Need Help? We are right here!
Search Results:
×A directory service is a crucial database designed to store and manage user & resources. It is often called Directory as a Service (DAAS), directories, user stores, Identity Stores, or LDAP directories. Directory services are essential tools for network and system admins to efficiently manage user onboarding, access privilege management, regulate apps, and monitor infrastructure access. Directory services play a vital role in Identity Security strategies. They are frequently integrated with Identity and Access Management (IAM) solutions, supporting functionalities like Single Sign-On (SSO), Multifactor Authentication (MFA), Identity Lifecycle Management, Adaptive Authentication, Role-Based Access (RBAC), and Privilege Access Management (PAM).
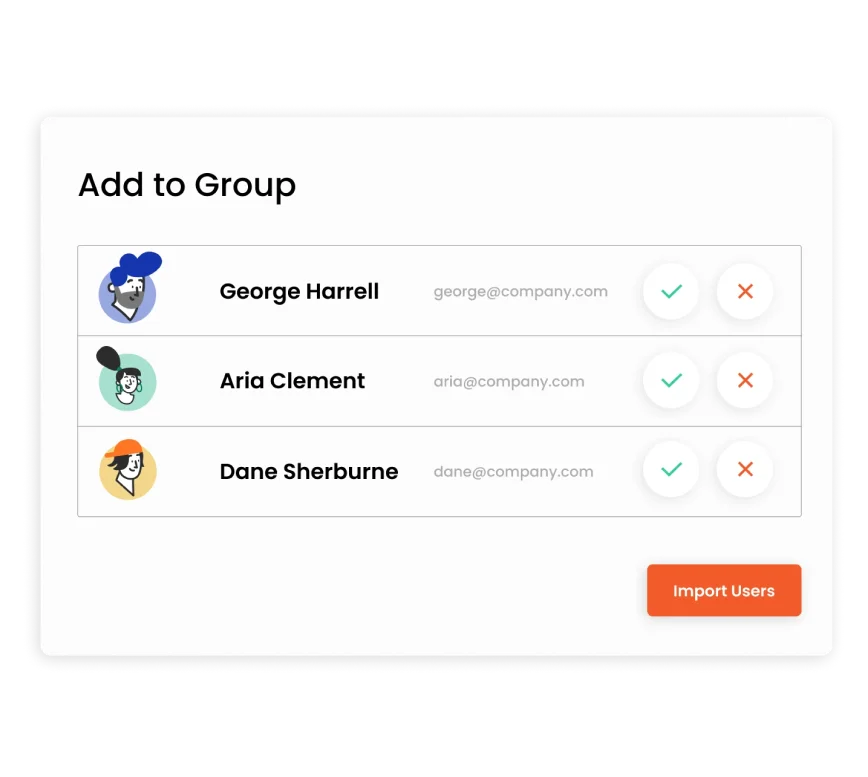
Easily provision users across platforms with Directory Service, connecting devices, apps, servers, and cloud infrastructure. miniOrange DaaS offers a unified view of data. SCIM and JIT Provisioning simplify user management and enhance security with access controls based on identity source data.
Directory Service unifies user profiles, manages attributes, and syncs changes in real-time. It auto-creates users during authentication. Set access policies based on location, IP, and device with MFA for added security. Group-based password policies and self-service resets reduce IT helpdesk burden.
Migrate from AD and LDAP to a cloud directory, storing unlimited users with custom attributes and app allocations. With miniOrange, access real-time logs for troubleshooting, pre-built reports for usage insights, and export data via CSV or API.
Single Sign-On (SSO) allows users to access web and on-premise apps with one set of credentials. Without managing on-premise endpoints, users can connect to applications, file servers, and control VPN/Wi-Fi access via a browser. Adding MFA further secures accounts.
*Please contact us to get volume discounts for higher user tiers.
Admins can add multiple Active directories (AD)/Identity Sources, and use them as a single user store, preventing the need to manage directories in separate places.
Automatically provision and administrate multiple on-premise and cloud application accounts from one centralized system.
Real-time synchronization in Directory Service reflects a minor attribute change in a single source to all your identity sources at the same time.
Identity solutions from miniOrange can be easily deployed in your organization's existing environment.
Directory Service and Active Directory are both a part of Identity and Access Management (IAM). Directory Service is a user database which includes email addresses, passwords, user preferences, and information about devices and networks. UD is usually software implemented and distributed among multiple servers. Directory Service can connect with all sorts of directories like On-Premise Active Directory (AD), user stores, Identity Stores, or LDAP.
In contrast, Active Directory is a Microsoft product and primarily provides identity management services like organizing users, computers, and printers. Active Directory can only be integrated AD eases the management of users and computers by storing information about them in a single directory.
Due to the difference in functionality between these two directories, enterprises can combine a combination of features to create their identity management solution as required.
In an identity management system, a cloud directory stores and manages user identities in the cloud. With this centralized platform, users can be authenticated across a wide range of devices and applications. miniOrange directory as a service integrates multiple Directories to get a single Cloud directory to manage users, groups and their access.
LDAP (Lightweight Directory Access Protocol) works with Active Directory by providing a standard protocol for accessing and managing directory information, including user authentication and authorization.
Enterprise-level directory services, such as Microsoft Active Directory, offer several key features:
