SAML SSO for JSM Customers using SimpleSAML as IDP
You can now allow External Customers to log in via SSO into Jira Service Management (previously Jira Service Desk or JSD). Integrate various customer portals like Atlassian Service Management and access tickets with the help of SAML SSO for JSM Customers.
Download and Installation
- Log into your Jira instance as an admin.
- Navigate to the settings and Click on Apps.
- Locate SAML/OAuth SSO for JSM Customers.
- Click on free trial to begin a new trial SAML/OAuth SSO for JSM Customers.
- On menu bar click on Apps. Locate SAML/OAuth SSO for JSM Customers.
Step 1: Set Up SimpleSAML as Identity Provider
- In config/config.php, make sure that 'enable.saml20-idp' is true. Example: ‘enable.saml20-idp’ => true
- In metadata/saml20-idp-hosted.php, configure SimpleSAML as an Identity Provider by adding code below:
$metadata['__DYNAMIC:1__'] = array(
'host' => '__DEFAULT__',
/* X.509 key and certificate. Relative to the cert directory.*/
'privatekey' => '<YOUR_PRIVATE_KEY_FILE_NAME>',
//eg. RSA_Private_Key.pem 'certificate' => '<YOUR_PUBLIC_KEY_FILE_NAME>',
//eg. RSA_Public_Key.cer
/* Authentication source to use. Configured in 'config/authsources.php'. */
'auth' => '<YOUR_AUTH_SOURCE_NAME>',
);
- In metadata/saml20-sp-remote.php, register your Servider Provider like this:
/* Replace example.com with your atlassian domain name. */$metadata['https://example.com/plugins/servlet/saml/metadata'] = array(
'AssertionConsumerService' => 'https://example.com/',
'SingleLogoutService' => 'https://example.com/',
'NameIDFormat' => 'urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress',
'simplesaml.nameidattribute' => 'mail',
'simplesaml.attributes' => true,
'attributes' => array('mail', 'givenname', 'sn', 'memberOf'),
);
Step 2: Setup JSM as Service provider
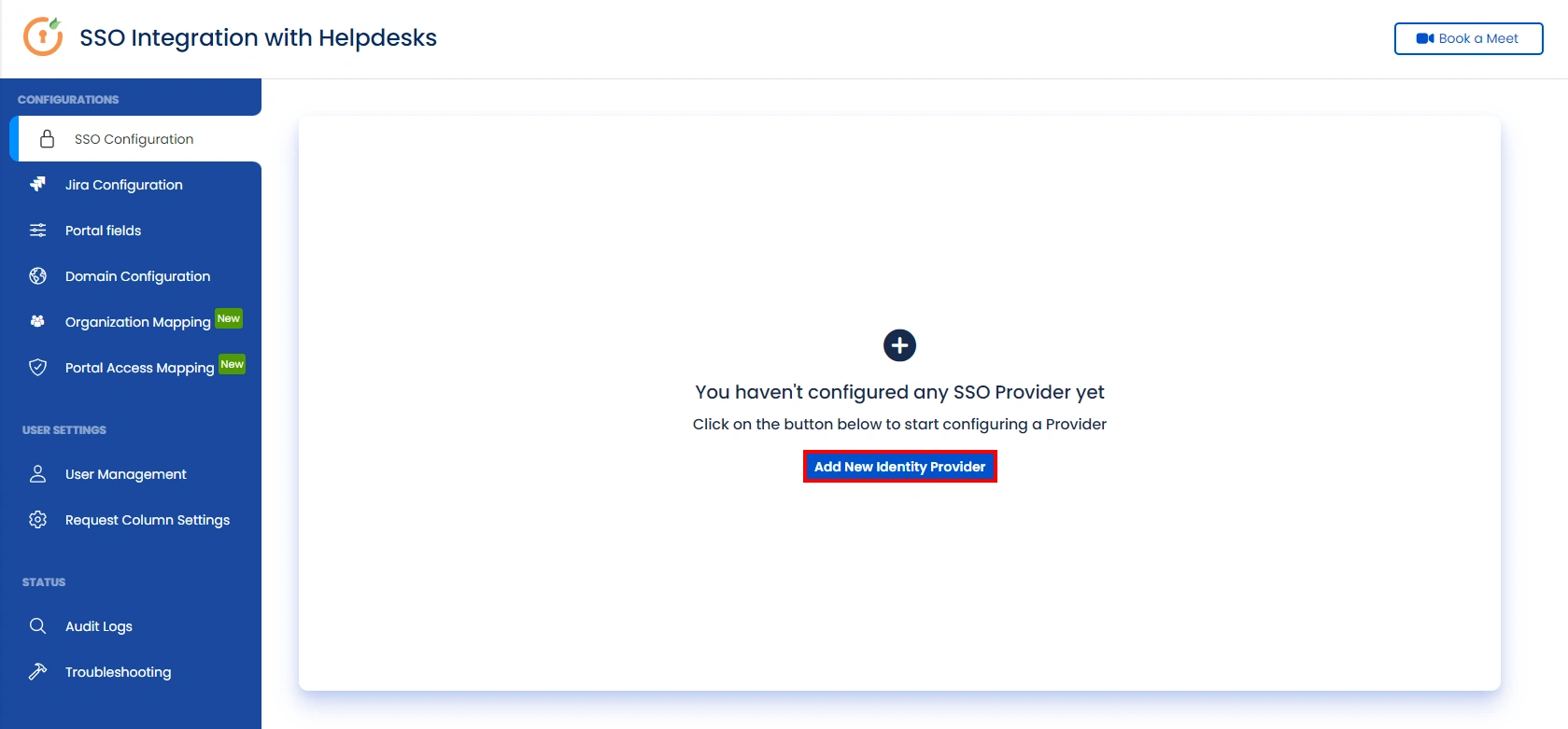
- Go to the Manage Apps -> click Getting started under SSO Integration with Helpdesk then click on the Add New Identity Provider.
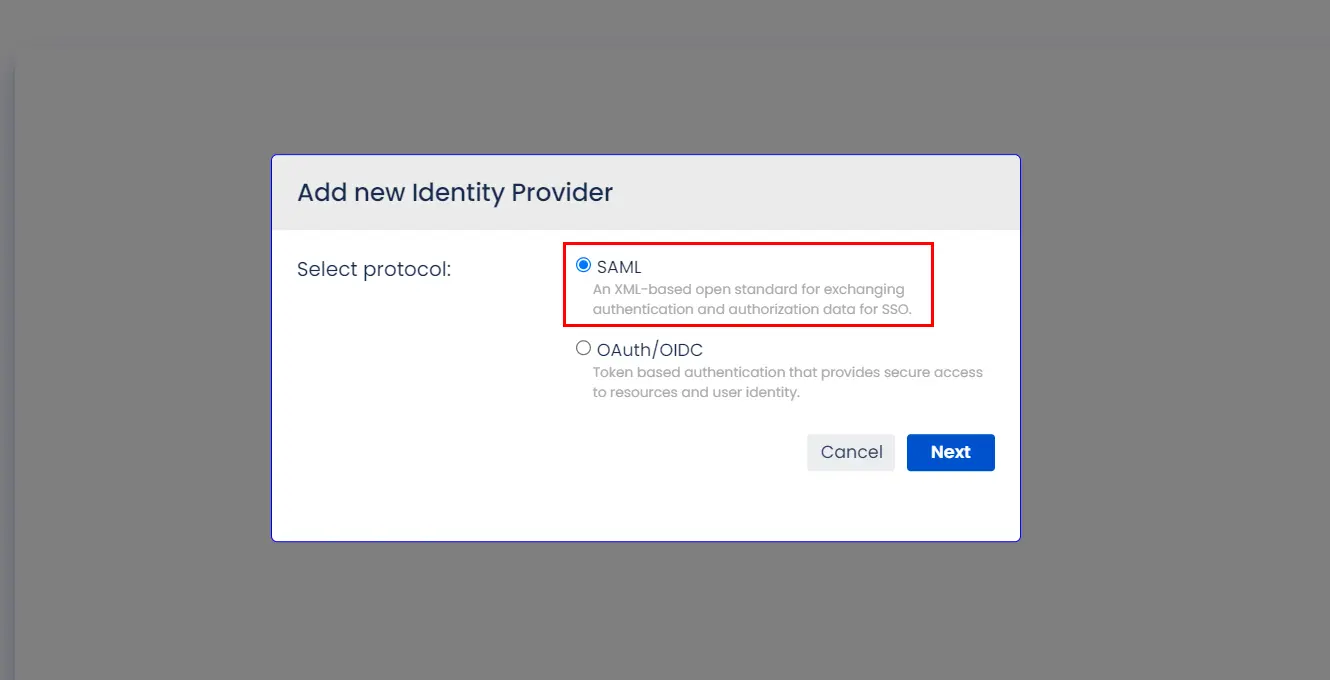
- Select SAML and click on the next button.
