Around 97% of the identity attacks are password-based, and they are just surging. Low-and-slow attacks are redefining how breaches happen today, and password spraying attacks sit right at the center of that shift.
Instead of triggering alarms, these attacks quietly exploit weak identity controls, making identity-first security a business necessity rather than an option.
What Is a Password Spraying Attack in Cybersecurity?

A password spraying attack is a technique where an attacker tries a single commonly used password across multiple user accounts instead of trying many passwords on a single account. This cybersecurity attack is designed to avoid account lockouts and detection mechanisms that traditional brute force attacks often trigger.
A password spraying attack in cybersecurity is a low-noise authentication attack that targets human behavior rather than system vulnerabilities. The hackers simply rely on the fact that users reuse and use the same set of passwords, such as “Password123” or “12345678.”
What are the Tactics Used for Password Spraying?
Some of the common tactics used for password spraying by the attackers include:
- Exfiltration: Once a password-spraying attack successfully compromises an account, attackers quietly explore email, cloud storage, and internal applications to identify valuable data they can steal.
- Trying Common Passwords: Attackers rely heavily on lists of common or default passwords, such as “Password123,” “Welcome1,” or seasonal variants like “Spring2026!,” and systematically try these across many accounts.
- Social Engineering: To improve their success rate, attackers may first use social engineering attacks to learn more about employees, internal culture, and naming conventions, which helps them guess credentials more accurately.
- Intelligence Gathering: Before launching a spraying attack, adversaries perform reconnaissance to build a high-quality list of targets and context-aware guesses. They mine LinkedIn, company websites, data breach dumps, and OSINT sources to enumerate usernames, understand email formats, and tailor password guesses to the organization’s location, industry, and culture.
How is Password Spraying Different from Brute Force and Credential Stuffing Attacks?
Understanding how password spraying differs from related attacks is crucial for effective defense.
| Attack Type | Noise Level | Primary Target | Lockout Risk | Defense Efficacy |
|---|---|---|---|---|
| Password Spraying | Very Low | Many accounts | Low | Poor |
| Brute Force | Very high | Single account | High | Good |
| Credential Stuffing | Medium | Known credential pairs | Variable | Moderate |
This difference explains why organizations focused solely on defeating brute force and credential stuffing often remain dangerously exposed to spraying campaigns. The attack doesn’t fail against your defenses; it simply walks around them.
Business Impact: Why Password Spraying Hurts More than You Think
Password spraying is a business risk with tangible consequences that ripple through operations, finances, and market perception.
1. Data Security Risks
This is the most dangerous risk. Because after gaining initial access, hackers are likely to look for crucial data.
Here’s what a hacker would normally do after gaining initial access to a low-risk account:
- Harvest internal email for phishing templates, only to target executives.
- Get hold of customer data and intellectual property data.
- Escalate privileges through unpatched systems or misconfigured cloud permissions
2. Reputation Damage
B2B relationships thrive on trust. When clients learn their data was exposed due to weak password hygiene at your organization, confidence erodes rapidly.
Unlike ransomware (which announces itself loudly), spraying breaches often emerge months later during forensic audits, forcing companies to disclose preventable failures that make them look negligent. This can trigger contract penalties, delayed renewals, and lost enterprise deals.
3. Financial Loss
Password spraying is responsible for huge financial losses to businesses.
The direct costs are:
- Incident response expenses
- Potential ransomware payments
- Regulatory fines and penalties
Indirect costs are:
- Increased insurance premiums
- Customer churn
- Opportunity costs
These financial losses may be hard to recover from; it is even more difficult for small and medium-sized enterprises to do so.
4. Compliance Adherence
Frameworks like GDPR Article 32, HIPAA, and ISO 27001 A.9.2.3 mandate strong access controls.
A successful spraying attack often reveals gaps in password policies, MFA coverage, or monitoring, turning a security incident into a compliance violation.
For publicly traded companies, this can mean material weaknesses in SOX 404 disclosures or SEC cybersecurity risk disclosures, impacting investor confidence.
Warning Signs: Is Your Organization Under Spray Attack?
Password spraying avoids dramatic alerts, but subtle patterns emerge in authentication logs if you know where to look:
- Geographic Anomalies: Login attempts from countries where you have no offices or remote workers.
- Temporal Clustering: Spikes in failed logins at 2:00 AM local time across multiple unrelated accounts.
