SAML Single Sign On (SSO) Into Crowd Using RSA SecureID
Crowd SAML app gives the ability to enable SAML Single Sign-On for JIRA, Confluence, Bitbucket, Bamboo, Fisheye, and other connected applications from any SAML Identity Providers. Here we will go through a guide to configure SSO between Crowd and Identity Provider. By the end of this guide, your users will be able to SSO into Crowd.
Pre-requisites
To configure your Identity Provider integration with Crowd SAML SSO, you need the following items:
- Crowd should be installed and configured.
- Admin credentials are set up in Crowd.
Pre-configurations to make SSO work
- Navigate to Applications->Crowd->Directory and Group and make sure user is allowed to authenticate (This is not needed in the premium plugin).
- Navigate to Application->Crowd->Remote address and make sure Crowd server's IP Address is configured here.
- If you are using Crowd Server/Datacenter version 4.3.0 and above, please navigate to Applications->Crowd->Options. Select Allow to generate user tokens option and Save it.
Download and Installation
- Log into your Crowd instance as an admin.
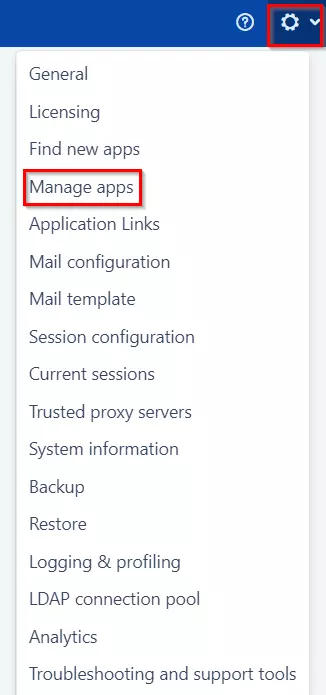
- Navigate to the Administration menu and Click Manage Apps.
- Click Find new apps or Find new add-ons from the left-hand side of the page.
- Locate SAML Single Sign-On for Crowd via search and click on install.
- Log in to the Crowd Admin console.
- Navigate to Administration > Manage Apps.
- Click on the Upload App and upload the jar file.
- Now, click on the Configure button. You will be asked to verify the miniOrange credential and license key.
Plugin Activation
B.a Plugin Activation with Online License- Navigate to Crowd Admin Console → Manage Apps.
- Click on the Configure button of the miniOrange Crowd SAML SSO plugin.
- Log in with your miniOrange account. Once authenticated, you will be prompted to enter the license key.
- Enter the license key and click on the verify button.
- You will be provided license for activation.
- Navigate to Crowd Admin Console → Manage Apps.
- Click on the Configure button of the miniOrange Crowd SAML SSO plugin.
- Click on Choose File button under the Upload your license File here section.
- Upload the license key and click on the Verify button.
Step 1: Set Up RSA SecurID as Identity Provider
All the information required to configure RSA as Identity Provider i.e. plugin’s metadata is given in the Service Provider Info tab of the miniOrange SAML plugin.
- Login to the RSA Secure ID as Super Admin.
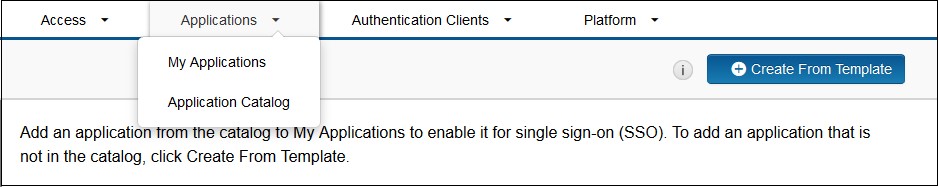
- In the Administration Console, click Applications → Application Catalog.
- Click Create From Template button on the top right corner.
- Next to the SAML Direct, click the Choose Connector Template page. The Add Connector wizard appears.
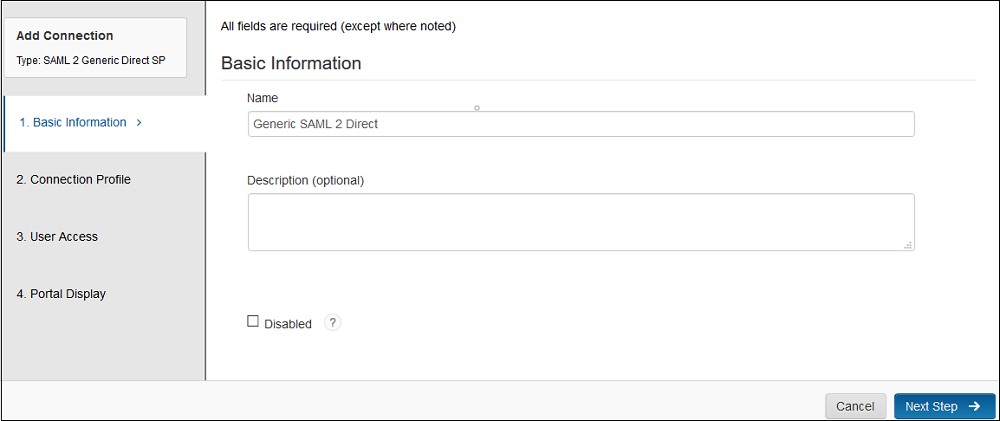
- Fill the required information in the Basic Information page on the Add Connector wizard.
- Name:- Name of the application for eg. miniOrange Plugin.
- Description (Optional):- Description for your application.
- Disabled [a checkbox] (optional): Select this only if you want to make this application unavailable to users. When disabled, the application appears in My Application but does not appear in the RSA application portal.
- Click Next Step button.
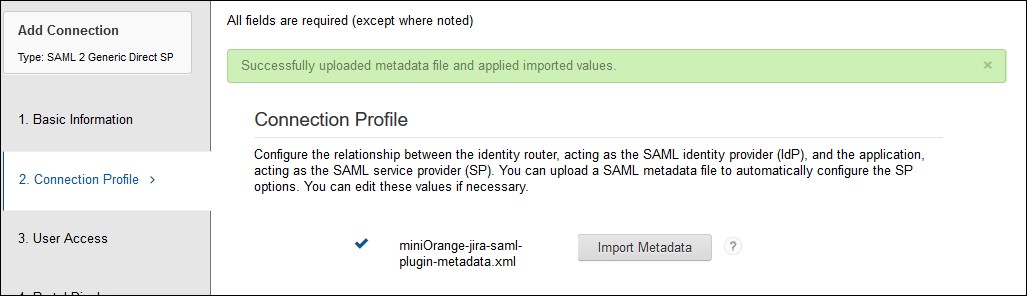
- Fill the required information in the Connection Profile page.