- Click on Import IDP Metadata.
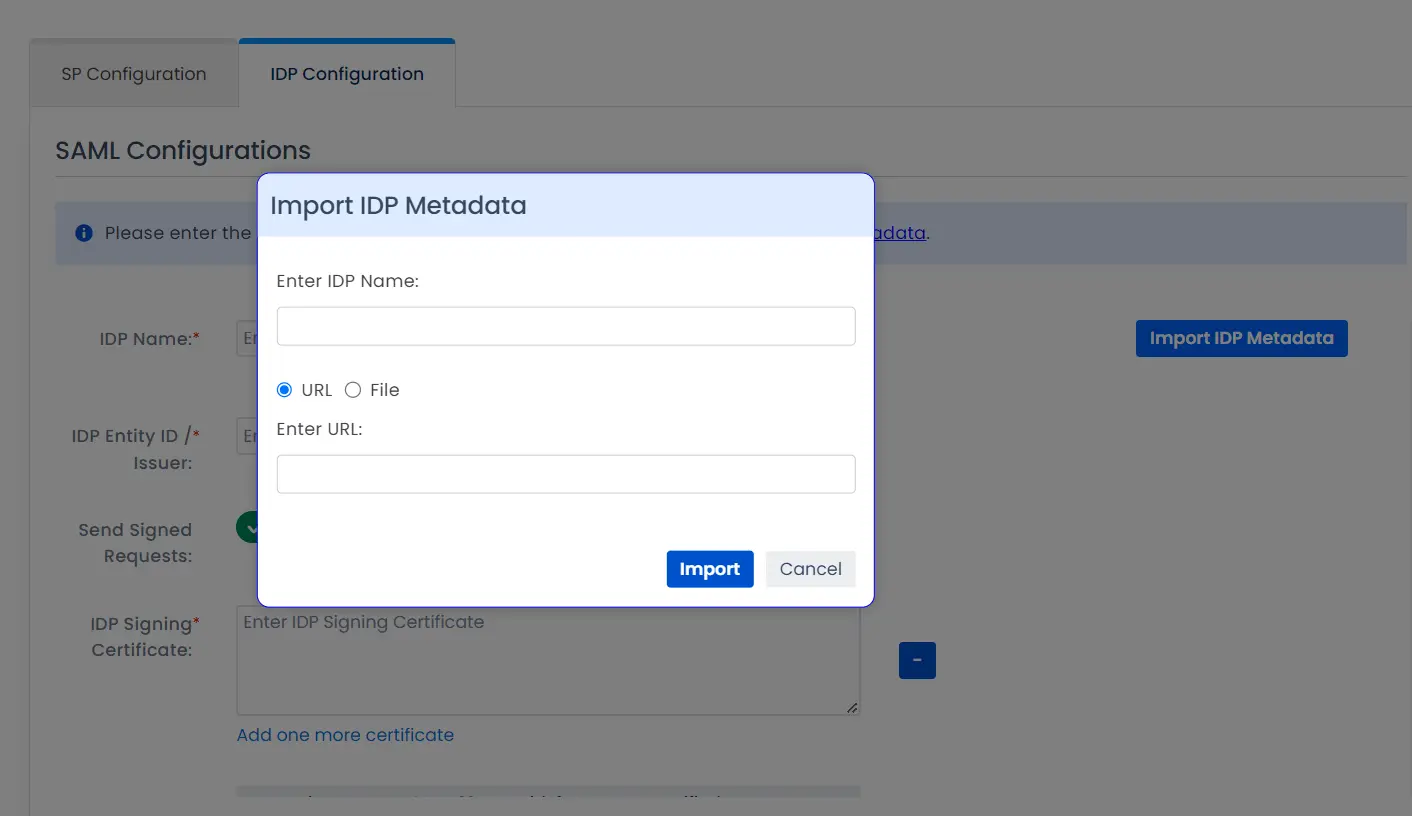
- Enter IDP name.
