Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
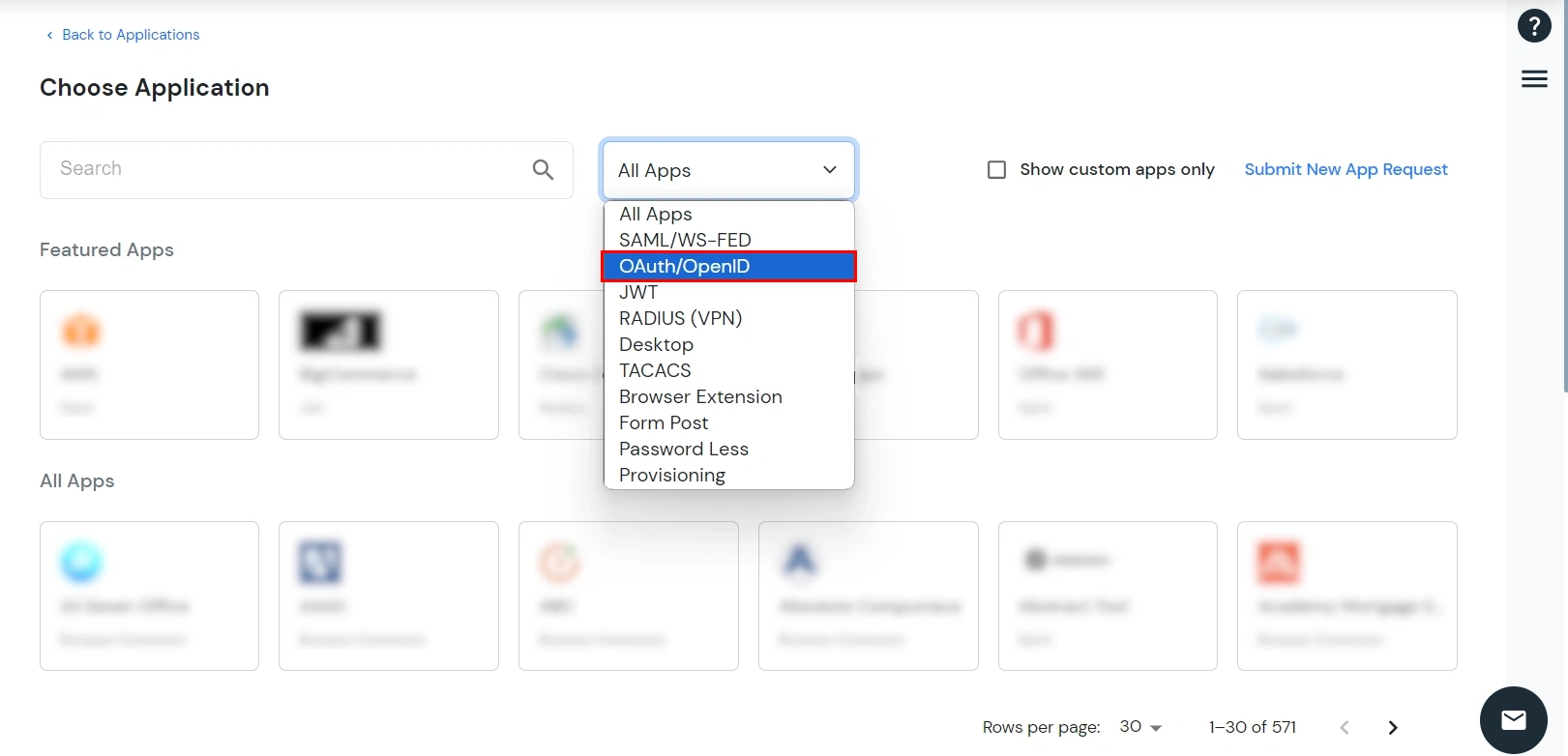
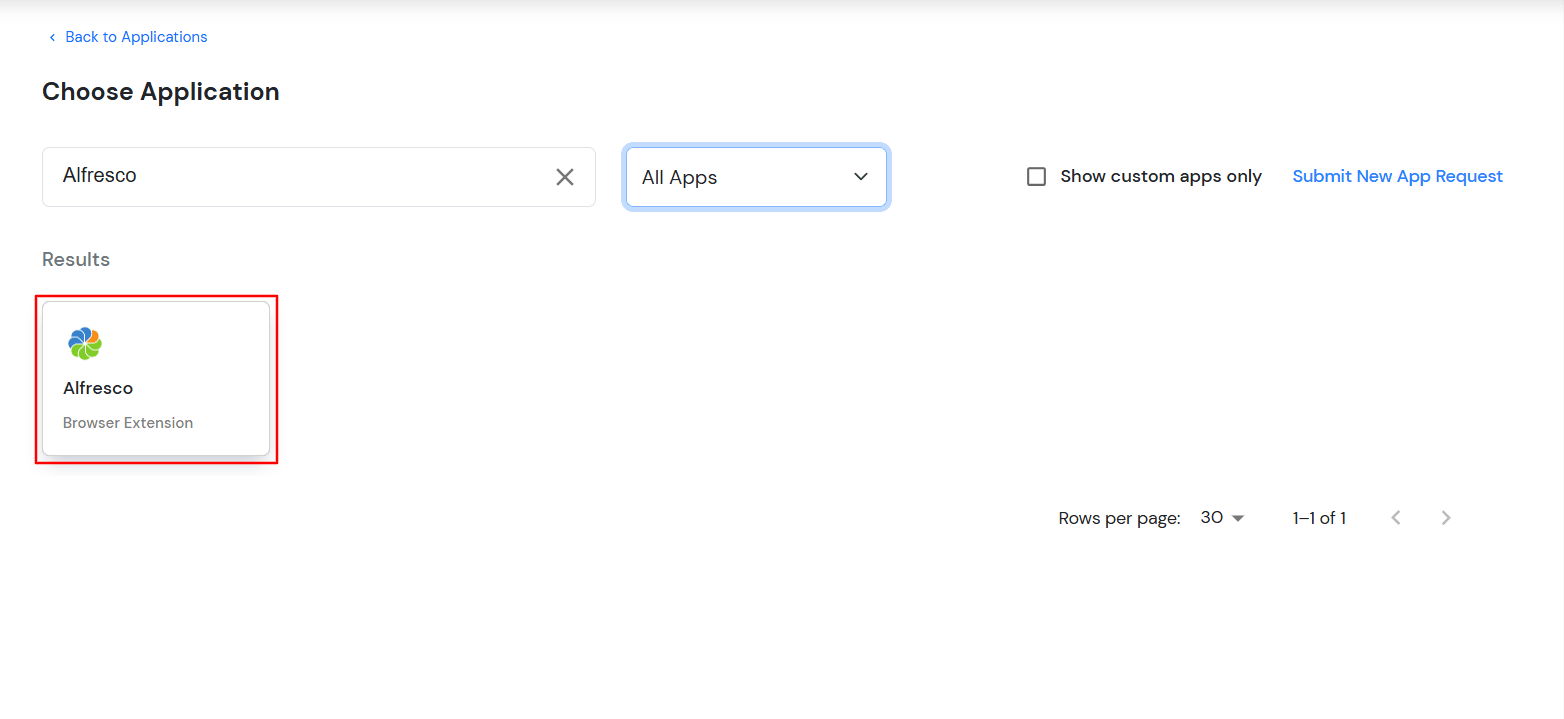
×miniOrange provides secure access to Alfresco for enterprises and full control over access of Alfresco application. Single Sign-On (SSO) solution for Alfresco is a cloud based service. With this service you need only one password for all your web & SaaS apps including Alfresco. miniOrange provides secure access and full control to Alfresco for enterprises and applications. With the help of the given guide you can configure Alfresco easily.
miniOrange offers 1 hour free help through a consultation call with our System Engineers to Install or Setup Alfresco SSO SAML solution in your environment with 30 days free trial. For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you setting it up in no time.