- Upload the miniOrange plugin’s metadata file and click on the Import Metadata button. You can obtain plugin metadata from the Service Provider info tab of the plugin.
- Verify the configured URLs and clicks on the Save button on the top right corner of the pop-up window.
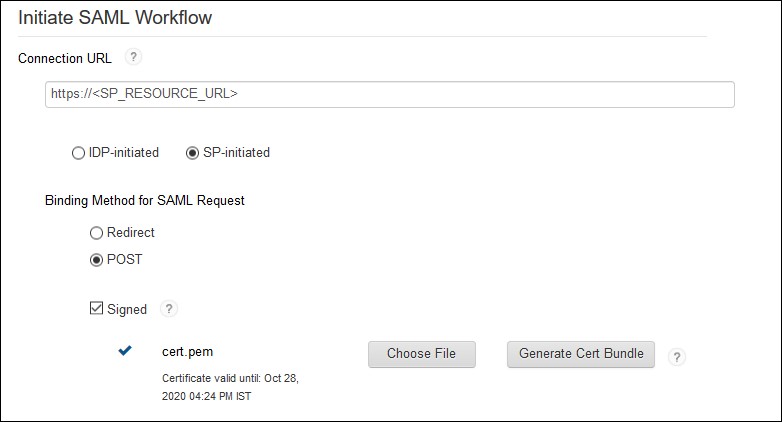
- Select SP-Initiated, if you want the SSO should be invoked from application or select IDP-initiated, if you want the user should log in into RSA first and then access application from his RSA Dashboard.
- Configure base URL of your application as Connection URL or you can leave it blank if IDP-initiated is selected.
- Select Binding type: POST and Signed option as Checked.
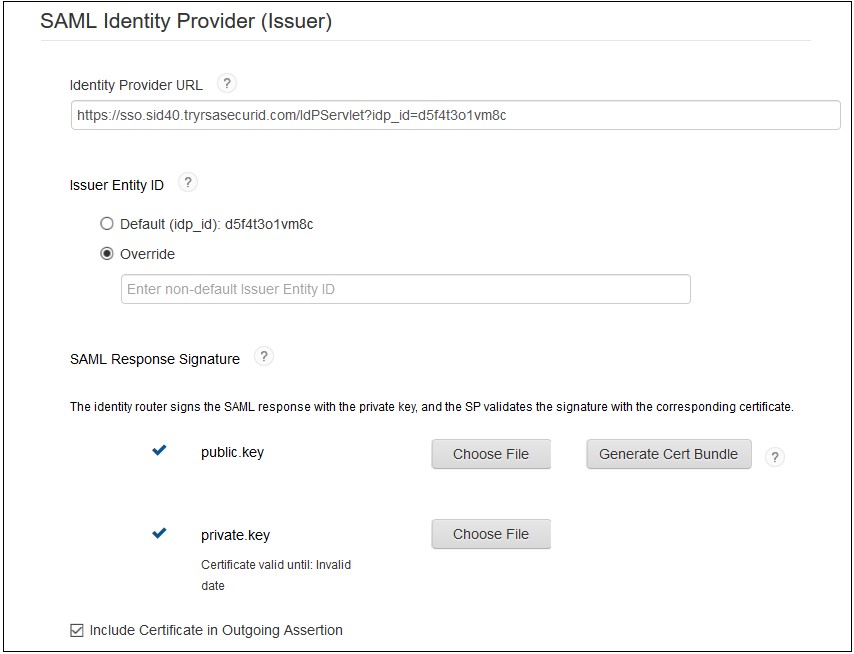
- Upload the public and private key which will be used to signed SAML response or you can generate new key pair by clicking on the Generate Cert Bundle button.
- (Optional) Enable checkbox for Include Certificate in Outgoing Assertion.
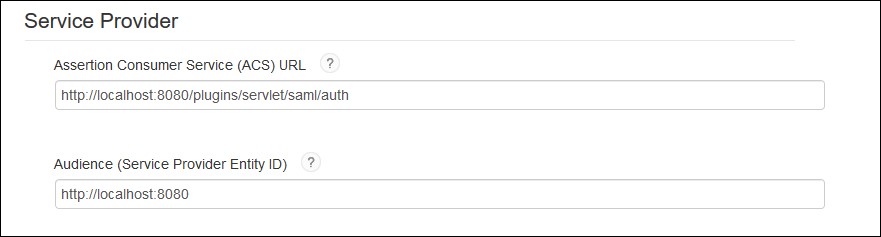
- Assertion Consumer Service URL and Audience URL should be preconfigured if you have uploaded plugin’s metadata in the Connection Profile section. If not, you can find the required URLs from Service Provider Info tab of the miniOrange SAML plugin and update the URL here.
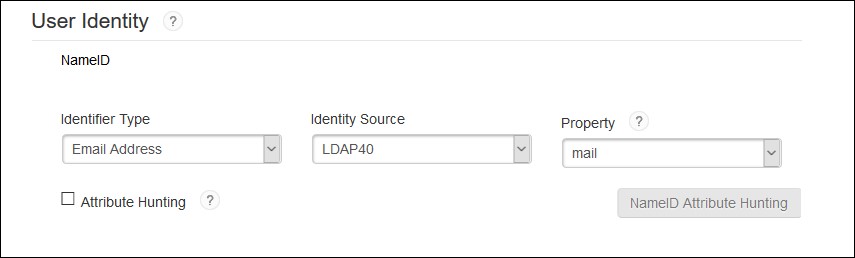
- Configure NameID information that identifies the user on whose behalf the SAML assertion is generated.
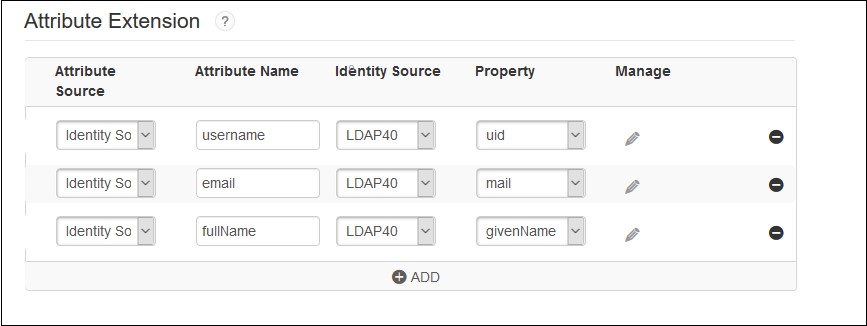
- Configure additional user information to be sent to the application in the SAML response, for example, username, email, display name, groups etc.
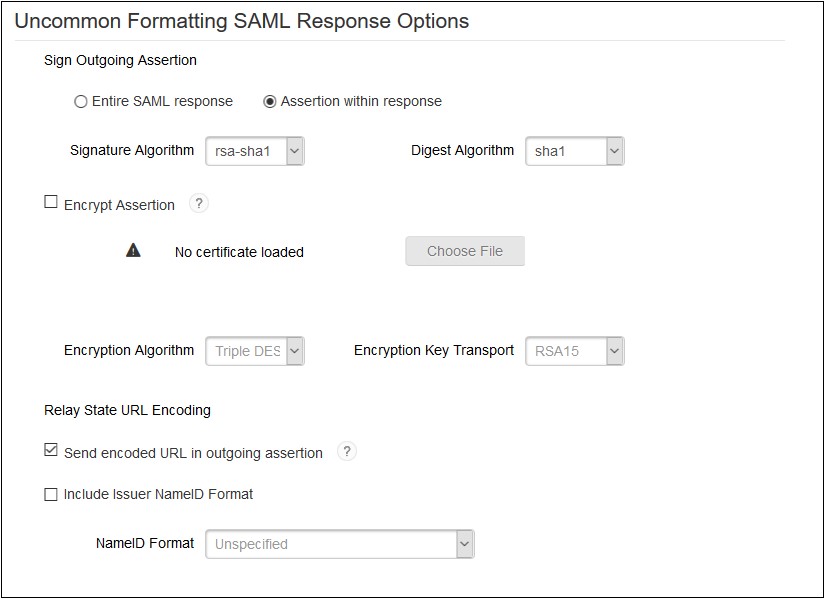
- Sign outgoing Assertion:- Assertion within Response.
- Encrypt Assertion (Optional): If checked, you need to load miniOrange plugin’s public certificate and you can download it from the Service Provider Info tab of the plugin.
- Unchecked Send encoded URL outgoing in assertion .
- Checked include issuer NameID format and select NameID Format as Unspecified.
- Save the configuration and move to the next page i.e. User Access page.
- Define application access in the User Access page.
- Configure application display settings for RSA end users like app icon etc and save the settings.
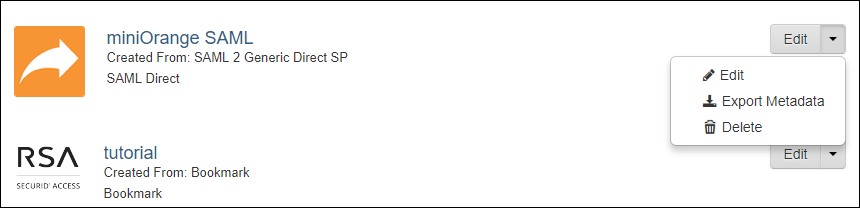
- Now, In the Administration Console, click Application My Application.
- Find the app that you have configured and click on Edit Export Metadata. Keep the metadata handy, it will require to configure miniOrange plugin.
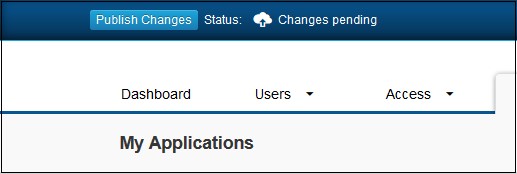
- Click on Publish Changes in the top left corner of the RSA Admin Console to publish this configuration and immediately activate it.

 Connection Profile
Connection Profile
 Initiate SAML Workflow
Initiate SAML Workflow
 SAML Identity Provider(Issuer)
SAML Identity Provider(Issuer)
 Service Provider
Service Provider
 User Identity
User Identity
 Advanced Configuration: Attribute Extention
Advanced Configuration: Attribute Extention
 Advanced Configuration: Uncommon Formatting SAML Response
Advanced Configuration: Uncommon Formatting SAML Response
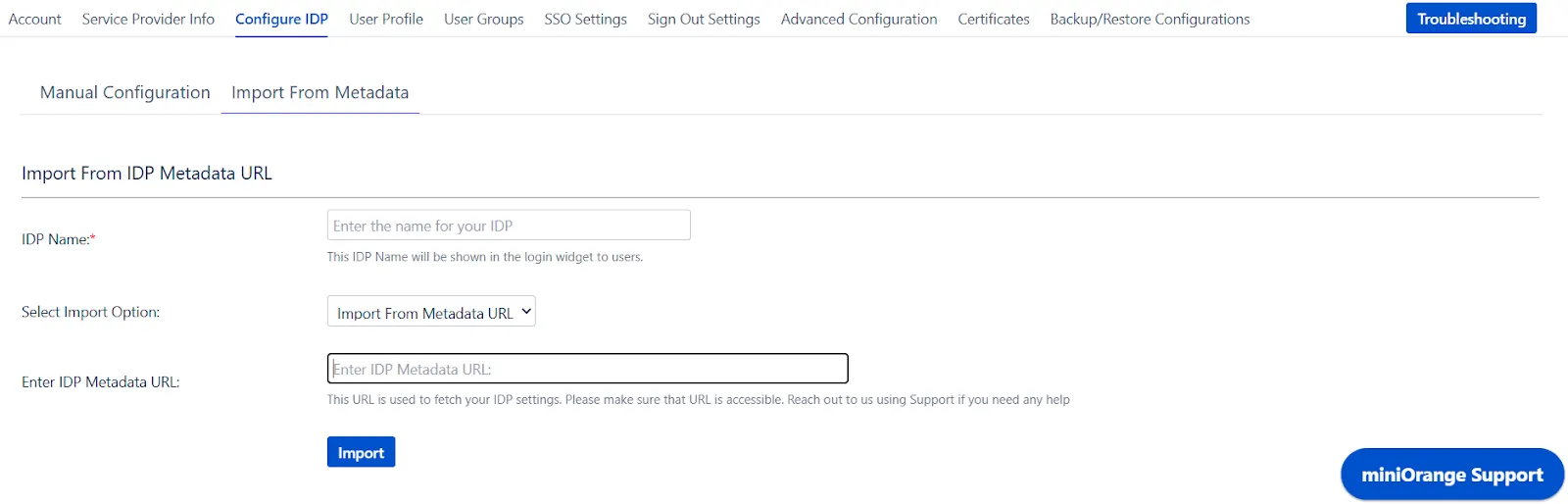
Step 2: Set Up Crowd as Service Provider
With the information you have been given by Your IDP team, you can configure IDP settings in 2 ways:
- By Metadata URL
- Manual Configuration
- Click on Import from Metadata in Configure IDP tab
- Give IDP Name that you want to.
