How to Set Up Two-Factor Authentication (2FA) for JSM Portal Customers
miniOrange Two-Factor Authentication (2FA) app allows you to enforce 2FA for your Jira Service Management (JSM) portal-only customers through Atlassian Guard. This step-by-step guide walks you through the complete setup, from activating Atlassian Guard Standard to configuring SAML SSO and enabling 2FA authentication policies.
Pre-requisites
- Jira is installed and configured on your system.
- Admin credentials for Jira.
Download and Installation
- Log into your Jira instance as an admin.
- Navigate to the Settings menu and click Manage Apps.
- Click Find new apps or Find new add-ons from the left navigation panel.
- Search for miniOrange 2FA for JSM Customers in the Atlassian Marketplace.
- Click Try free or Buy now to begin the installation.
- Enter your information and click Generate license.
- Click Apply license to complete the installation.
Once installed, the miniOrange 2FA plugin will be available under Manage Apps in your Jira administration console. You can now proceed with the setup steps below.
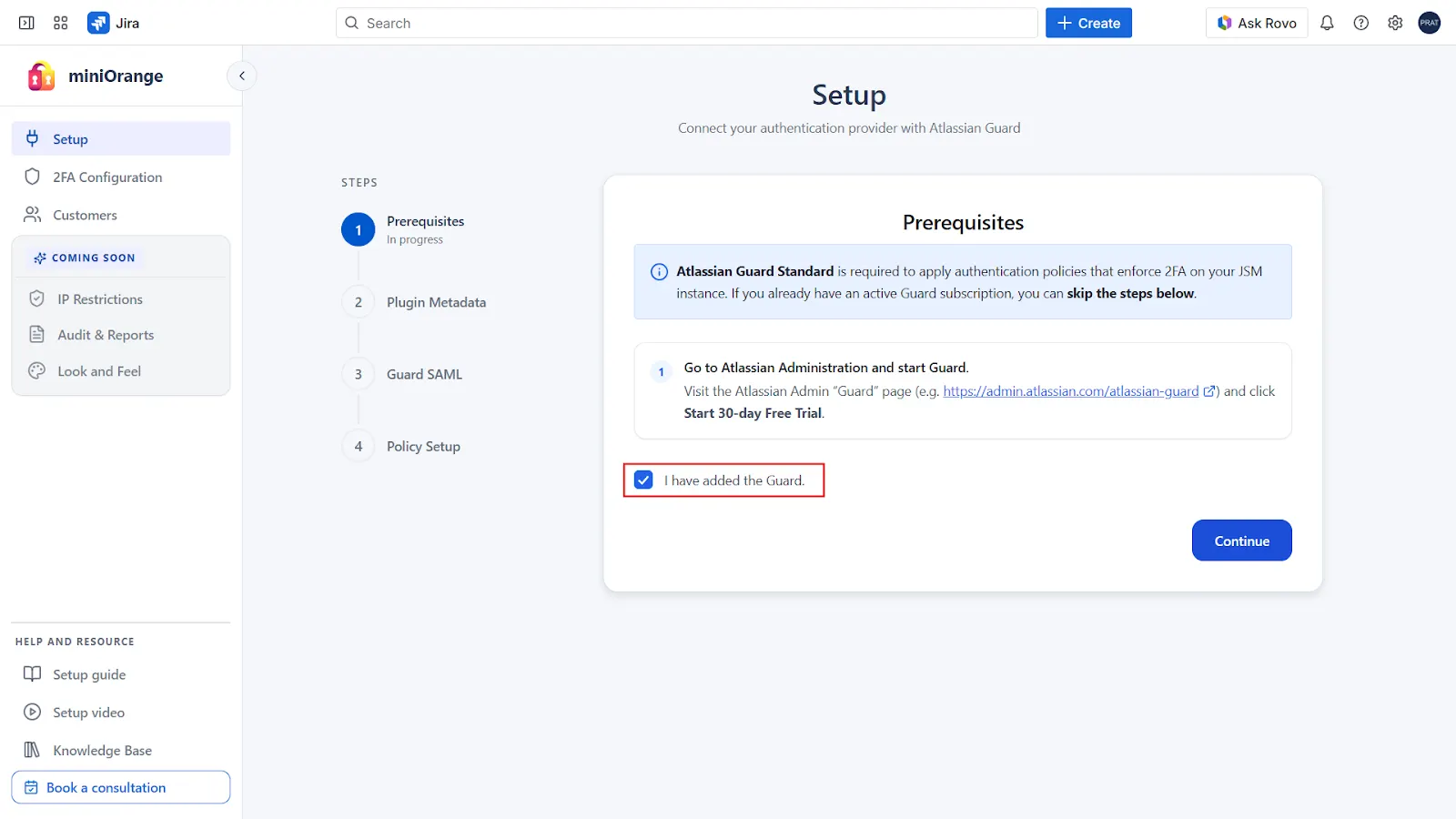
1: Configuring Atlassian Guard
To configure 2FA for your Jira Service Management (JSM) portal customers, you must have an active Atlassian Guard Standard subscription for your organization.
If Atlassian Guard Standard is already active for your organization, you can skip this step and proceed to the next section.
If you do not yet have an active Guard subscription, follow the steps below:
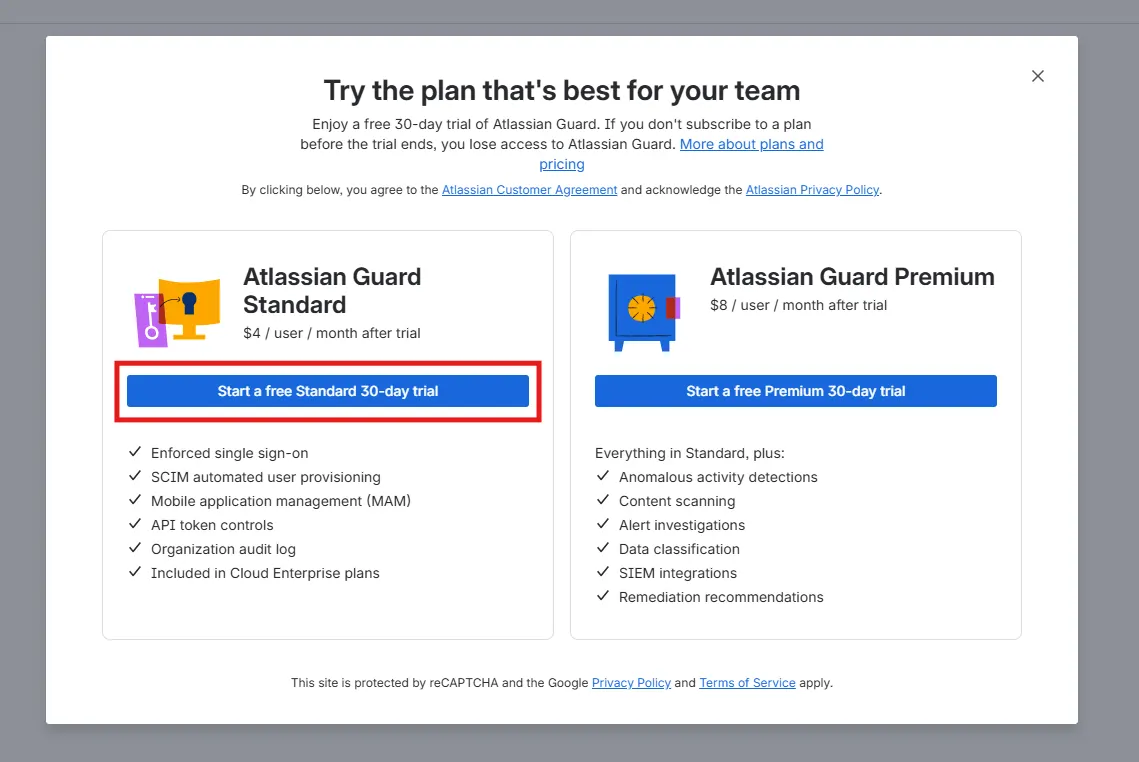
Enable Atlassian Guard Standard (Free Trial)
- Open the Atlassian Guard admin page: https://admin.atlassian.com/atlassian-guard
- If your account manages multiple organizations, select the organization where you want to configure 2FA for portal users.
- Click Start a free Standard 30-day trial to activate the trial for the selected organization.
- After starting the trial, return to the 2FA app’s Setup tab, select the confirmation checkbox then click Continue to proceed.
2: Configure Authentication Source in Atlassian Guard
Follow the steps below to configure the authentication source for portal-only customers using SAML SSO.
-
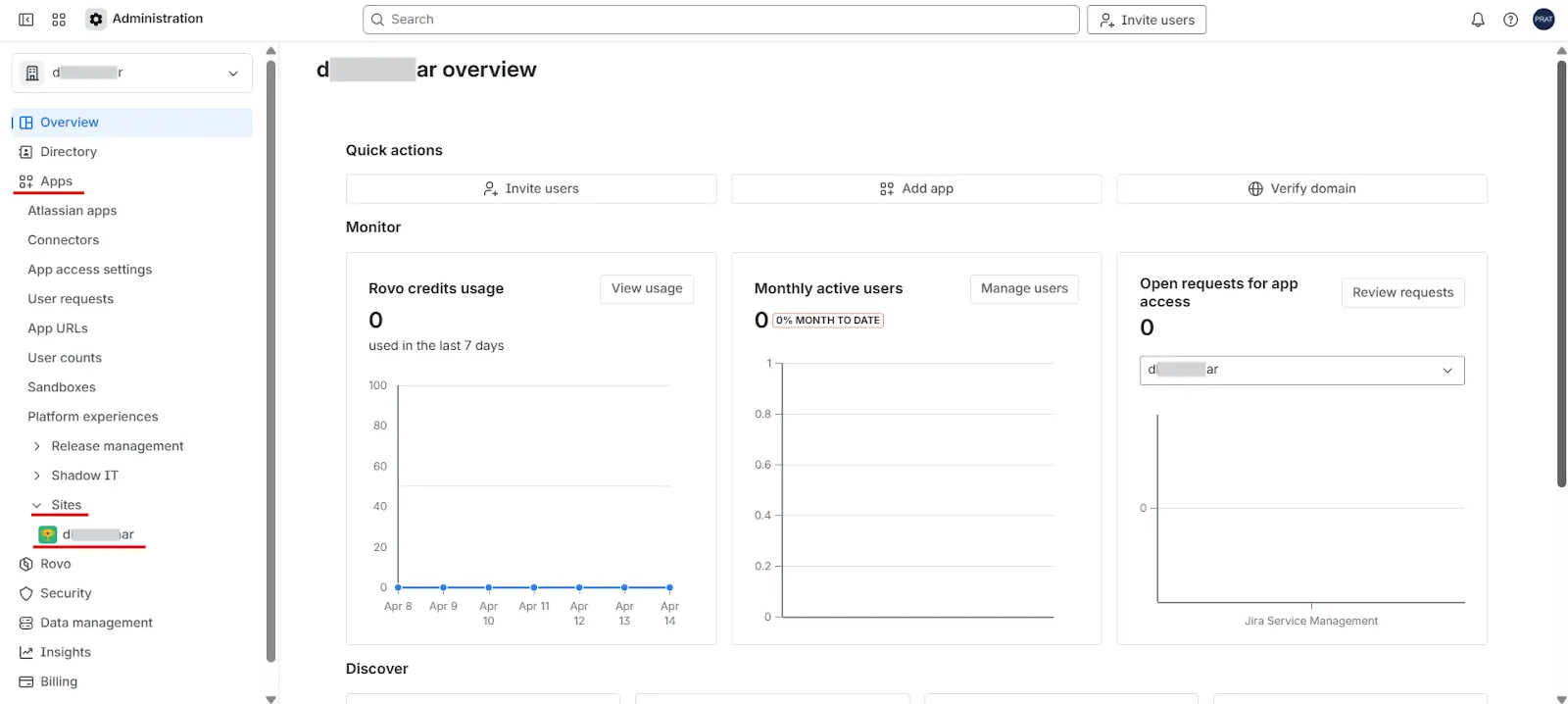
Open the Atlassian Admin console:
https://admin.atlassian.com
If your account manages multiple organizations, select the organization where you want to configure 2FA for portal users. - From the left navigation panel, go to: Apps → Sites. Then select your Jira Service Management (JSM) site.
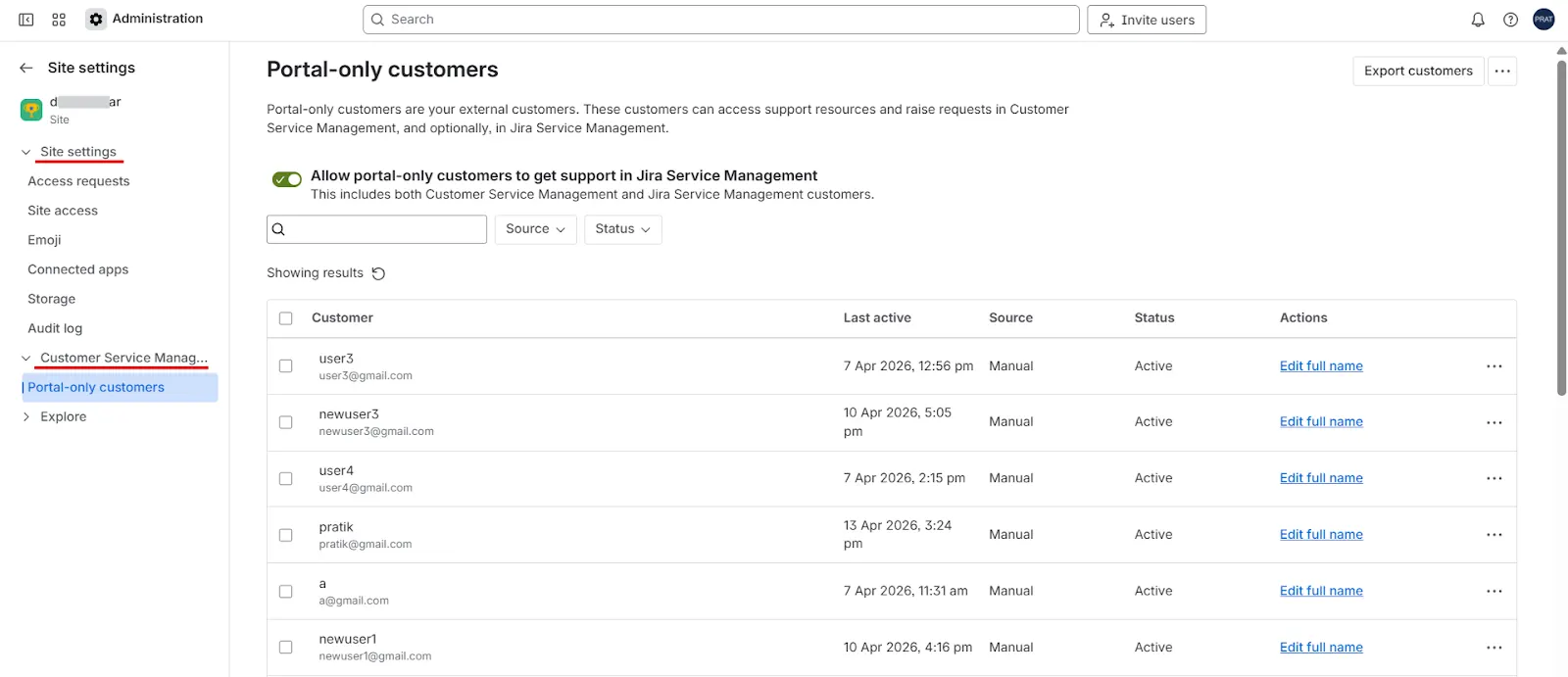
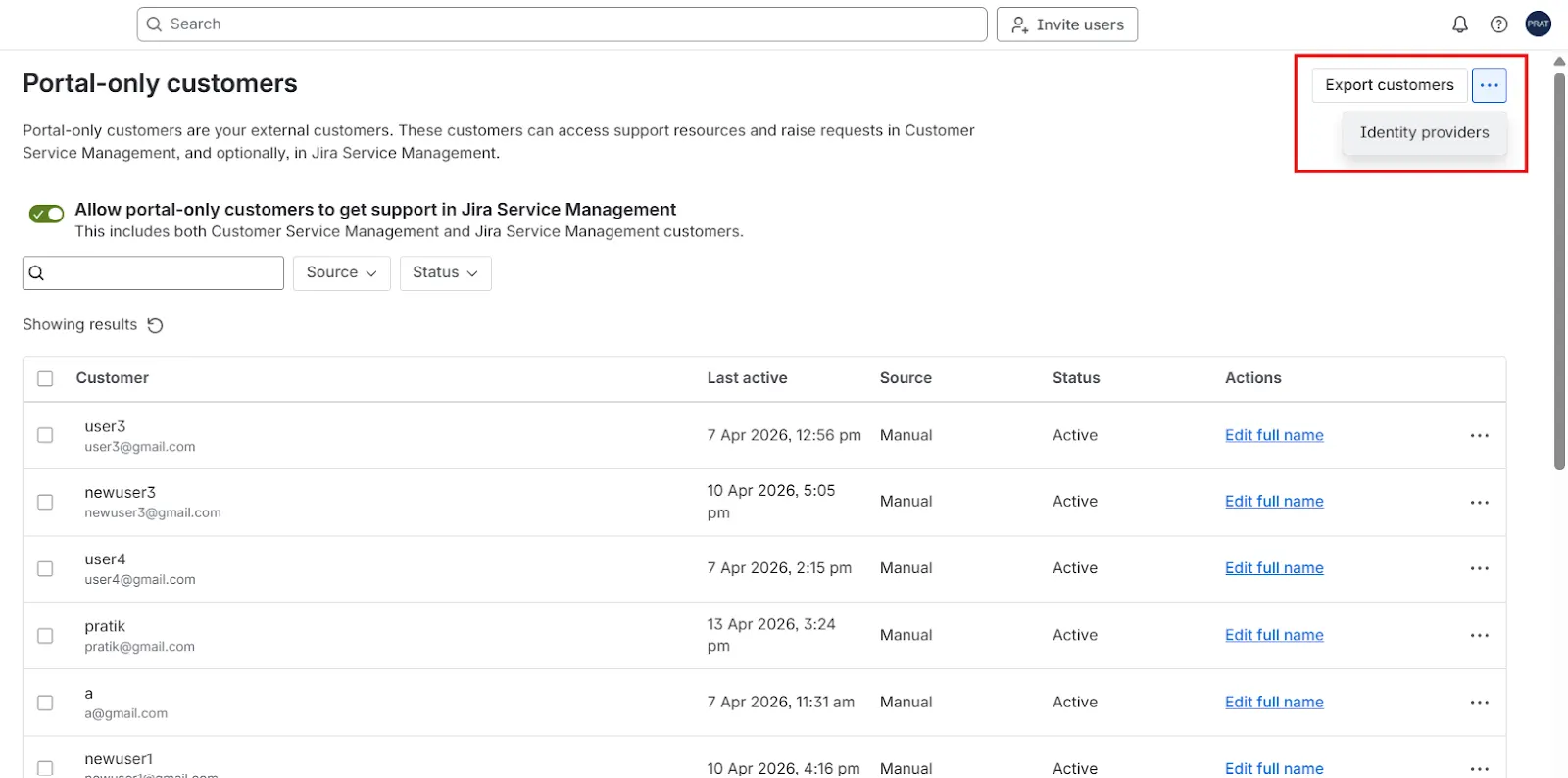
- Under Customer Service Management, click Portal-only customers.