- Password Repetition: The same weak password (e.g., “Welcome1!”) failing across 50+ accounts in one hour.
- Successful Anomalies: Legitimate-looking logins followed by immediate access to unusual resources (e.g., a marketing user querying financial databases).
- SSO Irregularities: Multiple failed SAML authentications from unfamiliar IP addresses targeting your identity provider.
These signs often appear in isolation, a few failed logins here, a weird login there, which is why they get overlooked.
Organizations that correlate authentication data with contextual factors (user role, device, location) detect spraying 3-5 times faster than those relying solely on threshold-based alerts.
Anatomy of an Attack: How Password Spraying Attacks Actually Work
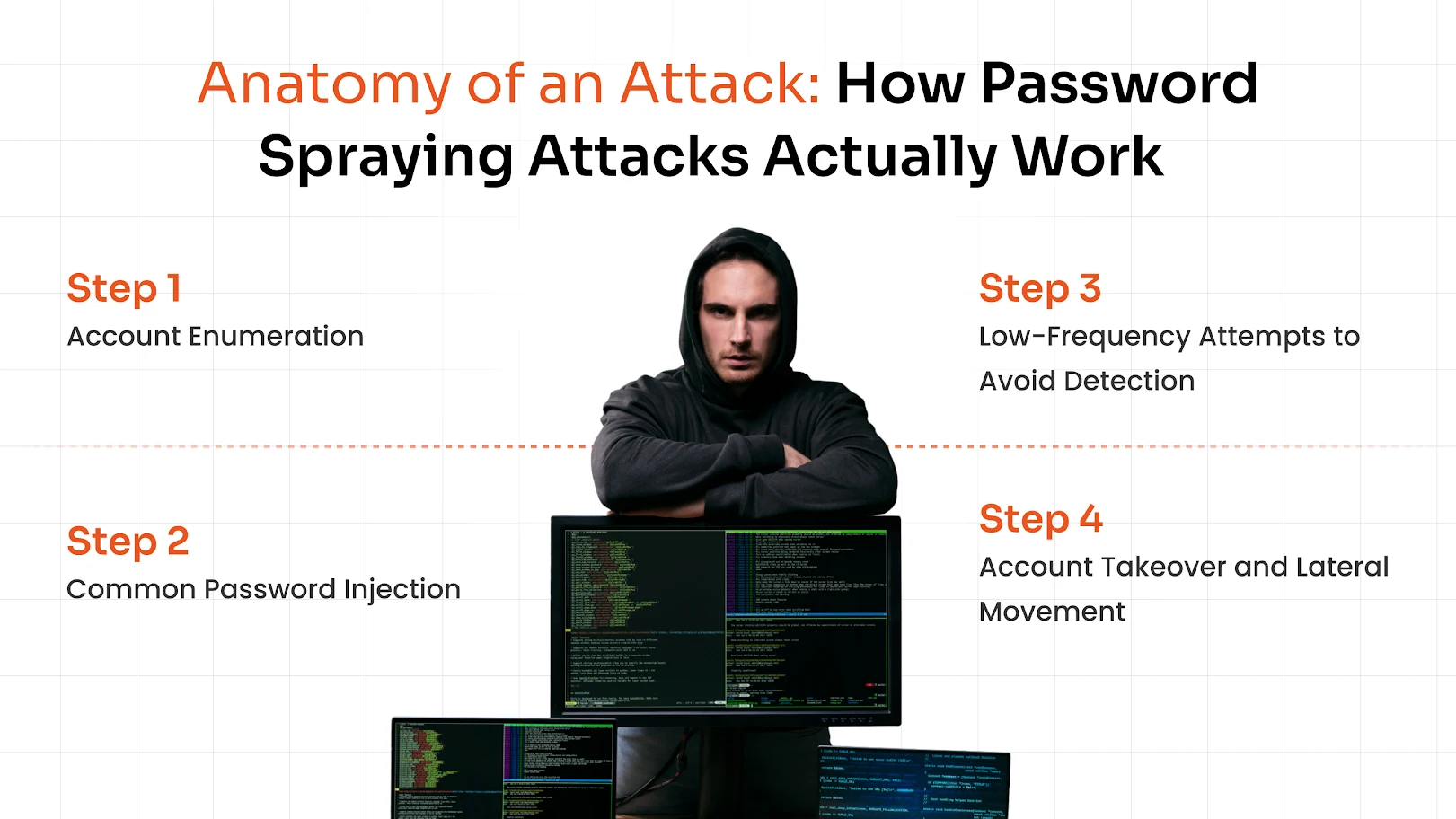
Understanding the attacker workflow helps defenders spot intervention points. Here’s how a typical spraying campaign unfolds based on real-world incident response reports:
Step 1: Account Enumeration
Attackers gather valid usernames and passwords via low-risk methods such as:
- Searching LinkedIn for employee names and standard email addresses.
- Guessing common aliases, e.g., support, admin, or information at your domain.
- Checking breach collections for previously exposed corporate accounts.
Step 2: Common Password Injection
Using breached password lists or human behavior databases, attackers select 1-3 high-probability passwords.
These aren’t random; they’re curated based on:
- Cultural events like holidays or major sporting events.
- Company-specific terms, taken from job posts or press releases.
- Seasonal trends
Step 3: Low-Frequency Attempts to Avoid Detection
Rather than hammering accounts, attackers space out their tries deliberately:
- Copying business hour activity patterns
- Rotating through IP addresses to avoid rate limits
- One attempt per account every 2-4 hours
Step 4: Account Takeover and Lateral Movement
Once access is gained (even to a low-privilege account), attackers:
- Search for crucial information in email, SharePoint, and more places.
- Attempt privilege escalation via unpatched vulnerabilities.
- Enroll their own device if possible.
- Use the initial foothold to internally spray high-value accounts.
Detection and Response: What to Do After a Password Spraying Attempt
Speed matters in password spraying incidents. The average dwell time for identity-based attacks exceeds 200 days, giving attackers ample time to establish persistence.
Here’s your action plan:
- Detect Abnormal Login Patterns: Make use of User and Entity Behavior Analytics (UEBA) to spot impossible login attempts, for e.g. from NYC or London. Or look at repeated failures from analyzing networks.
- Force Password Resets: Immediately reset passwords for all accounts showing spraying indicators; don’t wait for confirmation.
- Revoke Sessions: Invalidate all active tokens and sessions for compromised accounts to kick out attackers.
- Audit Access Logs: Trace lateral movement from the initial foothold, check for abnormal data access or privilege changes.
- Block Malicious IPs: Temporarily block source IPs while investigating.
- Notify Affected Users: Transparently explain the incident and required actions; secrecy erodes trust.
Most importantly, treat spraying as a symptom, not the event. Investigate why the initial compromise succeeded: Was MFA missing? Were passwords too weak? Did monitoring gaps allow the spray to continue undetected?
Why Traditional Authentication Methods Fail Against Password Spraying

Legacy, aka traditional, authentication architectures were built for a different threat model – one where attackers guessed passwords loudly and locally. They contain inherent blind spots that spraying exploits:
- Password-only Authentication Flaws: Relies on users creating strong passwords, which often fail in practice.
- Static Login Thresholds: Systems locking accounts after 5 failed attempts fail against spraying because attempts are distributed.
- Lack of Context-aware Validation: Traditional systems validate credentials in isolation. They don’t ask: Is this login from the user’s usual location? On their registered device? During their typical work hours? Without this context, spraying attempts look like legitimate user errors.
These gaps make traditional authentication methods ineffective against spray attacks in cybersecurity scenarios.
Building Your Defense: Proven Prevention Strategies
Stopping spraying requires moving beyond password complexity rules to layered identity controls. Here’s what works in practice:
1. Strong Password Policy
If done right, this can prove to be a strong prevention method.
Complex passwords drive users to write them down, instead:
- Encourage passphrases (CorrectHorseBatteryStape!) over complex gibberish
- Prioritize the length (12-14 characters)
- Screen new passwords against breached lists
2. Account Lockout and Rate Limiting
Move beyond static thresholds:
- Implement IP-based locking after 10 failures from one address (this prevents brute force attacks).
- Lock accounts only after failures + anomalous context (like new country, odd time).
- Increase wait time after each failed attempt (this avoids spraying efficiency).