- Enter IDP metadata URL: Enter your metadata URL
- Click Import
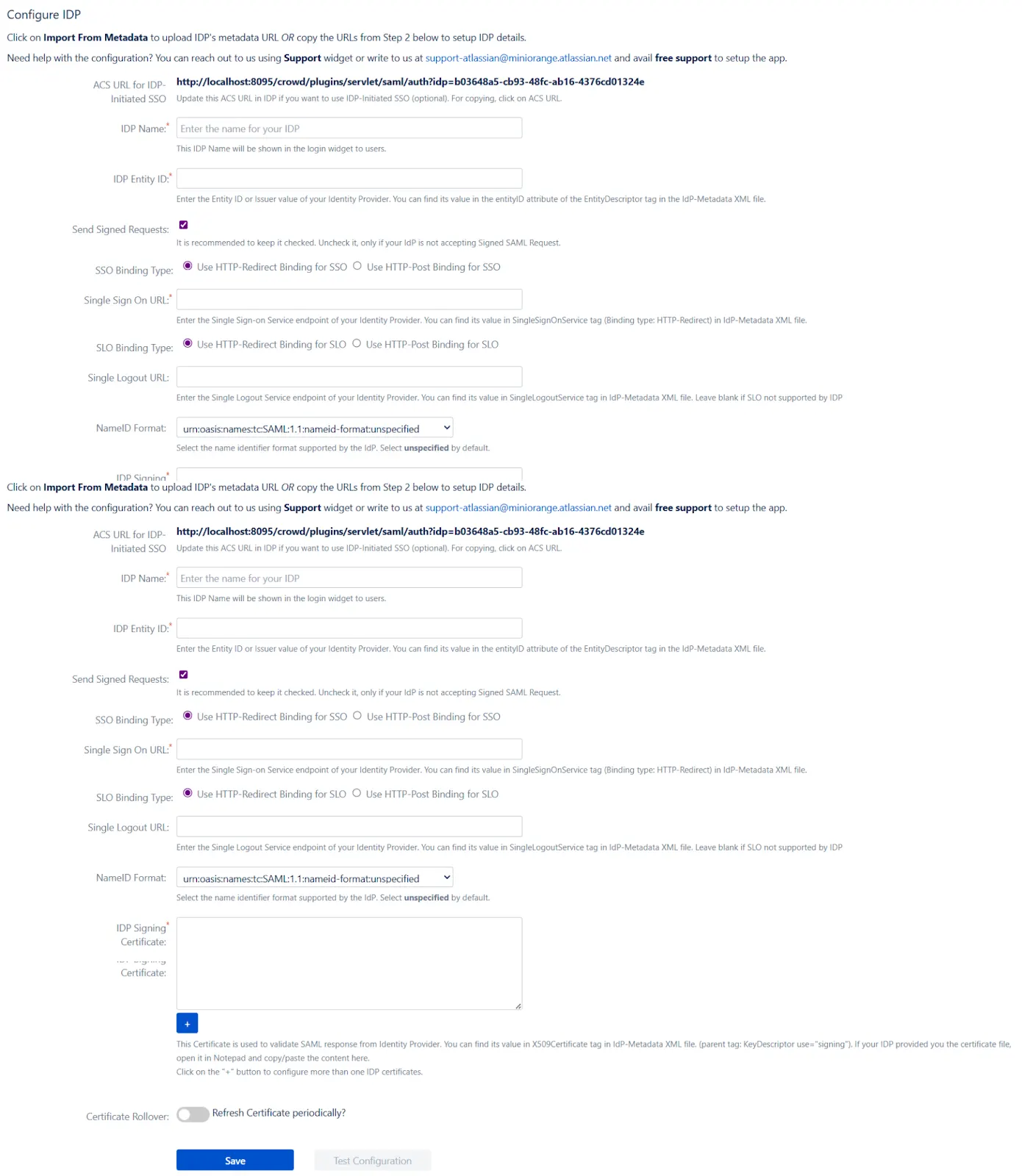
B. Manual Configuration
Go to Configure IDP tab and enter the following details
- IDP Entity ID
- Single Sign On URL
- Single Logout URL
- X.509 Certificate
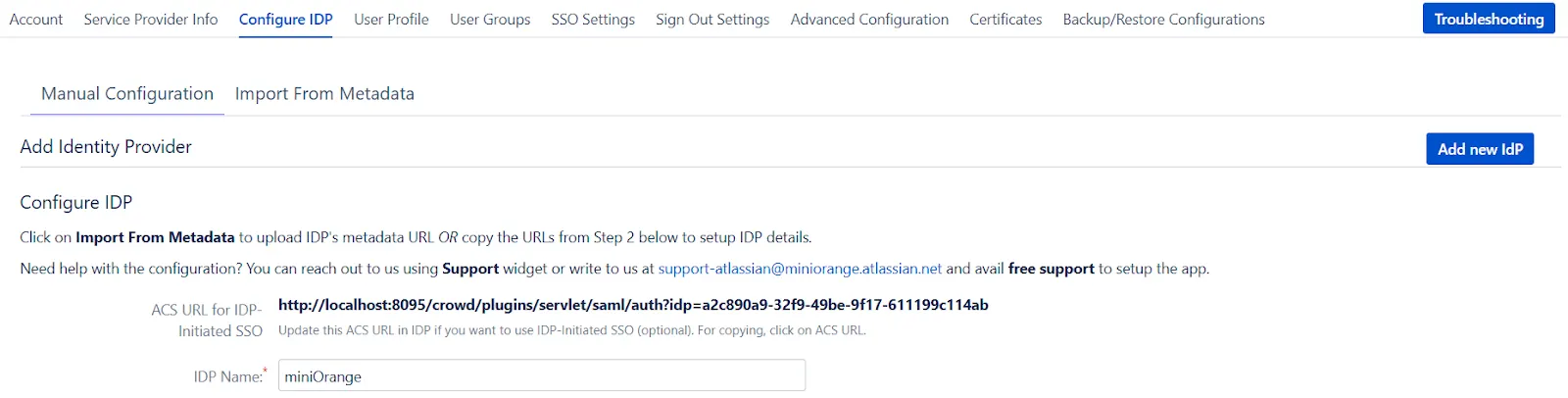
If you already have one IDP & you are looking to add Second IDP then you can do it by performing the following steps.
- Navigate to Configure IDP tab.
- Click on Add new IDP.
- It will present a blank form & you can configure new IDP using steps from Single IdP Setup.
