REST API Authentication In Atlassian using API Tokens
The miniOrange REST API Authentication plugin provides a secure way of
accessing Jira, Confluence, and Bitbucket REST APIs. It provides a
variety of authentication methods, like API tokens, OAuth tokens, and
JWTs. The plugin offers additional functionalities like a maximum
expiration time for API tokens, API restrictions based on IP addresses
and user groups, rate limiting, and much more.
This guide will walk you through the steps to configure different
authentication methods.
Download and Installation
- Log into your Atlassian instance as an admin.
- Navigate to the settings menu and click Manage Apps.
- Click Find new apps or Find new add-ons from the left-hand side of the page.
- Locate API Token/OAuth Authentication app.
- Click Try free to begin a new trial or buy now to purchase a license.
- Enter your information and click Generate License when redirected to MyAtlassian.
- Click Apply License.
Authentication Methods
1: Configuring API Key Authentication Method
1.1 Generating API Tokens
- Click on the Add Key button on the Manage API Keys page in the API Token Tab.
- Add the key name and select the type as Basic or Bearer.
- Set the expiry as custom or never. If you select custom make sure you select the Interval count and Expiry Interval.
- You can also select if you want to receive the API token via email.
- Once everything is set, click on Create.
- Now you have the token and you can proceed further with setup steps or set the advance settings for API tokens and then move ahead.
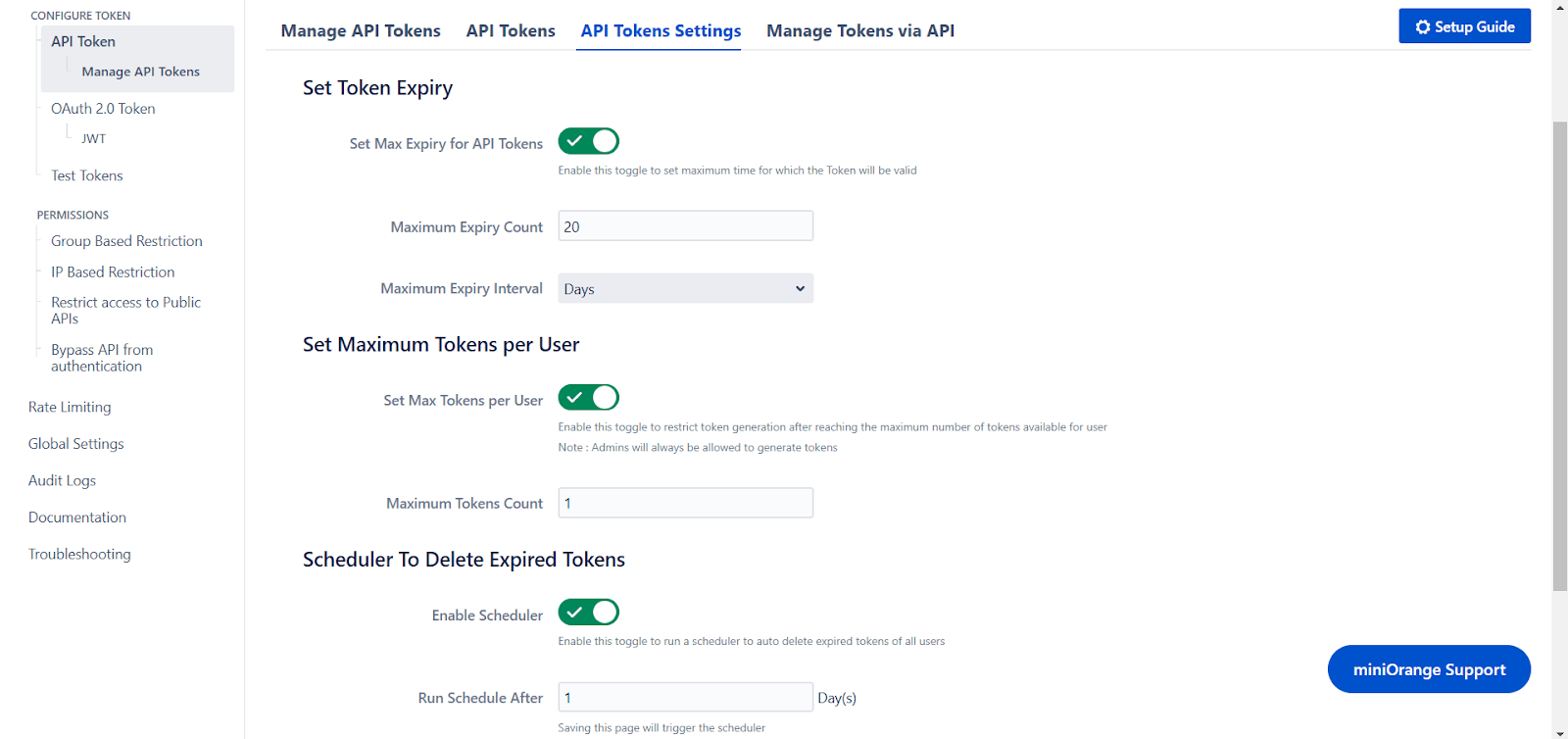
1.2 API Key Settings
- You can enable Set Max Expiry for API keys and set the maximum expiry time for an API token. Once enabled token generation will only be allowed only if the time is less than or equal to the configured maximum expiration time.