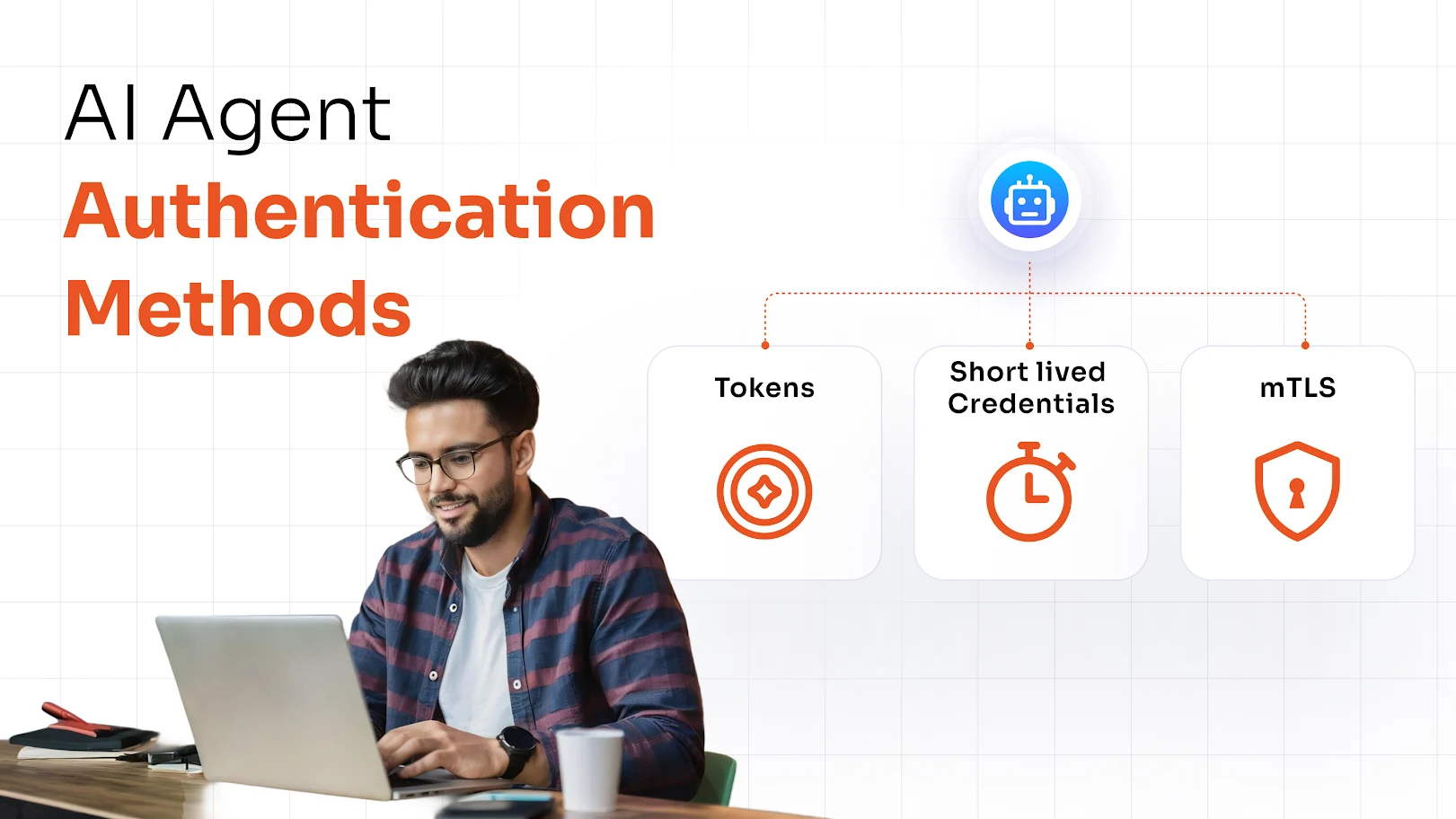
3. Integrate Passwordless Authentication Methods
This helps to eliminate the password attack surface for high-risk access:
Implement passwordless authentication methods like:
- Biometric authentication
- FIDO2 security keys
- Magic links, passkeys, and push notifications
- Grid pattern matching
- Hardware tokens
Inculcate these methods on accounts and remote access, where spraying does the most damage.
4. Opt for MFA/2FA Solution
A multi-factor authentication (MFA) security solution stops spraying if implemented correctly. Basic SMS-based OTPs help but remain vulnerable to SIM swapping and real-time phishing.
For true spraying resistance:
- Require MFA for all access points and not just VPN.
- Prioritize phishing-resistant methods such as passkeys, FIDO2, grid pattern matching, and more.
- Ensure MFA covers legacy protocols (IMAP, POP, ActiveSync) often abused in spraying.