- In the top-right corner of the page, click the three-dot menu (⋯) and select Identity provider.
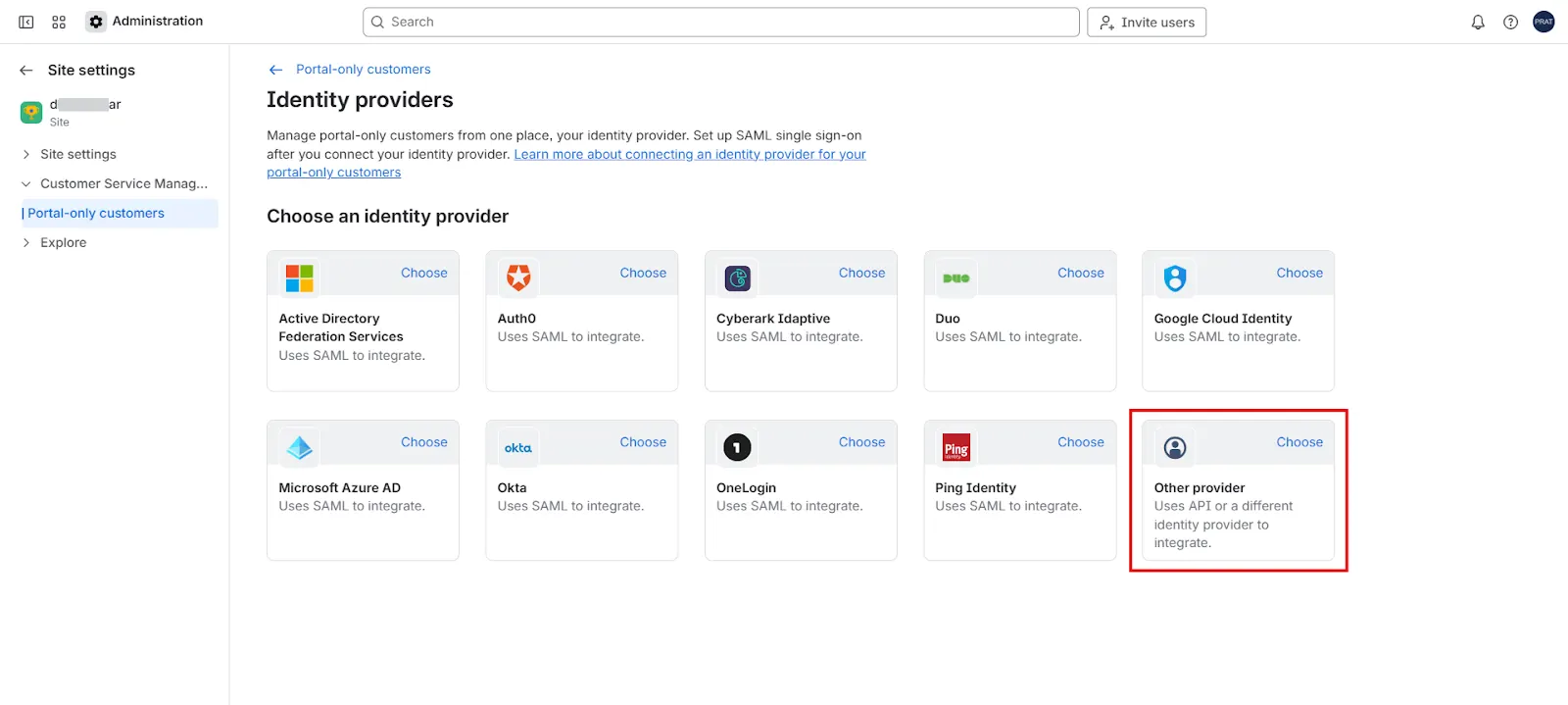
- From the list of available providers, choose Other provider.
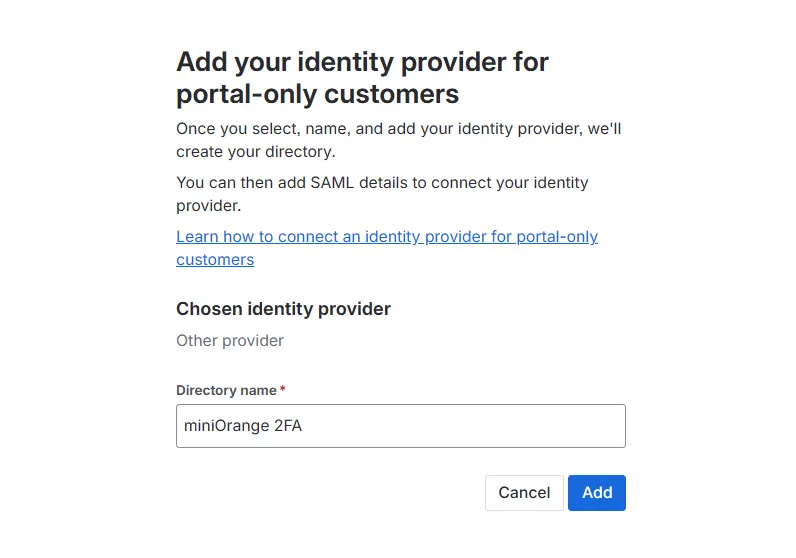
- Enter a Directory name (any meaningful name for identification), then click Add.
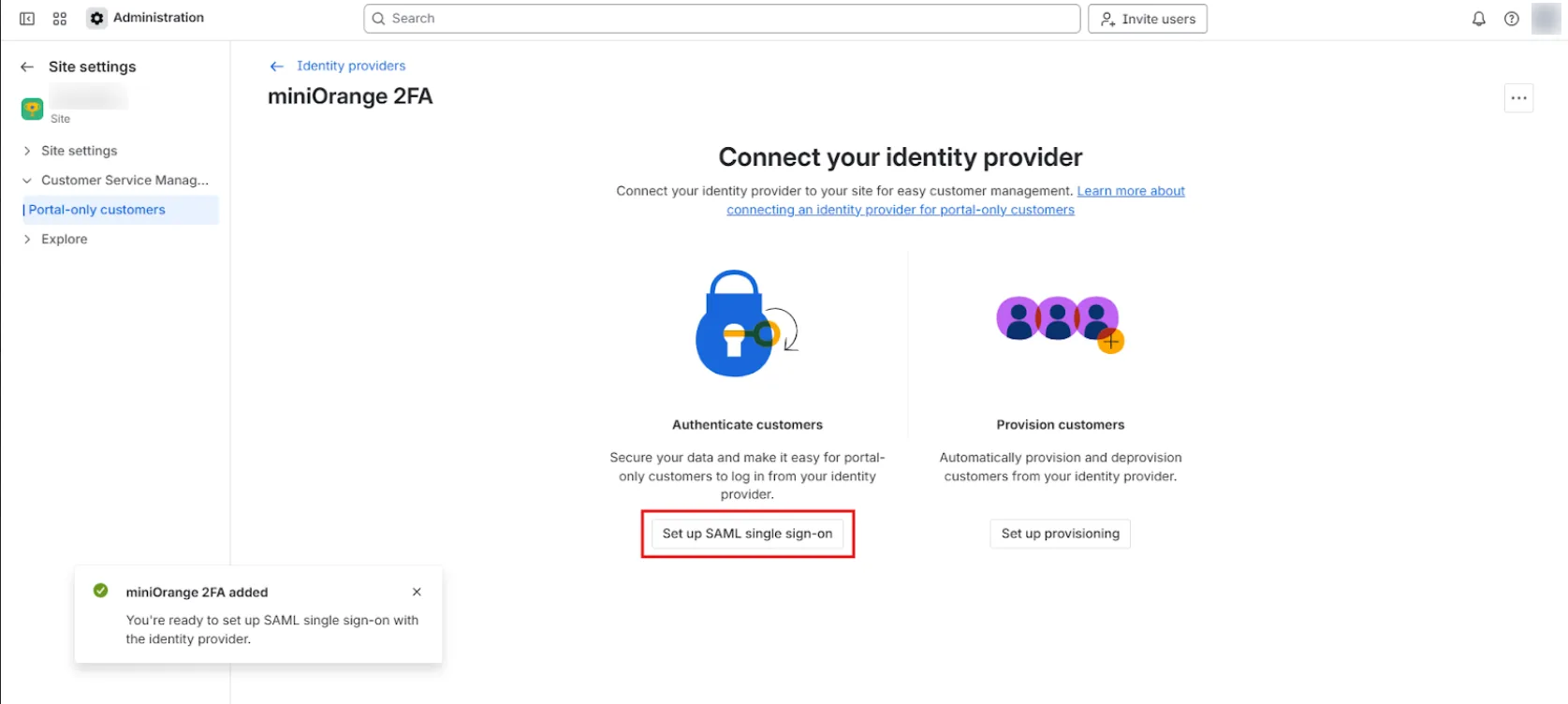
- After the directory is created successfully, a confirmation message will appear. Click Set up SAML single sign-on.
- On the SAML configuration page, enter the following values:
- Identity provider entity ID
- Identity provider single sign-on URL
- Public X.509 certificate
- Atlassian Guard will now generate SAML configuration details.
- Service provider entity ID
- Assertion Consumer Service (ACS) URL
- After entering these details in the app, click Save & Continue in the app.
These values are available in the app configuration page.
Copy each value from the app and paste it into the corresponding fields in Atlassian Guard. After entering the details, click Next on both configuration screens.
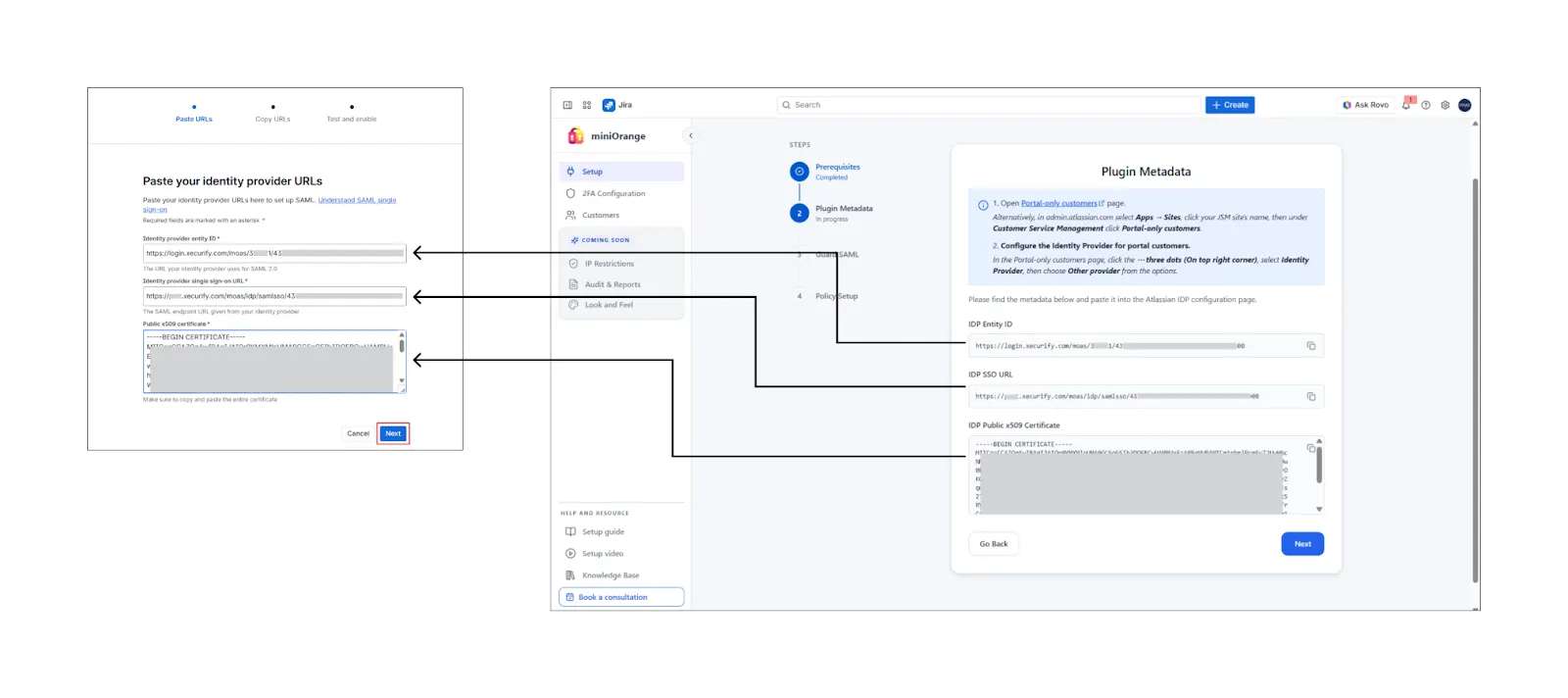
Copy the following values from the Atlassian Admin page and paste them into the corresponding fields in the app:
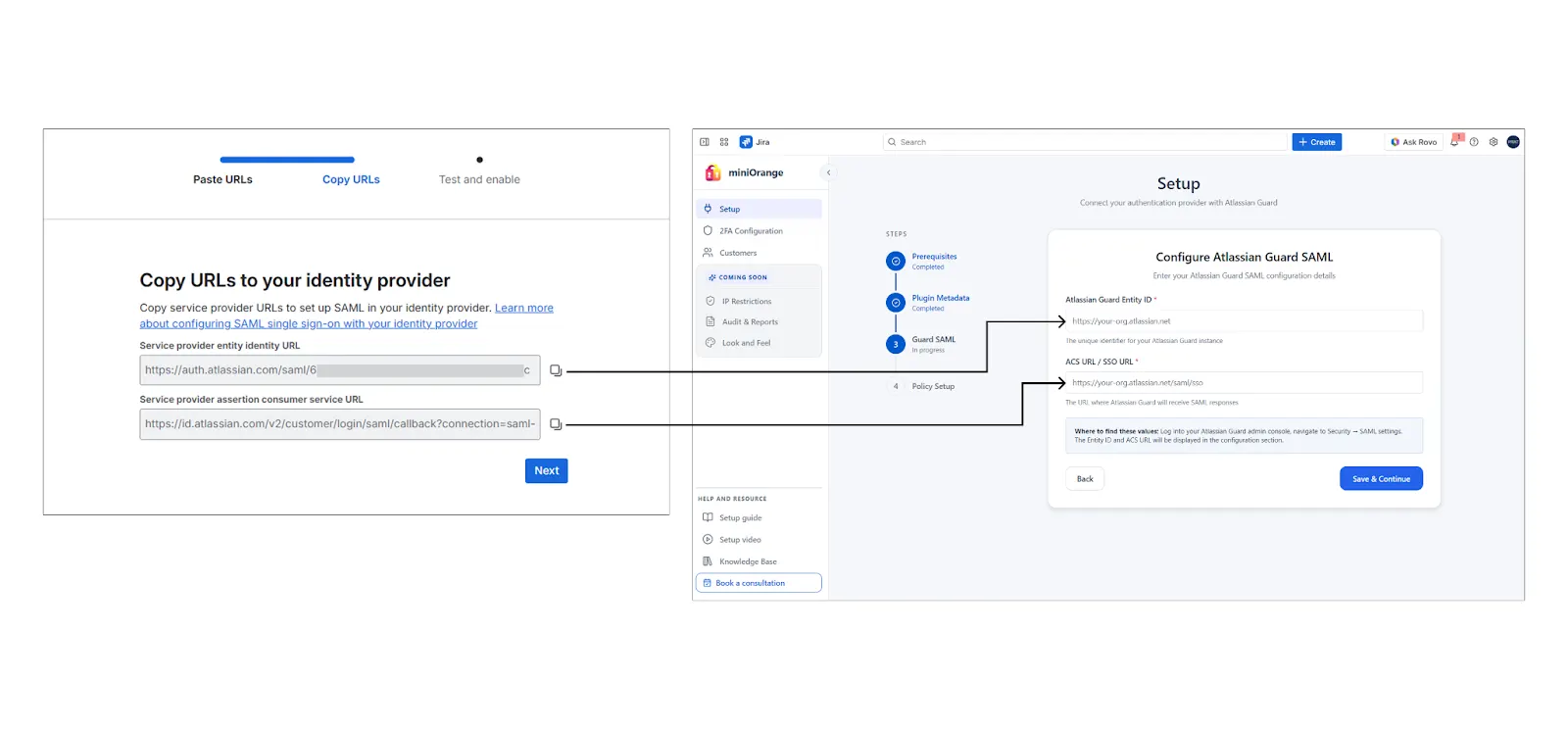
Then return to the Atlassian Admin page and click Next to proceed.