- Choose IDP metadata URL / File: Enter your metadata URL / File
- Click Import
A. By Metadata URL :
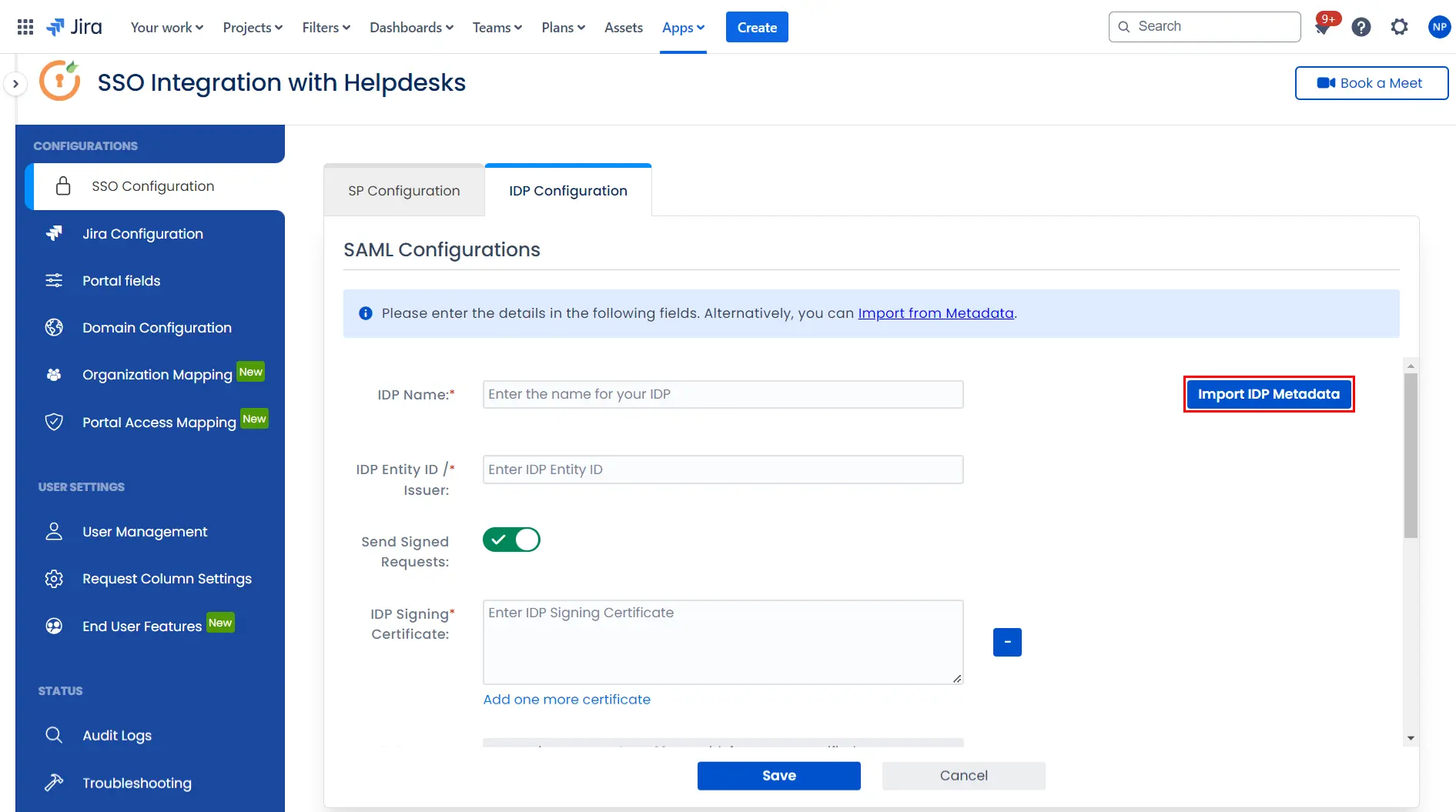
To configure the IDP manually, you will need to have the following details from your IDP's metadata.
