this information, go to Apps -> Share confluence with external users
- Then click on SSO Configuration -> SP Configuration
Step 1: Set Up Microsoft Entra ID as Identity Provider
- SP Entity ID
- ACS URL
 Prerequisites:
Prerequisites:
Copy these values from the Service Provider Info tab of the Plugin .
 Instructions:
Instructions:
Note: Enterprise app configuration is the recommended option for SAML . If you do not have Azure subscription or using free account please setup App Registration Configuration.
To perform Single Logout using Microsoft Entra ID (Previously known as Azure AD), the Atlassian instance (E.g. Jira,Confluence) must be https enabled.
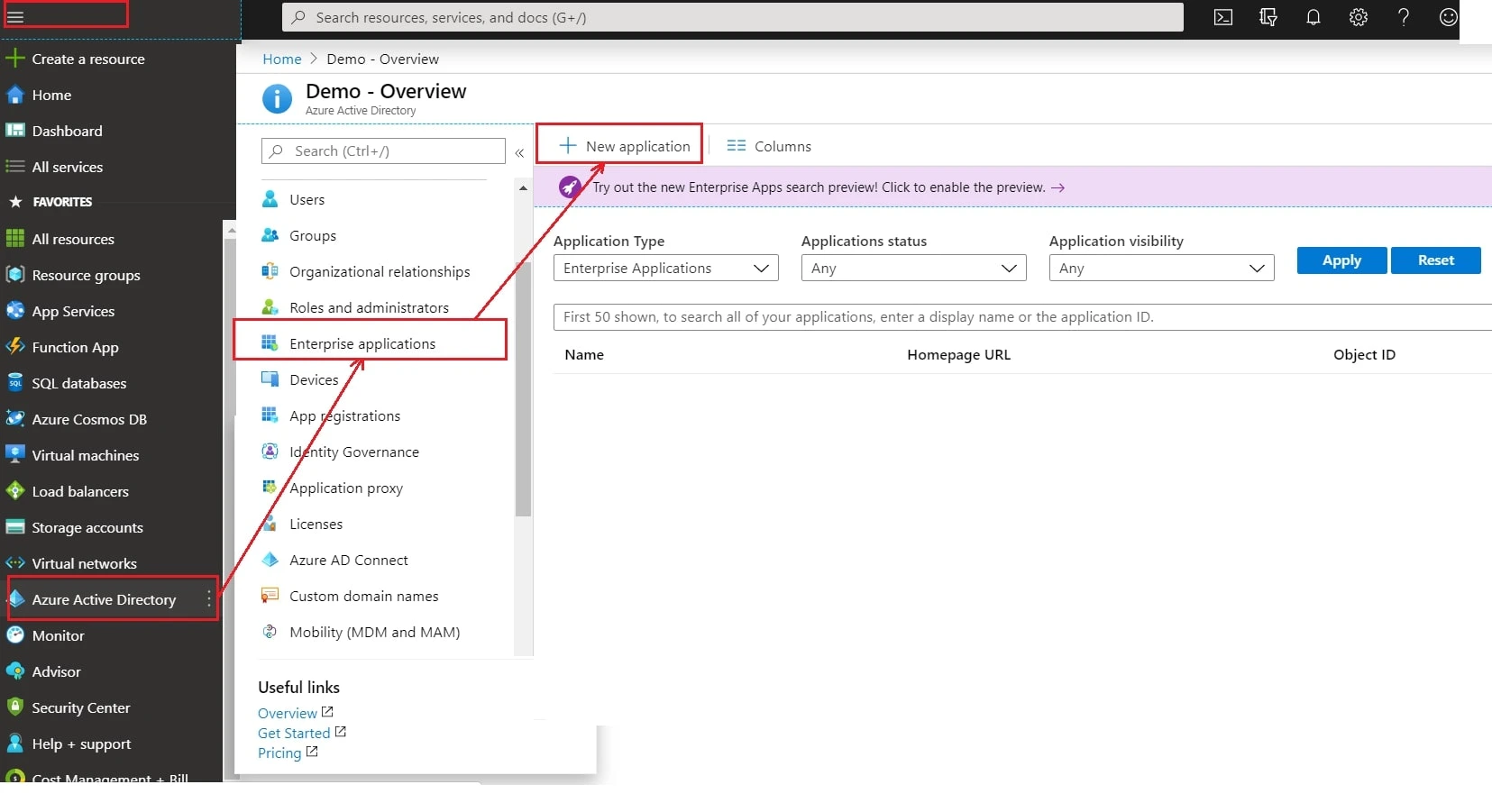
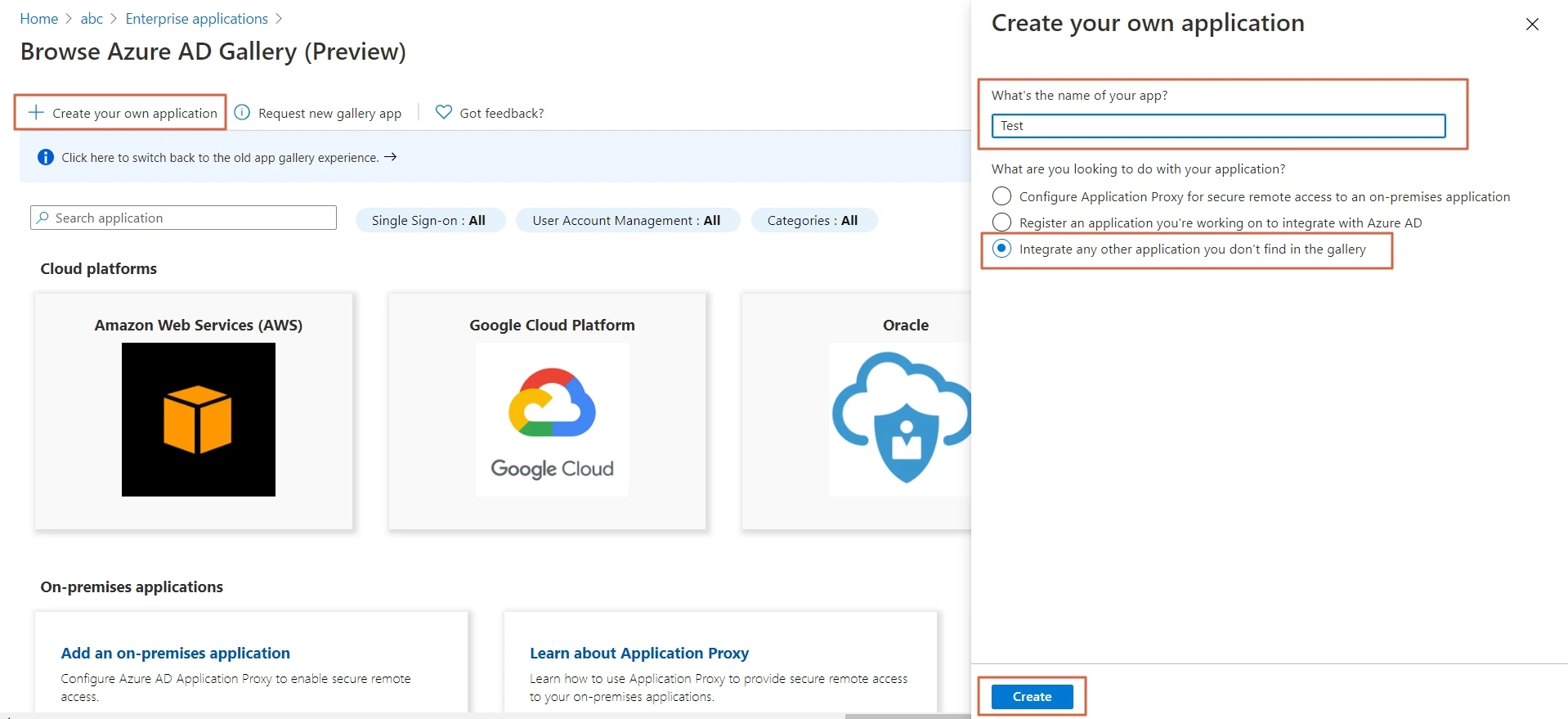
- Log in to Microsoft Entra ID (Previously known as Azure AD) Portal
- Select ⇒ and Azure Active Directory ⇒ Enterprise Applications.
