REST API Authentication On Atlassian using Okta as OAuth Provider
Enhance API Security for Jira REST APIs with OAuth/API Token plugin will let you authenticate any application (Jira, Confluence, Bitbucket) APIs using any third-party OAuth/OIDC provider or API Tokens. The app supports Azure AD, Keycloak, Okta, AWS Cognito, Google, Github, Slack, Gitlab, Facebook, and any custom provider.
Atlassian provides REST APIs to perform several operations such as Create Page, Delete Page, Add Comment, Create Space, etc. However, it supports only two authentication methods for REST APIs:
1. Basic Authentication
2. Using OAuth 1.0
Video Setup Guide
Download and Installation
- Log into your Atlassian instance as an admin.
- Navigate to the settings menu and click Manage Apps.
- Click Find new apps or Find new add-ons from the left-hand side of the page.
- Locate Enhance API Security for Jira REST APIs with OAuth/API Token app.
- Click Try free to begin a new trial or Buy now to purchase a license.
- Enter your information and click Generate license when redirected to MyAtlassian.
- Click Apply license.
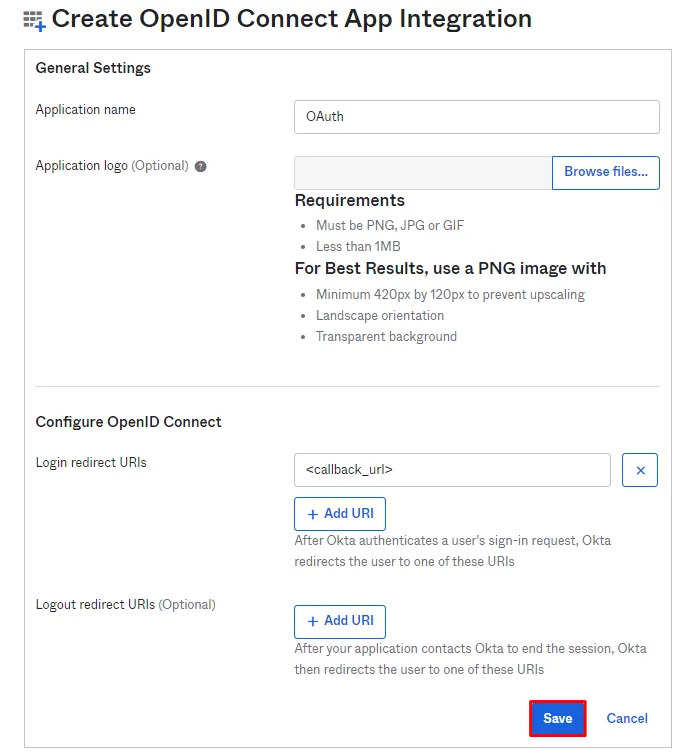
Step 1: Configure Okta server:
- First of all, go to https://www.okta.com/login and log into your Okta account.
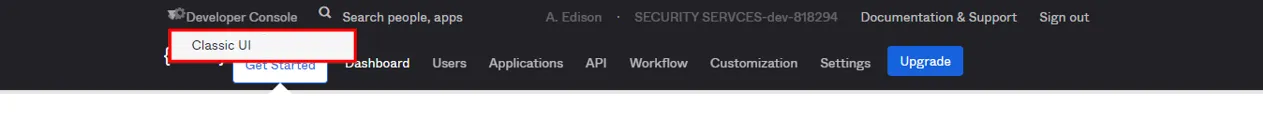
- Switch to Classic UI to configure app.