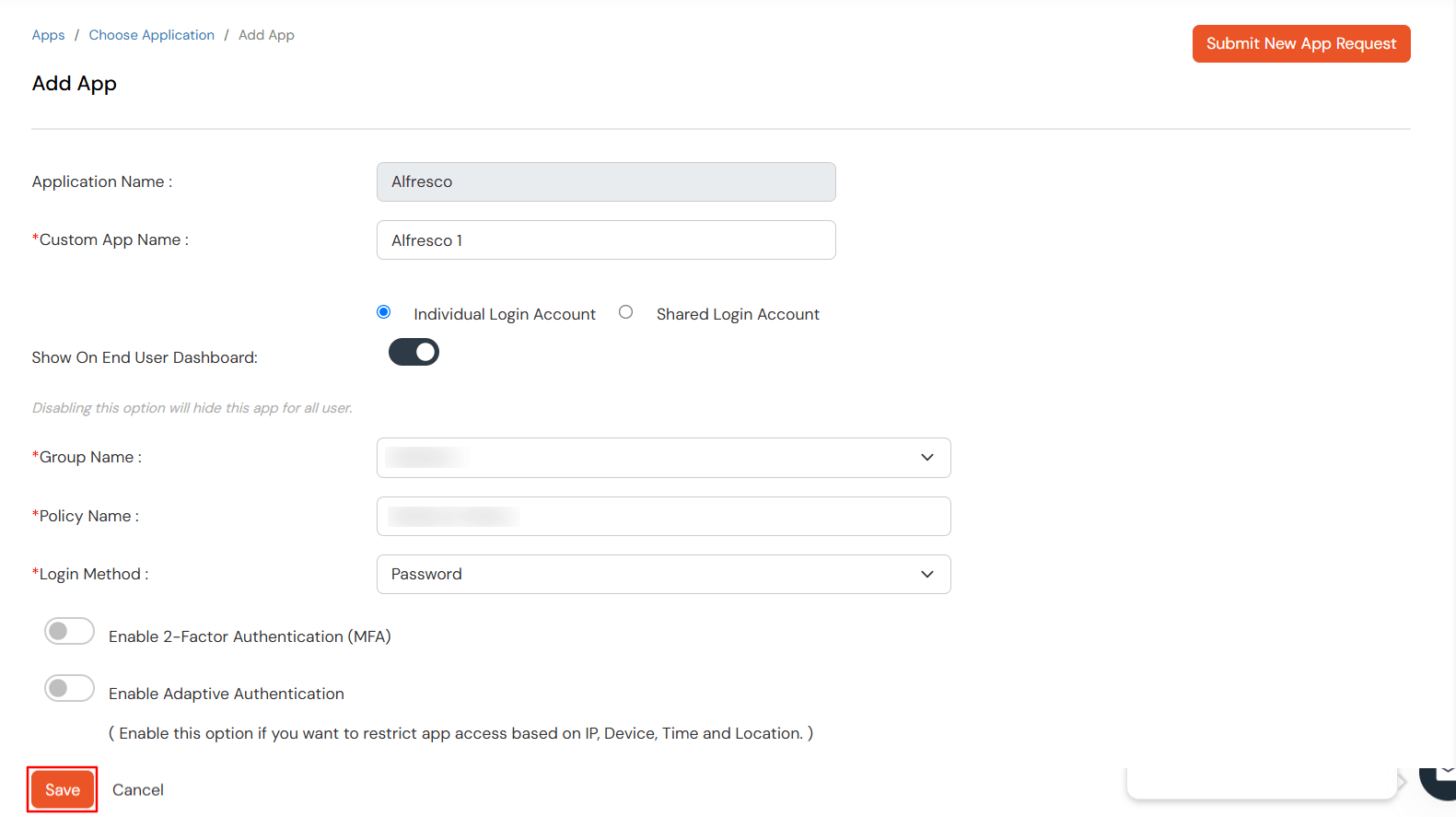
| Basic Tabs | Description |
|---|---|
| Application Name: | The pre-selected app from the catalog in this case, Alfresco is automatically filled in. |
| Custom App Name | Provide a unique name for this app instance to differentiate it from others. |
| Individual Login Account | Each user logs in with their own unique credentials specific to this application. |
| Shared Login Account: | All users access the application using the same set of shared credentials configured by the admin. |
| Show on End User Dashboard | Enabling this option displays the application on the user's dashboard for easy access. |
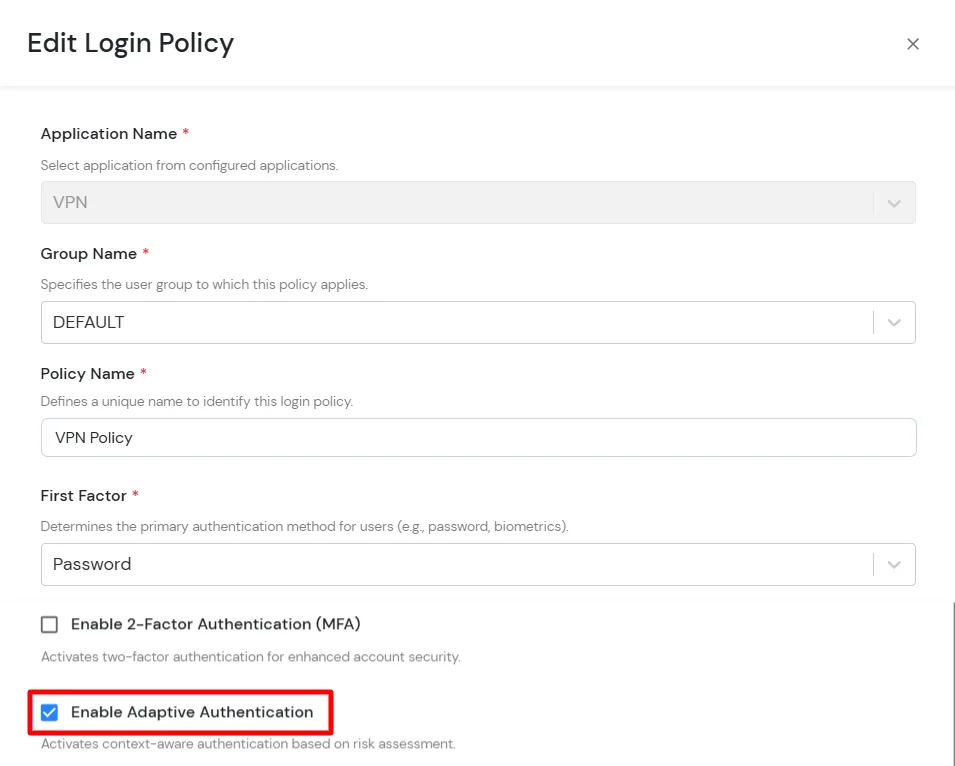
| Group Name | Select the group for which you wish to add a this policy. For multiple groups, you can click here to add a multiple/separate policies for each group. |