- You can enable Set Max Tokens per user and set the maximum number of tokens a user can have. Once the user reaches the configured limit, he/she will not be allowed to generate new tokens unless he deletes old, unused or expired tokens.
- You can enable the Scheduler to Delete Expired Tokens feature and specify the number of days after which the scheduler will automatically delete all expired tokens. The scheduler will run immediately after you save the page and will continue to run simultaneously after the specified number of days.
2: Test Configurations
- Select the appropriate token type.
- Paste the token and click on Test Token.
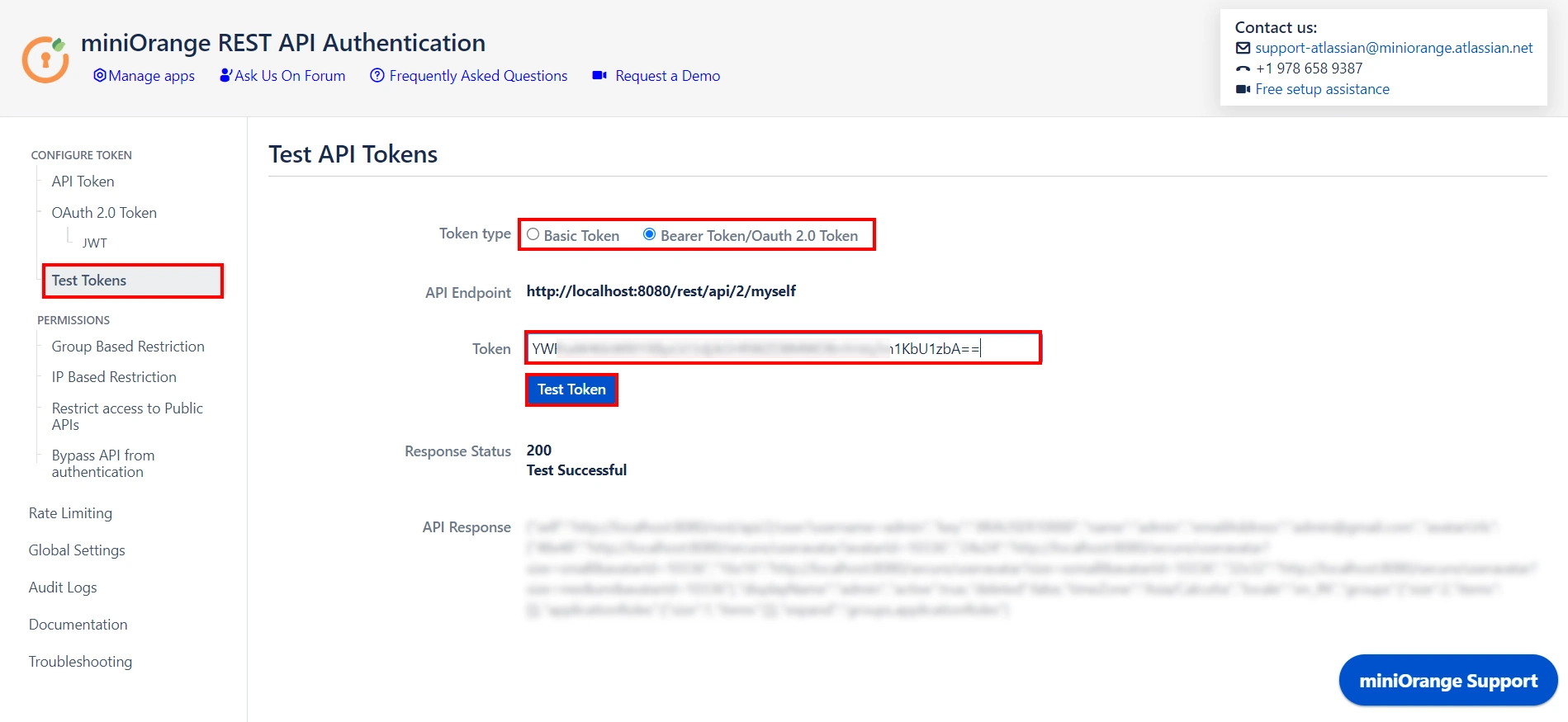
Test Successful! You can proceed further.