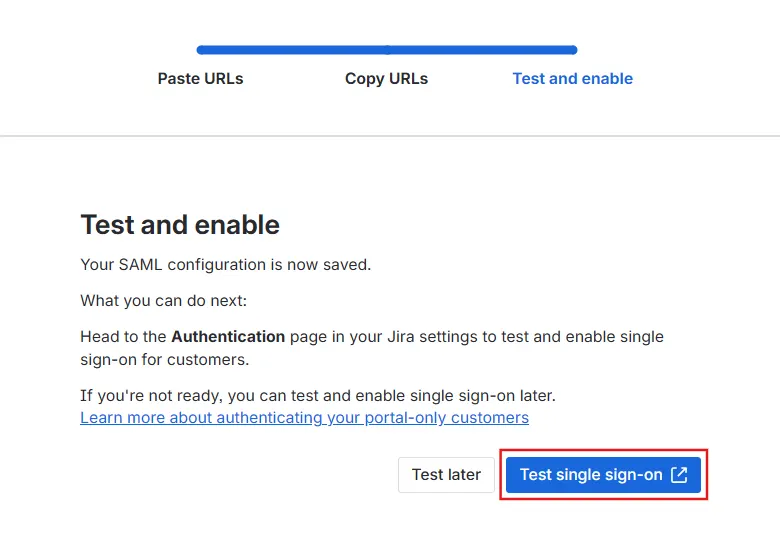
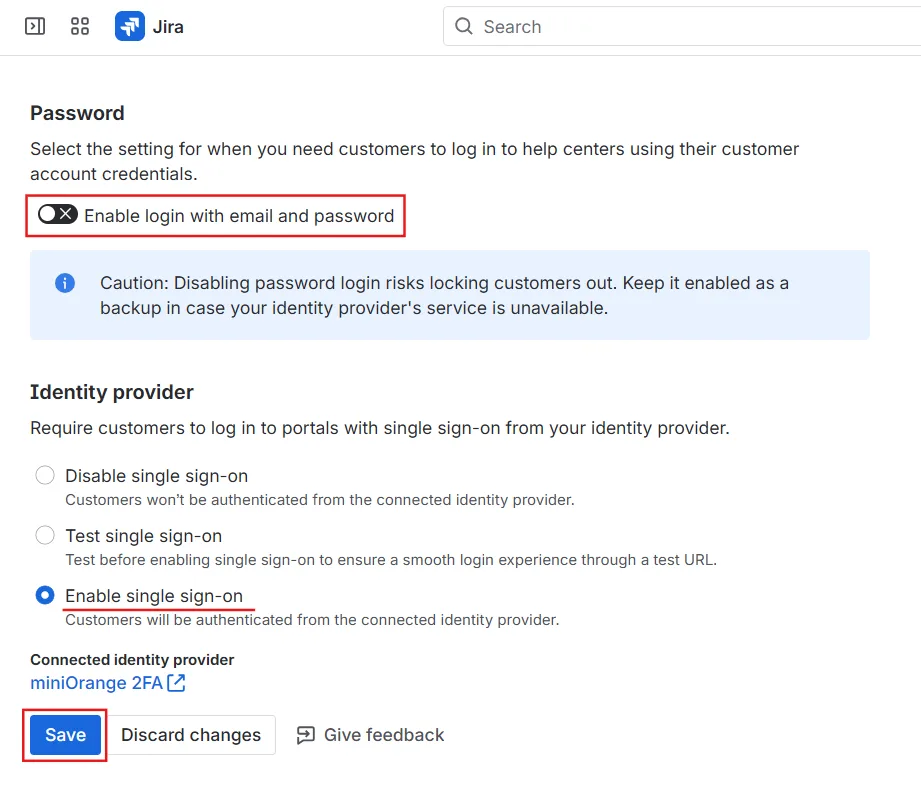
3: Configure Authentication Policy
After completing the SAML configuration, configure the authentication policy for portal-only customers.
-
On the Test single sign-on screen, click
Test single sign-on.
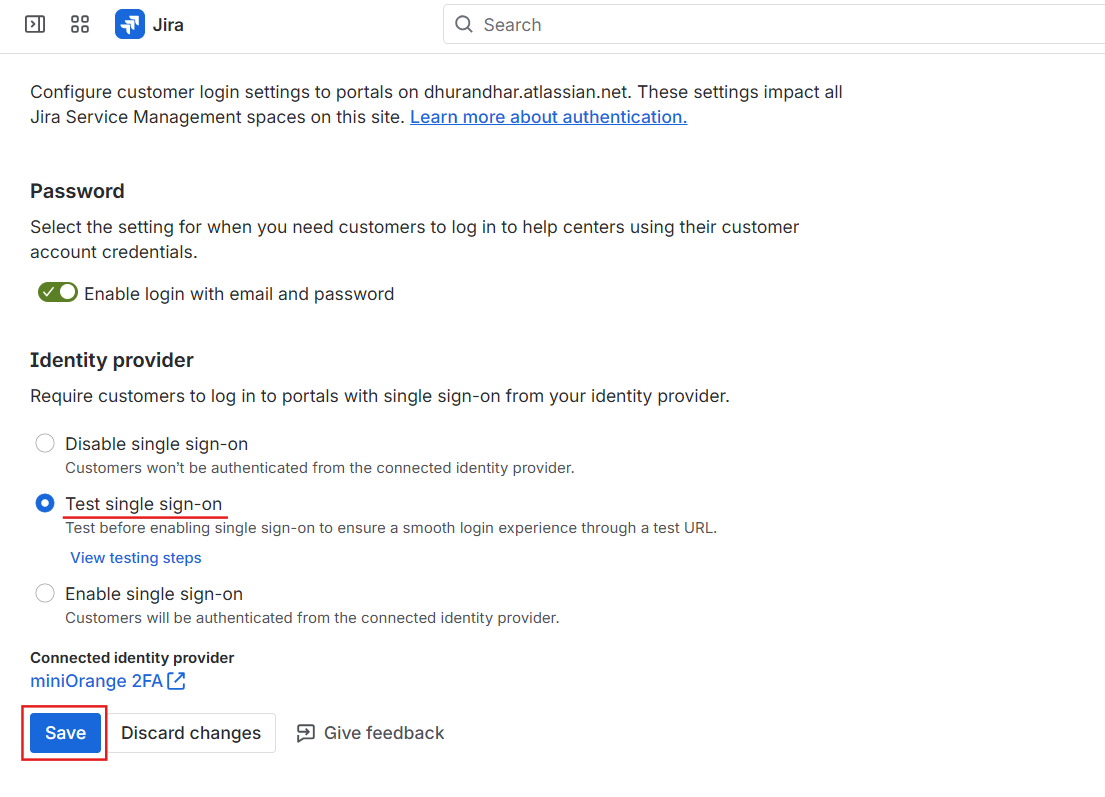
You will be redirected to the Authentication for portal-only customers settings page. - Select Test single sign-on, then click Save.
- After saving, click View testing steps.
- Once testing is successful:
- Select Enable single sign-on
- Disable the toggle for Login with email and password
- Click Save
- Return to the app configuration page. Select the confirmation checkbox (as shown in the app UI), and click Save.
A popup window will appear with instructions to verify the SAML login
configuration.
Follow the steps shown in the popup to complete the verification
process.
This ensures portal-only customers authenticate using SSO.
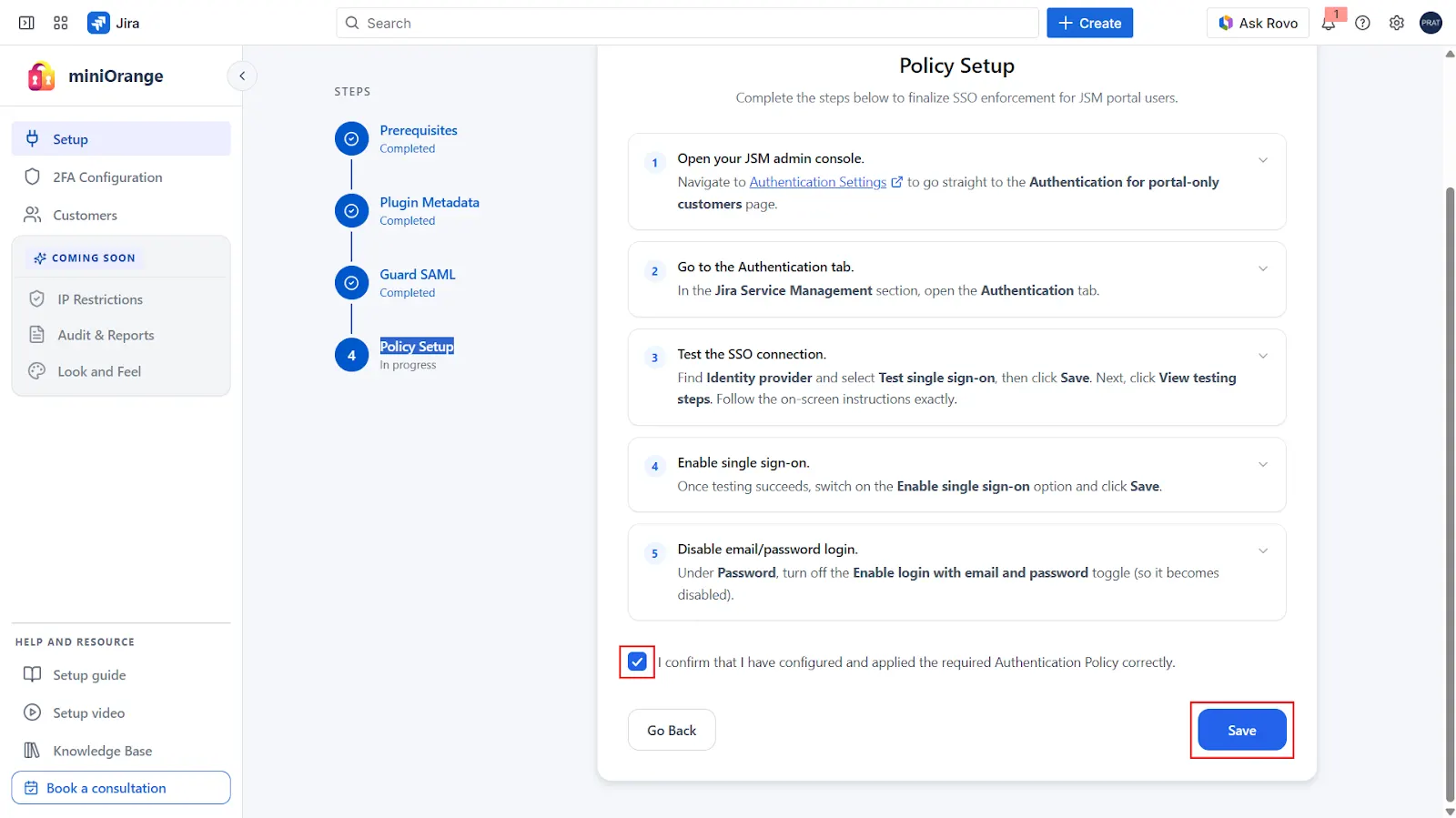
You have now completed the Guard integration setup successfully 🎉
You can proceed to the 2FA Configuration page in the app and configure authentication methods according to your requirements.
4: 2FA Configuration Tab
After completing the Guard integration, navigate to the 2FA Configuration tab in the plugin to enable and configure Two-Factor Authentication for your JSM portal customers.
 4.1 Enable 2FA for Jira Service Management
4.1 Enable 2FA for Jira Service Management
Enable the toggle for Jira Service Management to activate 2FA for portal customers. Once enabled, you can configure the available 2FA methods and manage customer-level settings.
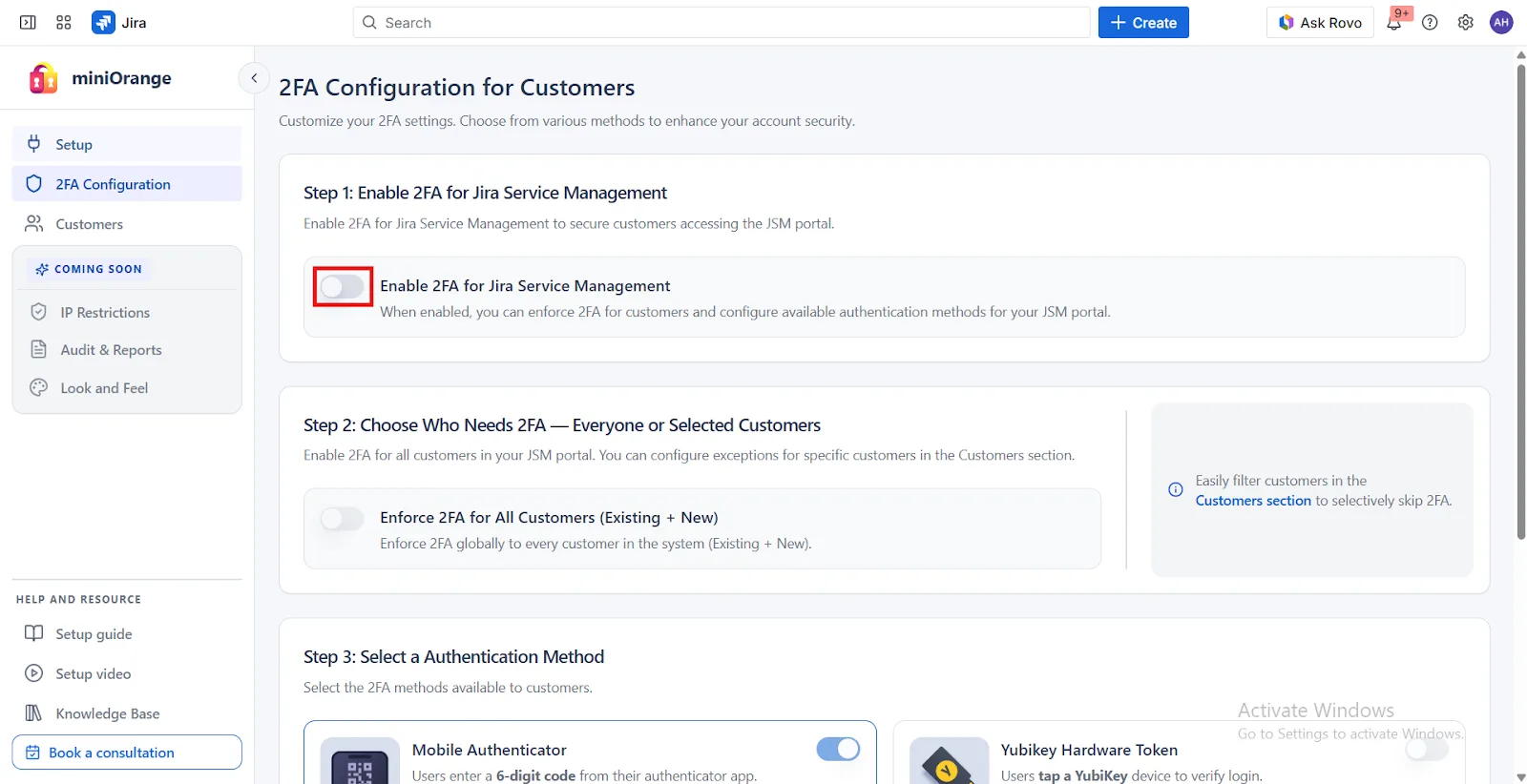
 4.2 Choose Who Needs 2FA — Everyone or Selected Customers
4.2 Choose Who Needs 2FA — Everyone or Selected Customers
-
Enable 2FA for All Users in Your Organization:
Activate Two-Factor Authentication (2FA) across your to enhance security for all users. You can create exceptions for specific users or groups from the Customers tab. -
Enforce 2FA for All Users (Existing + New):
Enforce 2FA for all users—both existing and newly created—ensuring consistent security coverage across your organization.
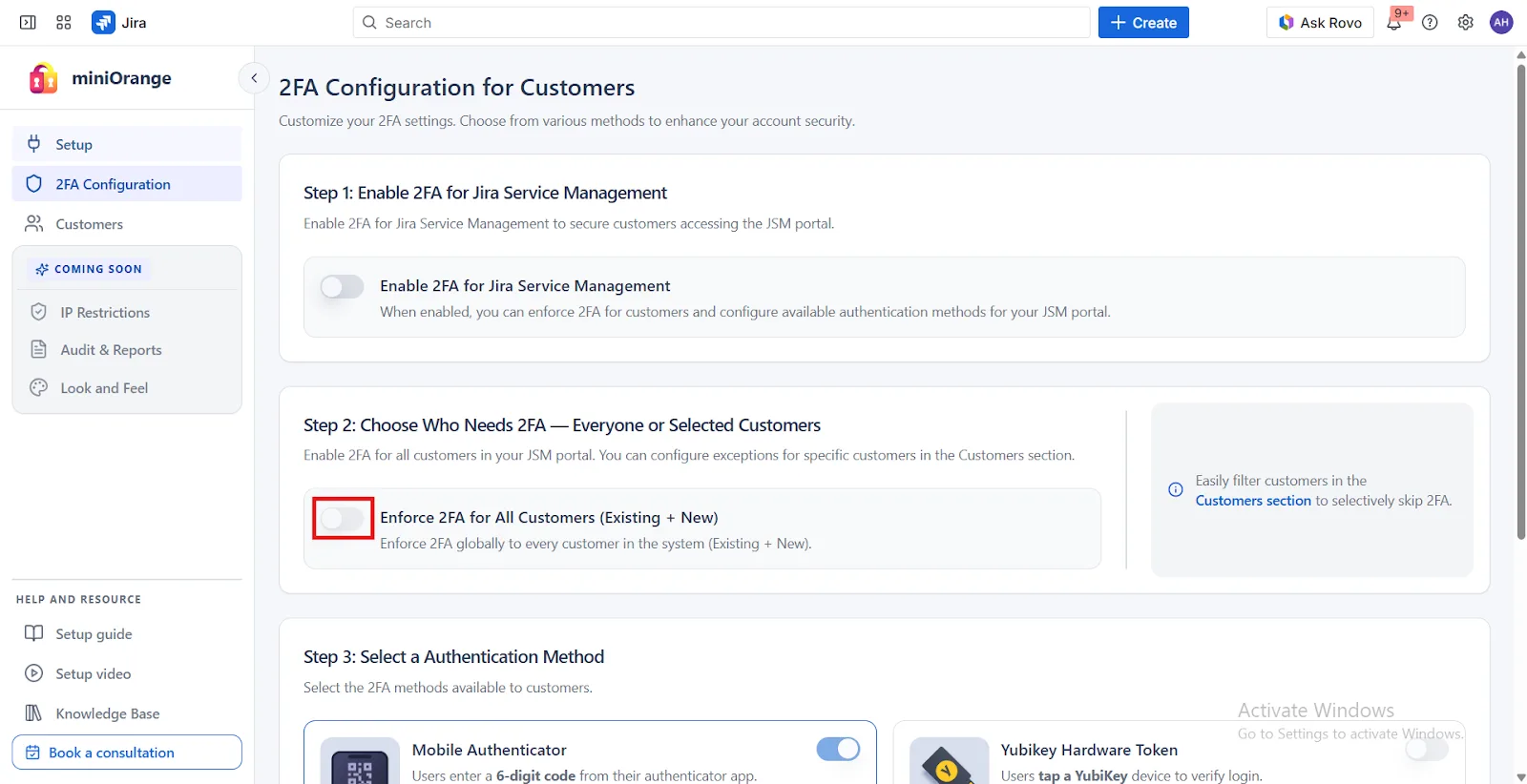
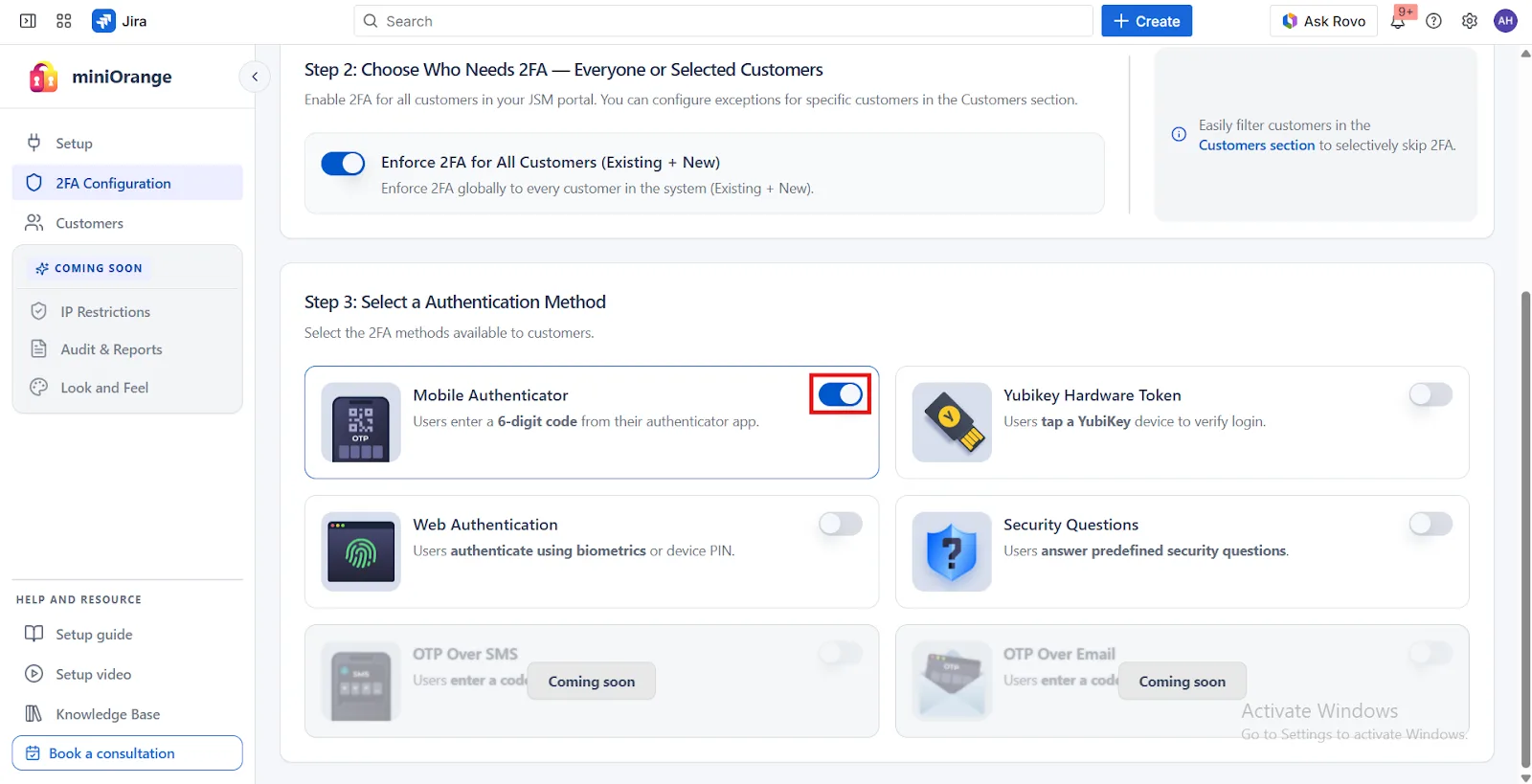
 4.3 Select an Authentication Method
4.3 Select an Authentication Method
Choose 2FA Methods: The miniOrange 2FA add-on offers users a range of 2FA methods, including Web Authentication, KBA, TOTP, and more, for authentication. You can enable the desired 2FA methods from the provided list during app configuration. To enable the chosen methods for your users, you just have to select the 2FA method option and toggle it active.
5: Customers Tab
The Customers Tab provides a centralized setup interface to manage JSM portal customers and their 2FA settings. It allows efficient administration of customer accounts along with support for individual and bulk 2FA operations.
The following sections are available in Customers Tab:
- 2FA Enabled Customers
- 2FA Disabled Customers
- All Customers
 5.1 Import Portal Customers
5.1 Import Portal Customers
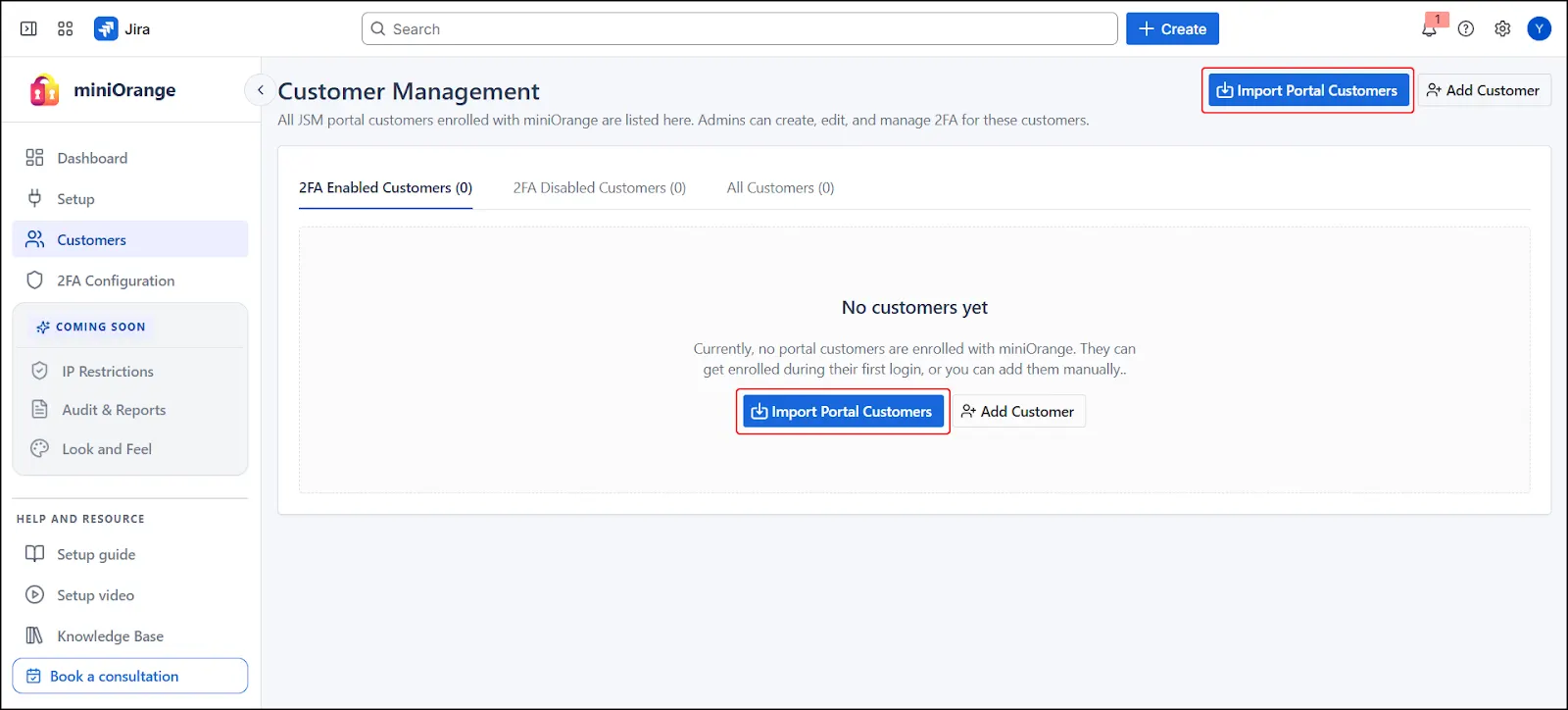
- Click Import Portal Customers in the Customers tab.
- A step-based modal wizard opens.
- Selection of the import method is required to proceed.
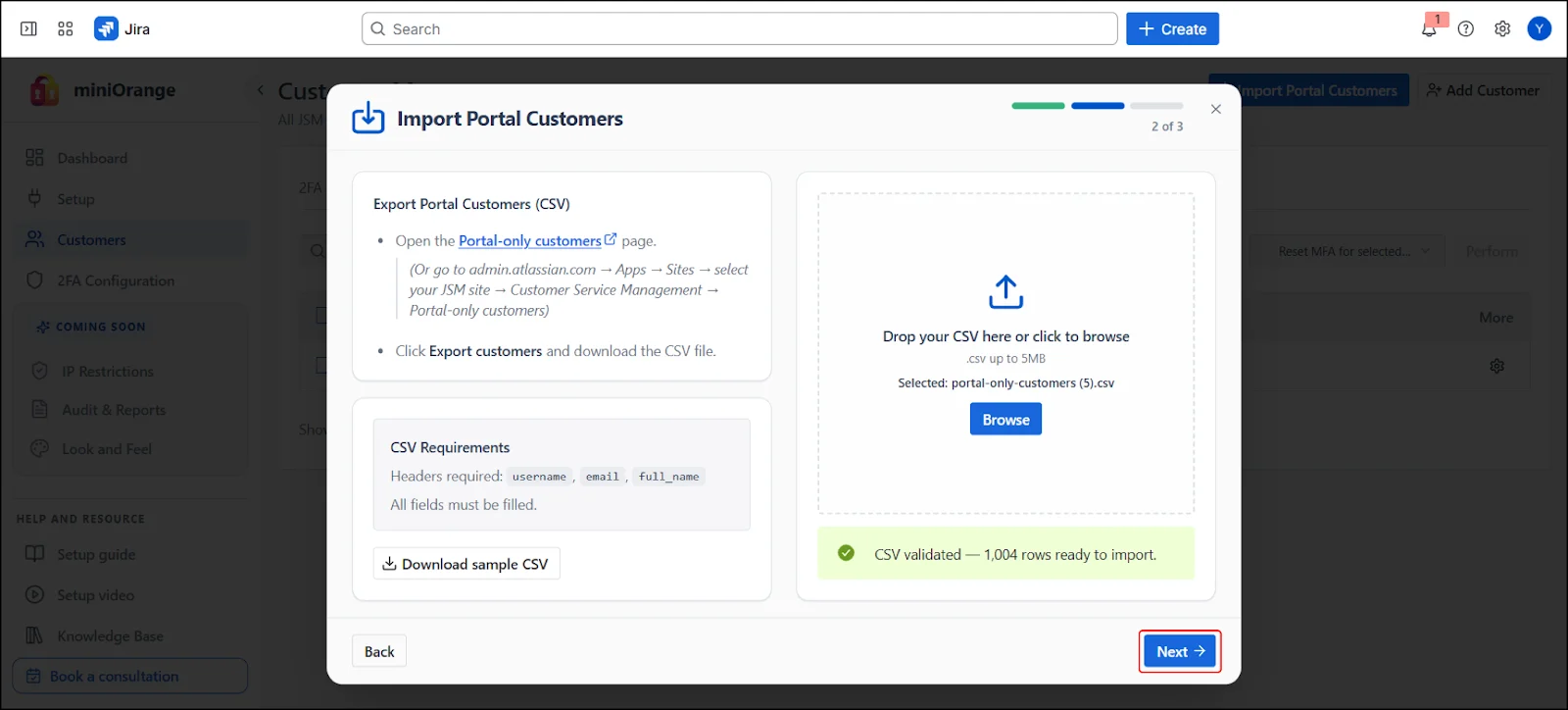
1.A. Import from CSV:
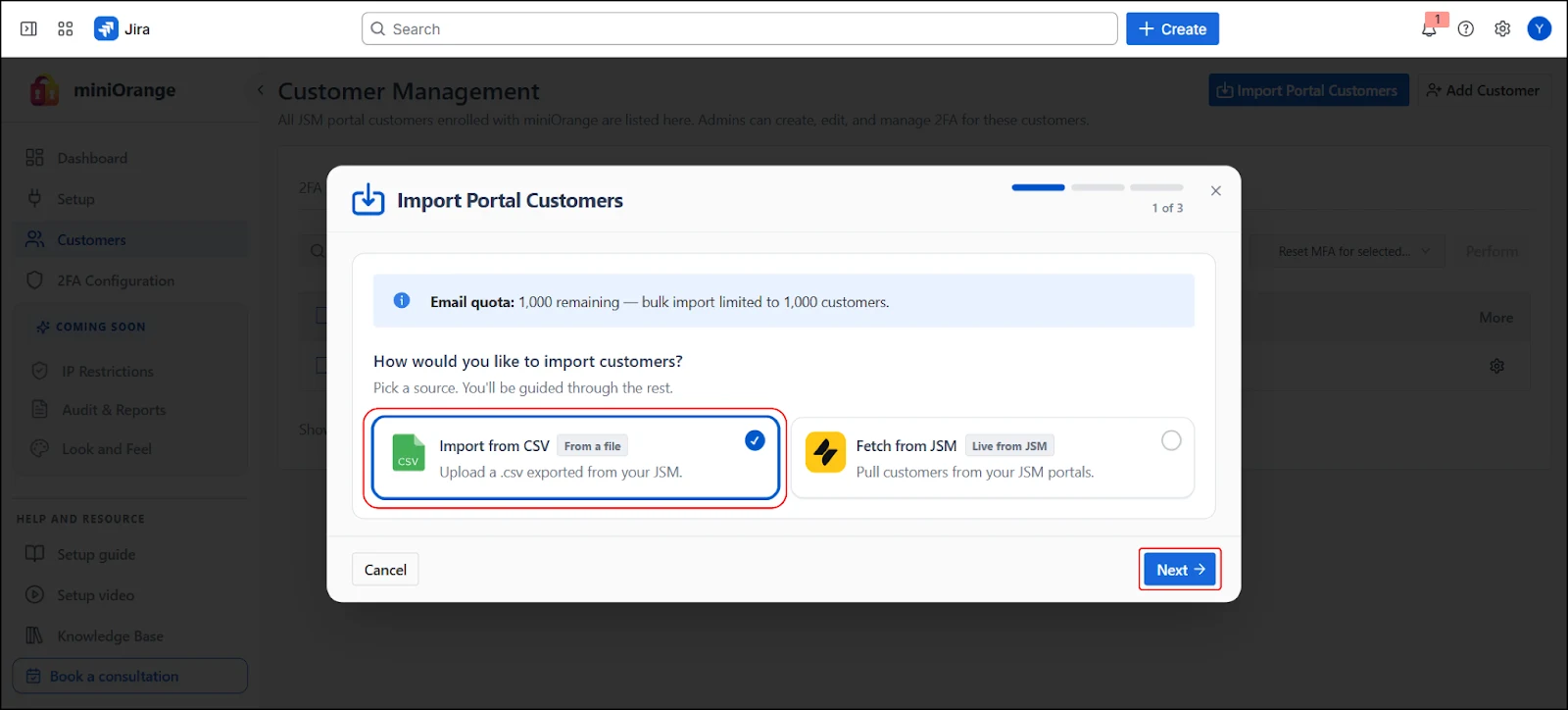
Allows upload of a CSV file exported from JSM.