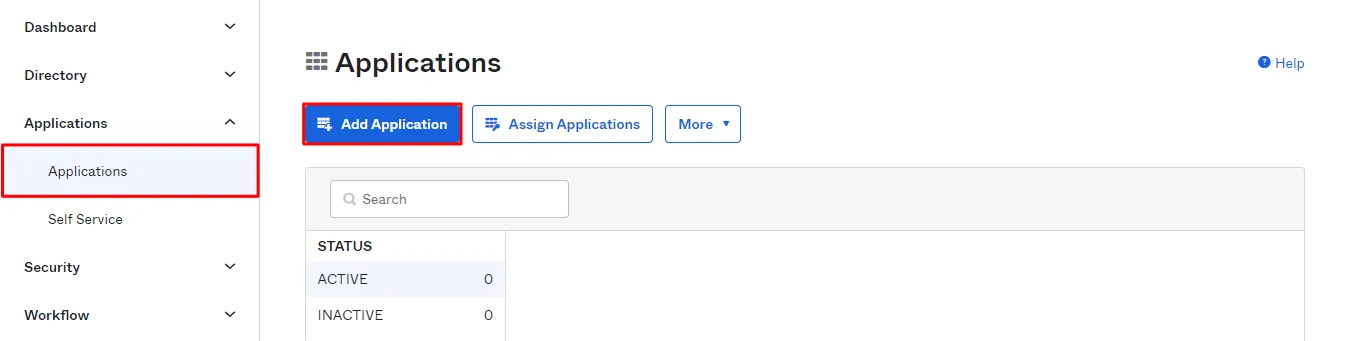
- Go to the Applications from the left menu and then click on Add Application button and select Create New App.
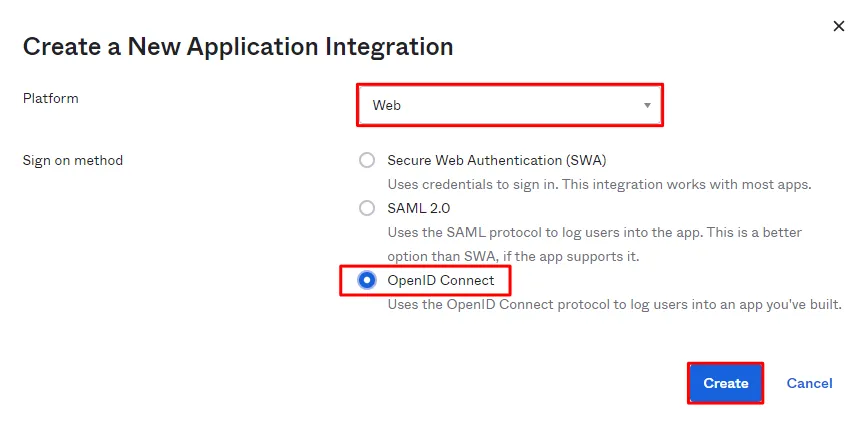
- Choose Web as platform, OpenID Connect as Sign on method, and click on Create.
- You will be redirected to the app details page. Enter Application name and Login Redirect URIs. Copy Callback URL from the plugin . Click on Save.
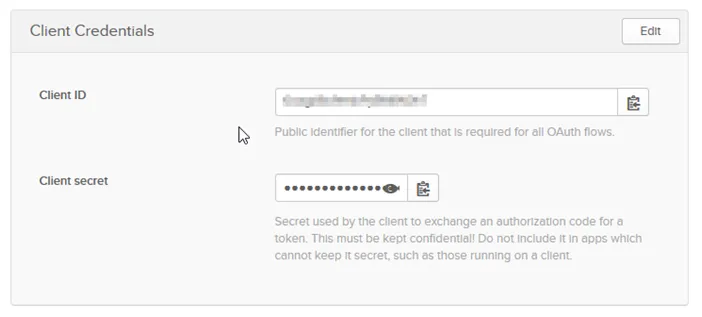
- You will be brought to App details page. Scroll down to Client Credentials section.
Step 2: Fetch Access token through POSTMAN:
- Open the Postman Application (Here is the link to download Postman Application).
- Go to Authorization tab.
- From the dropdown select type as OAuth 2.0 and click on Get access token.
- Add the following information from the table below.
- Postman starts the authentication flow and prompts you to use the access token.
- Select Add token to the header.
- Copy the Access Token or click on Use Token.