- Click on Create your own application. Then enter the name for your app, select the Integrate any other application you don't find in the gallery checkbox and click on Create button
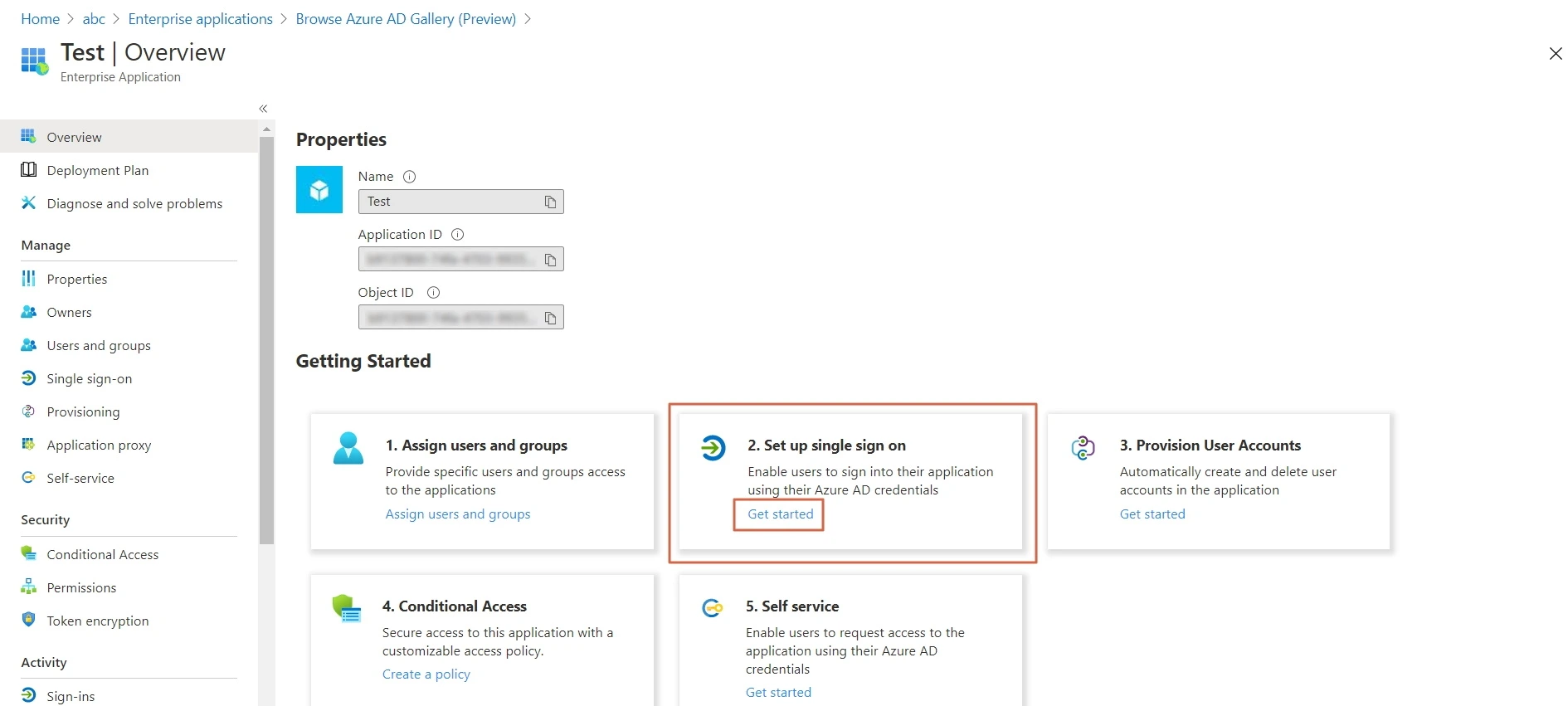
- Click on Set up Single sign-on.
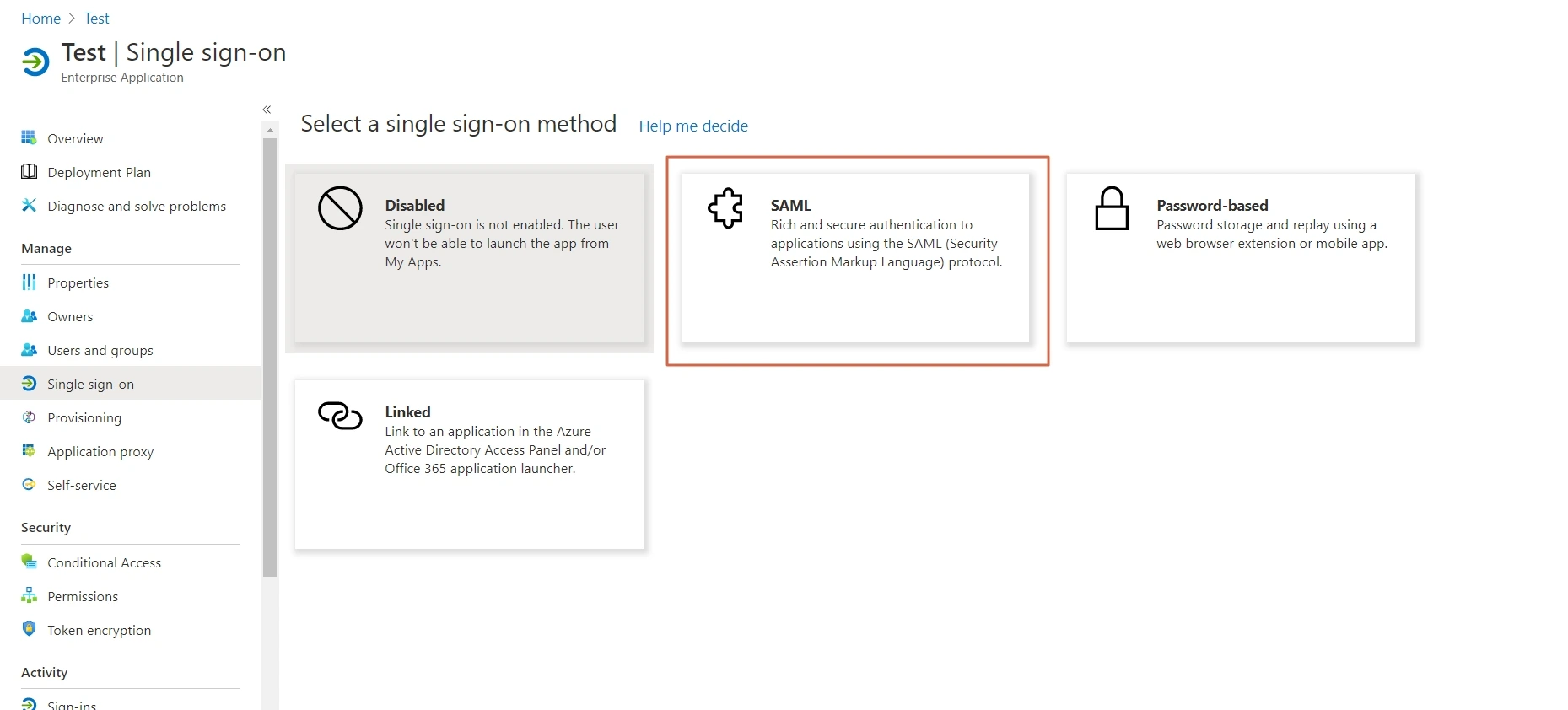
- The next screen presents the options for configuring single sign-on. Click on SAML.
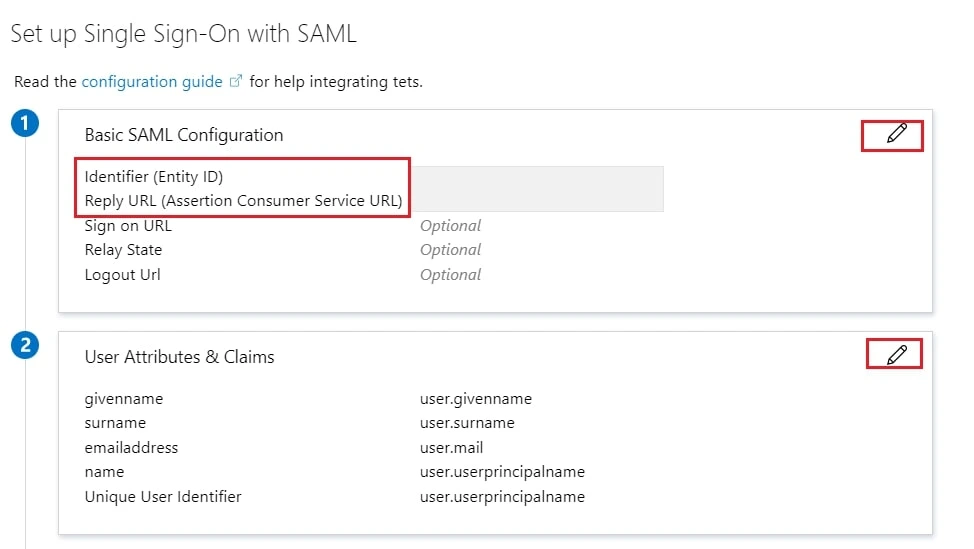
- Edit the option 1 :Basic SAML Configuration to configure plugin endpoints.
