Operational Technology (OT) was never meant to be exposed.
For decades, industrial systems like SCADA, PLCs, and ICS operated in isolated environments where uptime mattered more than cybersecurity. That assumption has fundamentally changed. Today, OT environments are deeply connected to IT systems, cloud platforms, remote vendors, and increasingly, IoT devices.
This connectivity has also reshaped the threat scenario.
Modern attackers don’t just focus on directly breaking systems. Instead, they target identities, compromising credentials, escalating privileges, and moving laterally across interconnected environments. In OT, this means a single compromised account or unmanaged session can disrupt physical operations, halt production, or impact safety.
This is why PAM for OT environments is more than just an access control solution. It has shaped into an identity-centric security layer that governs how users, devices, and services interact with industrial systems.

Key Takeaways
- PAM for OT enforces least privilege access across industrial systems, reducing risk without impacting uptime
- It replaces VPN-based access with secure remote access for OT, ensuring controlled vendor connectivity
- Modern PAM, such as miniOrange PAM, extends beyond users to include machine identities and IoT devices
- Agentless deployment enables the protection of legacy and sensitive OT environments
- Continuous monitoring, session control, and audit trails support OT cybersecurity solutions and compliance
What Is PAM for OT Security?
Privileged Access Management (PAM) for OT is a framework that controls, monitors, and secures access to industrial systems such as SCADA, PLCs, and ICS environments.
At a deeper level, PAM acts as an identity control layer that sits between users and critical infrastructure. Instead of allowing direct access to systems, it introduces a mediated approach where every interaction is verified, controlled, and recorded.
This is particularly important in OT environments where systems are highly sensitive. Many of these systems were built decades ago with little consideration for modern cybersecurity. They cannot be patched frequently, do not support advanced authentication, and may fail under intrusive security controls.
PAM addresses this challenge by introducing agentless, proxy-based access mechanisms. This allows organizations to enforce strong access control without modifying the underlying systems. Every access request is evaluated based on identity, context, and policy, ensuring that only authorized interactions take place.
In essence, PAM transforms OT security from a network-based model to an identity-driven model, which is far more resilient against modern attack techniques.
PAM for IT vs PAM for OT
While Privileged Access Management originated in IT environments, applying the same approach to OT does not work without adaptation. The two environments differ not just in technology, but in risk, operational priorities, and system behavior.
| Aspect | IT PAM | OT PAM |
|---|---|---|
| Environment | Dynamic, frequently updated systems | Legacy, sensitive, often unpatchable systems |
| Deployment | Agent-based deployments are common | Requires agentless, non-intrusive deployment |
| Risk Impact | Data breaches, compliance violations | Physical disruption, safety risks, production downtime |
| Access Patterns | Internal admins and DevOps users | External vendors, operators, and engineers |
| Network Model | Broad network access often acceptable | Strict segmentation and controlled pathways are required |
| Downtime Tolerance | Moderate | Near-zero tolerance for disruption |
Key Challenges in OT Security
Before understanding why PAM is critical, it is important to recognize the structural challenges that define OT environments.
OT systems are often built on legacy infrastructure that cannot support modern security controls. Visibility is limited, making it difficult to track assets, identities, and access pathways. Vendor access introduces additional complexity, often without proper governance. At the same time, the convergence of IT, OT, and IoT environments creates new pathways for attackers to exploit. These challenges make traditional security approaches ineffective and highlight the need for identity-driven controls.
Why PAM Is Critical for OT Security
PAM is essential in OT to prevent unauthorized access, minimize downtime risks, and secure third-party vendor interactions.
Physical Consequences Change the Stakes
In OT environments, security incidents extend far beyond data loss and directly impact physical operations. Unauthorized access can disrupt production lines, alter system behavior, or damage critical equipment, creating safety and financial risks. This shifts access control from a technical requirement to an operational necessity, where every action must be governed, monitored, and tied to a verified identity.
Legacy Systems Depend on External Security
Most OT systems were not built with modern cybersecurity in mind and often lack native security controls or the ability to support updates and agents. This makes them inherently vulnerable. PAM introduces a protective control layer around these systems, ensuring secure access without modifying them, allowing organizations to strengthen security while maintaining system stability and uninterrupted operations.