Configure multiple IDPs
If you have configured more than two IDPs then it will show you the list of IDP that you have configured with Crowd.
Click on Add new IdP button for adding new IDP on Crowd. The steps for adding new IDP will remain the same.
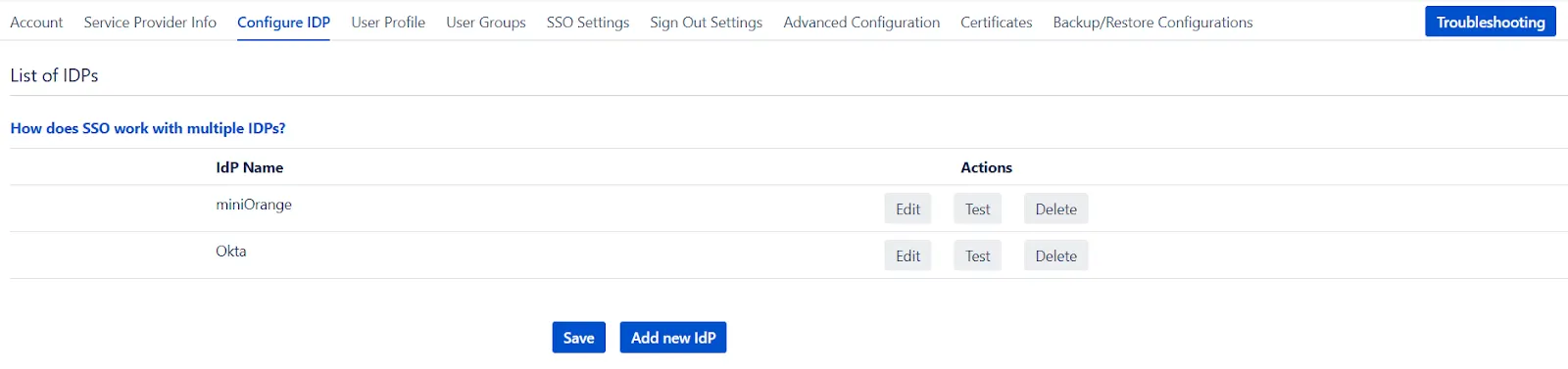
An operation that you can perform with List of IdPs page.
- Add / delete Identity Provider.
- Test Connection between Crowd & IdP by click on Test button for respective IDP.
- Edit the IdP configuration by clicking on the Edit button.
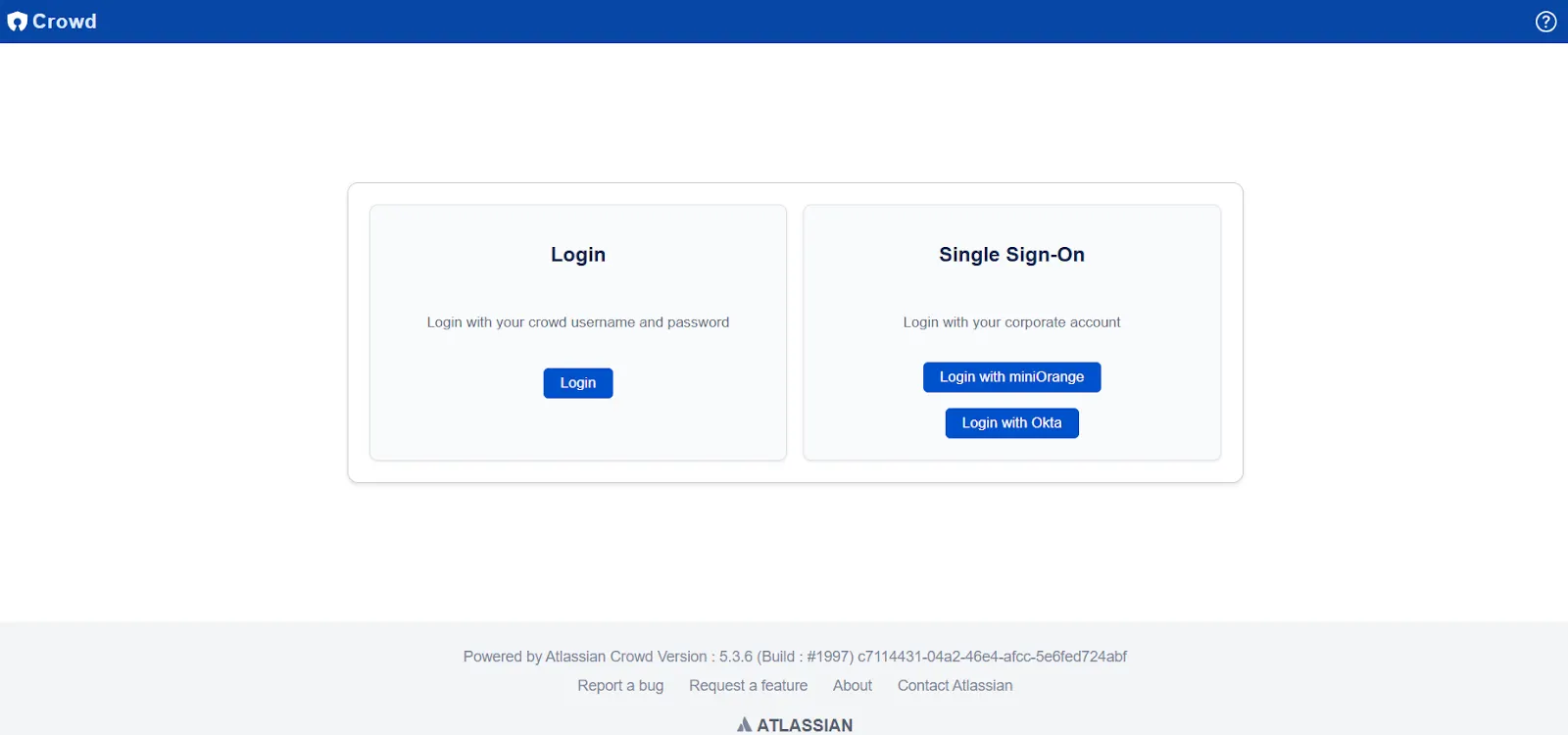
Single Sign-On with Multiple Identity Provider(IDP)
Select your IdP from the list. It will redirect you to selected IdP login page.
Step 3: Setting up Crowd user profile attributes
We will be setting up user profile attributes for Crowd. If your users are stored in a directory that is Read Only, please check Disable Attribute Mapping in User Profile tab and follow steps given in Matching a User.