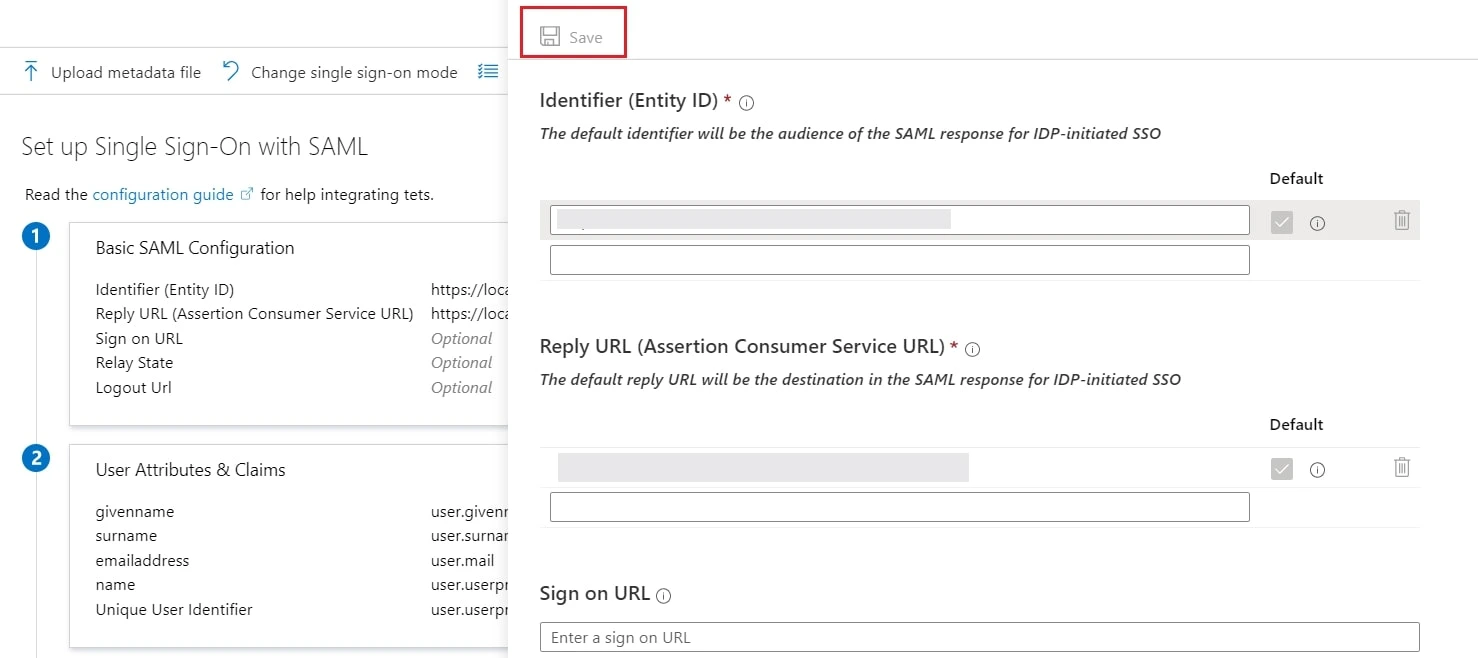
- Enter the SP Entity ID for Identifier and the ACS URL for Reply URL from Service Provider Info tab of the plugin.
- Click on Save icon.
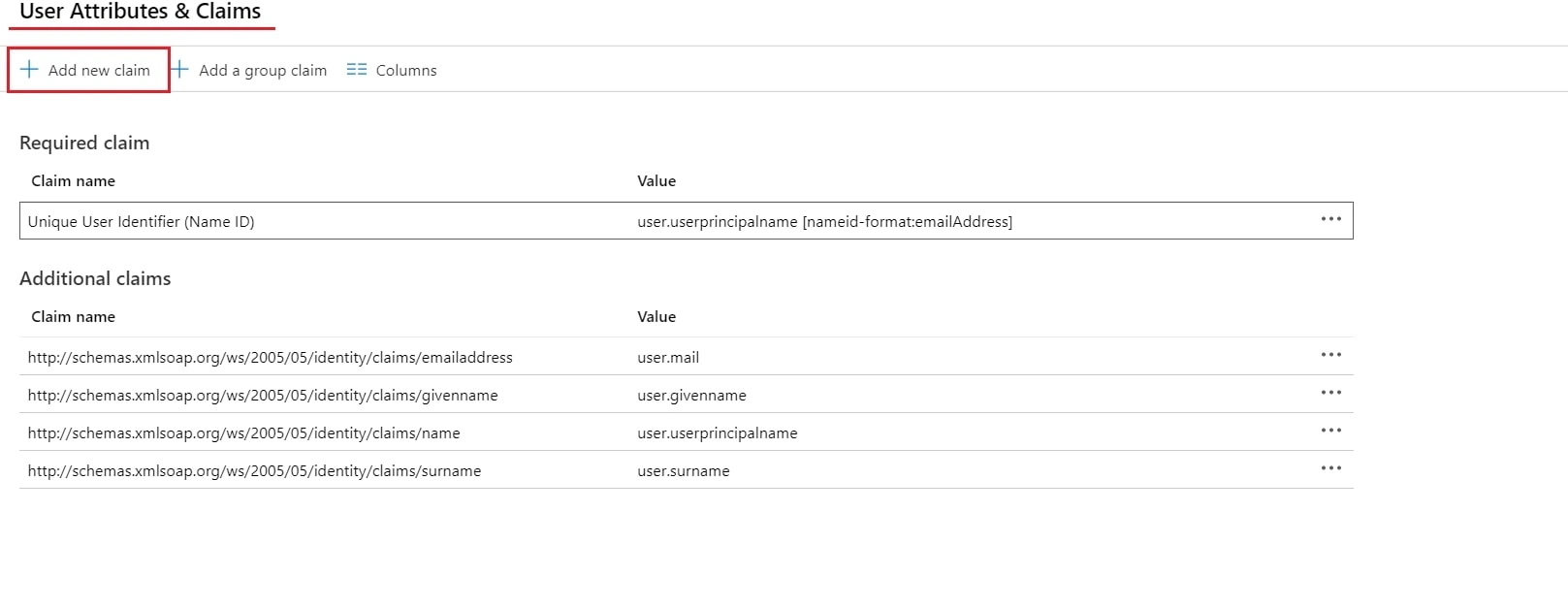
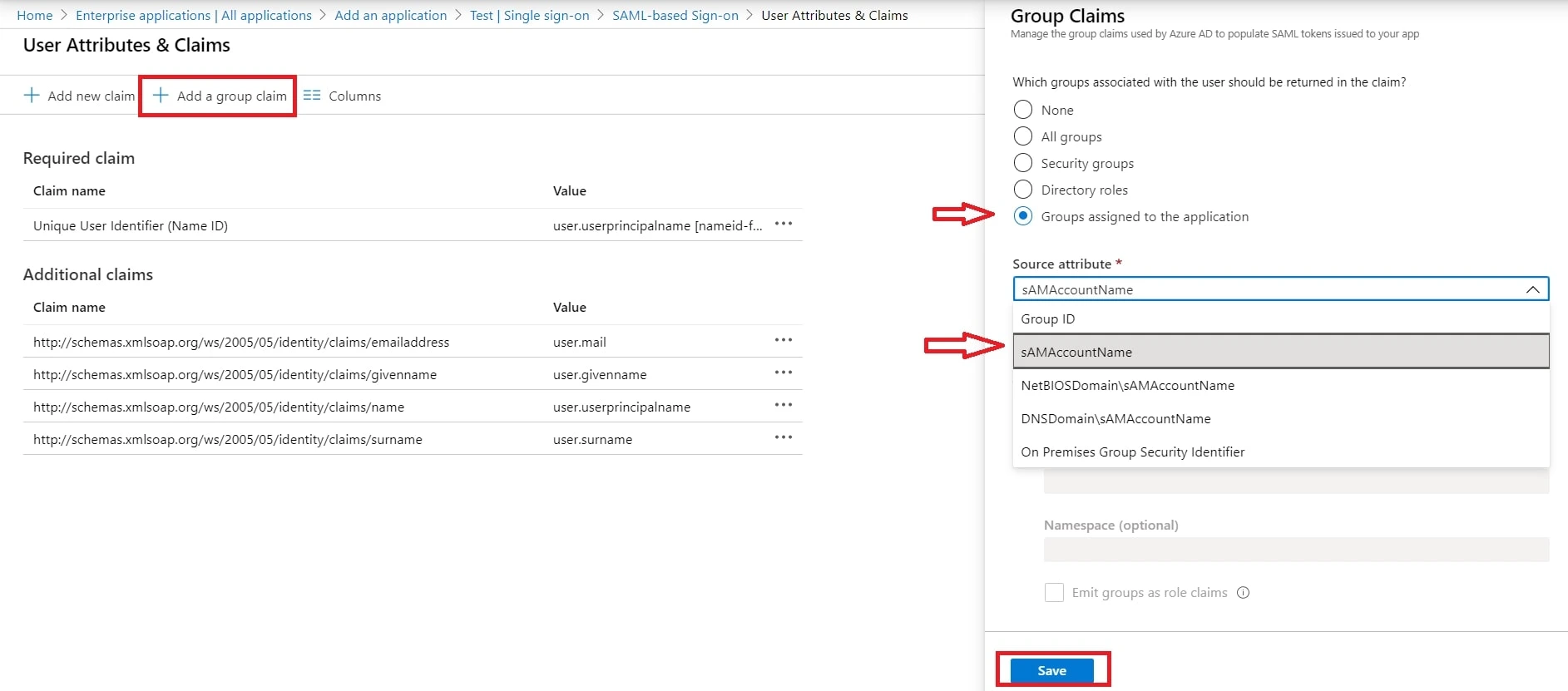
- By default, the following Attributes will be sent in the SAML token. You can view or edit the claims sent in the SAML token to the application under the User Attributes & Claims tab.