Vendor Access Introduces Significant Risk
Third-party access is essential in OT environments but remains one of the least controlled entry points. Vendors often rely on shared credentials and persistent access, creating visibility gaps and accountability challenges. PAM addresses this by enforcing time-bound, identity-based access with full session monitoring, ensuring every interaction is controlled, auditable, and limited to required systems.
IT to OT Attack Paths Are Increasing
As IT and OT networks converge, attackers increasingly exploit IT compromises as a gateway into OT environments. Once inside, they can escalate privileges and move laterally toward critical systems. PAM disrupts this attack path by introducing strict identity verification and controlled access layers, ensuring compromised credentials cannot be easily used to reach sensitive assets.
How Attackers Move from IT to OT
Most modern OT attacks follow a predictable path. Attackers first compromise an IT system, often through phishing or credential theft. They then escalate privileges and move laterally across the network, searching for access points into OT environments. Once inside, they exploit privileged accounts to interact with critical systems.
PAM disrupts this chain by controlling privileged access at every stage, ensuring that even if an attacker gains entry, they cannot easily reach or manipulate OT systems.
The Hidden Risk: Machine Identities in OT and IoT
OT environments are not just made up of human users. They include thousands of machine identities such as PLCs, sensors, APIs, and service accounts.
These identities often operate with high privileges and minimal oversight. Many use hardcoded credentials or lack proper authentication mechanisms, making them attractive targets for attackers.
Modern PAM solutions are evolving to address this challenge by extending identity management to machines. This includes securing device authentication, managing credentials, and monitoring interactions between systems. As IoT adoption grows, managing machine identities will become a critical component of OT security.
Key Capabilities of PAM for OT Environments
Effective OT PAM solutions must be agentless, support secure remote access, and provide full session visibility and control
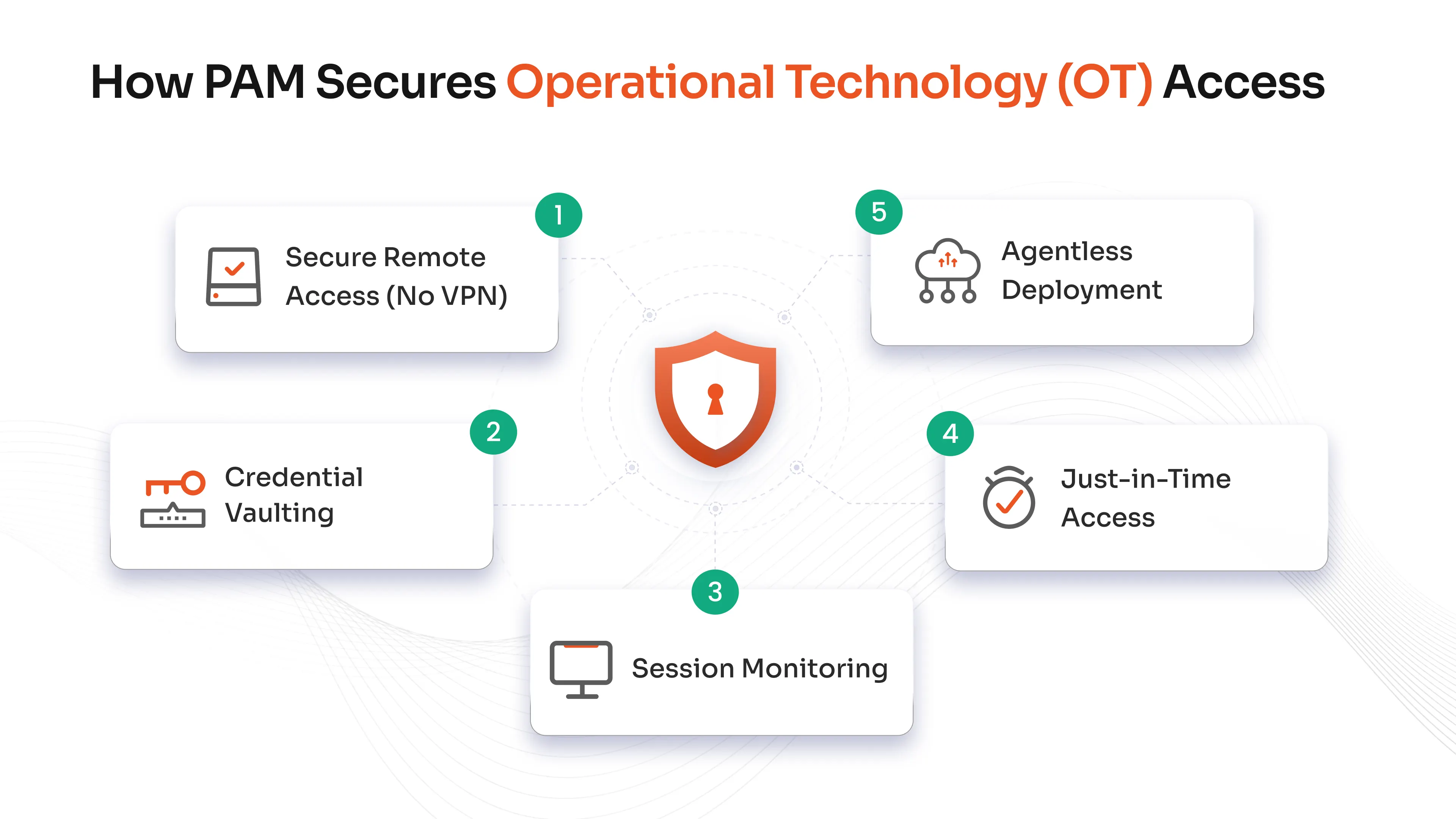
Secure Remote Access Without VPN
Traditional VPNs expose entire networks once access is granted, which is risky in OT environments where precision and control are critical. PAM replaces this with identity-based, session-level access, allowing users to connect only to specific systems they are authorized for, reducing exposure and aligning access with Zero Trust principles.
Credential Vaulting and Elimination of Shared Access
Shared credentials create significant security blind spots in OT environments by limiting accountability and increasing exposure. PAM eliminates this risk by securely storing credentials in a centralized vault and injecting them into sessions without user visibility, enabling better control, automated rotation, and consistent credential management.
Session Monitoring and Full Visibility