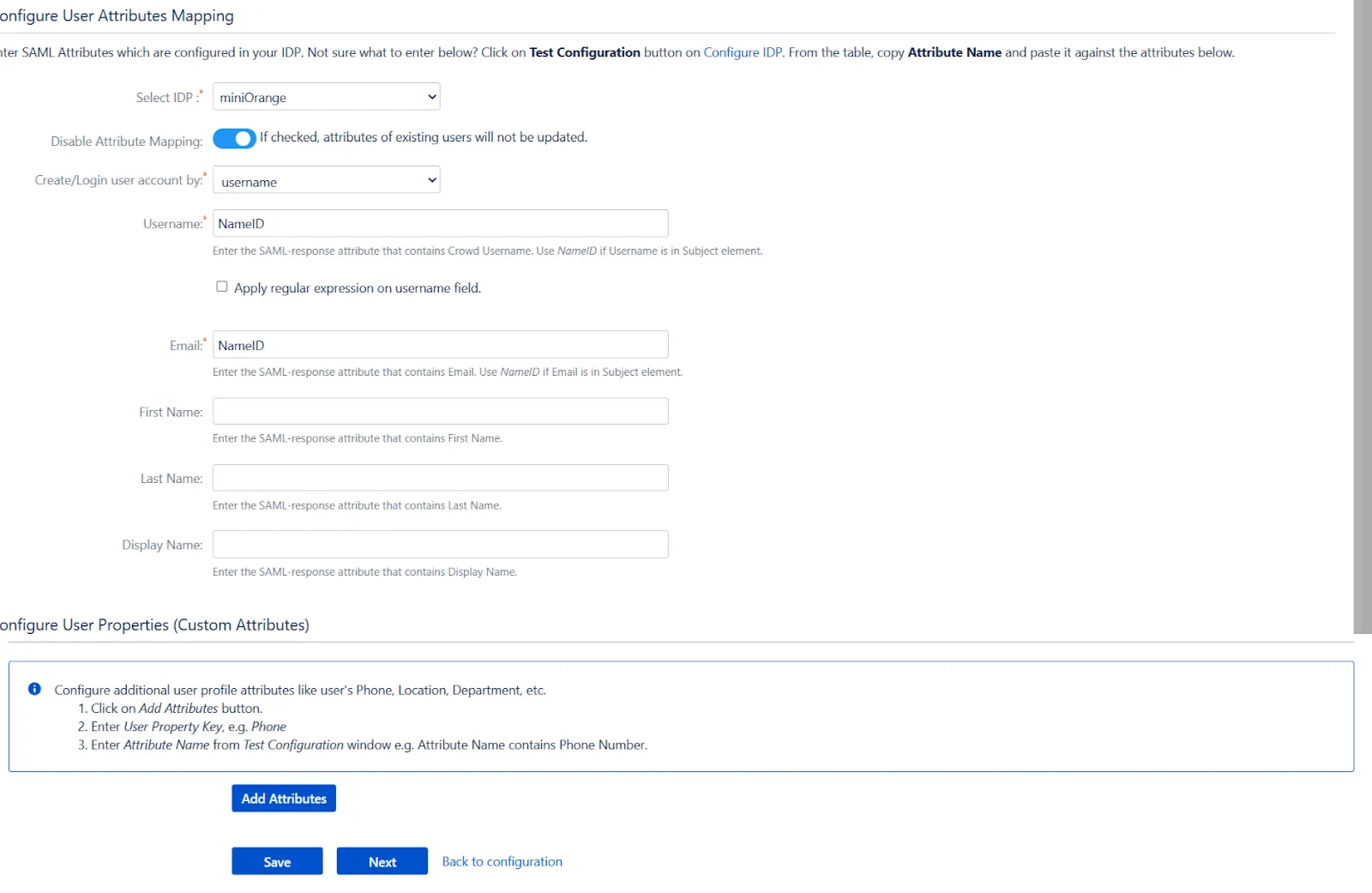
a. Finding correct attributes
- Go to Configure IDP tab. Scroll down and click on Test Configuration.
- You will see all the values returned by your IDP to Crowd in a table. If you don't see value for First Name, Last Name, Email or Username, make the required settings in your IDP to return this information.
- Once you see all the values in Test Configuration, keep the window open and go to User Profile tab.
b. Setting profile attributes
- In this tab, fill the values by matching the name of the attribute. For instance, if the Attribute Name in the Test Configuration window is NameID, enter NameID against Username
- Setting up both Username and Email is required if you want to let users register. If you want existing users to only login, configure the attribute using which you will match the user in Crowd.
-
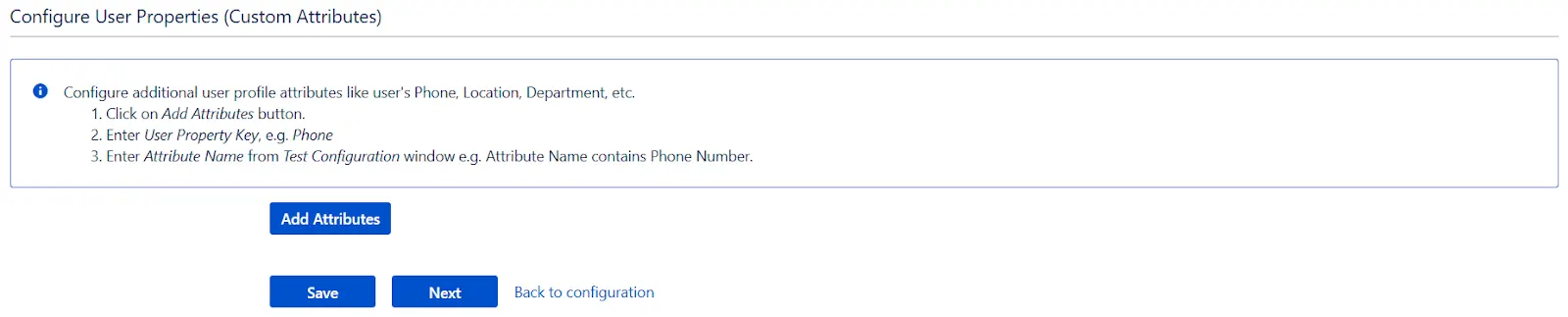
Configure additional user profile attributes like user's Phone, Location,
Department, etc.
- Click on Add Attributes button.
- Enter User Property Key, e.g. Phone
- Enter Attribute Name from Test Configuration window e.g. Attribute Name contains Phone Number.
c. Matching a User
When the user logs into Crowd, one of the user's data/attribute coming in
from the IDP is used to search the user in Crowd. This is used to detect the
user in Crowd and log in the user to the same account.