- You can add attribute using Add new claim
- You can add group attribute claim using Add a group claim
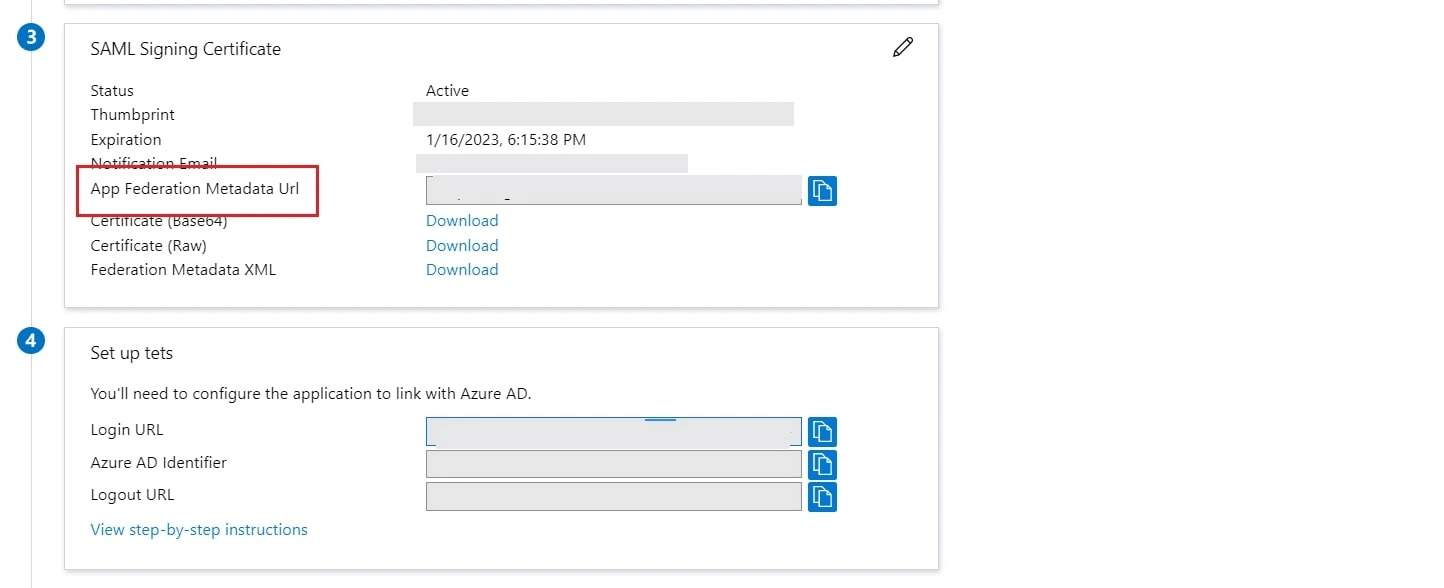
- Copy App Federation Metadata Url from setup tab.
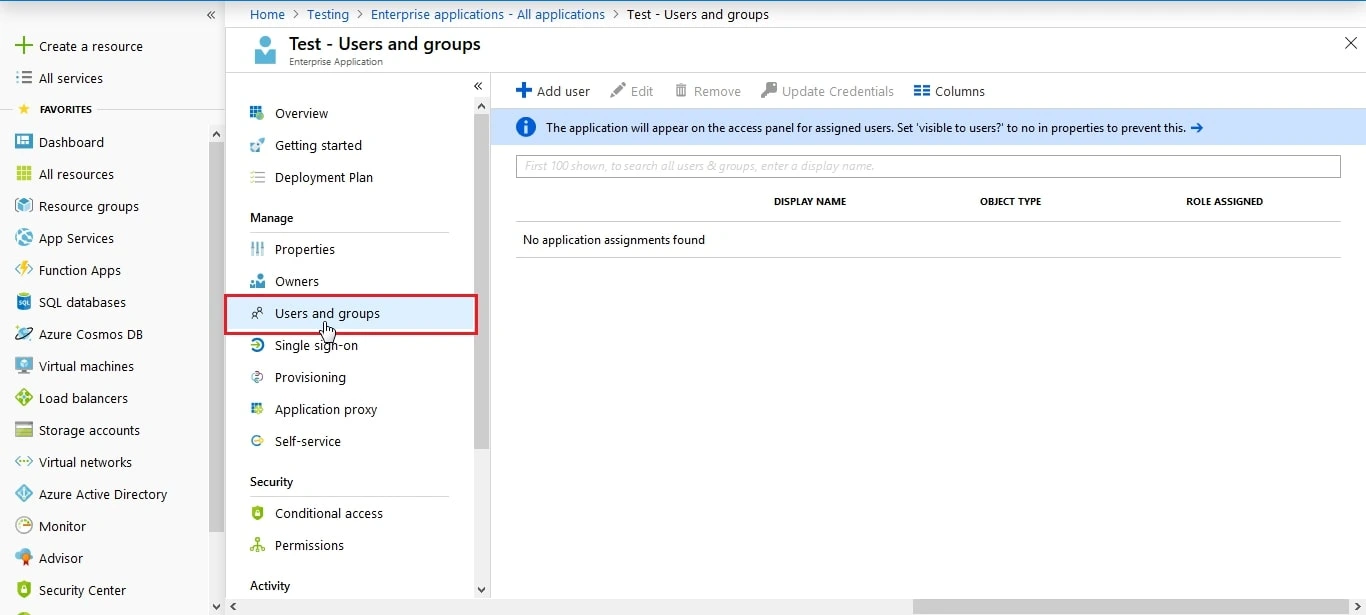
- Click on User and groups from the applications left-hand navigation menu. The next screen presents the options for assigning the users/groups to the application.