- A sample access token from Okta Provider looks like this.
| Grant type | Authorization Code or Client Credentials |
| Callback URL | Enter the Application's base URL if you dont have a callback URL |
| Auth URL | https://<Domain_Name>/oauth2/default/v1/authorize |
| Access token URL | https://<Domain_Name>/oauth2/default/v1/token |
| Client ID | Enter the Okta Client ID |
| Client secret | Enter the Okta Client secret |
| Scope | openid profile email |
| State | Random String |
| Client Authentication | Send client credentials in the body |
A834c0606ba71336423013699db8e971
Step 3: Fetch Username through Okta:
- Choose the method type as "GET".
- Enter the interoception Endpoint from the plugin to fetch the username in the Request URL. For Okta it is "https://{Domain_Name}/oauth2/default/v1/userinfo".
- Go to the Authorization tab select the Bearer Token and enter the access token here.
- Add the header "content-type: application/json" and click on Send.
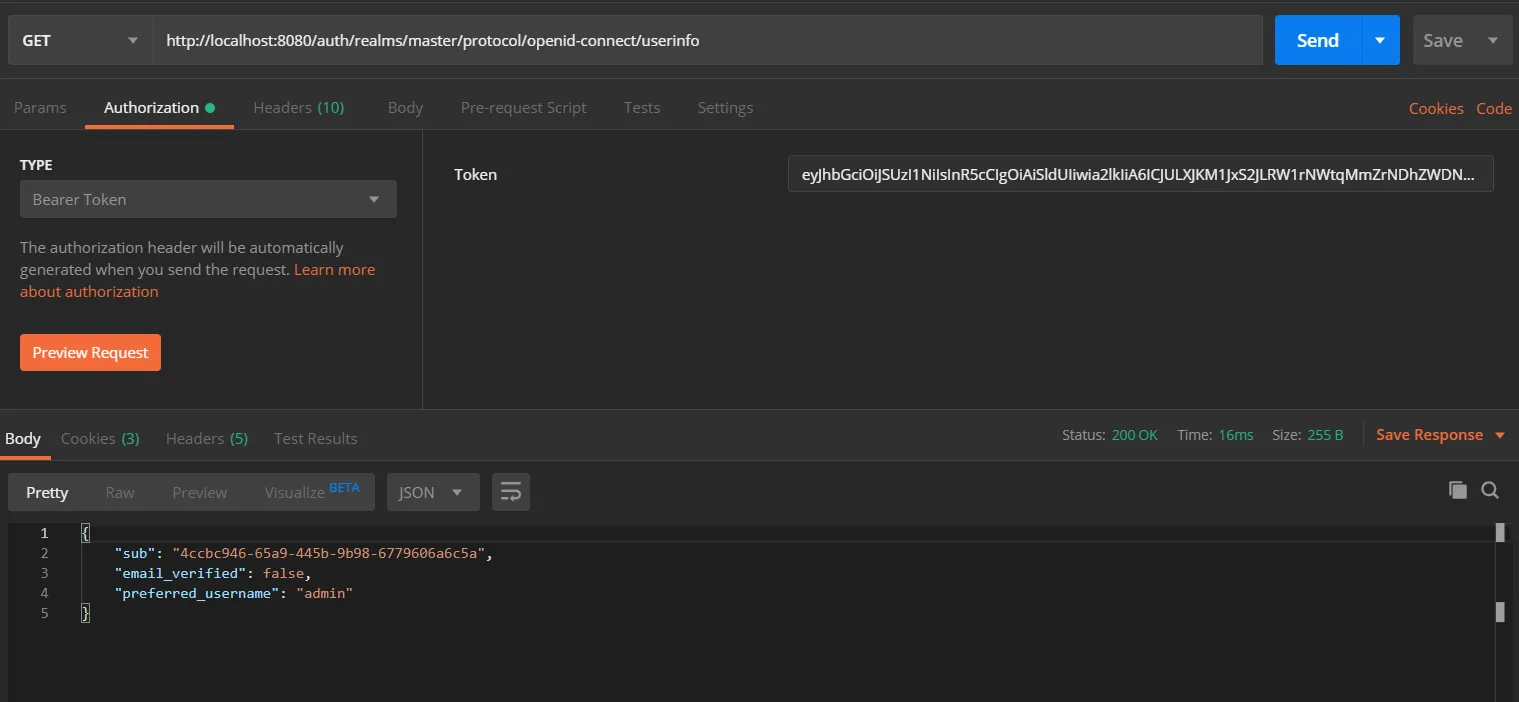
Request:
curl
-X GET
-H "Authorization: Bearer <Access Token>"
-H "Content-type: application/json"
https://{Domain_Name}/oauth2/default/v1/userinfo
Copy the attribute value against the username, you will need to configure it in plugin. In this example, the value is "preferred_username".