If you encounter any difficulties configuring add-ons, please contact us at atlassiansupport@xecurify.com or raise a support ticket here.
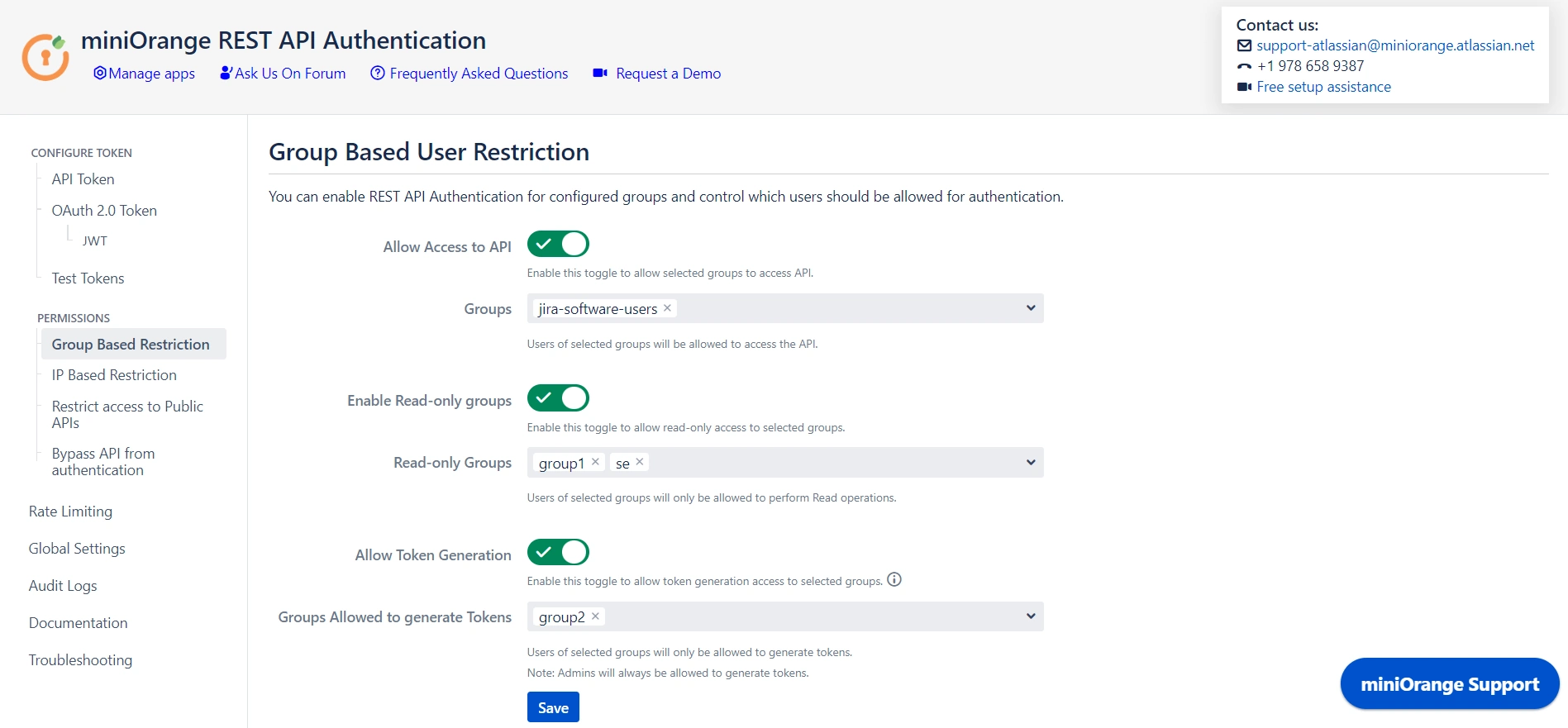
3: Adding Group and IP-Based Restriction
3.1 Group Based Restrictions
- You can Enable Allow API access and select groups who can access the APIs. Users who will not be part of selected groups cannot access the APIs.
- You can Enable Read-only Groups and allow selected groups to only access READ APIs. Users of selected groups will not be able to perform WRITE operations.
- You can Enable Allow Token Generation and select groups that can generate tokens. Users who will not be part of selected groups cannot generate tokens.