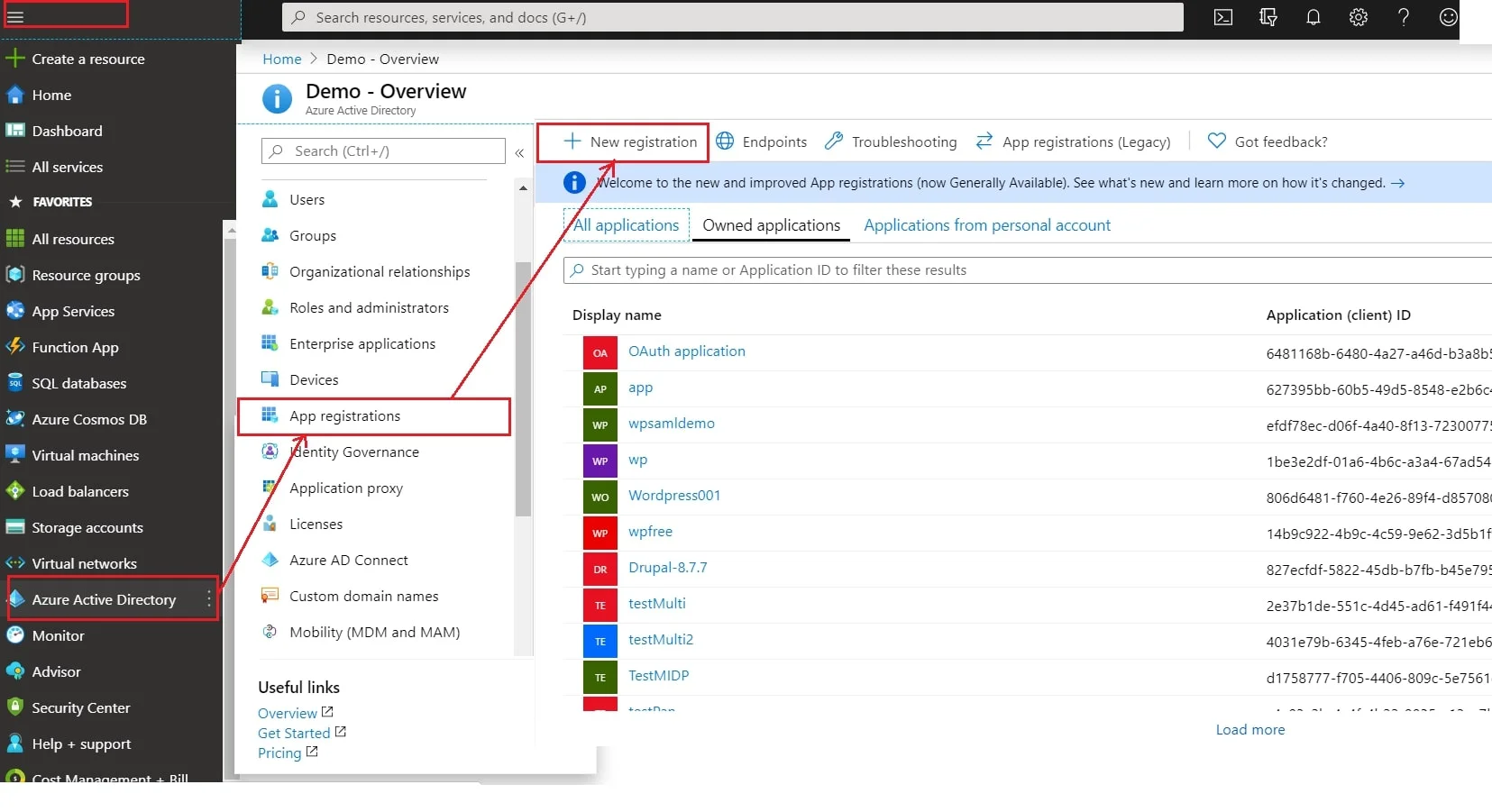
- Log in to Microsoft Entra ID (Previously known as Azure AD) Portal
- Select ⇒ Azure Active Directory ⇒ App Registrations. Click on New Application Registration.
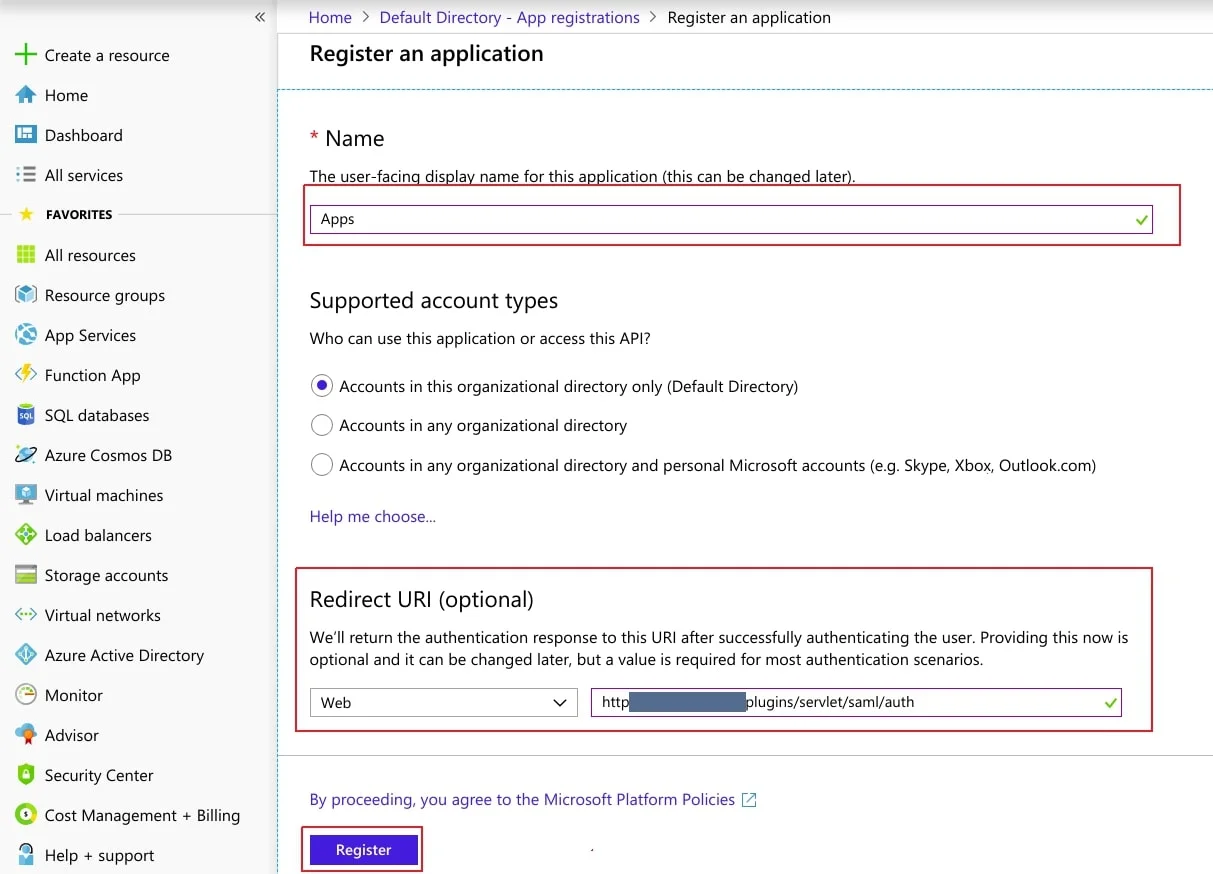
- Assign a Name and choose the account type. In the Redirect URI field, provide the ACS URL provided in Service Provider Info tab of the plugin and click on Register button.