| Policy Name | You can give a name for the authentication policy. |
| Login Method | Select how users authenticate—choose Password for traditional login or Passwordless Login for seamless access. |
| Enable MFA (Optional) | Toggle to enable 2-Factor Authentication for enhanced login security if required. |
| Enable Adaptive Authentication (Optional) | Activate this to enforce access based on user’s IP, device, location, and time conditions. |
<alfresco_root_folder>\tomcat\shared\classes\alfresco\web-extension\share-config-custom.XML
Note:
<config evaluator="string-compare" condition="Remote">
</config>
<connector>
<id>alfrescoHeader</id>
<name>Alfresco Connector</name>
<description>Connects to an Alfresco instance using header and cookie-based authentication</description>
<class>org.alfresco.web.site.servlet.SlingshotAlfrescoConnector</class>
<userHeader>X-Alfresco-Remote-User</userHeader>
</connector>
<endpoint>
<id>alfresco</id>
<name>Alfresco - user access</name>
<description>Access to Alfresco Repository WebScripts that require user authentication</description>
<connector-id>alfrescoHeader</connector-id>
<endpoint-url>http://<alfresco_base_url>/alfresco/wcs</endpoint-url>
<identity>user</identity>
<external-auth>true</external-auth>
</endpoint>
<alfresco_root_folder>\tomcat\shared\classes\alfresco-global.properties
### EXTERNAL AUTHENTICATION ###
authentication.chain=external1:external
external.authentication.proxyUserName=
external.authentication.enabled=true
external.authentication.defaultAdministratorUserNames=admin
external.authentication.proxyHeader=X-Alfresco-Remote-User
external.authentication.defaultAdministratorUserNames=admin1,admin2,admin3