5. Threat Intelligence Tools for Response and Detection
Deploy AI-based tools that can help to:
- Detect compromised credentials and create alerts when corporate emails appear in new breaches.
- Anomaly detection, which spots suspicious behavior with the help of AI.
- Malicious IP reputation feed that blocks known spraying botnets.
6. Strategic IP Whitelisting
This is how you can do it for businesses:
- Restrict SSO/VPN access to known corporate IP addresses.
- Implement geo-fencing for high-sensitivity systems.
- Use conditional access to require stronger authentication from unexpected locations.
7. A Zero Trust Approach
Stop trusting networks; verify every request:
- Assume Breach: Treat internal networks as untrusted
- Verify Explicitly: Authenticate and authorize based on all available data points
- Least Privilege Access: Give users only what they need for their role.
This framework inherently limits spraying’s impact by containing the blast radius.
How MFA Stops Password Spraying But Only If Done Right
MFA is the single most effective control against password spraying, but implementation flaws create dangerous illusions of security.
Why Basic MFA Is Not Enough
SMS and voice call MFA fail against determined attackers:
- Real-time phishing: Attackers proxy login sessions, capturing both password and One-Time Passwords (OTP) in real time.
- SIM Swapping: Social engineering convinces carriers to port a victim’s number
- SS7 Exploits: Intercepting SMS via telecom protocol weaknesses (less common but possible).
In these scenarios, MFA adds steps but doesn’t stop the account takeover; it just changes the attack vector.
Phishing-Resistant MFA Solution: The Better Approach
For true spraying immunity, deploy methods resistant to interception and replay:
- Passkeys: Use FIDO-based public key cryptography instead of passwords, so there is no shared secret for attackers to steal or phish.
- Grid Pattern Matching: Prompts users with a randomized numeric grid and verifies a secret pattern known only to the user. Because the numbers change on every login and only the pattern matters, captured screens or keystrokes are useless, making phishing and replay attacks extremely difficult.
- FIDO2 Security Keys: Hardware-based authenticators that store private keys in secure hardware and sign challenges locally, never exposing the key to the server or browser.
- Hardware Tokens: Physical devices that generate or hold cryptographic secrets used for authentication, often compliant with FIDO2 or PKI standards.
- Biometric Authentication: Uses unique traits such as fingerprints or facial recognition. Biometric data never leaves the device and is used only to unlock the cryptographic key, which prevents attackers from reusing captured biometric information on phishing sites.
Adaptive/Risk-Based MFA Solution: A Concrete Solution
Risk-based authentication solutions evaluate contextual factors in real time to determine authentication strength. Instead of asking “Is the password correct?” they ask: How confident are we that this is the legitimate user?
Contextual signals checked include:
- User behavior patterns (typical login times, locations, devices)
- Device
- Geolocation
- IP address
- Time
So, Adaptive MFA checks multiple accounts from the same IP attempting login at unusual hours; repeated failures with the same password across disparate user roles; successful logins from new countries followed by immediate access to atypical data.
Based on this, it spots potential spraying attacks and stops them.
Layered Defence: IAM and PAM Working Together
No single tool stops spraying. True resilience comes from integrating identity controls into a cohesive defense-in-depth strategy:
When Identity and Access Management (IAM) and Privileged Access Management (PAM) work together, they create a layered identity security stack that makes password spraying much harder to pull off and far less damaging if it succeeds.
IAM sits at the center, defining who your users are, what they should access, and enforcing policies like least privilege.
PAM then adds a deeper layer of control around your highest-risk accounts, such as domain admins or database owners, by vaulting privileged credentials, requiring strong MFA to use them, and recording or monitoring sensitive sessions.
Final Takeaway: Identity Security Is the New Perimeter
Password spraying succeeds not because of sophisticated zero-days, but because organizations still treat authentication as a checkbox exercise rather than a continuous identity verification process. The attack works when password policies are theoretical, MFA is partial, and monitoring ignores context.
The organizations that withstand spraying campaigns aren’t those with the most expensive tools; they’re the ones that understand identity as the foundation of trust.
They enforce MFA everywhere, monitor for behavioral anomalies, and design systems where stealing a password is like stealing a key to one room in a skyscraper: useful for that room, but nowhere near enough to take the building.
Connect with the miniOrange security expert for a solid strategy and solution to evade password spraying attacks at your organization.
FAQs
Can MFA stop password spraying attacks?