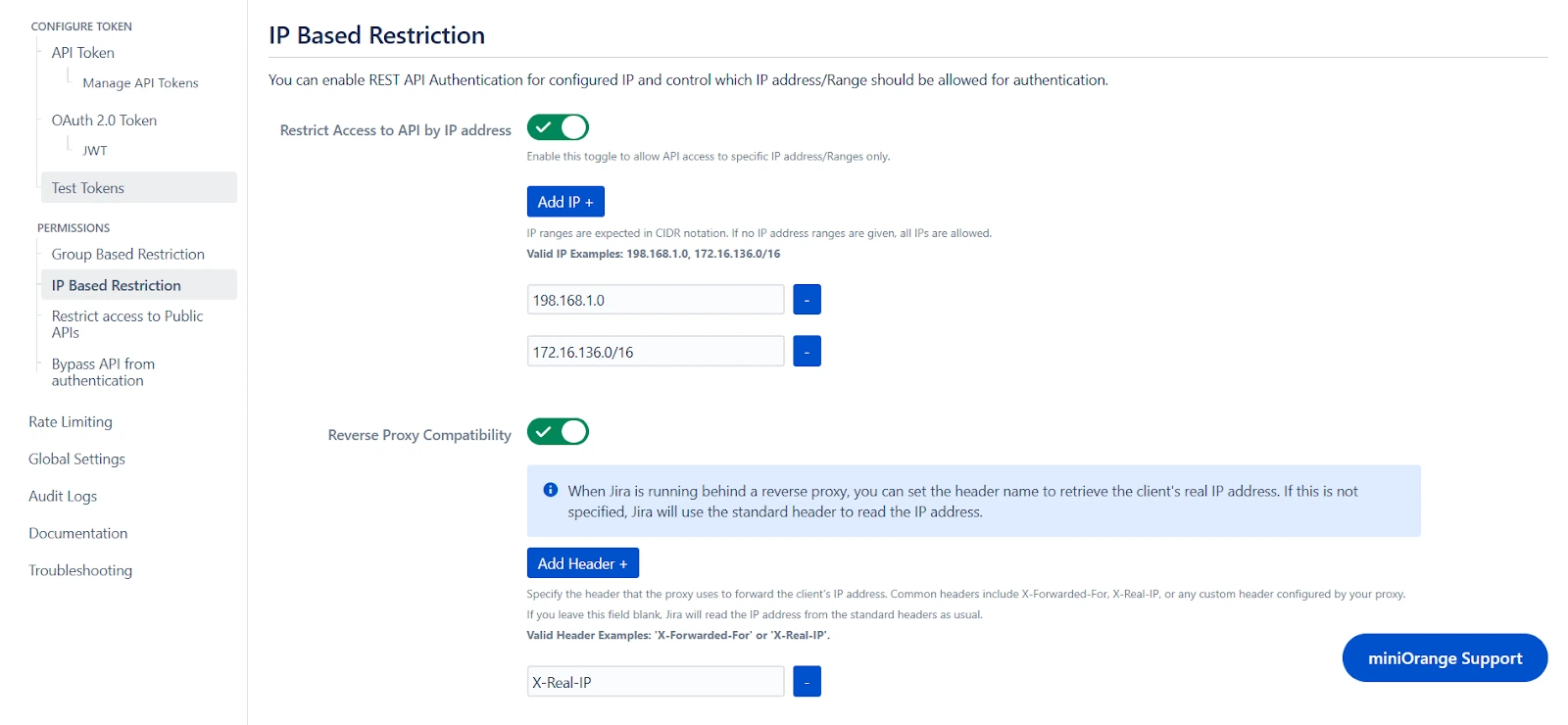
3.2 IP Based Restrictions
- You can enable Restrict Access to API by IP Address to allow API access from a specified network.
- You can add the specific IP address or IP range in CIDR notations; this will block all calls that do not belong to the configured values.
- You can enable Reverse Proxy Compatibility if your instance is running behind a reverse proxy and specify the header name to retrieve the client’s real IP address.