# HTTP server
server {
listen 80;
server_name alfresco.example.com;
error_page 401 = @error401;
location @error401 {
return 302 http://<base_url_of_http_connector>/httpauth/sso;
}
location / {
auth_request /auth;
proxy_set_header X-Alfresco-Remote-User $cookie_MO_REMOTE_USER;
#add_header X-Alfresco-Remote-User $cookie_MO_REMOTE_USER;
#proxy_set_header X-Alfresco-Remote-User admin;
#add_header X-Alfresco-Remote-User admin;
proxy_pass http://<localhost:port_for_alfresco>;
}
location = /auth {
internal;
proxy_pass http://<localhost:port_for_http_connector>/siebelauth/check;
}
}
# HTTP server
server {
listen 80;
server_name <base_url_for_http_connector>;
location / {
proxy_pass http://<localhost:port_for_http_connector>;
}
}
| redirect.uri | http://<http_oauth_connector_base_url>/httpauth/redirect |
| client.id | Client Id value |
| client.secret | Client Secret value |
Application.properties (OAuth Connector)
siebel.cookie.name=MO_REMOTE_USER
siebel.cookie.path=/
siebel.cookie.domain=example.com
siebel.app.url=http://alfresco.example.com
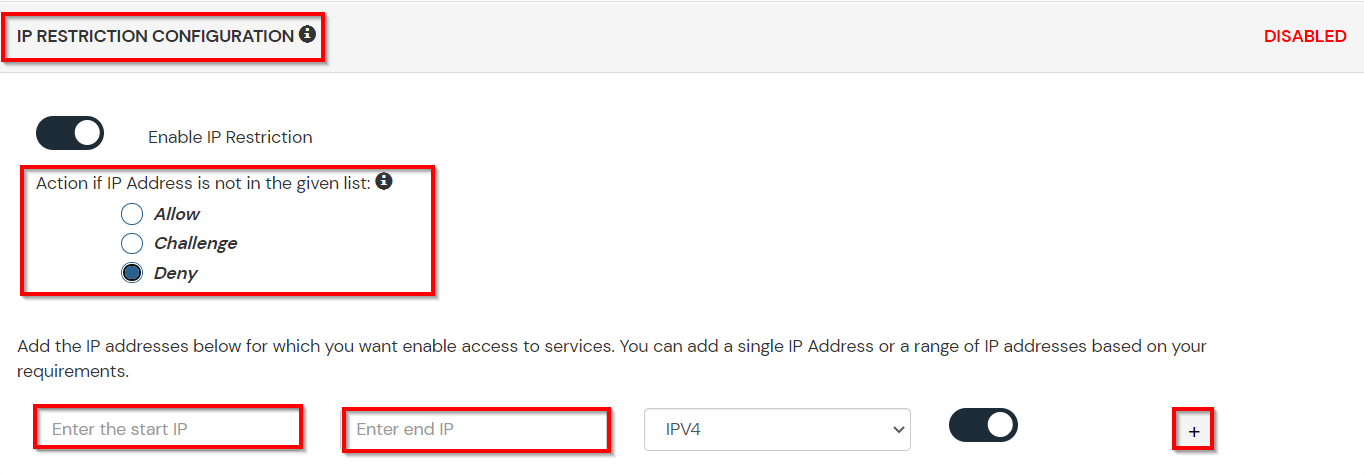
A. Restricting access to Alfresco with IP Configuration
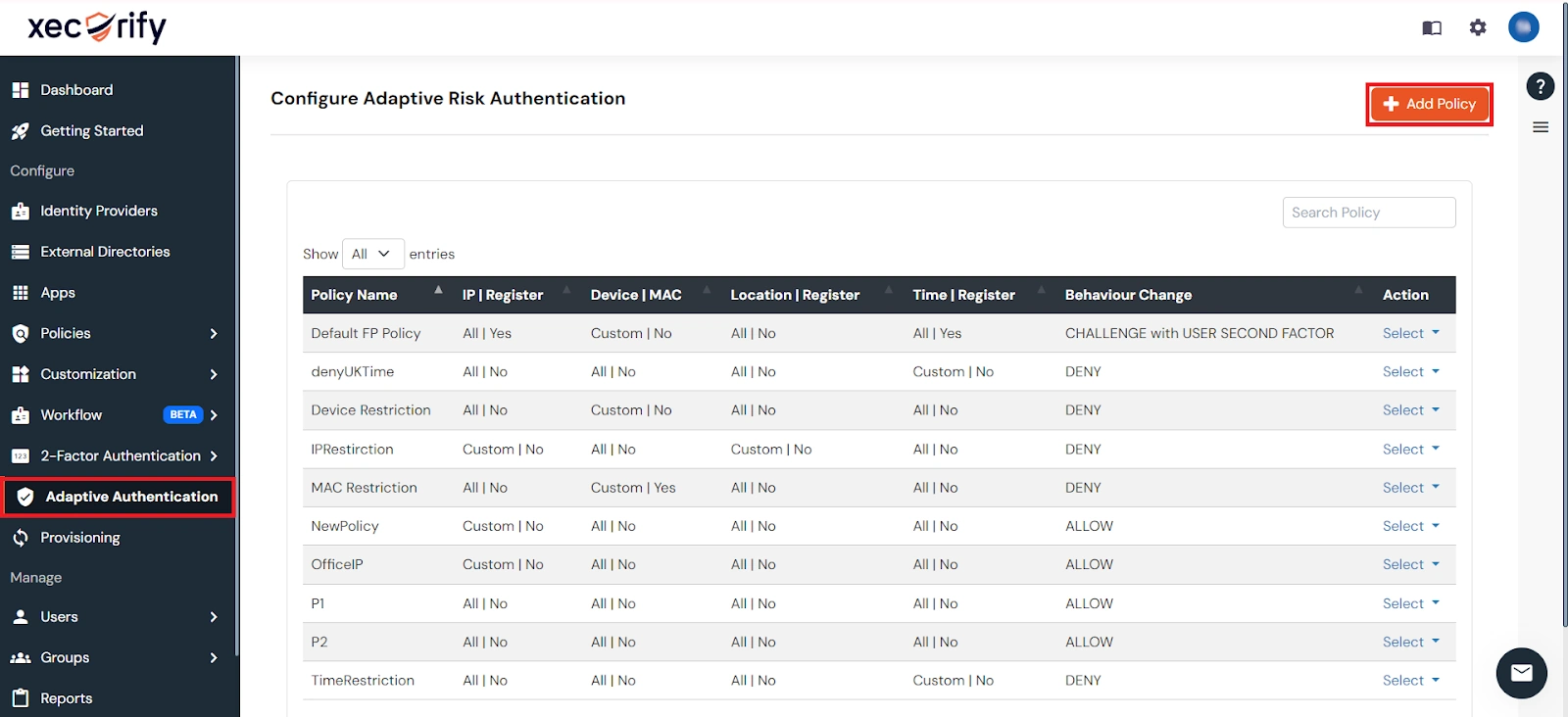
You can use adaptive authentication with Alfresco Single Sign-On (SSO) to improve the security and functionality of Single Sign-On. You can allow a IP Address in certain range for SSO or you can deny it based your requirements and you can also challenge the user to verify his authenticity. Adaptive authentication manages the user authentication bases on different factors such as Device ID, Location, Time of Access, IP Address and many more.