You can
configure it using steps given below:
- Go to User Profile tab
- Select Username or Email for Login/Search Crowd user account by
- Enter the attribute name from IDP which corresponds to Username or Email using Finding Correct Attributes
Step 4: Assigning groups to users
We will be setting up user group attributes for Crowd. If your users are stored in a directory that is Read Only, please check Disable Group Mapping in User Groups tab and skip to Setting default group.
a. Setting default group
- Select the users' Default Group in the tab User Groups. If no group is mapped, users are added by default to this group.
- You can enable default groups for All Users or New Users using the option. Select None if you don't want to assign any default group to SSO users, using the option Enable Default Groups for.
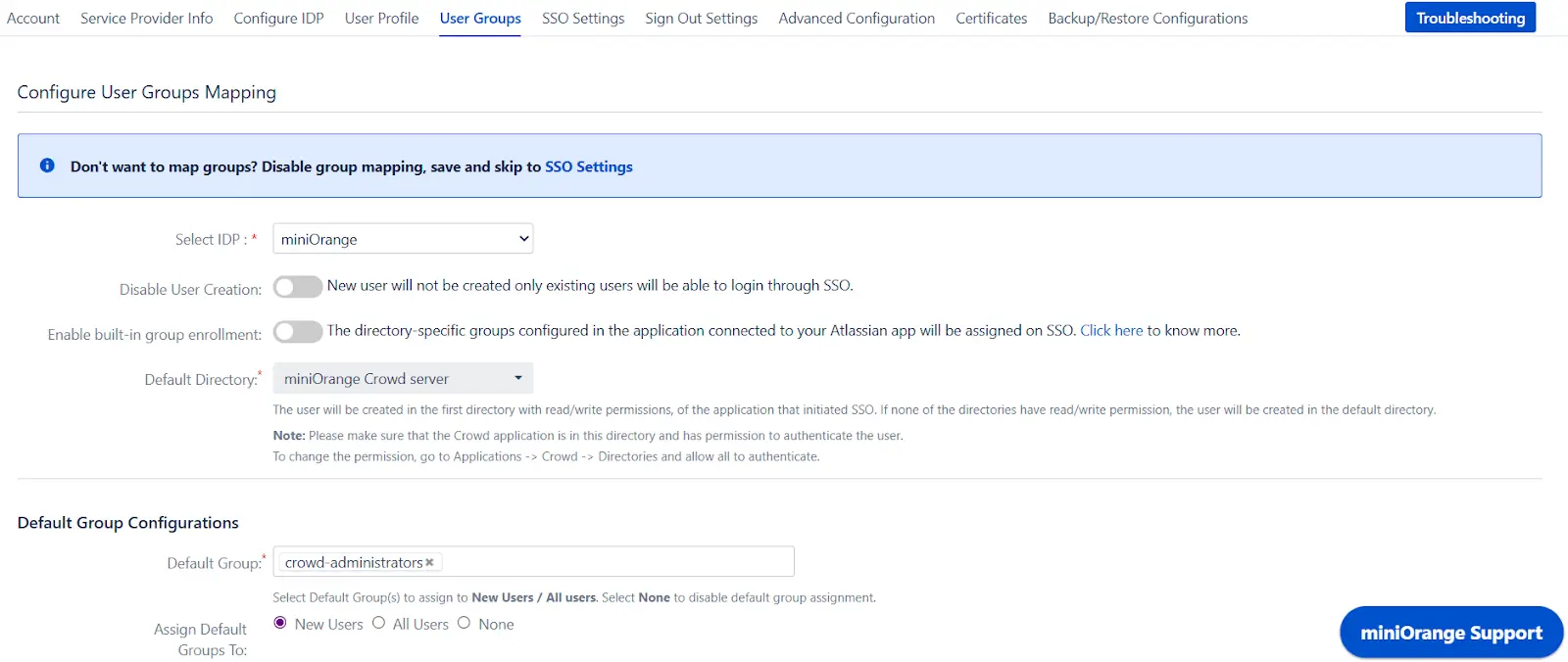
b. Finding Group Attribute
- Just like we found Attribute Name for User Profile attributes, we find group attribute.
- Go to Configure IDP tab. Scroll down and click on Test Configuration.
- You will see all the values returned by your IDP to Crowd in a table. If you don't see value with groups, make the required settings in your IDP to return group names.
- Once you see all the values in Test Configuration, keep the window open and go to User Groups tab.
- Enter the Attribute Name of group against Group Attribute.
- Check Disable Group Mapping option if you don't want to update groups of existing users.
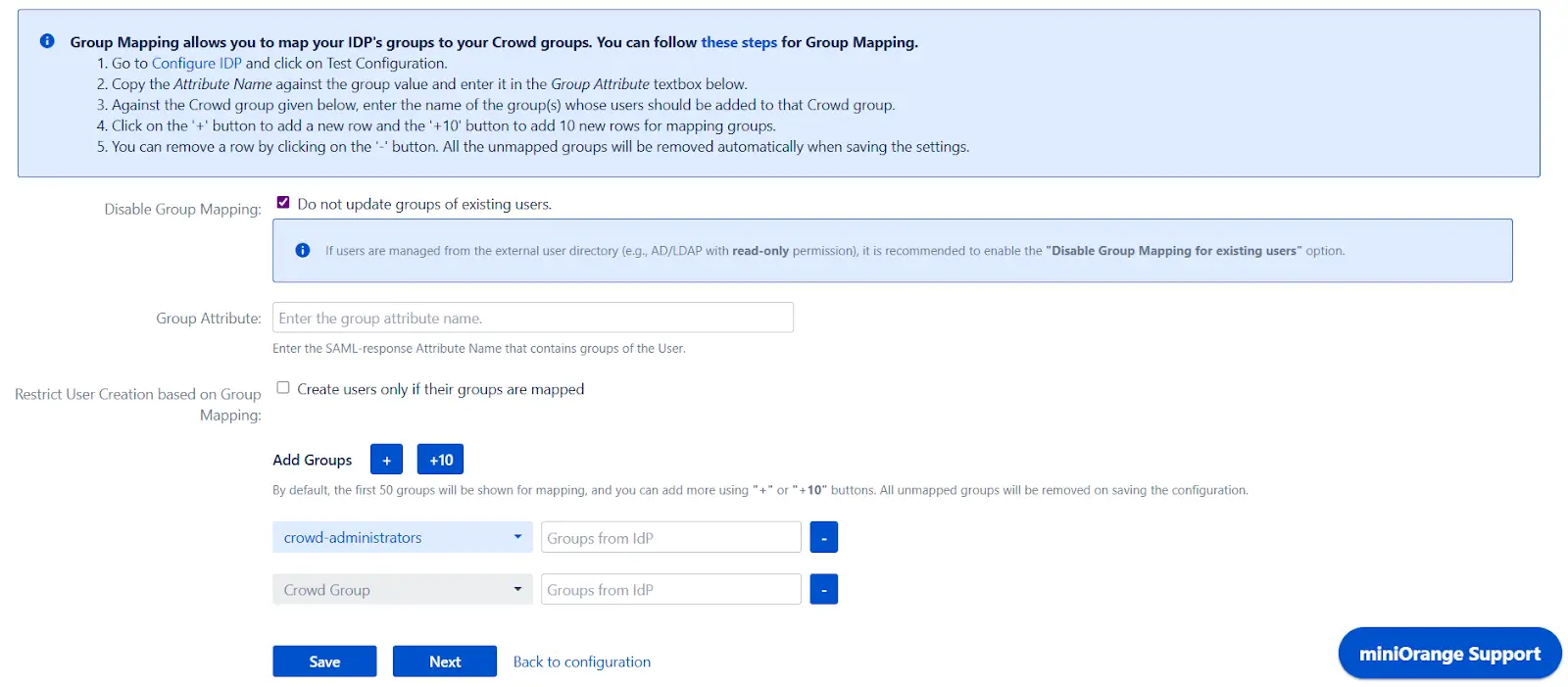
c. Group Mapping
Group Mapping can be done in following way:Manual group mapping: If the names of groups in Crowd are different than the corresponding groups in IDP, you should use Manual group mapping
- Check Restrict User Creation Based on Group Mapping option if you want new users to be created only if at least one of the user's IDP groups is mapped to a group in the application.