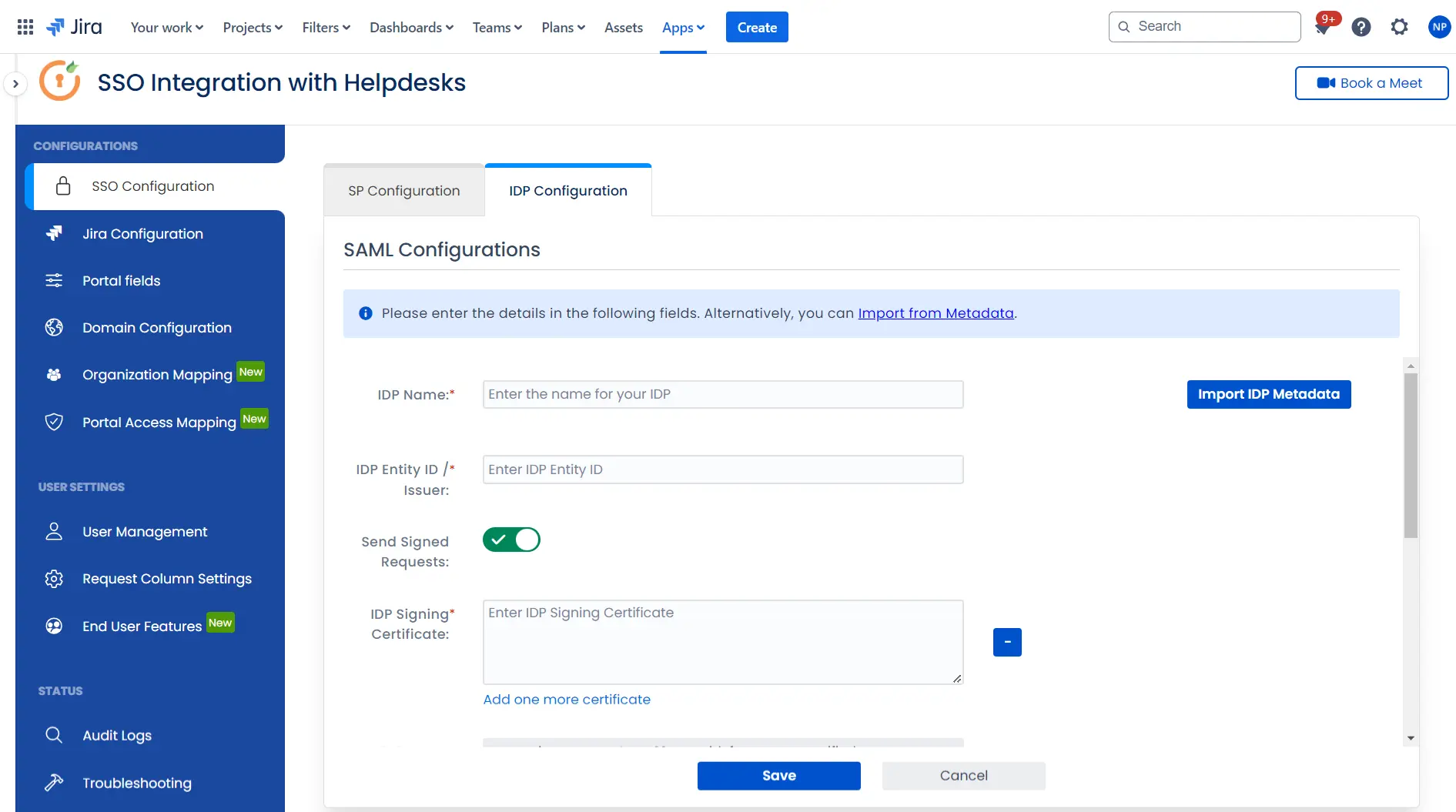
Once you have added the IDP metadata, click on Save. If the IDP has been added successfully, Click on the Test Configuration button to test if the IDP was added successfully.