You can configure Adaptive Authentication with IP Blocking in following way :
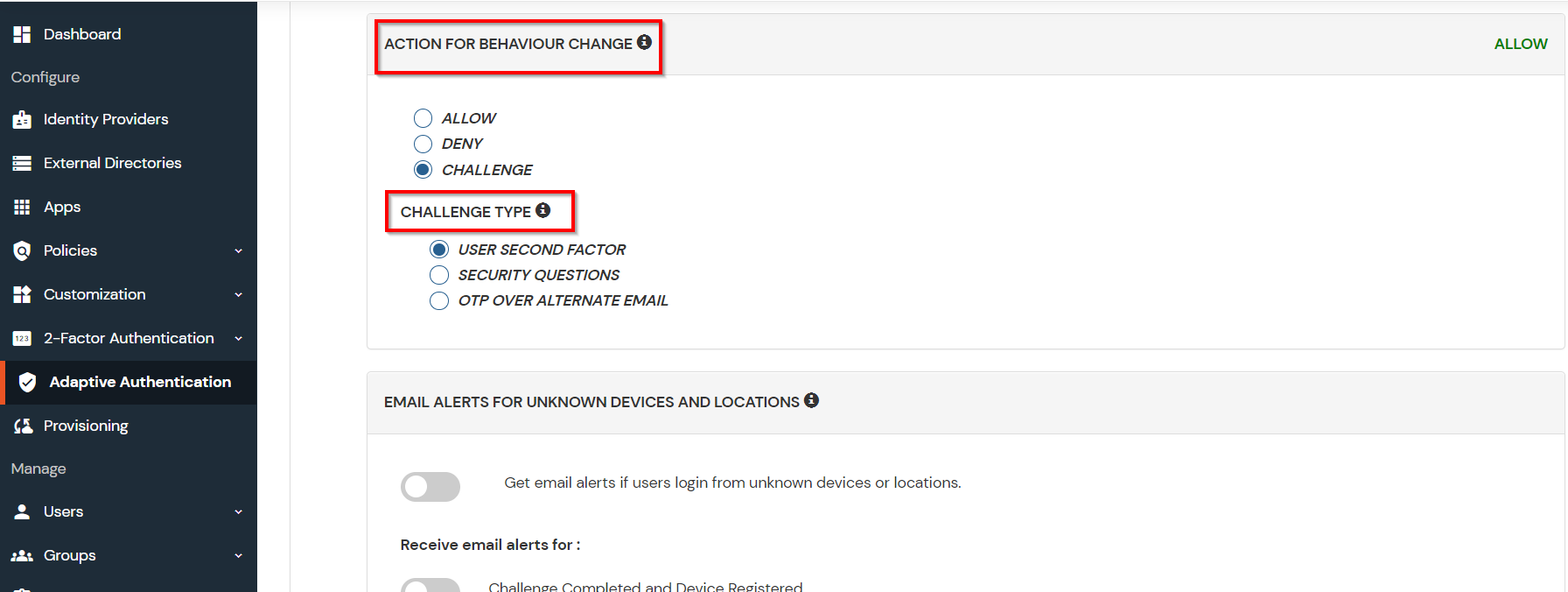
| Attribute | Description |
|---|---|
| Allow | Allow users to authenticate and use services if Adaptive authentication condition is true. |
| Deny | Deny user authentications and access to services if Adaptive authentication condition is true. |
| Challenge | Challenge users with one of the three methods mentioned below for verifying user authenticity. |
| Attribute | Description |
|---|---|
| User second Factor | The User needs to authenticate using the second factor he has opted or assigned for such as
|
| KBA (Knowledge-based authentication) | The System will ask the user for 2 of 3 questions he has configured in his Self-Service Console. Only after the right answer to both questions is the user allowed to proceed further. |