Step 4: Configure the Rest API plugin:
1: Enable Rest API Authentication:
- After installing the app, click on Configure to configure plugin.
- Select the Authentication type and navigate to Oauth/OIDC tab, then click on Configure.
- From the drop down select Okta as OAuth Provider.
- Enter the Domain Name from Okta.
- Enter the attribute value against which we received the username in the Postman response.
- Save the settings.
- Now navigate to the Global Settings tab.
- Here you will have to Enable the Authentication through Enable REST API Authentication and click on Save.
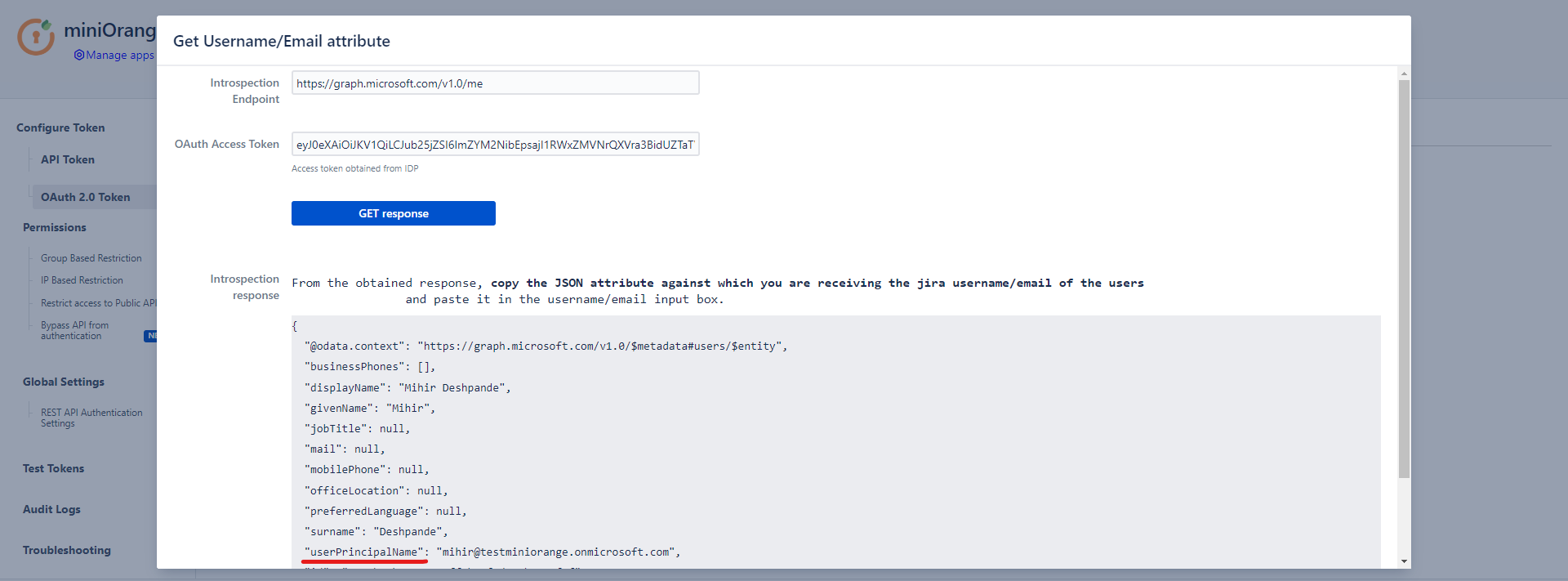
- To configure the username attribute, click on Get username/email Attribute button.
