Crowd SSO Documentation: Step-by-Step Guides for Every IdP
Set up Crowd SSO with your preferred IdP. Find full documentation for SAML, OAuth & connector integrations.
Crowd SSO Video Guides
App Resources: Explore Blogs and Usecases
Handbook
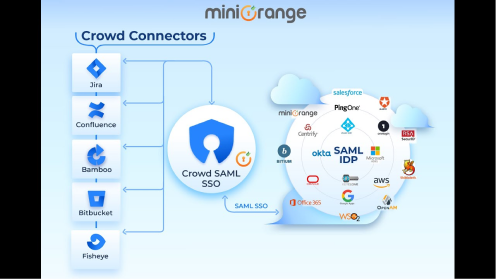
Crowd SSO Connector
Crowd SSO Connector allows users to sign into Crowd Server and Data Center with any Identity Provider (IdP) like ADFS, Entra ID/Azure AD, Okta, OneLogin and many more.
Know More
Blog
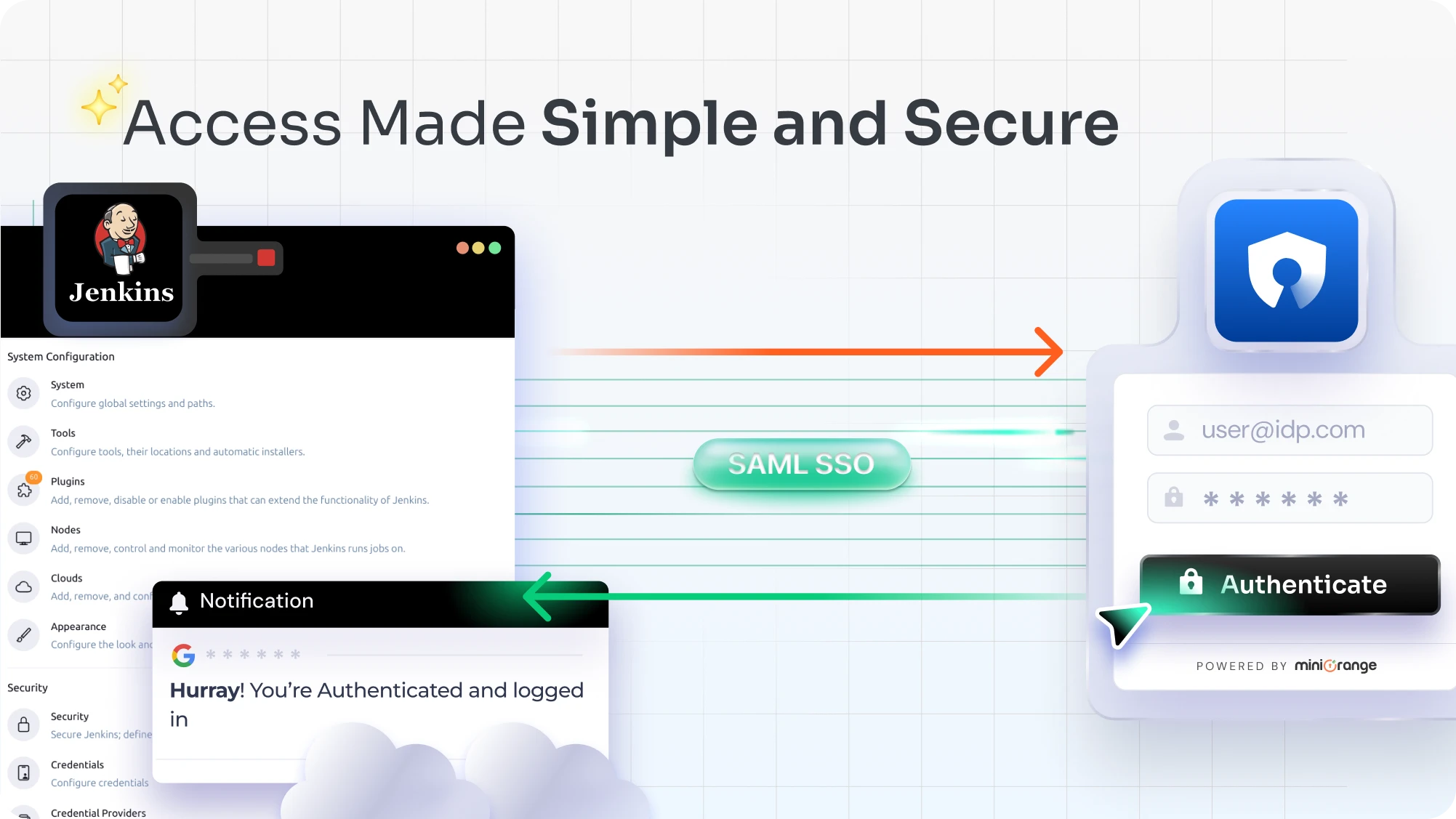