Visibility is critical in OT environments where even minor changes can have major consequences. PAM provides real-time session monitoring and detailed recordings, enabling organizations to track every action performed on critical systems, detect anomalies early, and maintain a complete audit trail for security and compliance.
Just-in-Time Access for Least Privilege
Standing access increases risk by leaving privileged accounts exposed for extended periods. PAM enforces just-in-time access by granting permissions only when required and revoking them immediately after use, reducing the attack window and ensuring access aligns strictly with operational needs.
Agentless Deployment for Legacy Systems
OT environments demand non-intrusive security solutions that do not interfere with system performance or stability. PAM enables agentless deployment, allowing organizations to secure access without installing software on critical devices, ensuring compatibility with legacy systems while maintaining operational continuity.
Benefits of Implementing PAM in OT
Reduced Attack Surface
PAM significantly reduces the number of potential entry points for attackers by limiting access to only what is necessary. This makes it more difficult for threats to move laterally within the environment.
Improved Compliance and Audit Readiness
Regulatory frameworks such as NERC CIP and IEC 62443 require strict access controls and audit capabilities. PAM provides the necessary tools to meet these requirements, including detailed logs, session recordings, and policy enforcement mechanisms.
Enhanced Operational Continuity
OT environments depend on stability and uptime. By preventing unauthorized or accidental changes, PAM helps ensure that systems continue to operate reliably. This is particularly important in industries where downtime can result in significant financial or operational impact.
Stronger Security for Critical Infrastructure
PAM strengthens security across industries by protecting the systems that drive production and service delivery. It ensures that access is controlled, monitored, and aligned with operational needs.
Secure and Controlled Vendor Access
By transforming vendor access into a controlled process, PAM enables organizations to collaborate with third parties securely. This reduces risk while maintaining the flexibility needed for maintenance and support.
Best Practices for PAM Architecture in OT
Use a Gateway-Based Access Model
A gateway-based architecture introduces a controlled entry point between users and OT systems. Instead of connecting directly, users access systems through a PAM gateway that enforces authentication, authorization, and monitoring.
This model centralizes control and ensures that all access is subject to consistent policies. It also simplifies auditing by consolidating access logs and session data in one place.
Enforce the No Direct Access Principle
Direct access to critical systems should be eliminated wherever possible. By ensuring that all interactions go through PAM, organizations can maintain full visibility and control.
This approach reduces the risk of unauthorized access and ensures that even privileged users cannot bypass security controls.