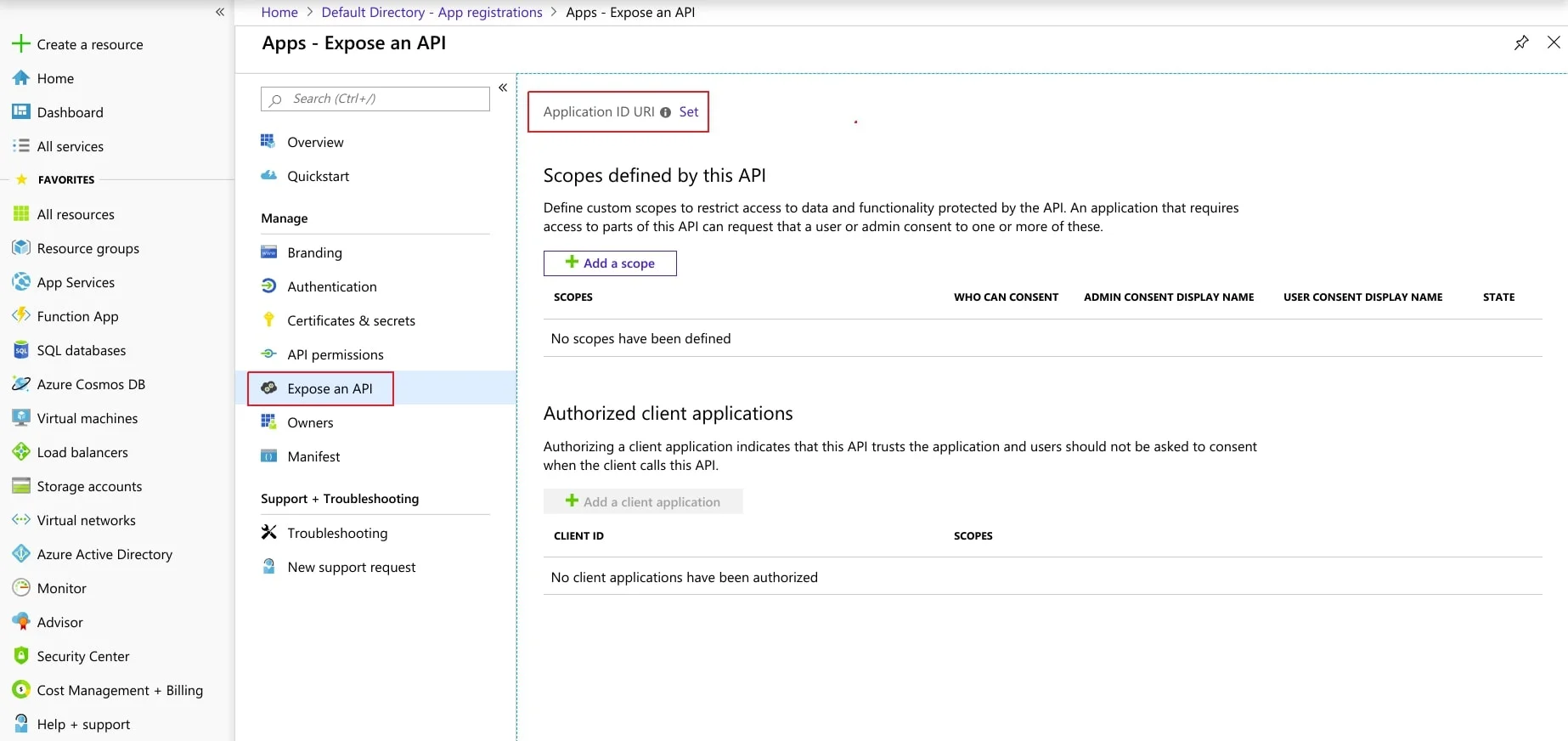
- Now, navigate to Expose an API menu option and click the Set button and replace the APPLICATION ID URI with the plugin's SP Entity ID
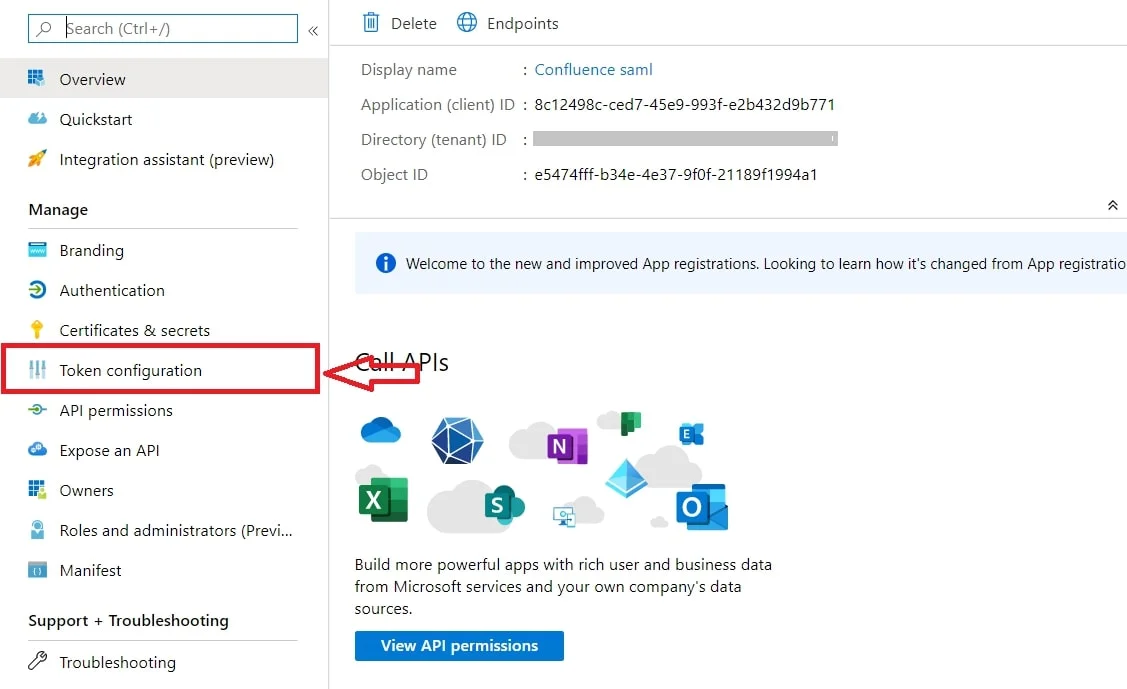
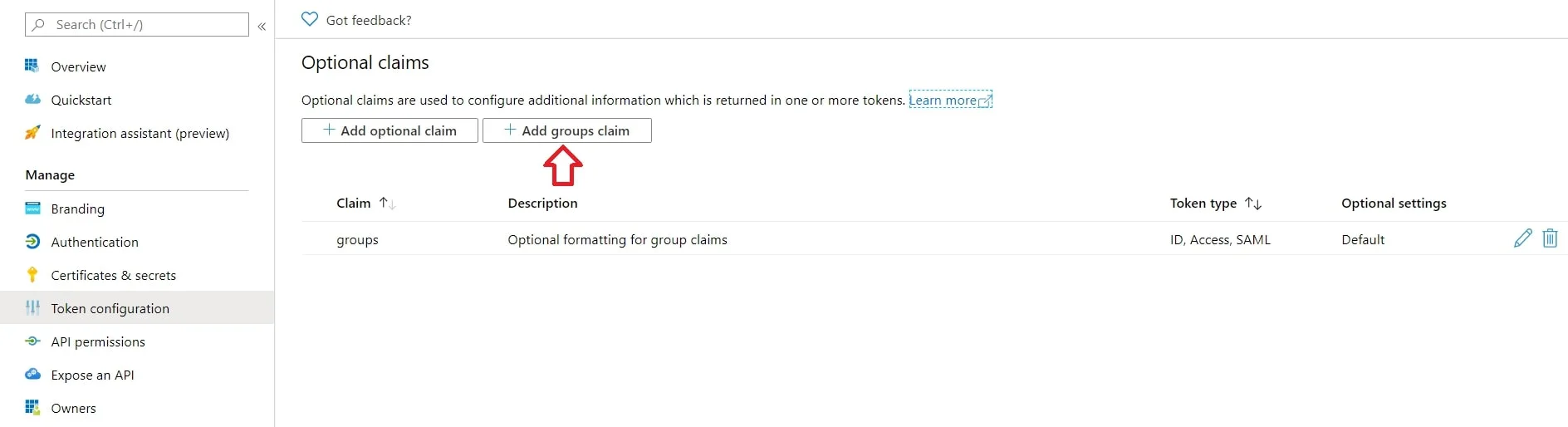
- By default, some Attributes will be sent in the SAML token. If you're not getting group information. Then, add Token configuration for Group information.
- Click on Add groups claim
- Copy the Federation Metadata URL given below. Replace the '{tenant_ID}' part with your
Directory/Tenant ID. This will be required while configuring the SAML plugin.