- Select Import from CSV
- Upload CSV by following the given steps:
- Export JSM Customers From Atlassian:
- Navigate to Portal-only Customers (Go to admin.atlassian.com → Apps → Sites → select your JSM site → Customer Service Management → Portal-only customers )
- Select Export Customers
- Download generated CSV file for upload
- Upload CSV file using drag & drop or file browser in the Step 2 section
- Proceed to next step
1.B. Choosing Fetch from JSM:
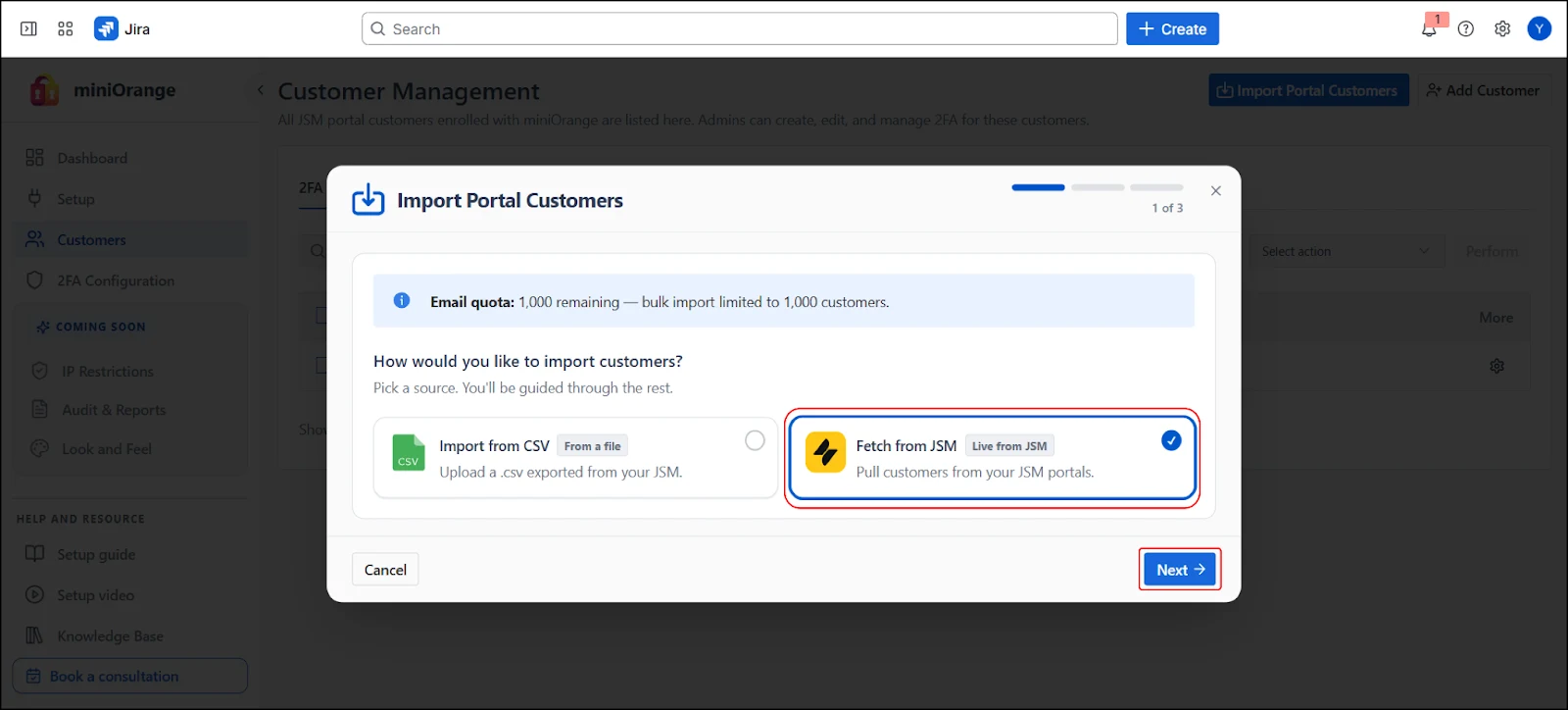
- Select Fetch from JSM
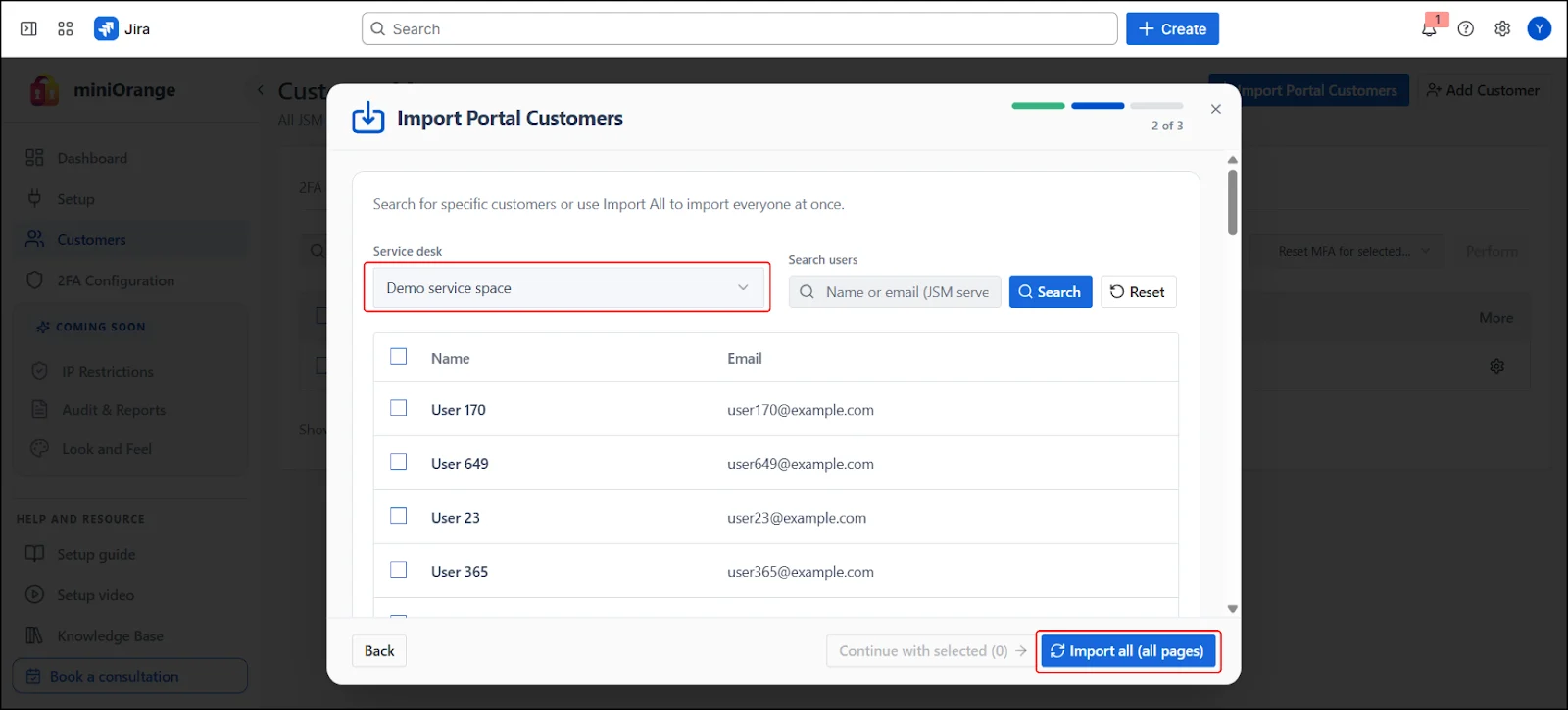
- Select Customers from Fetched List:
- Select a Service Desk / Portal from dropdown (e.g., “Demo service space”)
- Customer list is displayed in a table
- Search by name or email
- Select individual customers using checkboxes
- Select all customers from portal
- Import full portal customer list
- Select Import Mode:
- Safe Mode (Recommended) – Manually trigger each batch; inspect results between batches
- Auto Mode (Faster) – All batches run automatically in sequence on the server
- Select your preferred mode
- If Safe Mode: Click Create next to each batch to trigger it manually
- If Auto Mode: Click Start automatic run
- Wait for all batches to complete
- Click Finish
Capabilities:
Note:
 5.2 Add Customers Manually
5.2 Add Customers Manually
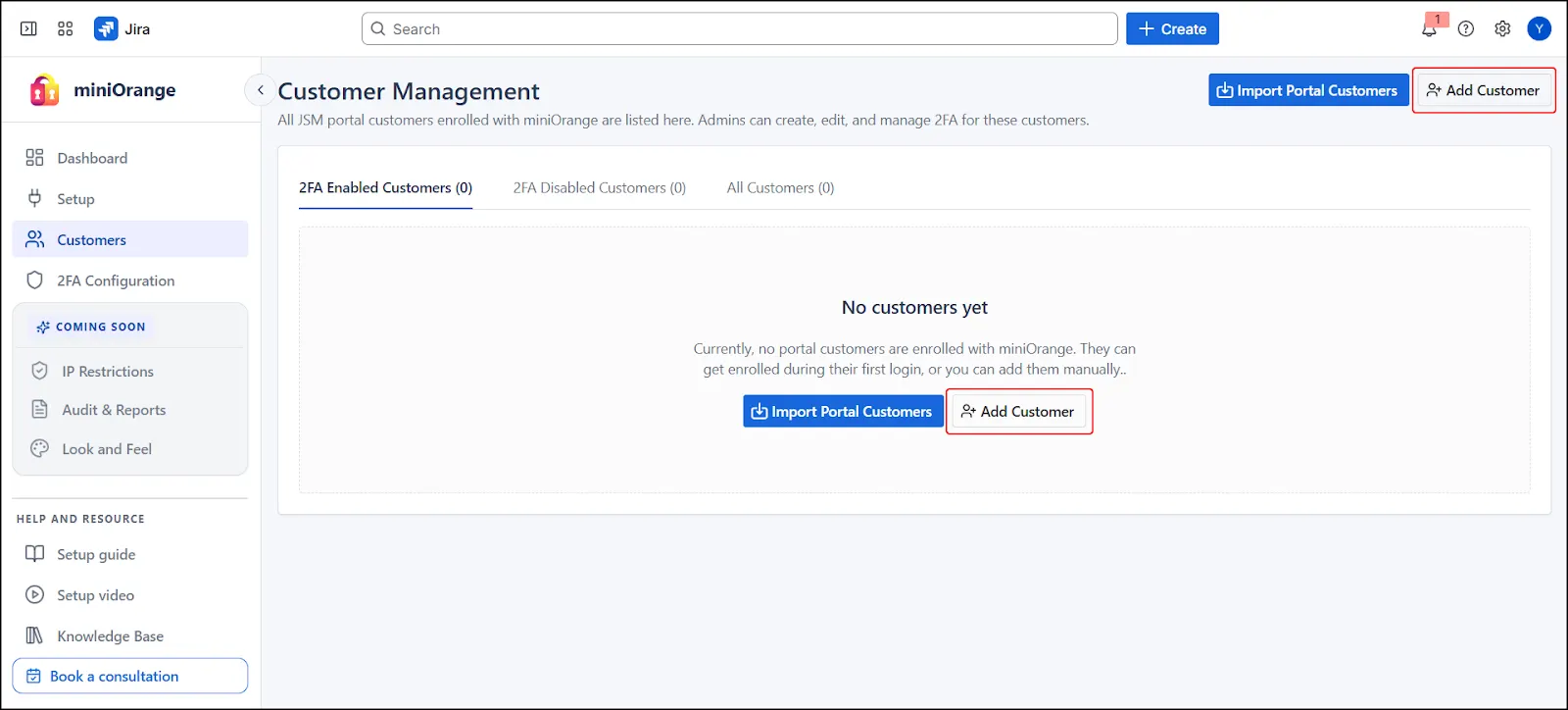
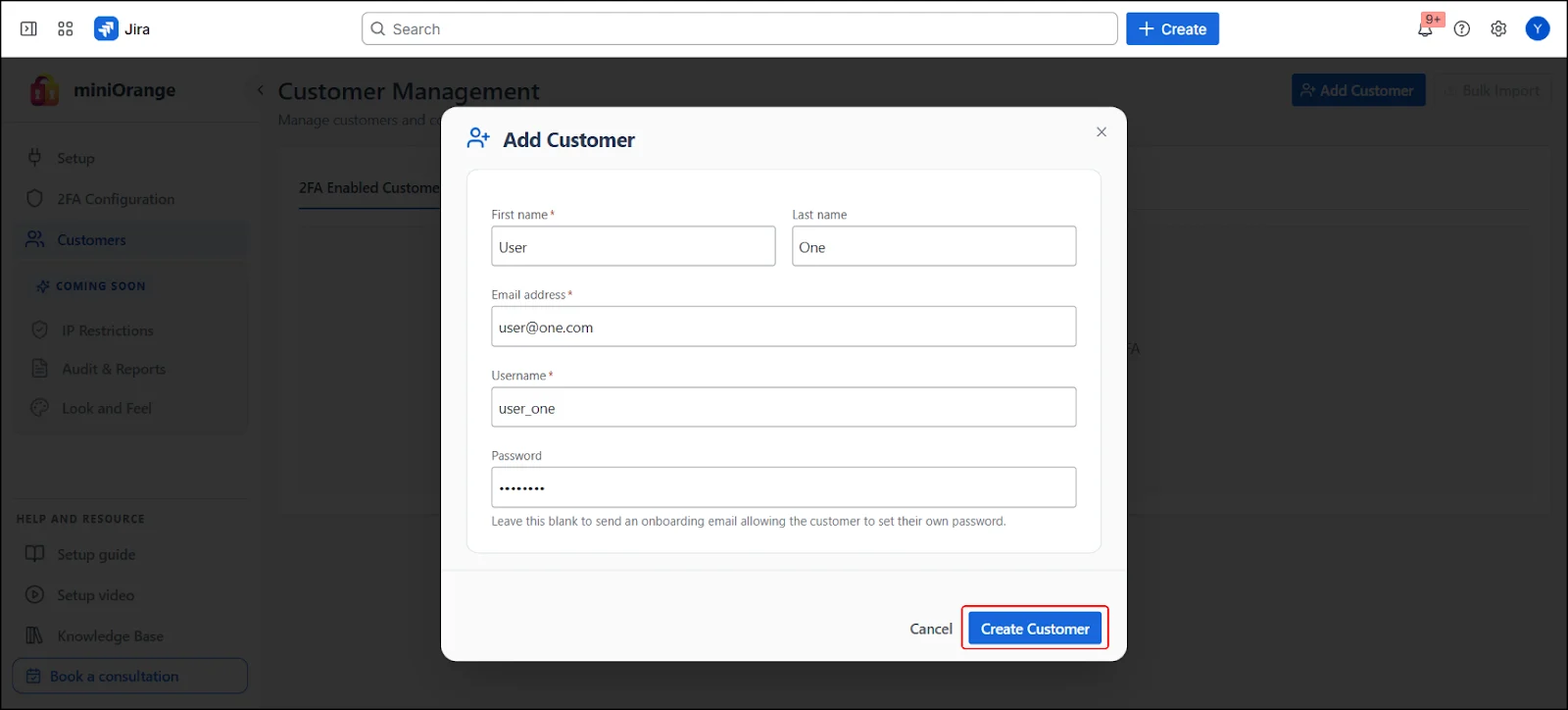
- Click Add Customer in the Customers tab. A modal form will be displayed for entering customer details.
- Fill in the required fields:
- First Name – Given name of the customer
- Last Name – Surname of the customer
- Email – Unique identifier for the customer and Used for communication and authentication
- Username – Unique identifier for the customer
- Password (Optional) – Set a password manually or leave blank
- Password Behavior
- If a password is provided, the customer receives a welcome email and then login is enabled using provided credentials
- If the password is left blank, the customer receives an onboarding email to set their own password
- Click Create Customer after completing the form.
- After creation, the customer will appear under the All Customers tab, as well as under either the 2FA Enabled or 2FA Disabled tab based on your MFA configuration.