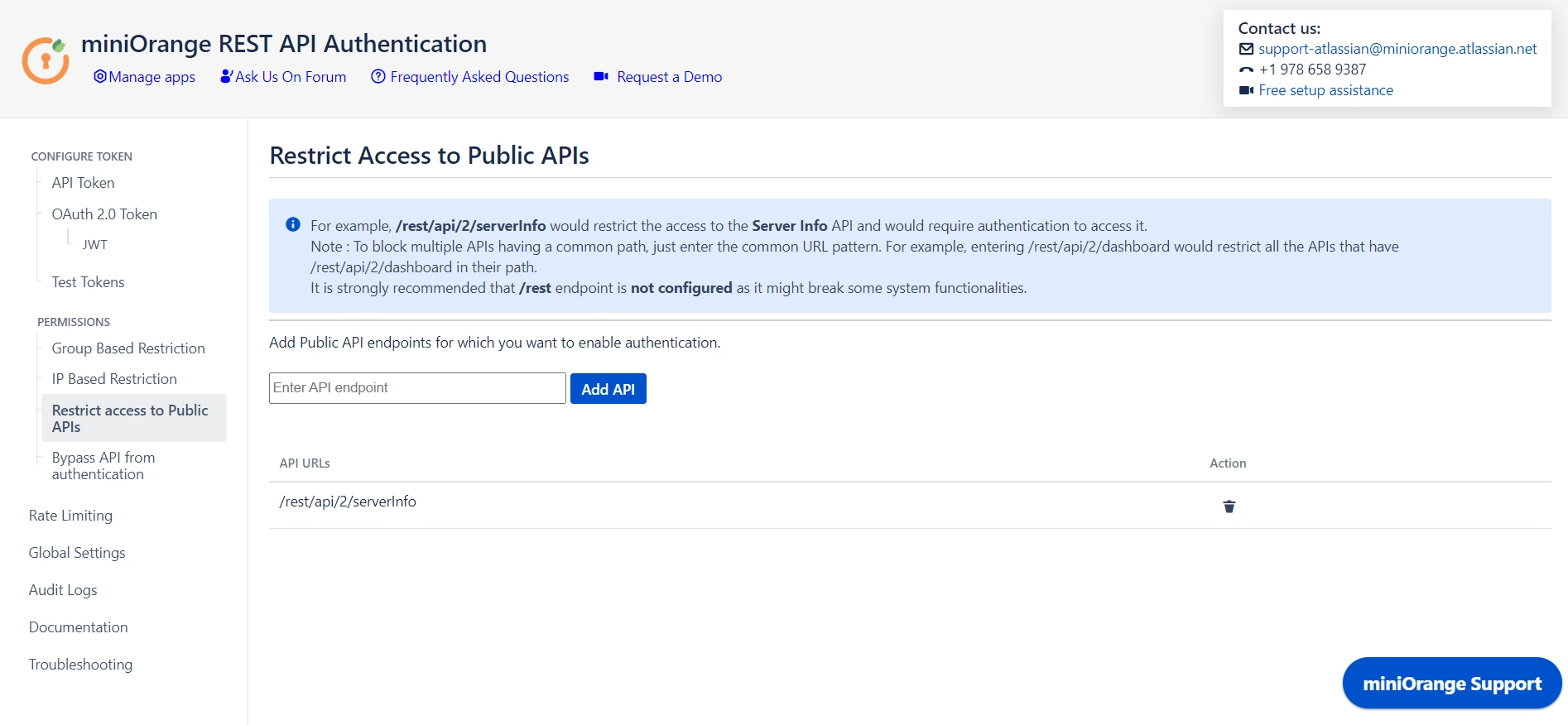
4: Public API Access
4.1 Restrict Access to Public APIs
- Public APIs do not require authentication and can be accessed anonymously. However, you can configure the API in Restrict Access to Public APIs and force authentication.
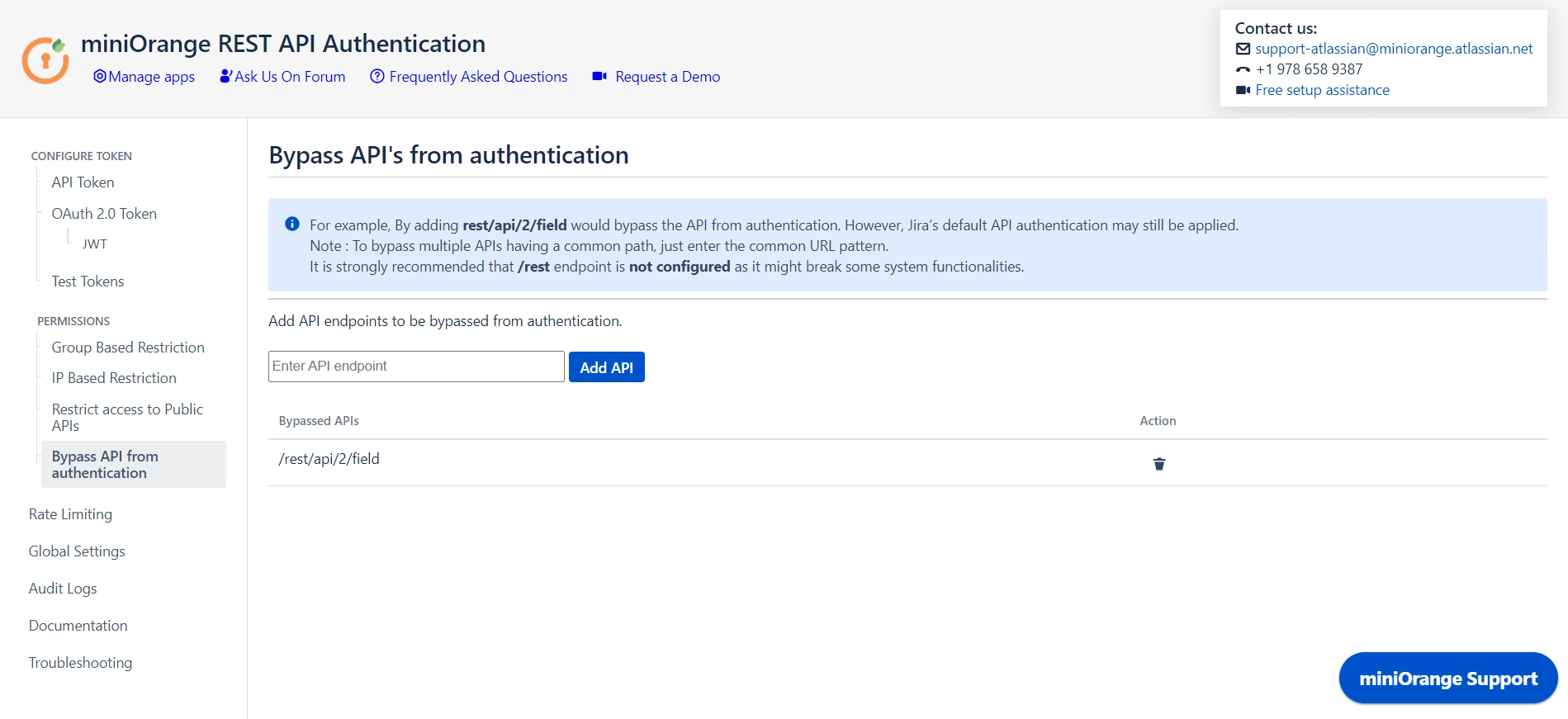
4.2 Bypass API from Authentication