Align with Network Segmentation
OT environments often rely on segmented networks to isolate critical systems. PAM should complement this strategy by acting as a secure bridge between segments.
By integrating with existing segmentation, PAM enhances security without adding unnecessary complexity or disrupting established architectures.
Enable Continuous Monitoring and Auditing
Security in OT is not a one-time implementation. It requires continuous monitoring and analysis.
PAM enables this by providing detailed logs and session recordings that can be used for both real-time monitoring and retrospective analysis. This ensures that organizations can detect anomalies, investigate incidents, and maintain compliance over time.
miniOrange PAM for OT Environments
Traditional PAM solutions often struggle in OT environments because they are designed for IT-first use cases. They rely on agents, require complex infrastructure, and can disrupt sensitive systems.
miniOrange PAM Solution is built with a different approach, lightweight, identity-centric, and OT-aware.
Designed for OT Realities
miniOrange PAM supports agentless deployment, making it ideal for legacy environments where installing software is not feasible. It integrates seamlessly with existing infrastructure without impacting system performance or uptime.
Secure Remote Access Without Complexity
Instead of relying on VPNs, miniOrange enables secure remote access for OT through a browser-based interface. This ensures:
- No network-level exposure
- Granular access to specific systems
- Easy onboarding for vendors and third parties
Strong Identity-Centric Access Control
Every access request is tied to a verified identity. miniOrange enforces:
- Role-based access controls
- Least privilege policies
- Just-in-time access
This ensures that users only get access when needed and only to what they need.
Complete Session Visibility and Control
miniOrange provides full session monitoring and recording, allowing organizations to:
- Track all user activity
- Detect anomalies in real time
- Maintain audit-ready logs
This is critical for both security and compliance.
Scalable and Easy to Deploy
Unlike traditional solutions that require heavy setup, miniOrange PAM is designed for quick deployment and scalability. It works across:
- Manufacturing environments
- Utilities and energy sectors
- Mid-sized enterprises with OT infrastructure
Future of PAM in OT and IoT Security
Identity Becomes the New Security Perimeter
As environments become more distributed, traditional network boundaries lose their effectiveness. Identity becomes the primary control point, and PAM plays a central role in managing and securing these identities.
Rise of Machine Identity Management
The growth of IoT introduces a new challenge: managing non-human identities. Devices, sensors, and systems all require secure authentication and authorization. PAM will evolve to manage these identities alongside human users, ensuring consistent security across the environment.
Zero Trust for OT and IoT
Zero Trust principles will become standard in industrial environments. Access will be continuously verified based on identity, context, and behavior, reducing reliance on implicit trust.
AI-Driven Access Decisions
Artificial intelligence will enhance PAM capabilities by analyzing user behavior, detecting anomalies, and dynamically adjusting access policies.
Convergence of IT, OT, and IoT Security
As these environments converge, organizations will need unified solutions that can manage access across all domains. PAM will serve as a central layer that ensures consistent security across interconnected systems.
Rethinking OT Security Starts with Identity Control
OT environments are entering a new phase of connectivity, and with that comes a new class of risks. The traditional approach of relying on network security and implicit trust is no longer sufficient. Attackers are targeting identities, exploiting access pathways, and leveraging interconnected systems to reach critical infrastructure.
PAM provides a way forward by shifting the focus from networks to identities. It ensures that every access request is controlled, every session is visible, and every action is accountable. For organizations looking to secure industrial environments without compromising operations, PAM is not just a tool. It is a foundational layer for building resilient, future-ready OT security.
FAQs
What is PAM for OT environments?
PAM for OT environments is a security solution that controls and monitors access to industrial systems, ensuring secure and auditable interactions.
How is PAM different in OT compared to IT?
OT PAM is designed to be agentless and non-intrusive, making it suitable for legacy systems, whereas IT PAM often relies on agents and direct system control.
Why is secure remote access important in OT?
Remote access is a major attack vector. PAM secures it by providing controlled, monitored, and identity-based access without exposing networks.
Can PAM help with IoT security?
Yes, modern PAM solutions extend to IoT by managing device identities and controlling access between devices and systems.
What industries benefit from PAM for OT?
Industries such as manufacturing, energy, utilities, and critical infrastructure benefit significantly from implementing PAM.
How does PAM improve compliance?
PAM provides detailed logs, session recordings, and access controls that help organizations meet regulatory requirements and maintain audit readiness.


Leave a Comment