Federation Metadata URL https://login.microsoftonline.com/{tenant_ID}/federationmetadata/2007-06/federationmetadata.xml
Step 2: Setup Confluence as Service provider
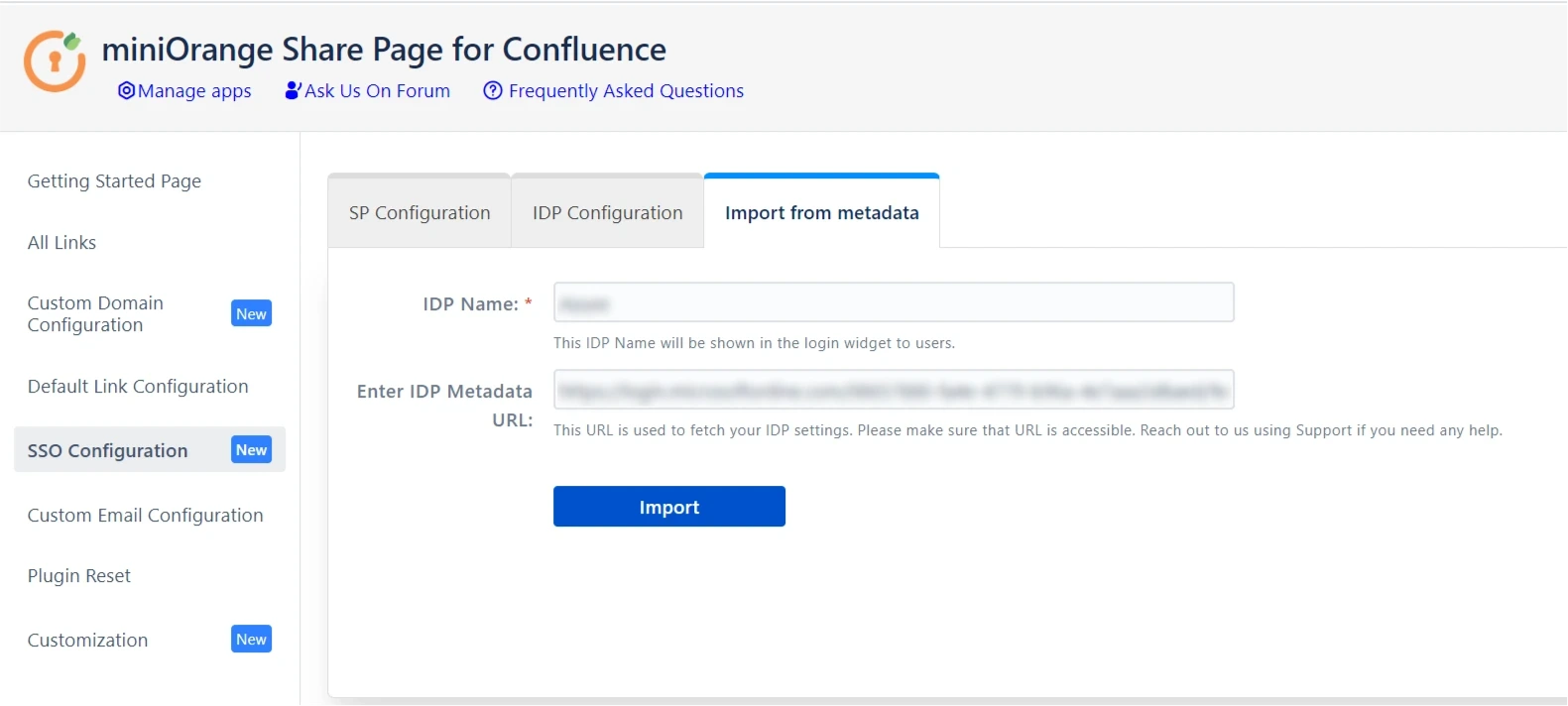
- Click on Import from the Metadata tab.
- Enter IDP name and metadata URL copied from IDP
- Click Import
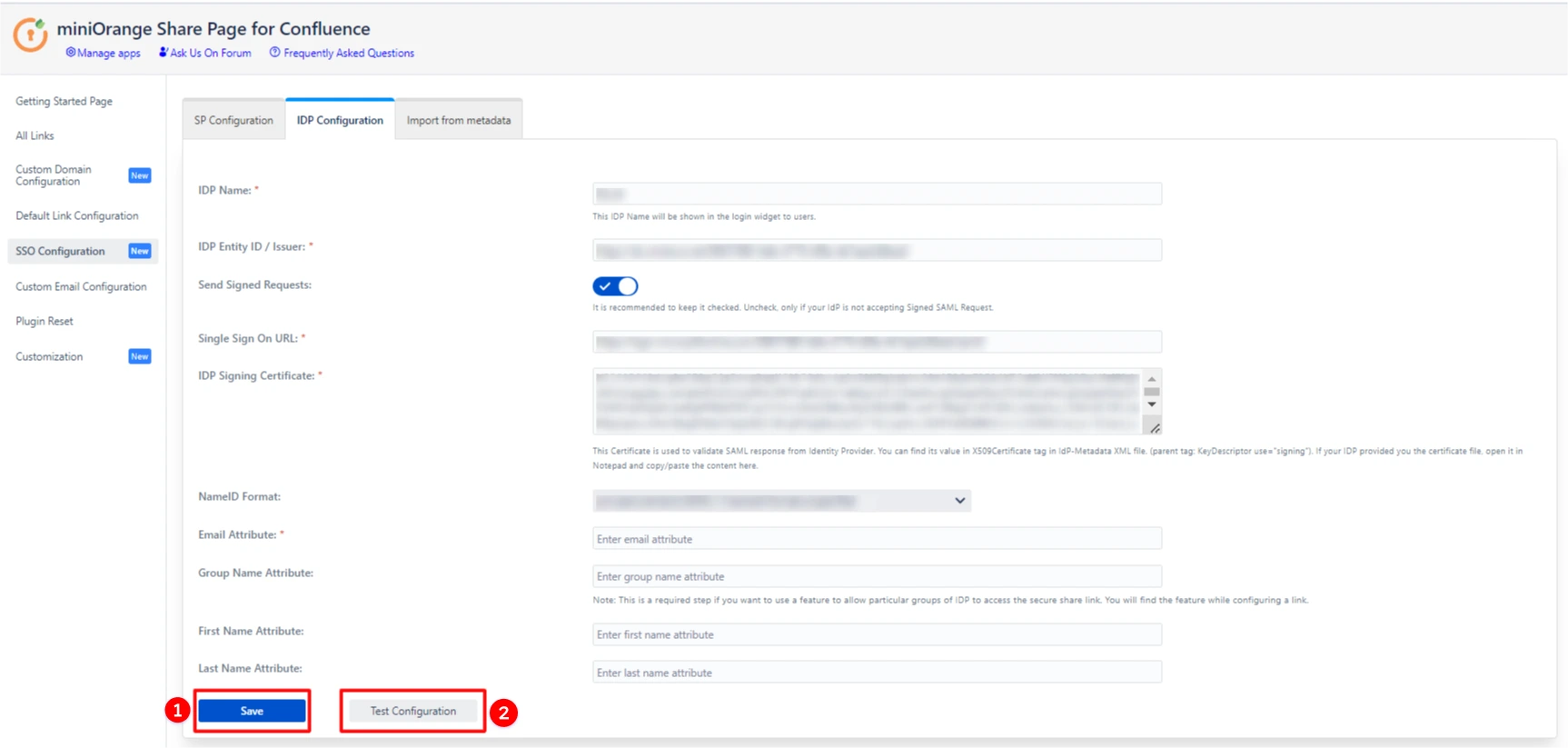
- To configure the IDP manually, you will need to have the following details from your IDP's metadata.
- IDP Entity ID
- Single Sign On URL
- X.509 Certificate
- Once you have added the IDP metadata, click on Save. If the IDP has been added successfully, Click on the Test Configuration button to test if the IDP was added successfully.