- You can disable authentication through the plugin for specified APIs by adding them under Bypass API Authentication. However, default authentication might still be applicable.
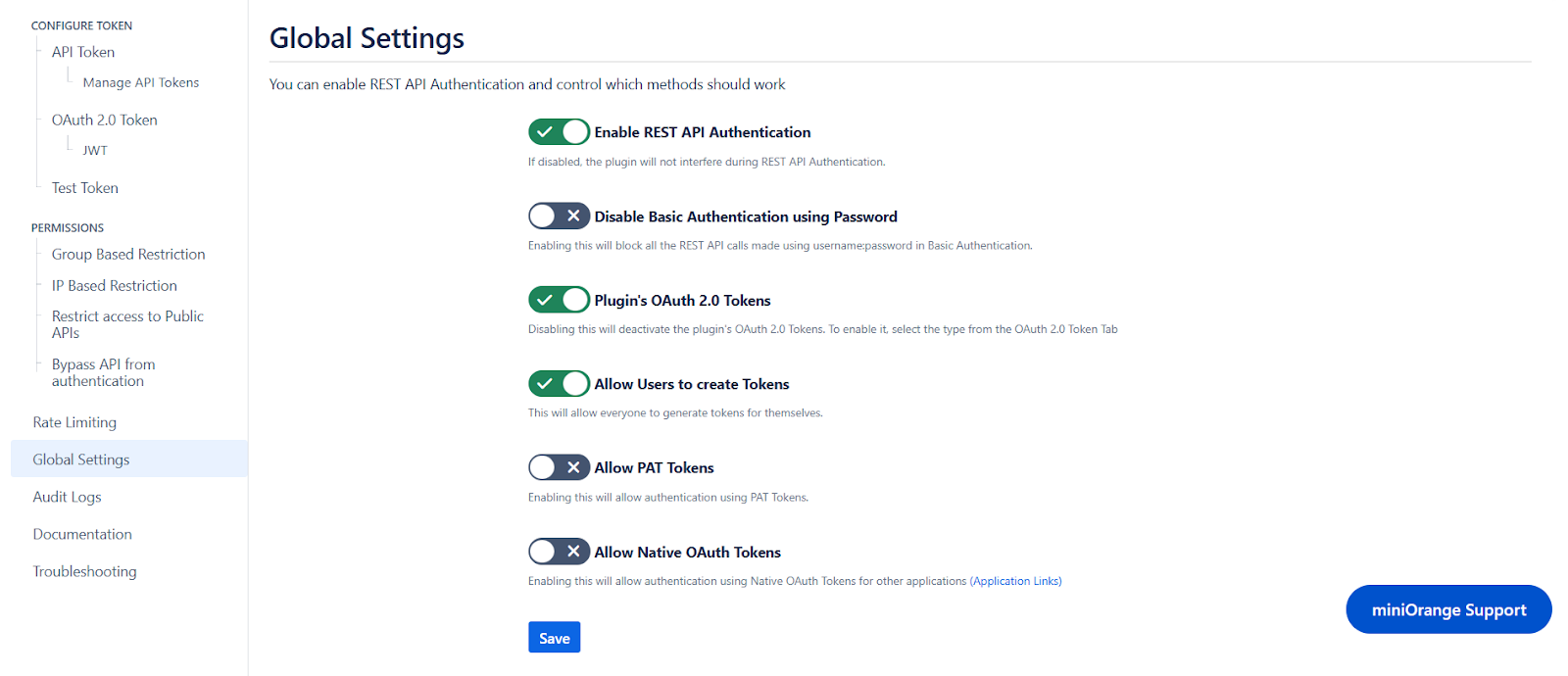
5: Global Settings
- The Enable REST API Authentication toggle ensures API authentication through the plugin. If disabled, the plugin will not be involved in API authentication.