Step 3: Integrate Atlassian HelpDesk with JSM SSO
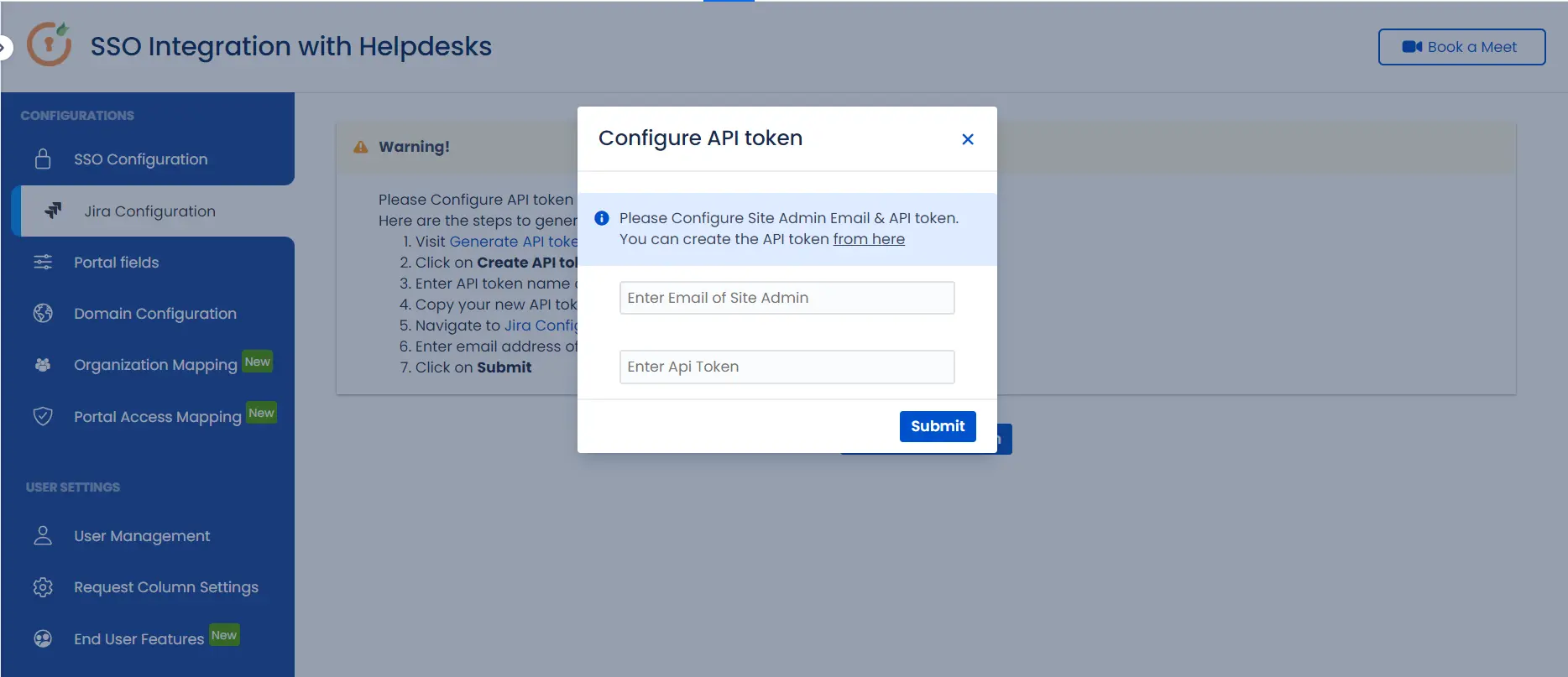
- Click on the Configure API Token and configure the Service Account API token with the email.