- Paste the OAuth 2.0 Access token obtained from the OAuth provider and click on Get response.
- In the received response, copy the JSON attribute against which you are receiving the username/email of the user in the local directory and paste it into the Username/Email Attribute input field, and click on Save.
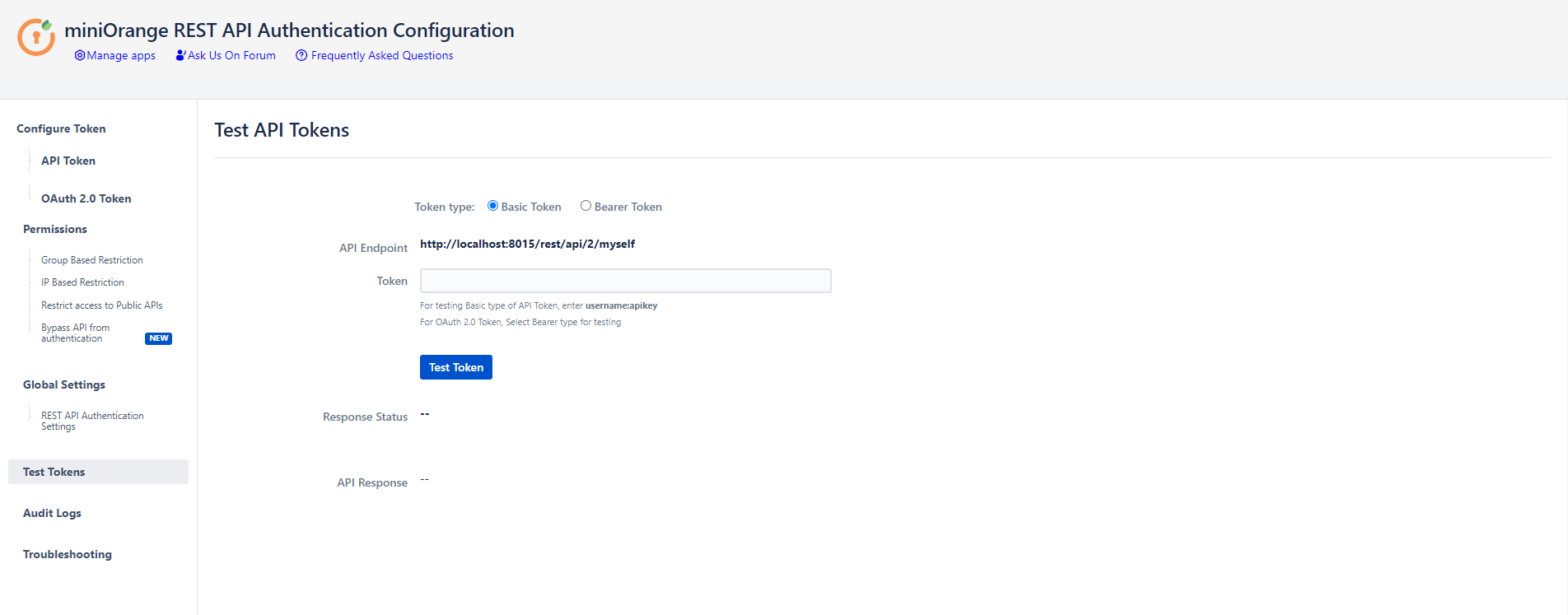
Step 5: Test REST API using access token:
- API keys and Tokens can be tested with the Test tokens feature. Select the type - Basic/Bearer, paste the token and click on Test token button.
Click here to get a FREE TRIAL of Confluence REST API Plugin
- Call Confluence REST API endpoint. Include the access token in the Authorization header. Here’s an example of fetching content from Confluence.