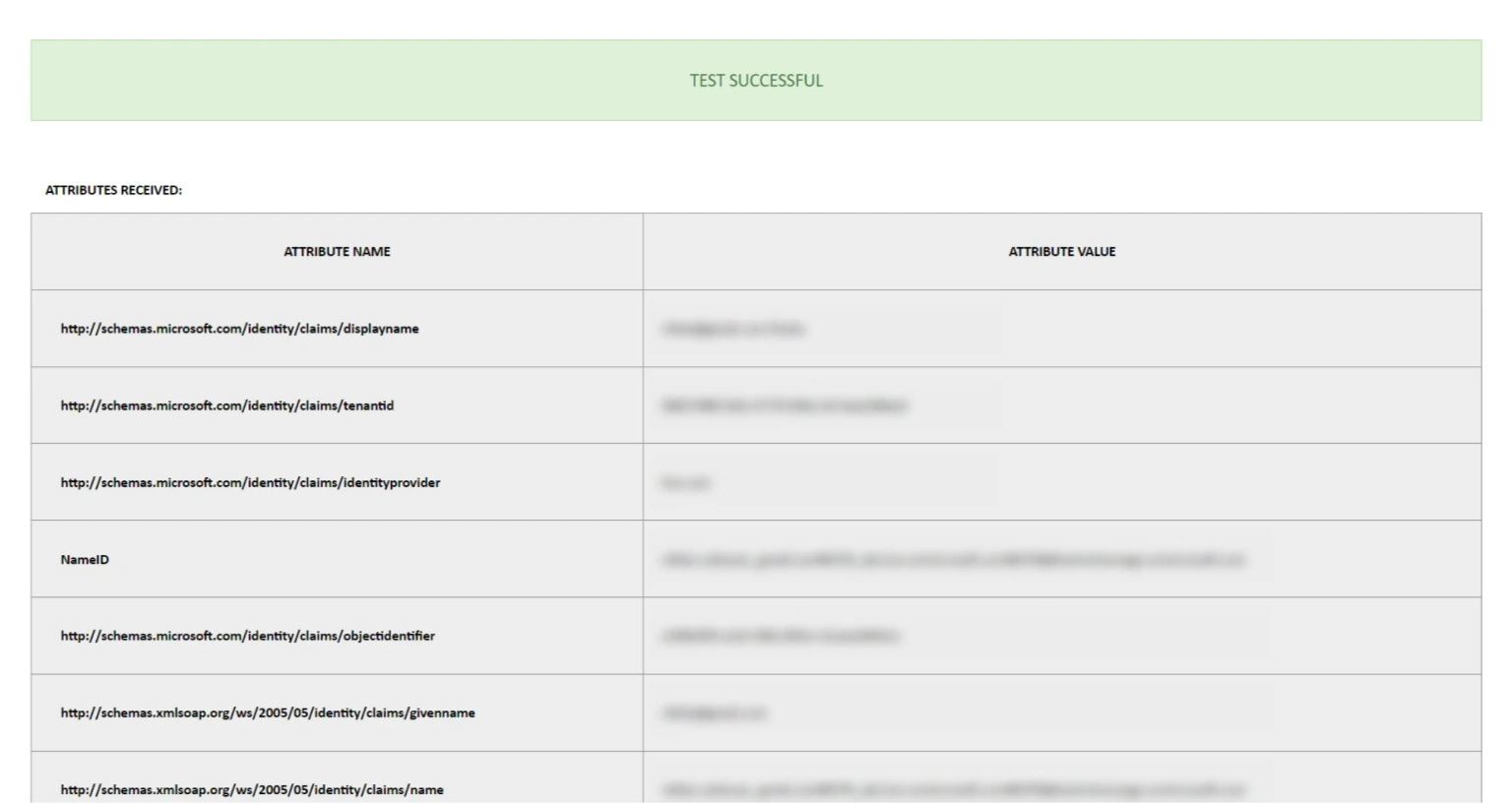
- You will see all the values returned by your IDP to Confluence in a table. If you don't see value for First Name, Last Name and Email, make the required settings in your IDP to return this information.
- Note : Setting up an email attribute is a must to access the Confluence Secure Share link.
- If the test configuration is failed, please verify the IDP metadata details in the IDP Configuration tab.
A. By Metadata URL :
B. Manual Configuration :
If you are having trouble configuring the SSO, please contact us at support-atlassian@miniorange.atlassian.net or raise a support ticket here.
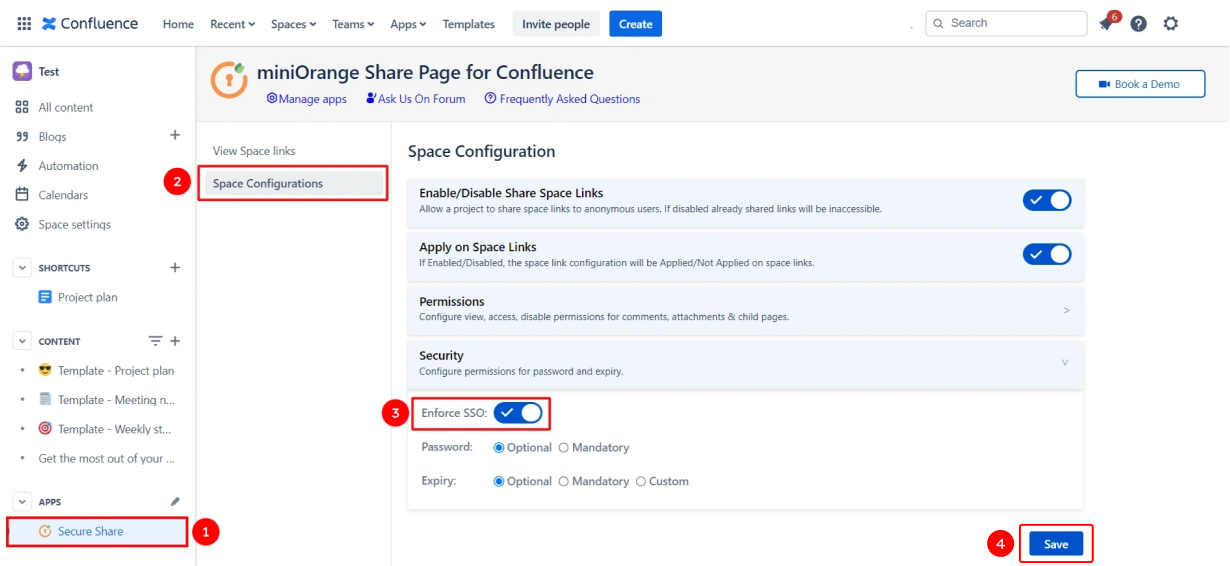
Step 3: Enable SSO for your Confluence Space
- Using our plugin you can enforce SSO on the specific Confluence spaces. To enable the SSO for secure share links of a particular space, go to the space and then select Secure Share from the sidebar.
- Now you can create and share Confluence page/space links to external users with an extra security layer.
- To learn more about creating and configuring a shared link please refer this page - Share Confluence with External Users
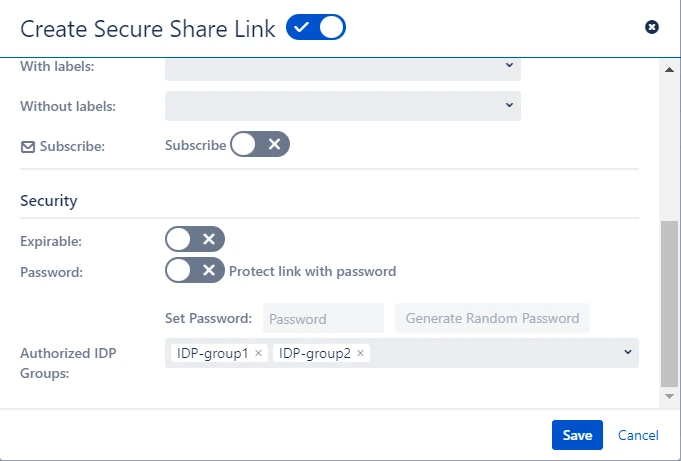
Step 4: Authorize link access based on Identity Provider groups (Optional)
- Prerequisite: You must configure the group attribute in the SSO Configuration tab to use this feature.
- Refer these steps to find the SSO Configuration tab.
- Just like we found an email Attribute previously, we will find a group attribute.
- Go to the IDP Configuration tab. Scroll down and click on Test Configuration.
- You will see all the values returned by your IDP in a table. If you don't see value with groups, make the required settings in your IDP to return group names.
- Once you see all the values in Test Configuration, keep the window open and go to the IDP Configuration tab again.
- Enter the Attribute Name of a group against Group Name Attribute.
- Go to the link configuration of the existing link or create a new Confluence link.
- Enter the names of the groups to which you would like to grant access.
- That’s it! Now only those users will be able to access the link who are members of the IDP-group1 and IDP-group2.
Finding Group Attribute
To control the link access to specific groups:
Recommended Add-Ons

Jira Secure Share (Cloud)
Create & share secure links for Jira issues allowing end-user to access the issue without login.
Know More
Confluence OAuth SSO (Cloud)
OAuth/OpenID Connect (OIDC) Single Sign On(SSO) allows users to login into Jira and Confluence with OAuth 2.0 and OpenID compliant applications
Know More
SAML/OAuth SSO for JSM Customers
External customers can now log in via SSO to your Jira Service Management portals with our exclusive solution, SAML/OAuth SSO for JSM Customers.
Know MoreBitbucket Git Authentication App | Kerberos/NTLM Apps | Word/PDF Exporter | WebAuthn | SonarQube SSO | Jenkins SSO
If you don't find what you are looking for, please contact us at support-atlassian@miniorange.atlassian.net or raise a support ticket here.