 5.3 View and Filter Customers
5.3 View and Filter Customers
Customers are organized into three sub-tabs:
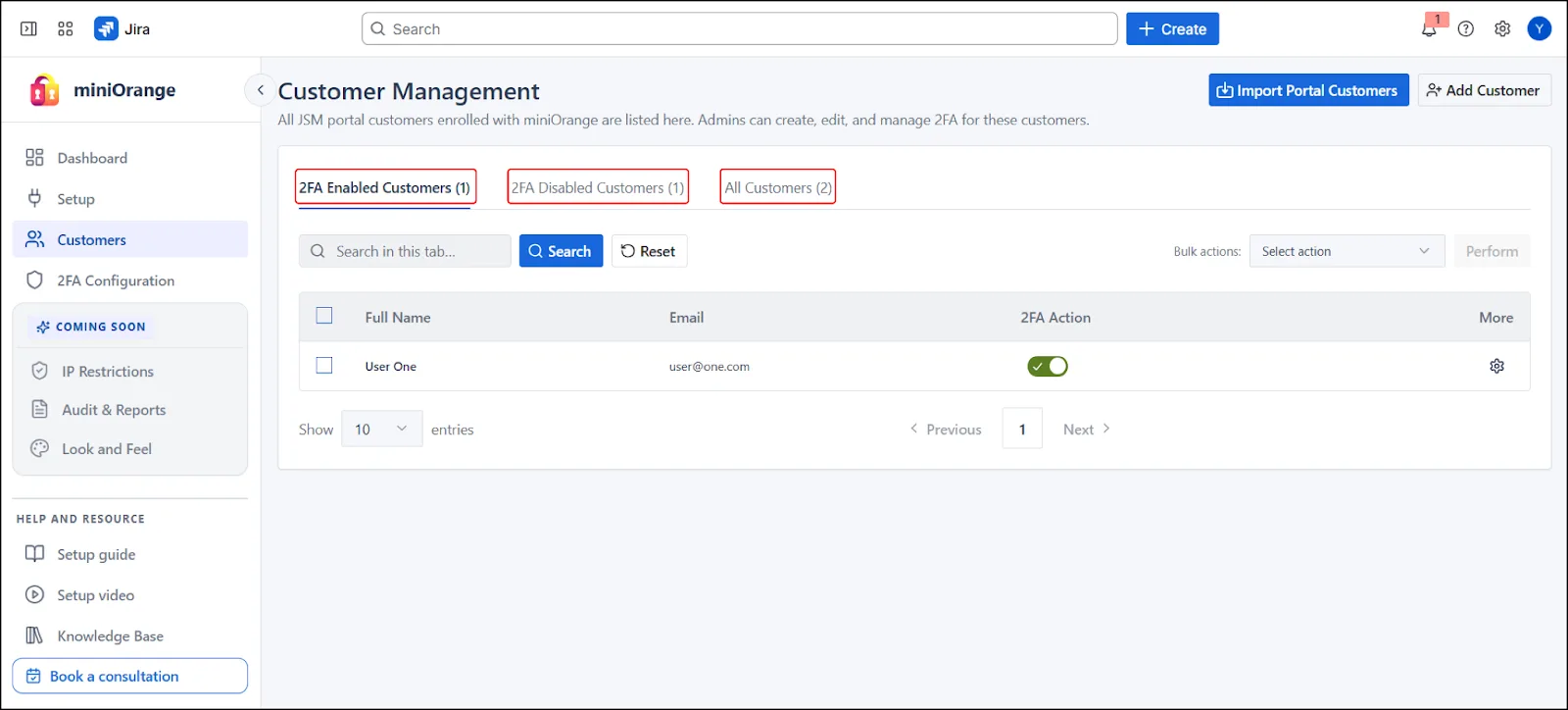
2FA Enabled Customers
- Displays all customers who currently have 2FA enabled
- Helps admins monitor customers who are already secured with 2FA
- Allows disabling 2FA for specific customers if required
2FA Disabled Customers
- Displays all customers who do not have 2FA enabled
- Useful for identifying customers who are not protected
- Allows admins to enable 2FA for these customers individually or in bulk
All Customers
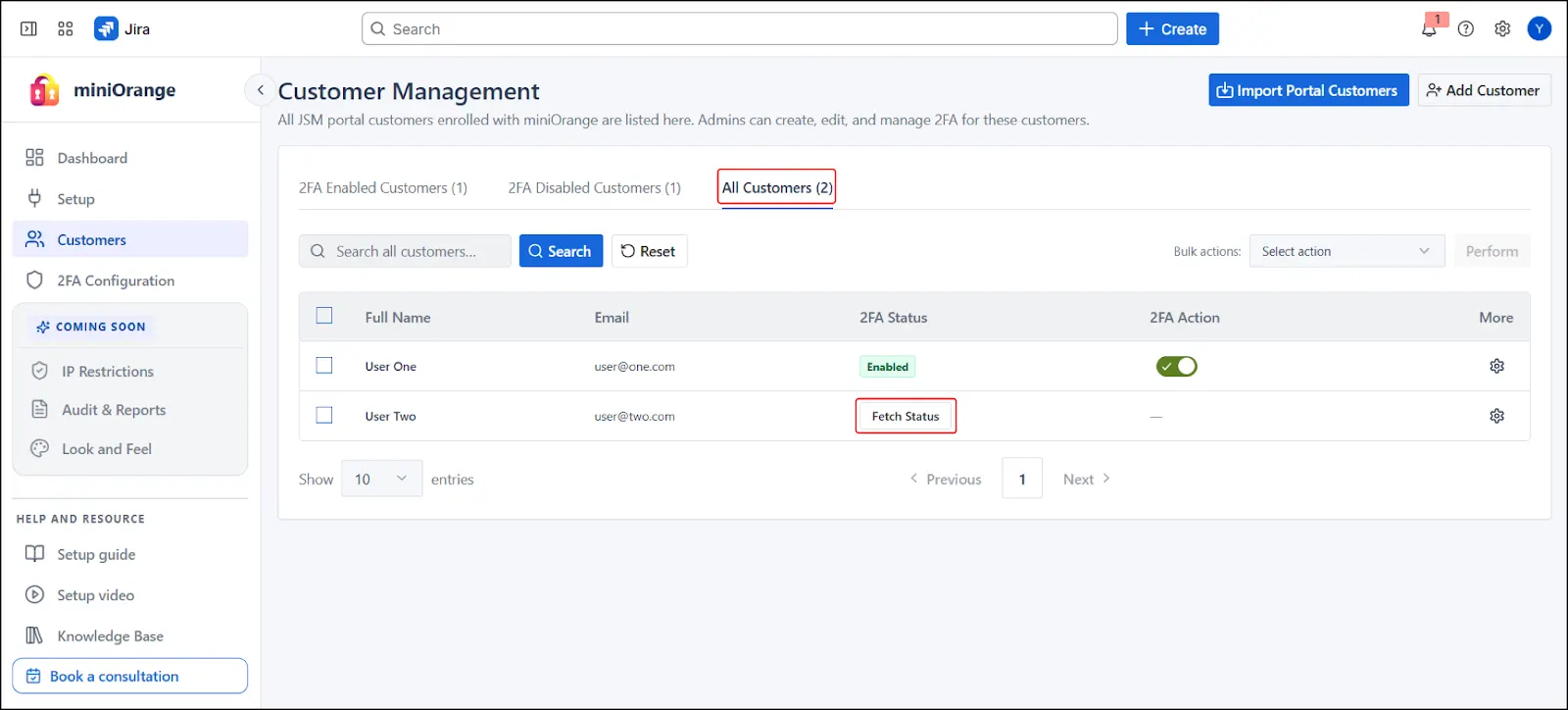
- Displays all customers, regardless of their 2FA status
- Includes an option (Fetch Status) to view 2FA status for each customers
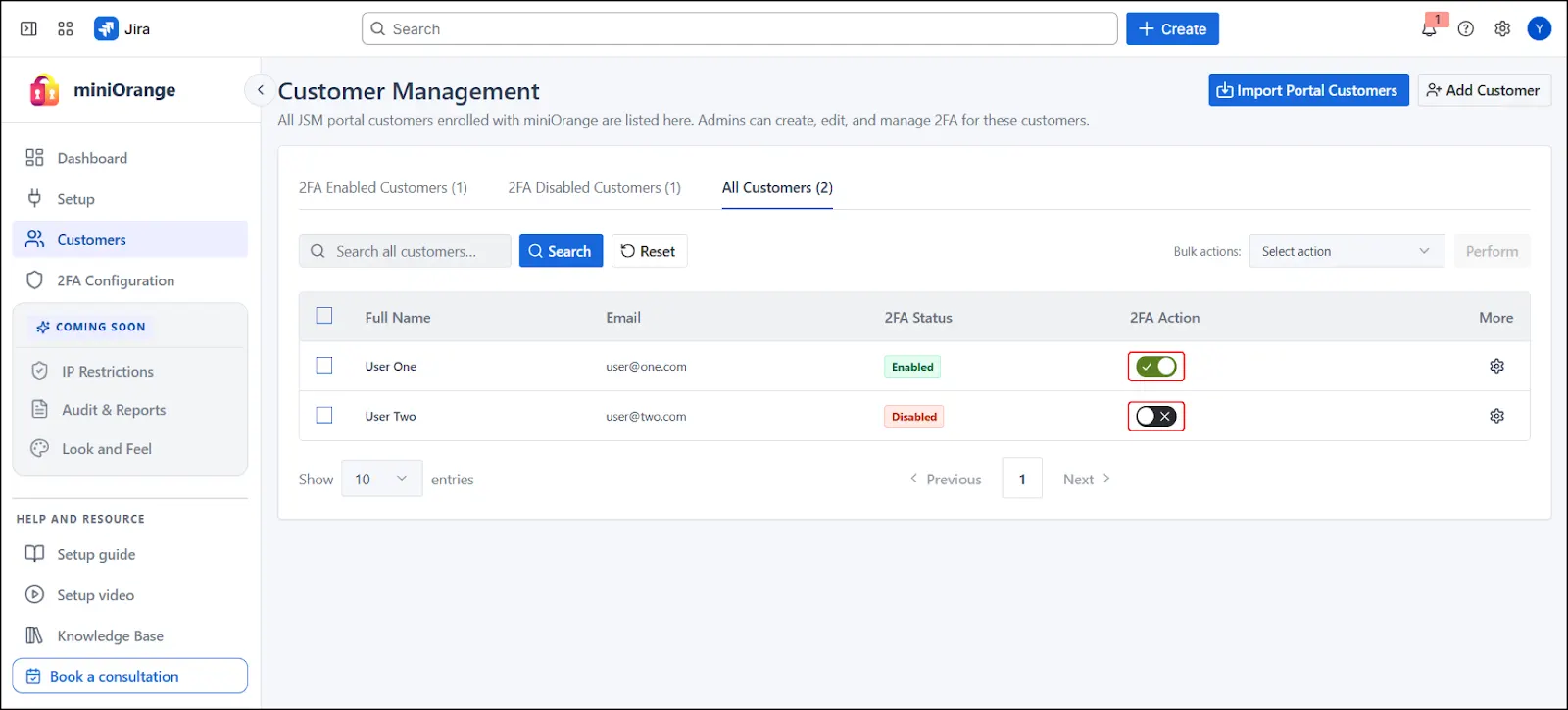
 5.4 Enable or Disable 2FA
5.4 Enable or Disable 2FA
2FA management is available from all three sub-tabs. However, actions available depend on the selected tab and current customer state.
Important Note (All Customers Tab)
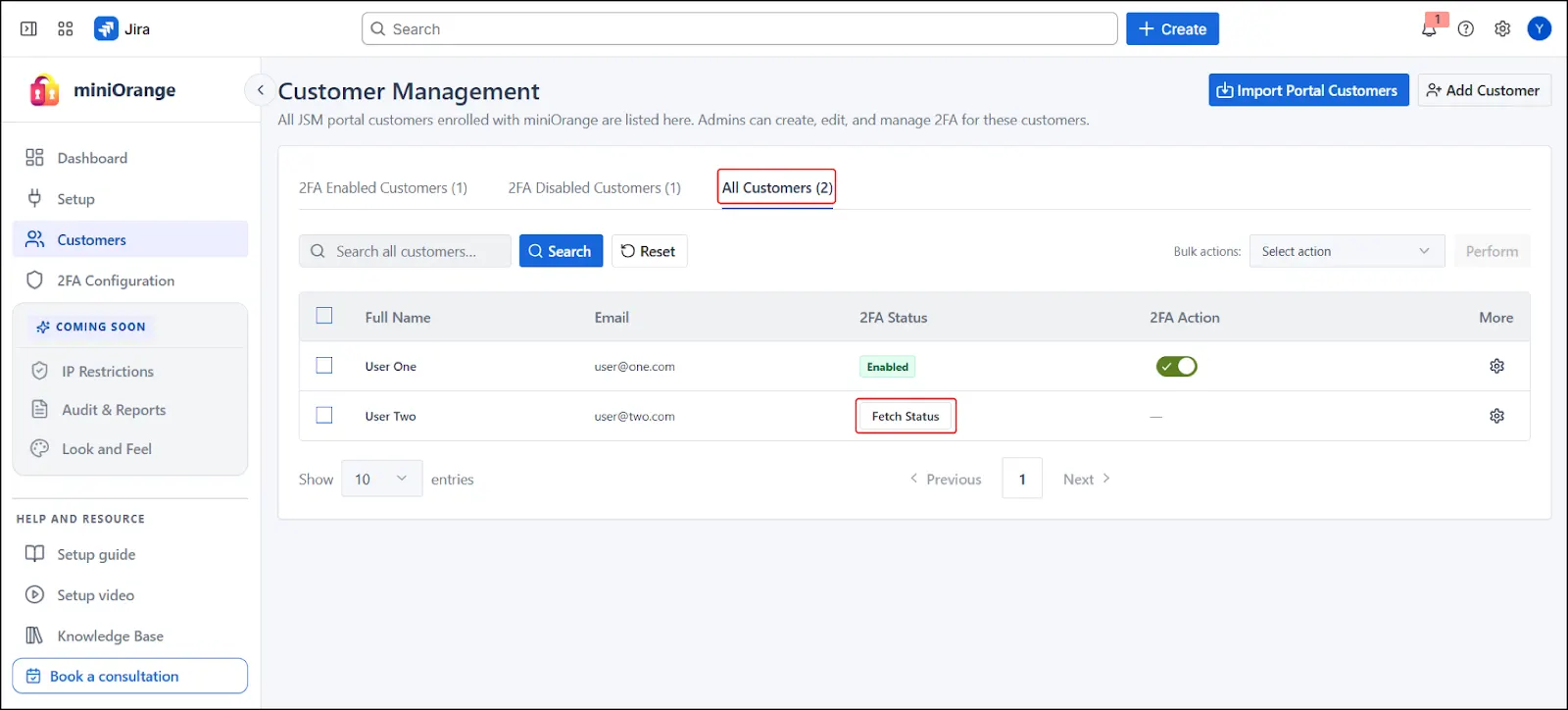
- 2FA status must be retrieved using Fetch Status before performing actions
- Enable/Disable actions become available after status retrieval
 5.5 Enable/Disable 2FA for Individual Customers
5.5 Enable/Disable 2FA for Individual Customers
Use the toggle switch under the 2FA Action column to control 2FA status for each customer.
- Toggle ON → Enables 2FA.
- Toggle OFF → Disables 2FA.