- The Disable Basic Authentication toggle allows you to enforce authentication through the plugin. Basic authentication using username and password will be restricted.
- You can use the Plugin's OAuth 2.0 Tokens toggle to disable OAuth 2.0 tokens if not in use.
- The Allow PAT Tokens will allow users to use PAT tokens generated by Jira/Confluence to access the API. To restrict the use of PAT tokens and enforce authentication through the plugin you can disable the toggle.
- The Allow users to create Tokens toggle will allow all other users to generate tokens. If disabled, only admins will be able to generate tokens. However, if you have enabled Allow groups to generate tokens from group-based restrictions, you need to keep the toggle on.
- The Allow Native OAuth Tokens toggle enables Jira integration via Application Links, bypassing requests to Jira to authenticate Native OAuth 2.0 tokens. Disabling this toggle will enforce authentication through the plugin instead.
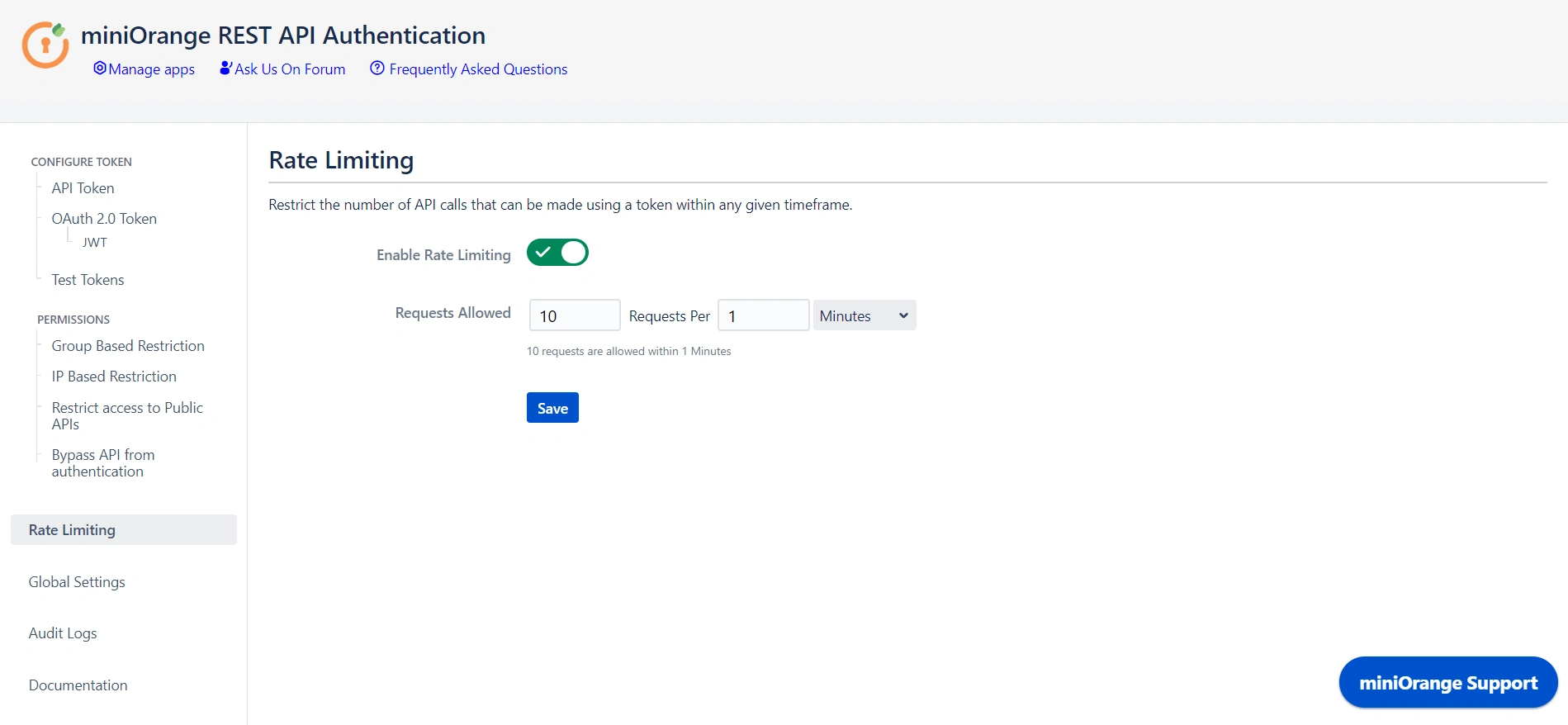
6: Rate Limiting
- Enable rate limiting to restrict the number of requests made by a token within the specified time frame.