SSO into Jenkins while managing users in Atlassian Crowd
Know More
Blog
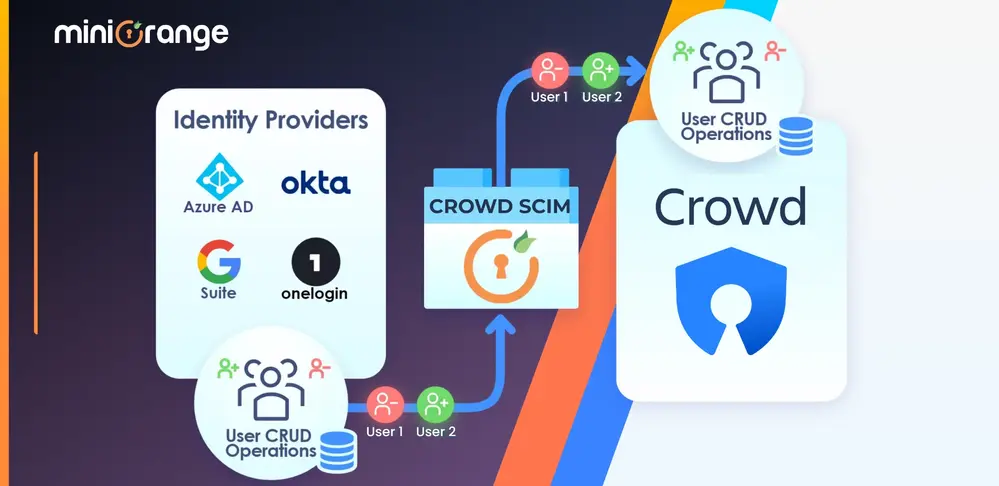
Crowd User Management at your fingertips
Know More
Blog
SSO for Atlassian Applications connected to Crowd
Know More
-
How do I install the miniOrange Crowd SSO Connector plugin?
Download the plugin JAR from the Atlassian Marketplace and place it in the plugins subdirectory of your shared Crowd home directory (for Crowd 3.0+). Then restart your Crowd server. The plugin will be detected and activated automatically on startup.