 5.6 Enable/Disable 2FA for Multiple Customers (Bulk Actions)
5.6 Enable/Disable 2FA for Multiple Customers (Bulk Actions)
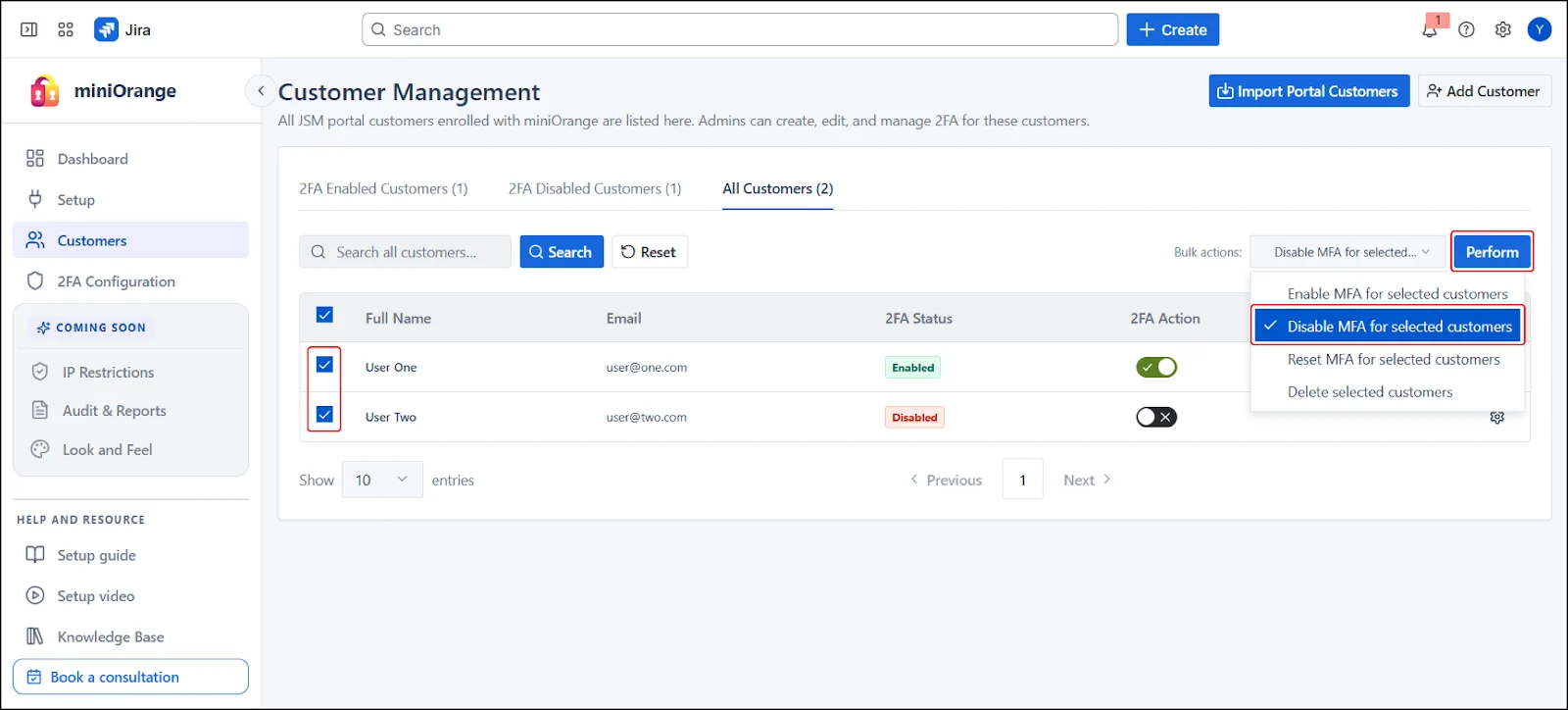
- Select Customers using the checkboxes
- Choose an action from the Bulk Actions dropdown
- Click Perform
Note : Tab-Based Action Restrictions
To prevent invalid operations, actions are restricted based on the selected tab:
2FA Enabled Customers Tab
- Only Disable 2FA action is available, Enable action is not applicable
2FA Disabled Customers Tab
- Only Enable 2FA action is available, Disable action is not applicable
All Customers Tab
- Both Enable and Disable 2FA actions are available
- Requires fetching 2FA status before performing actions
 5.7 Edit Customer Details
5.7 Edit Customer Details
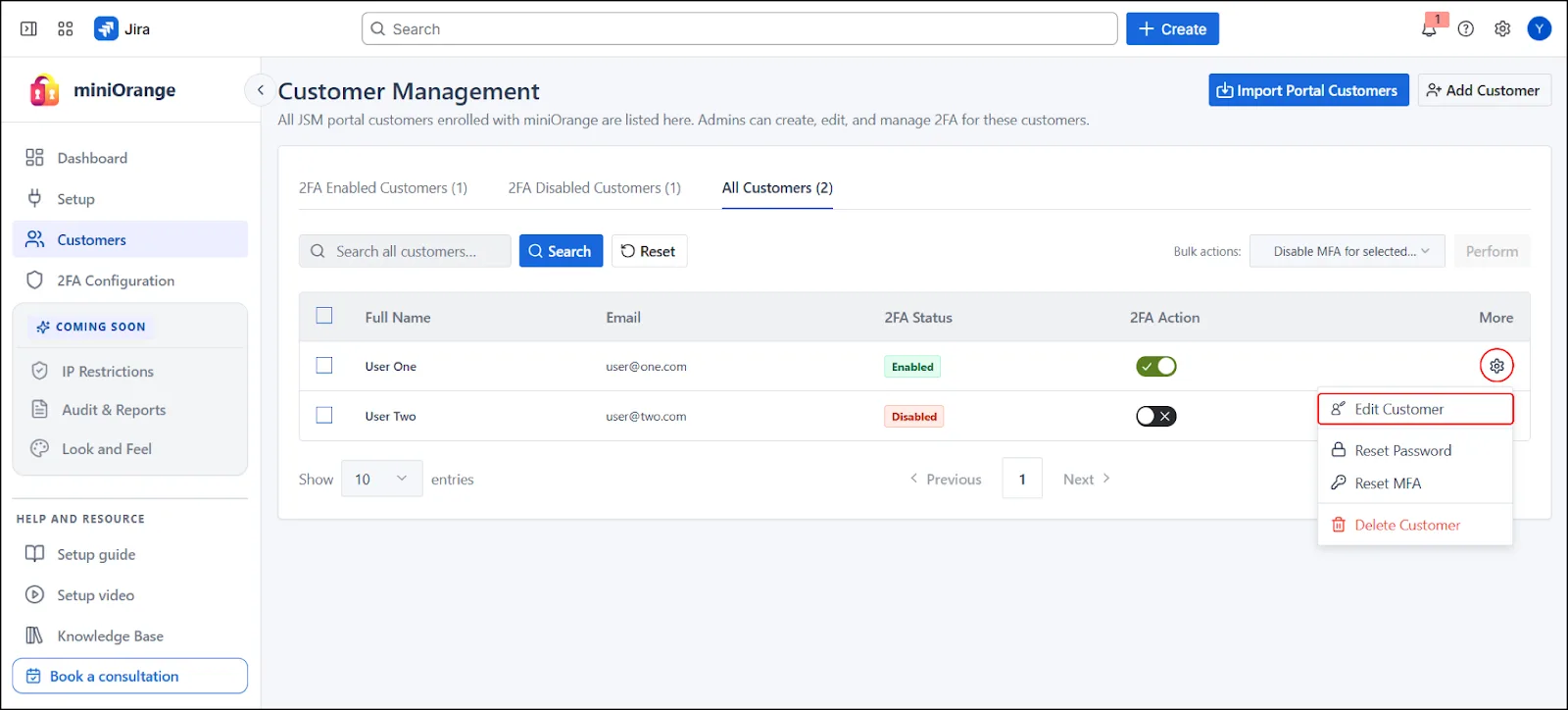
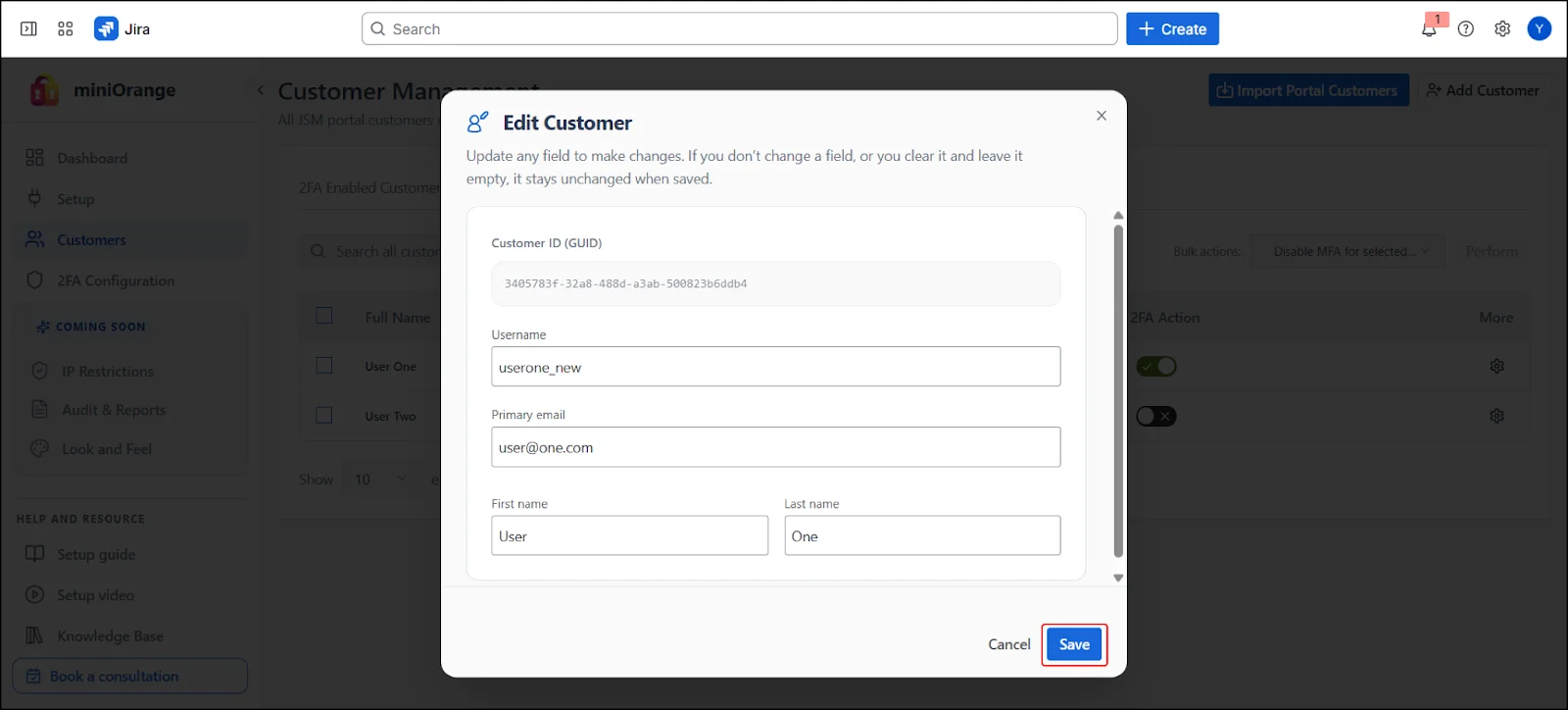
- Select settings (⚙️) icon next to customer entry
- Choose Edit Customer
- Update the required fields to modify the customer details
Note: Unmodified or cleared fields remain unchanged
 5.8 Reset Customer Password
5.8 Reset Customer Password
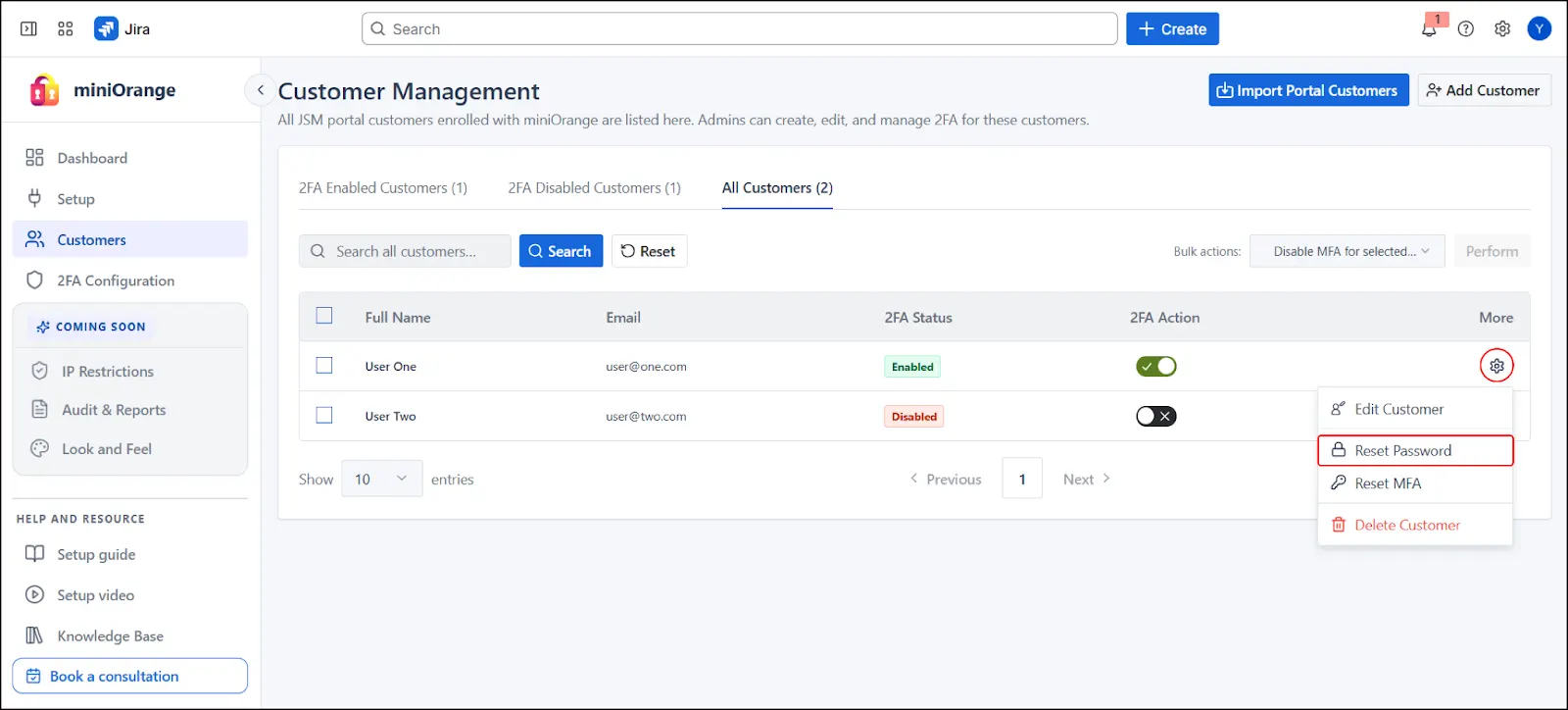
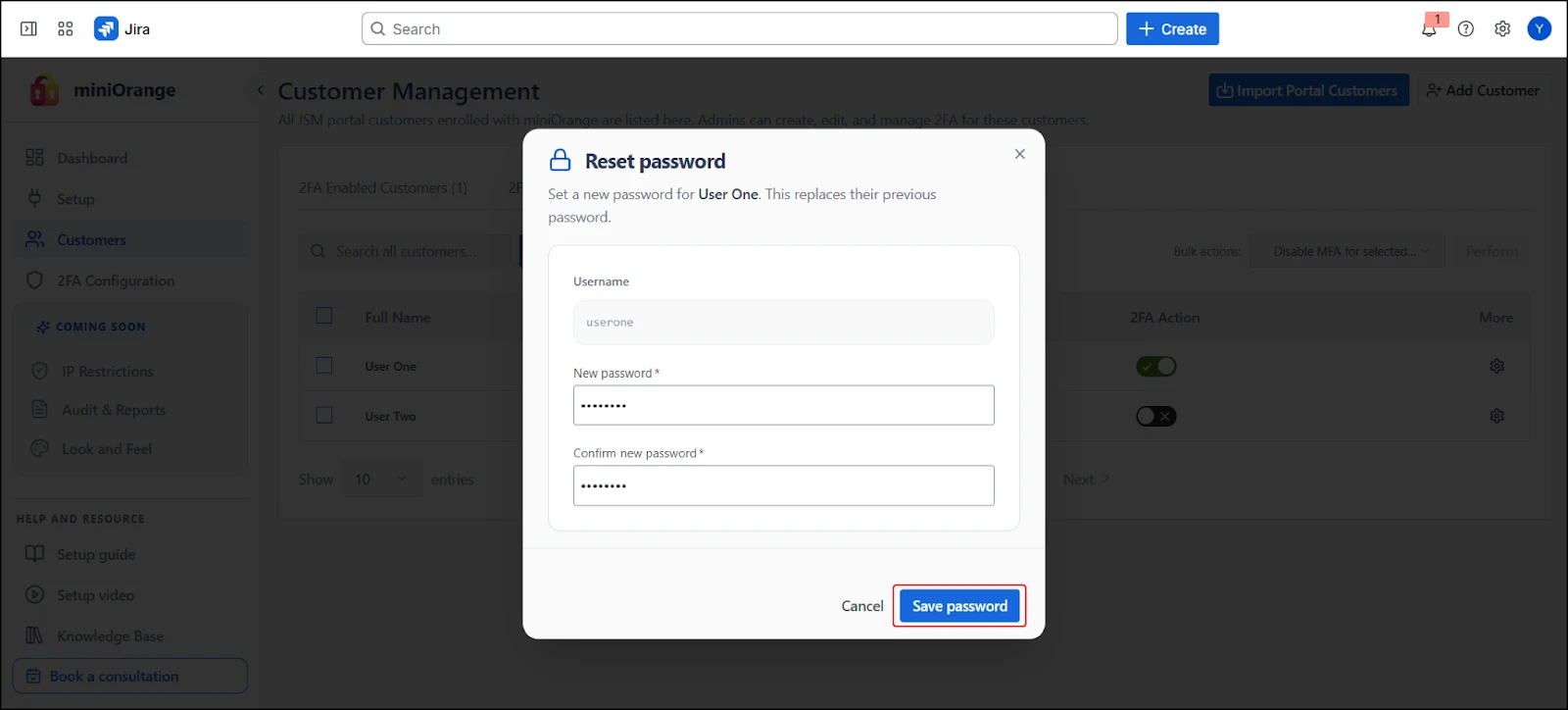
- Select settings (⚙️) icon next to customer entry
- Choose Reset Password
- In the modal dialog, enter and confirm the new password, then click Save Password
 5.9 Delete Customer
5.9 Delete Customer
9.A. Delete Individual Customer