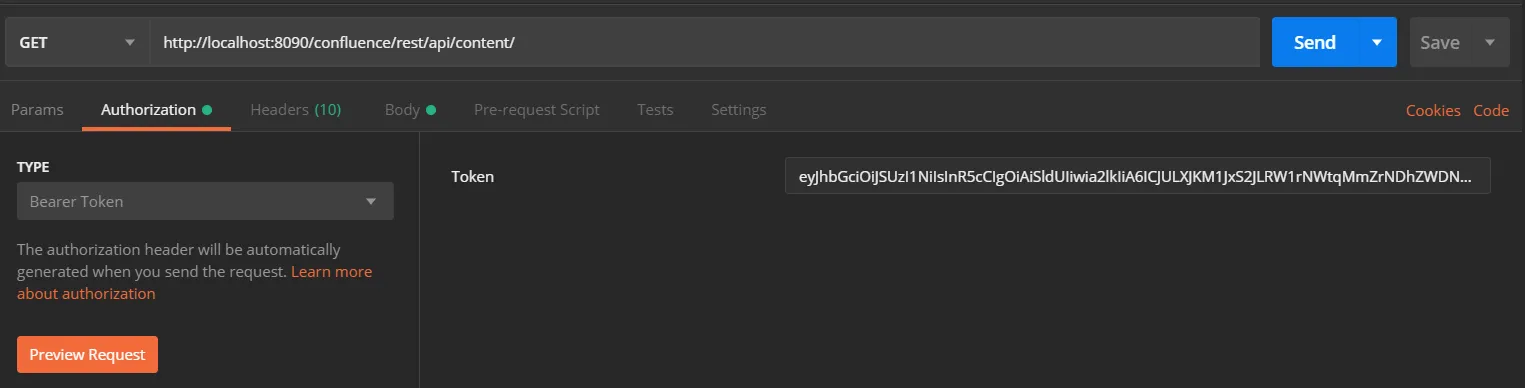
- Go to the Postman application select method type as GET and enter the Request URL. For eg. http://{Confluence_Base_URL}/confluence/rest/api/content/
- In the Authorization tab select type as Bearer Token.
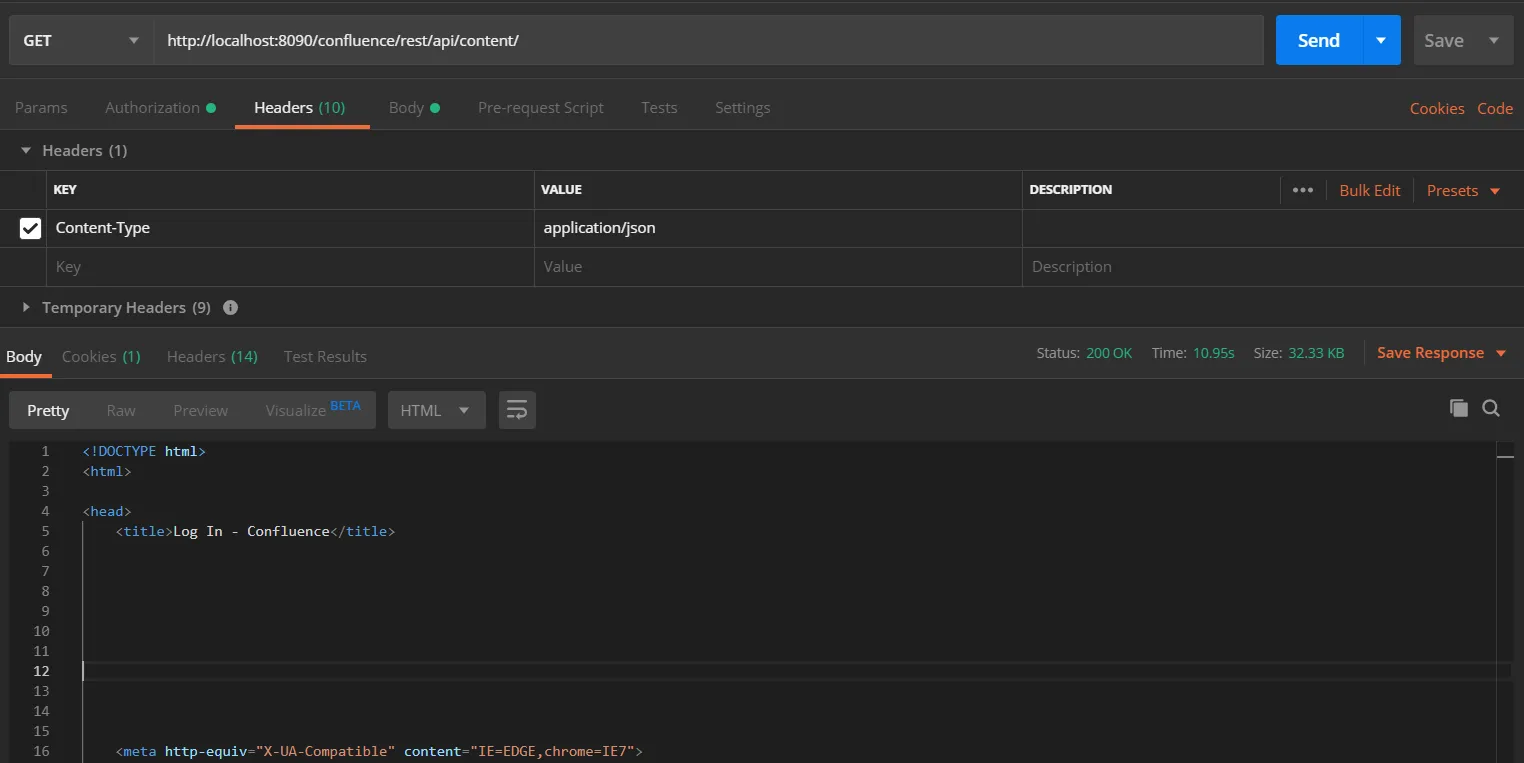
Request:
curl
-X GET
-H "Authorization: Bearer <Access Token>"
-H "Content-type: application/json"
http://{confluence_base_url}/confluence/rest/api/content/
Click here to get a FREE TRIAL of Bitbucket REST API Plugin
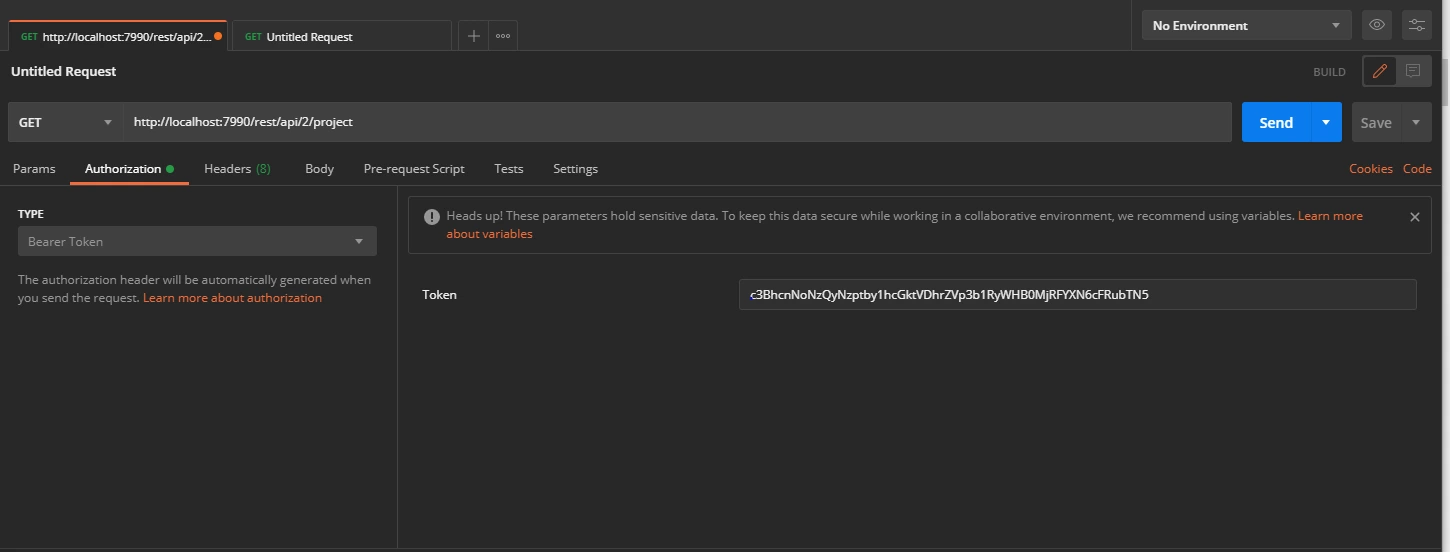
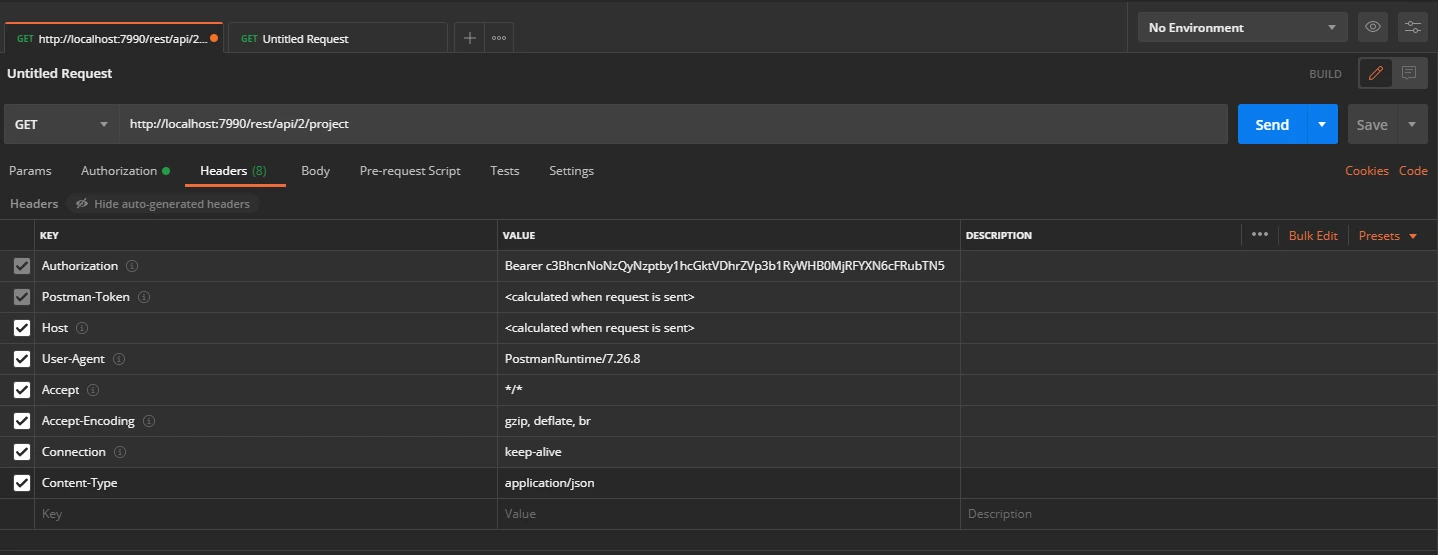
- Call Bitbucket REST API endpoint. Include the access token in the Authorization header. Here’s an example of fetching content from Bitbucket.
- Go to the Postman application select method type as GET and enter the Request URL. For eg. http://{Bitbucket_Base_URL}/rest/api/1.0/dashboard/pull-requests
- In the Authorization tab select type as Bearer Token.
- In the Header tab add the header “content-type: application/json and send the request.
Request:
curl
-X GET
-H "Authorization: Bearer <Access Token>"
-H "Content-type: application/json"
http://{bitbucket_base_url}/rest/api/1.0/dashboard/pull-requests/
Additional Resources
Did this page help you?

 Try it for free
Try it for free