- For mapping, first select a Crowd group from the dropdown which lists all groups present in Crowd and then enter the name of the IDP group to be mapped in the textbox beside
- For example, if you want all users in 'dev' group in IDP to be added to app-user, you will need to select app-user from the dropdown and enter 'dev' against app-user.
- Use '+1' and '+10' buttons to add extra mapping fields.
- Use '-' button next to each mapping to delete that mapping.
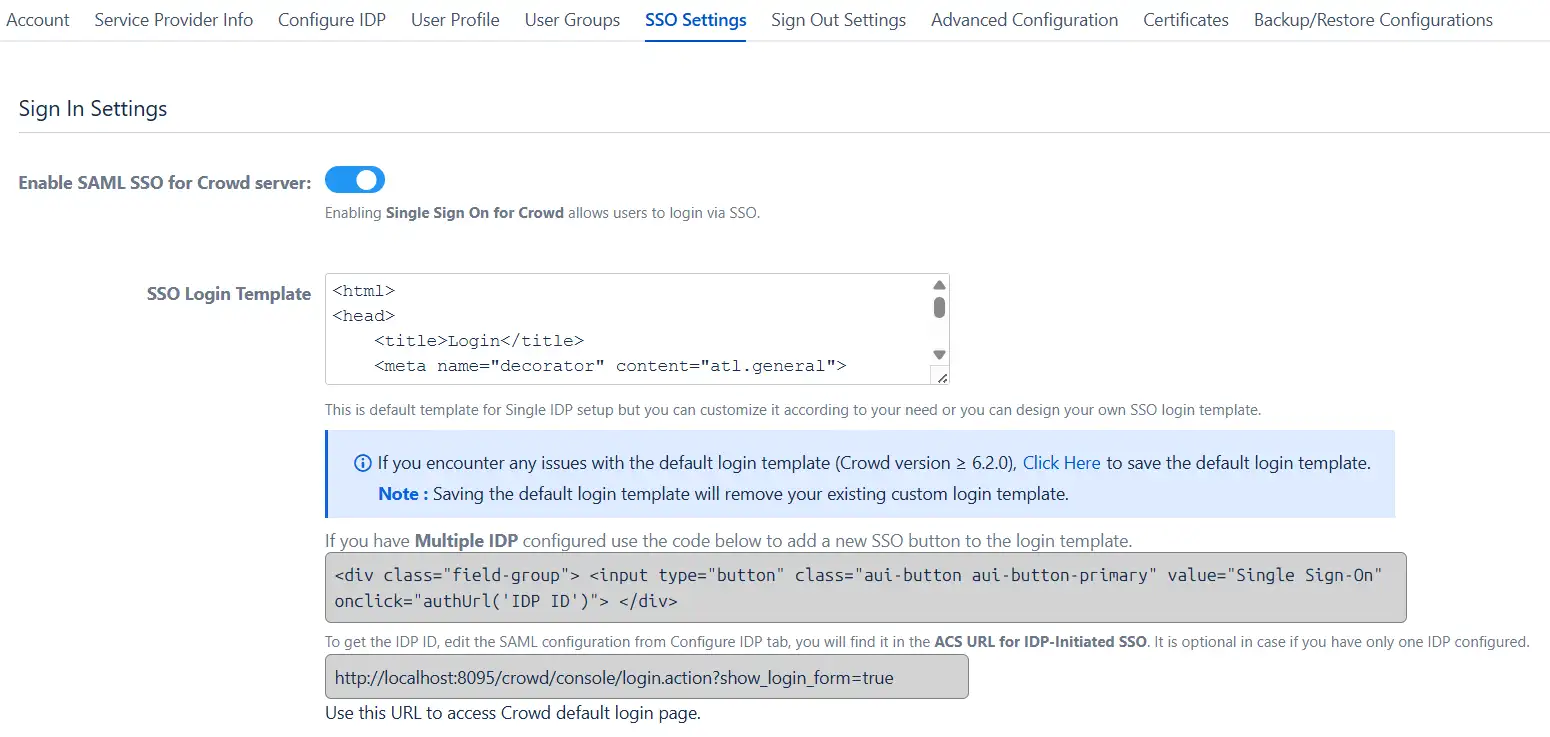
Step 5: SSO Settings
The settings in SSO Settings tab define the user experience for Single Sign On.
- Go to SSO Login Template. Design your own login template that will be used to initiate SSO.
- Set redirect URL after login using Relay State. Keep this empty for coming back to the same page user started from
- Enable Auto-redirect to IDP if you want to allow users to login only using IDP. Enable backdoor for emergency
Step 6: Crowd Connectors
The Crowd SSO connector expands the SAML SSO functionality from Crowd to its connected Atlassian applications where it allows users to login to their applications such as Jira, Confluence, Bitbucket, Bamboo, Fisheye while maintaining the users in Crowd.
Note: Click on the icons to view the SSO Connector guide for the application.
Crowd Troubleshooting
Additional Resources
Did this page help you?

 Try it for free
Try it for free