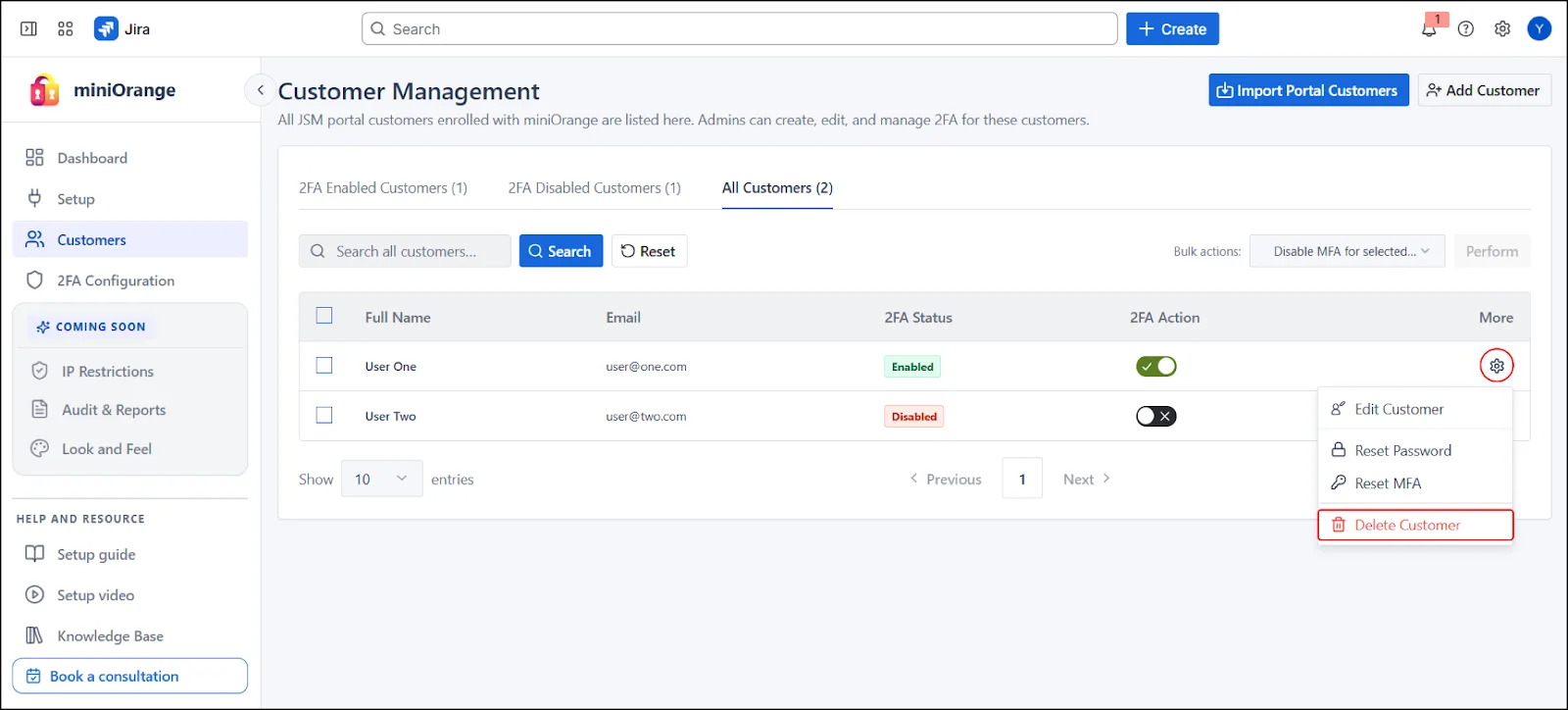
- Select settings (⚙️) icon next to customer entry
- Choose Delete Customer
- Confirm action
9.B. Delete Multiple Customers (Bulk Delete)
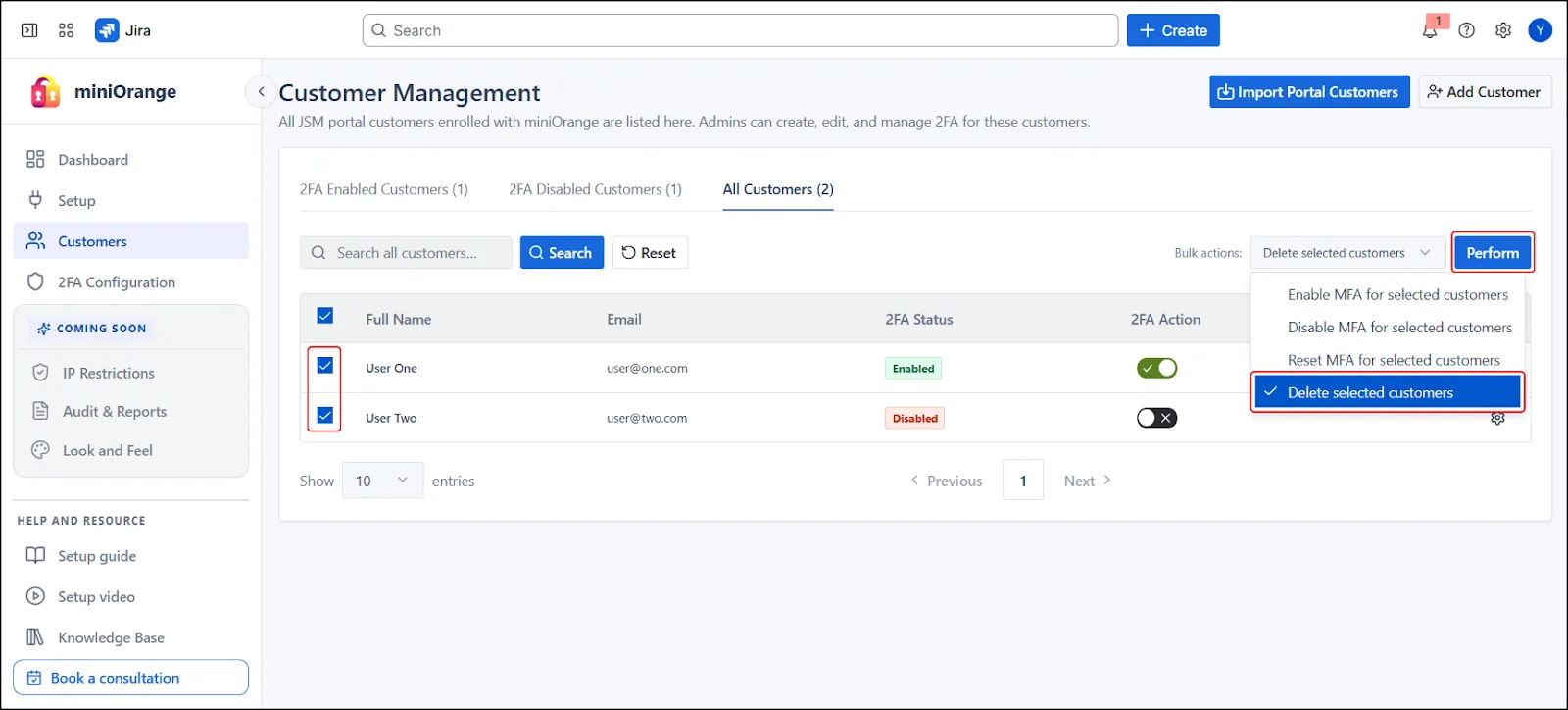
- Select multiple users using checkboxes
- Choose Delete Users from Bulk Actions
- Execute and confirm action
Note: This action permanently removes the customer and cannot be undone.
 5.10 Reset MFA
5.10 Reset MFA
10.A. Reset MFA for Individual Customer
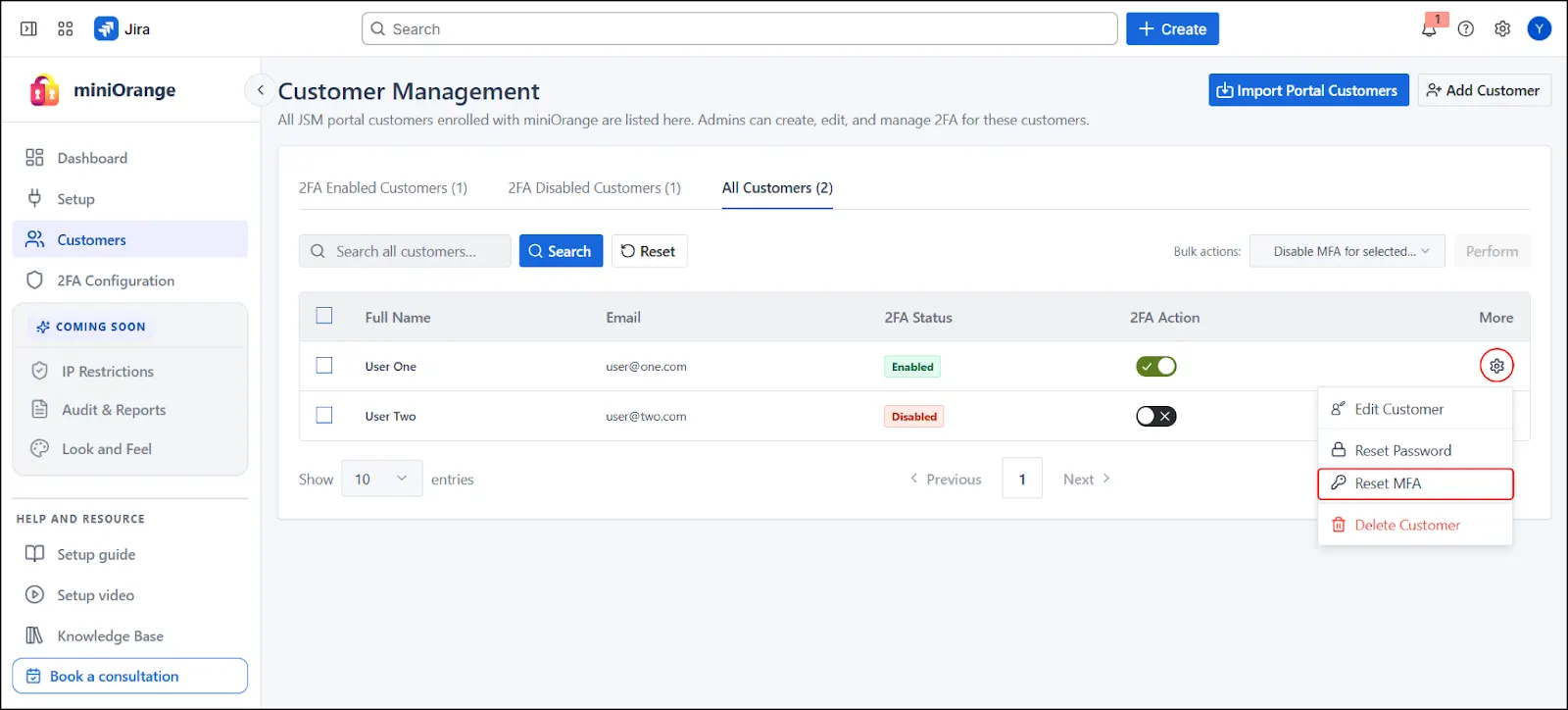
- Select settings (⚙️) icon next to customer entry
- Choose Reset MFA
- Confirm action
- MFA reconfiguration required on next login
10.B. Reset MFA for Multiple Customers (Bulk Reset)
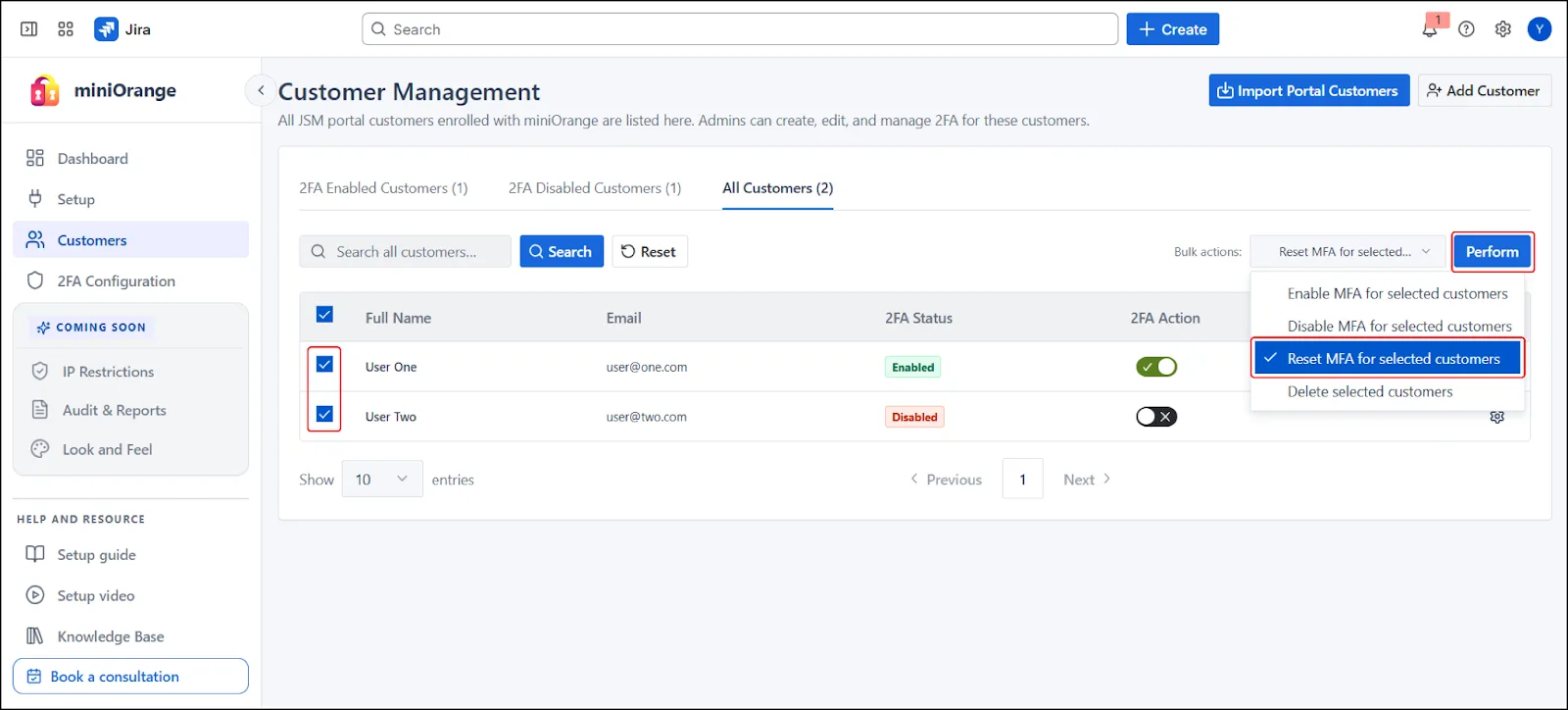
- Select multiple Customers
- Choose Reset MFA from Bulk Actions
- Execute and confirm
Note: This action removes existing MFA configuration and forces the customers(s) to set up MFA again on their next login.
 5.11 Search Customers
5.11 Search Customers
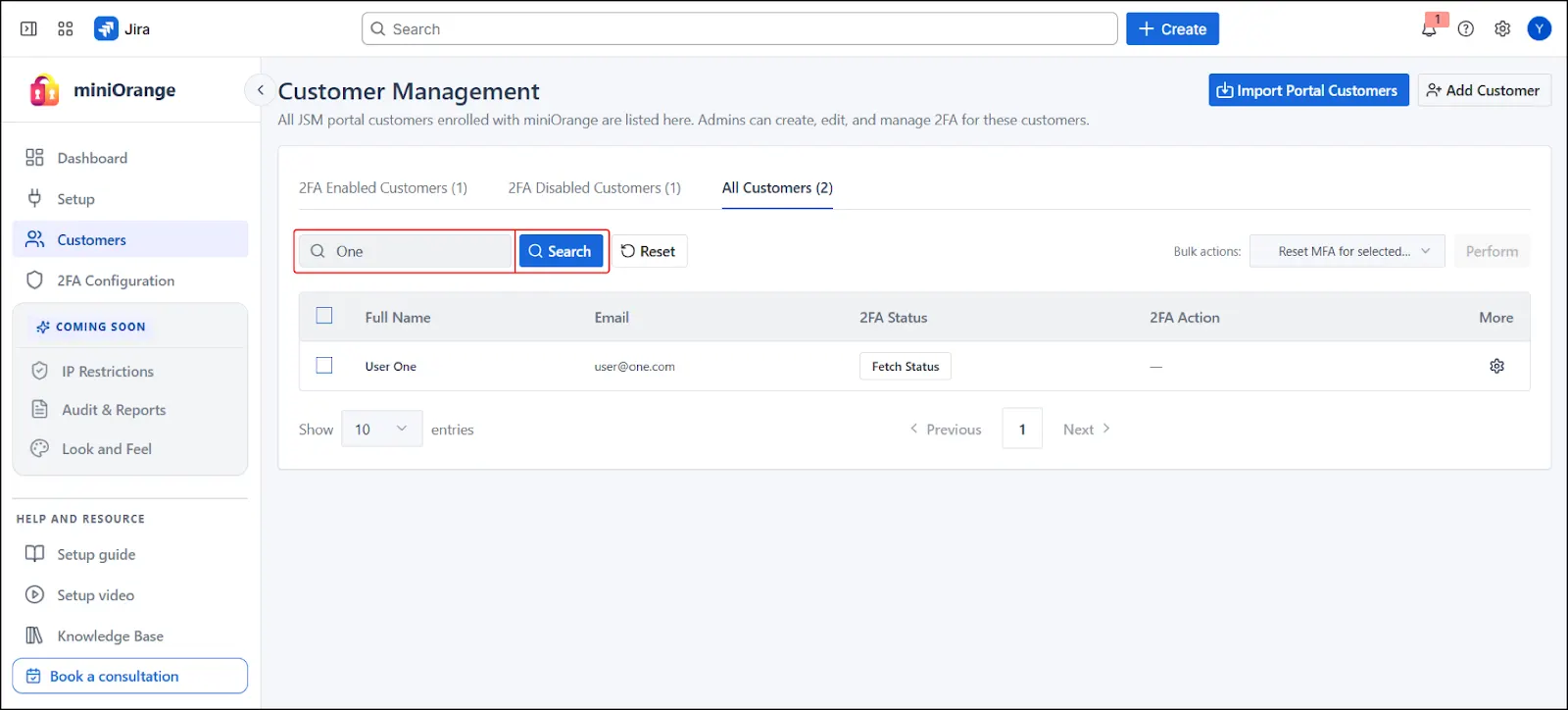
- Use the search bar to locate customers by:
- Name
- Search behavior depends on active tab:
- Enabled/Disabled tabs → filtered results based on 2FA status
- All Customers tab → Shows All Customers irrespective of their 2FA Status
If no results are found in a sub- tab, switching to All Customers provides complete visibility.
Additional Resources
Did this page help you?

 Try it for free
Try it for free