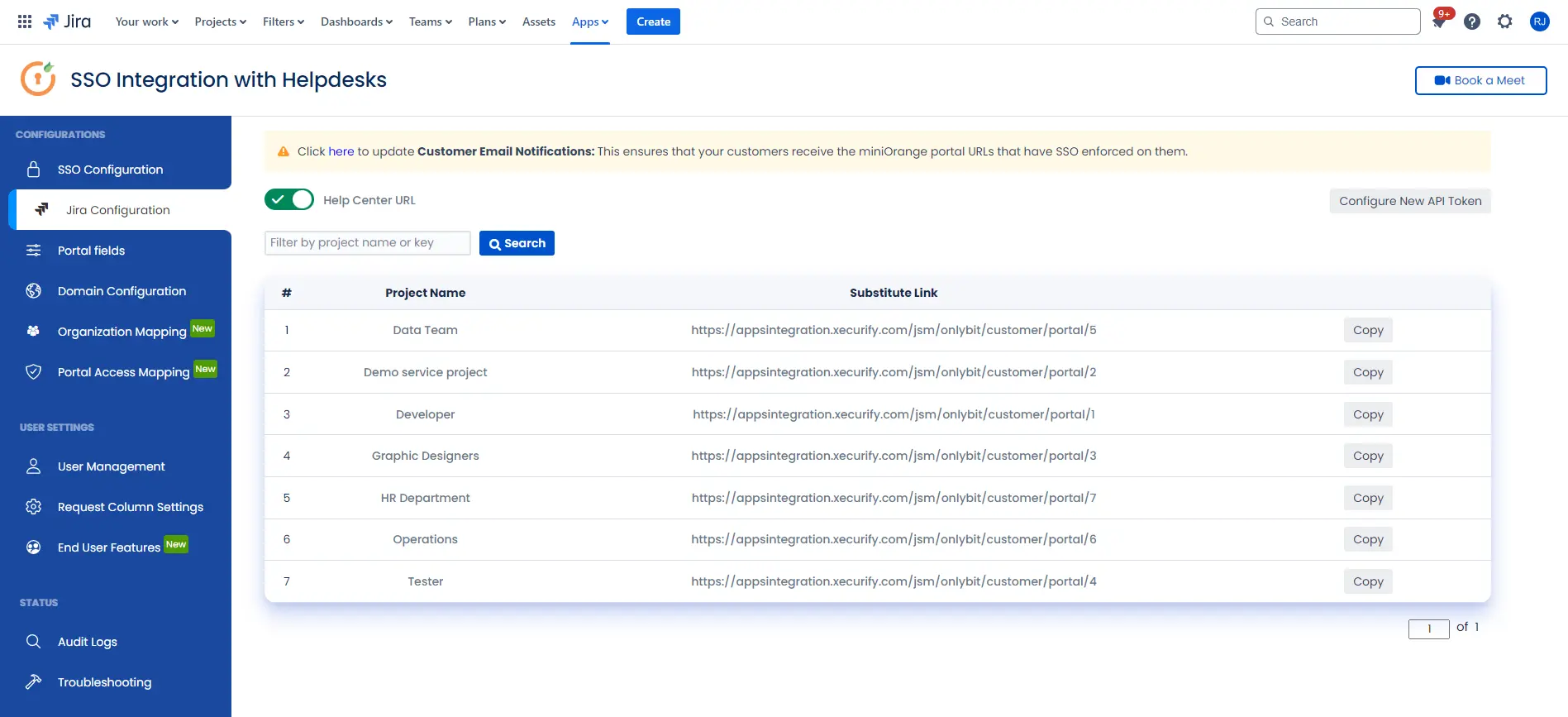
- After successful configuration of API token all the service desk projects with respective links will be displayed. These substituted links will be used by customers for accessing particular projects with SSO.
- Copy any of the substitute links you see for your portals and try accessing it in a private browser window. You would be automatically redirected to your Identity Provider for authentication and would be allowed access to the portal only after successful authentication.
It is necessary to have admin permissions for the service account.
×
![]()
Additional Resources
Did this page help you?

 Try it for free
Try it for free