-
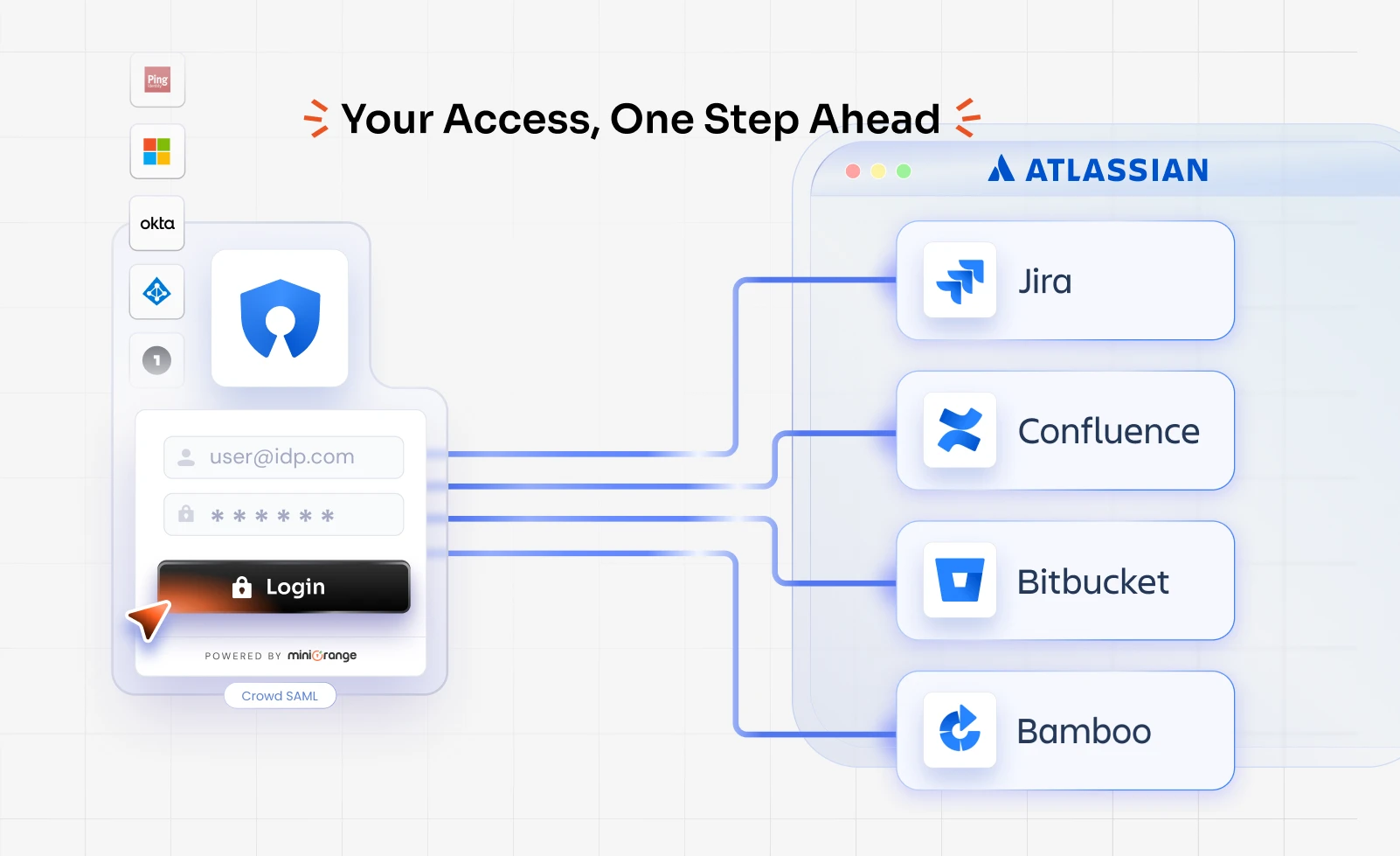
Which Atlassian applications does the Crowd SSO Connector support?
The Crowd SSO Connector enables single sign-on for all major self-hosted Atlassian applications: Jira, Confluence, Bitbucket, Bamboo, and Fisheye. It also extends to third-party DevOps tools such as Jenkins, SonarQube, and Nexus, allowing Crowd to act as the central authentication hub for your entire toolchain.
-
What is the difference between Crowd SAML SSO and the Crowd SSO Connector?
Crowd SAML SSO configures Crowd itself as a SAML Service Provider, so users authenticate via an external Identity Provider (like Okta or Entra ID) to log directly into Crowd. The Crowd SSO Connector, on the other hand, lets Atlassian apps like Jira and Confluence use Crowd as their authentication source, so once users are authenticated by Crowd, they gain seamless access to all connected apps without re-entering credentials.
-
Can I configure multiple Identity Providers (IdPs) for Crowd SSO?
Yes. The miniOrange plugin supports multi-IdP configurations. Once more than one IdP is configured, users see a dropdown on the login page to select their provider, or you can enable domain-based routing, where the user's email domain automatically redirects them to the correct IdP (for example, routing @acme.com to Okta and @partner.com to Entra ID).