Yes, a strong MFA security solution can block unauthorized access even if passwords are compromised, especially when using phishing-resistant methods.
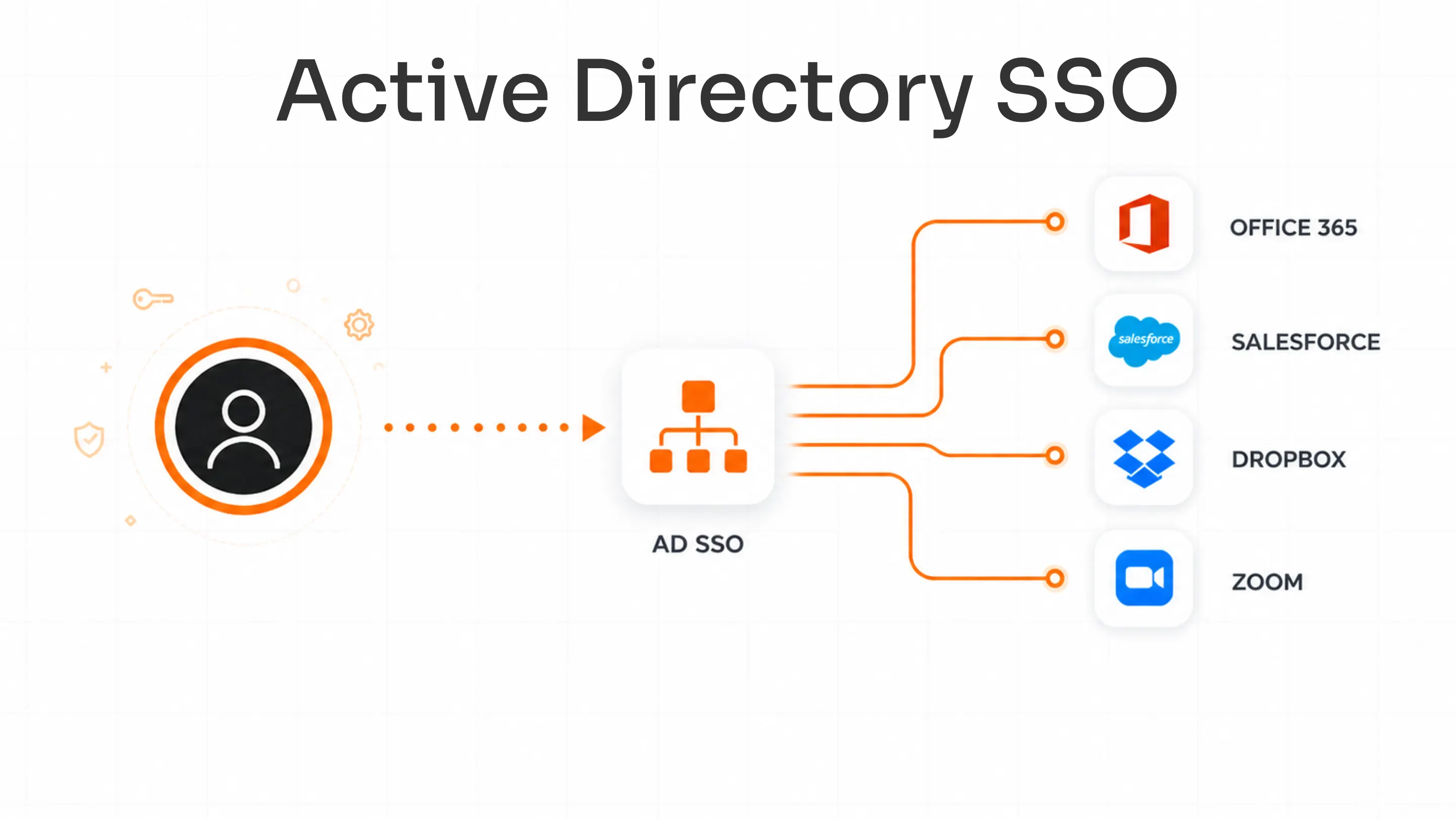
Why is SSO risky in password spraying attacks?
SSO solution centralizes access, so if one account is compromised, attackers may gain access to multiple systems, increasing the attack impact.
What is the best defense against password spraying?
The best defense includes a combination of a strong adaptive MFA solution, passwordless authentication, and continuous monitoring.
Leave a Comment