- Then select the number of requests to be allowed and the time frame.
- This will enforce rate limiting on the API tokens generated through the plugin.
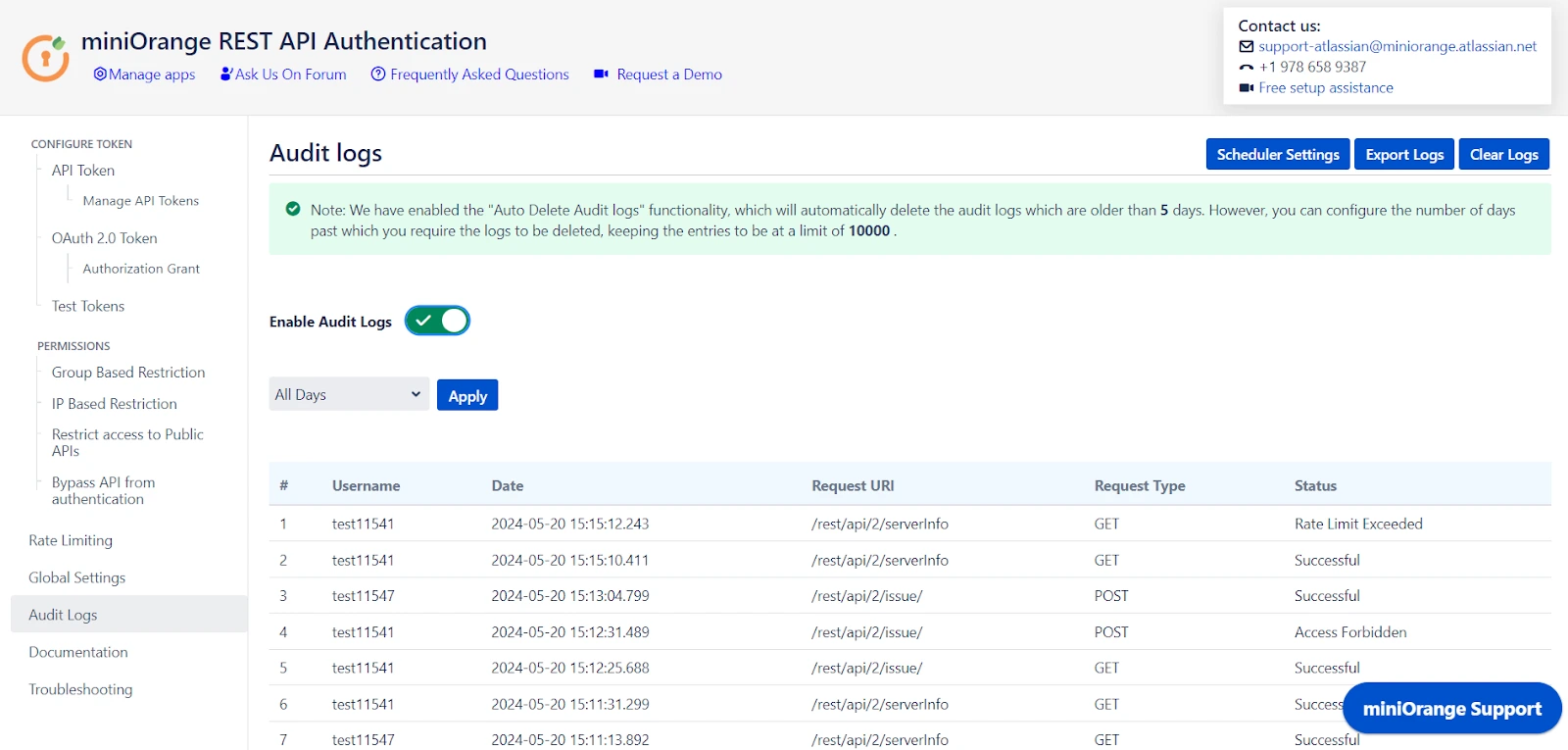
7: Audit Logs
- You can Enable Audit Logs to log the activity with REST APIs. This will help you monitor the REST API access.
- You can also update the Scheduler settings that automatically delete logs after a specific number of days or entries.
Additional Resources
Did this page help you?

 Try it for free
Try it for free