| OTP over Alternate Email | User will receive an OTP on the alternate email they have configured through the Self Service Console. Once the user provides the correct OTP, they are allowed to proceed further. |
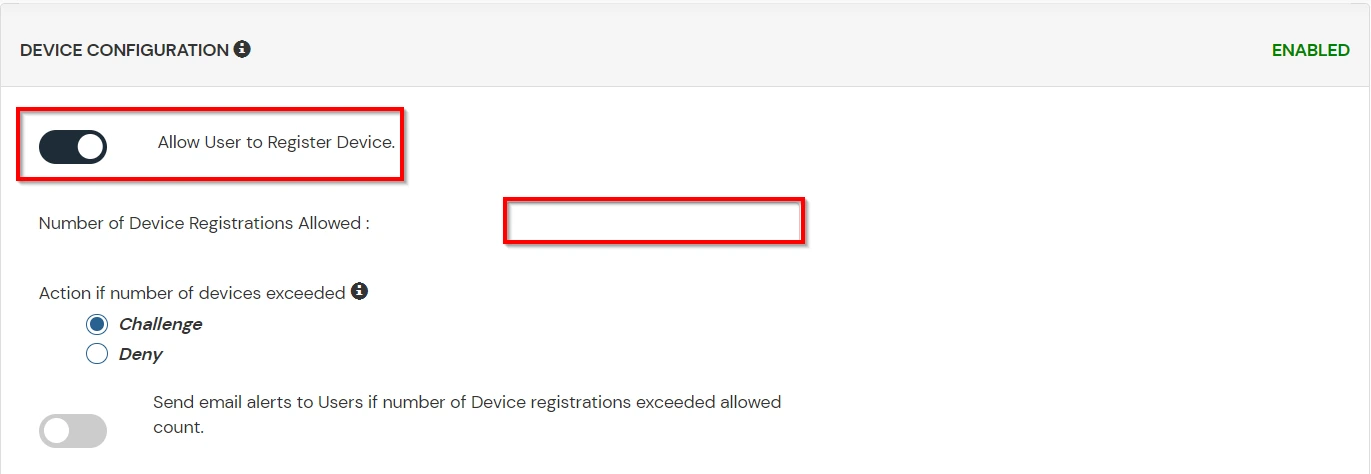
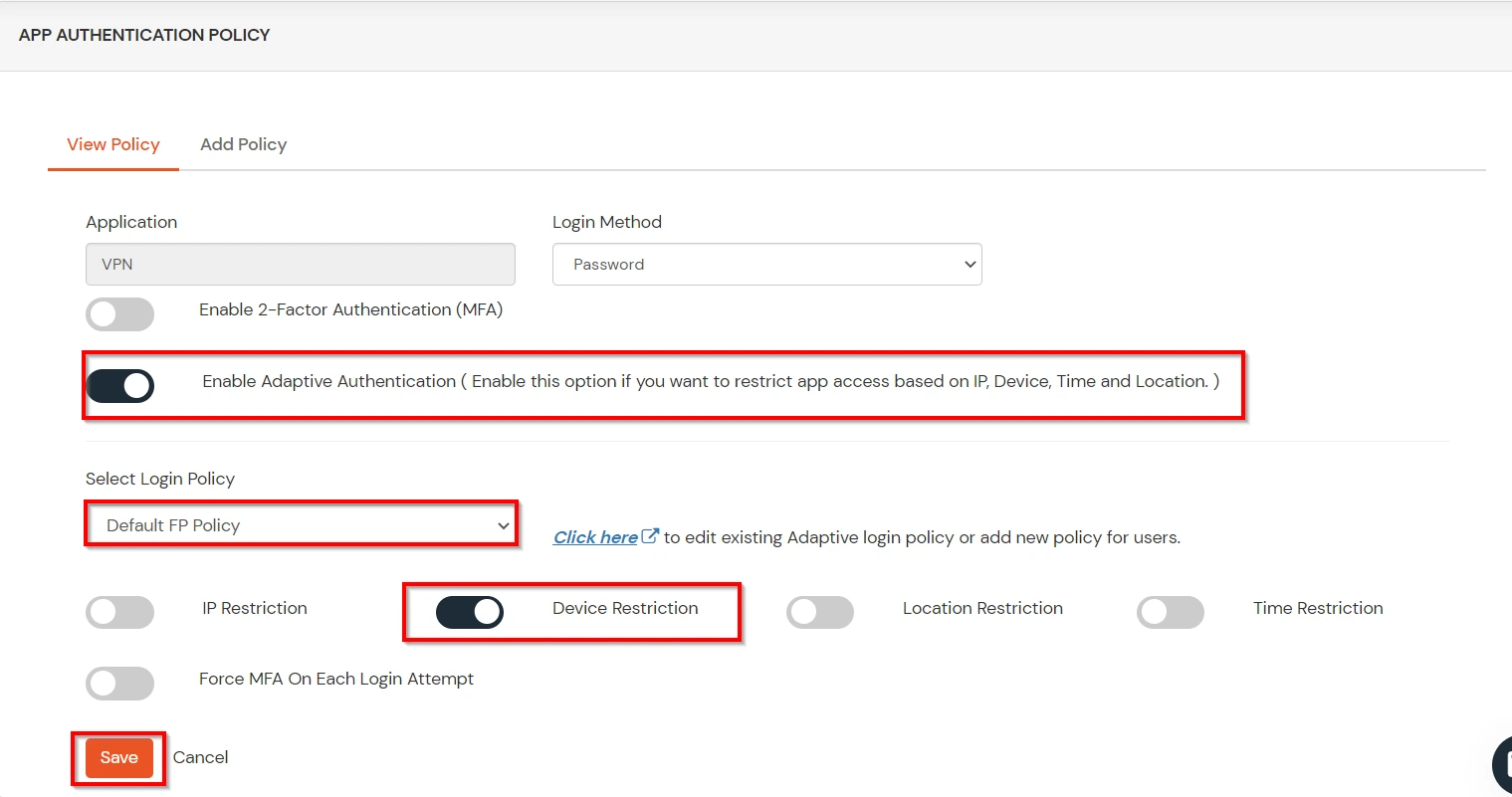
B. Adaptive Authentication with Limiting number of devices
Using Adaptive Authentication you can also restrict the number of devices the end user can access the Services on. You can allow end users to access services on a fixed no. of devices. The end users will be able to access services provided by us on this fixed no. of devices.
You can configure Adaptive Authentication with Device Restriction in following way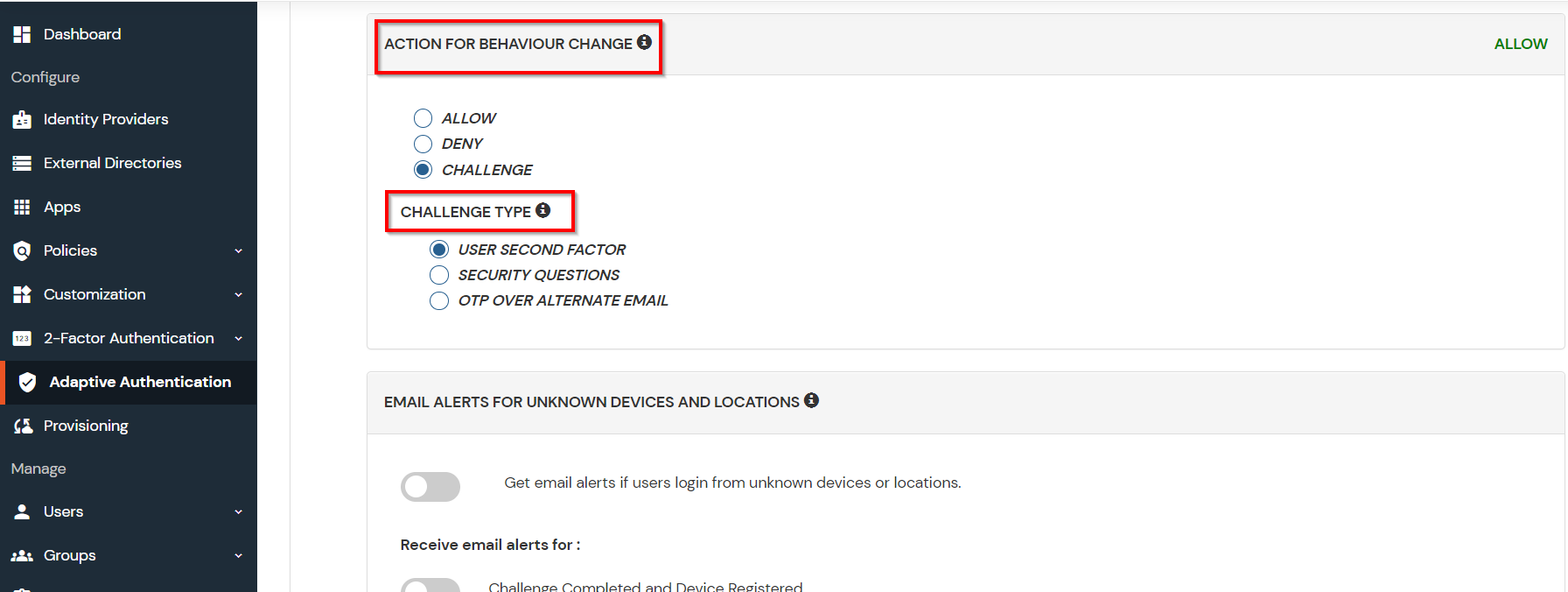
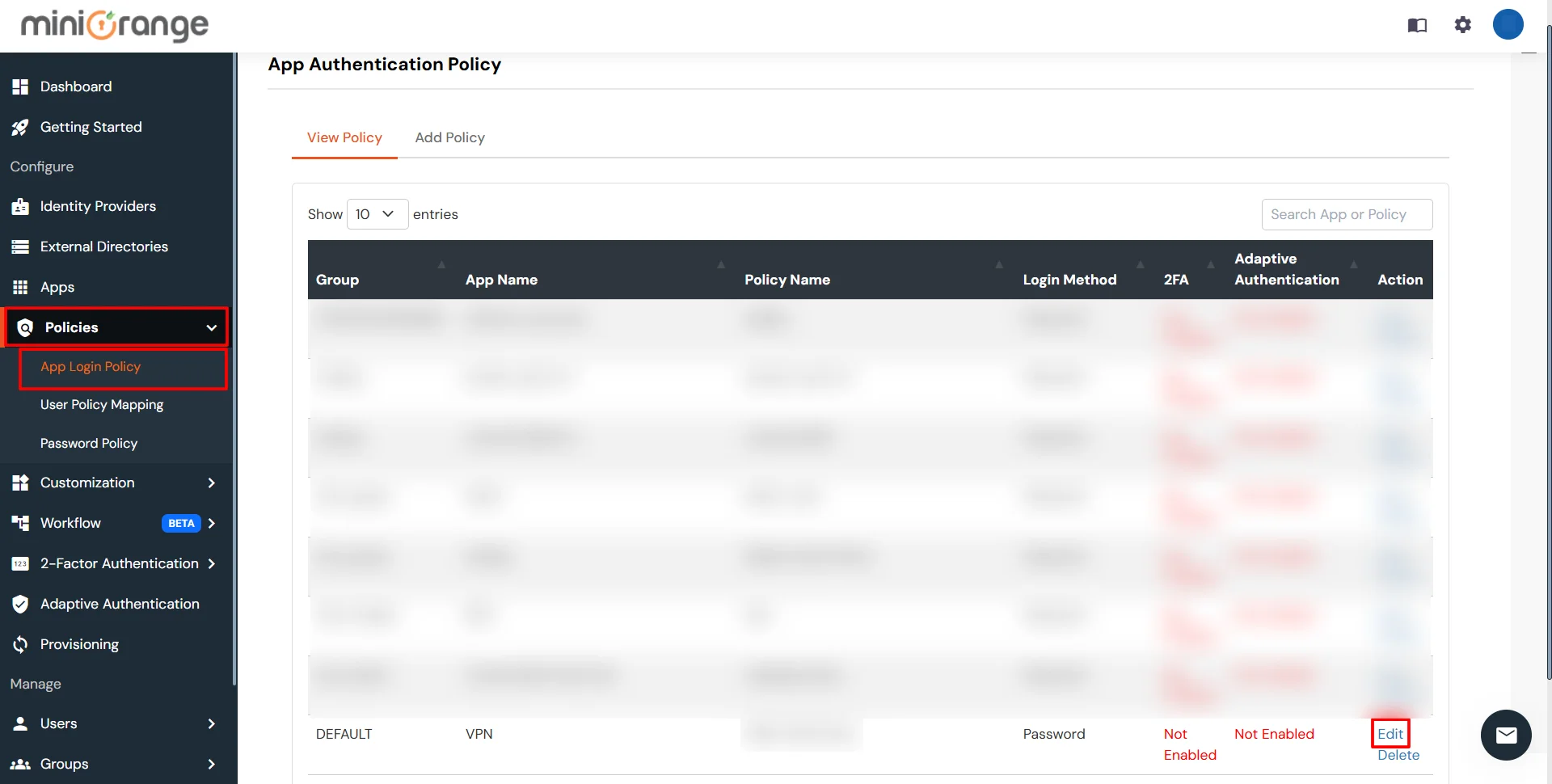
C. Add Adaptive Authentication policy to Alfresco
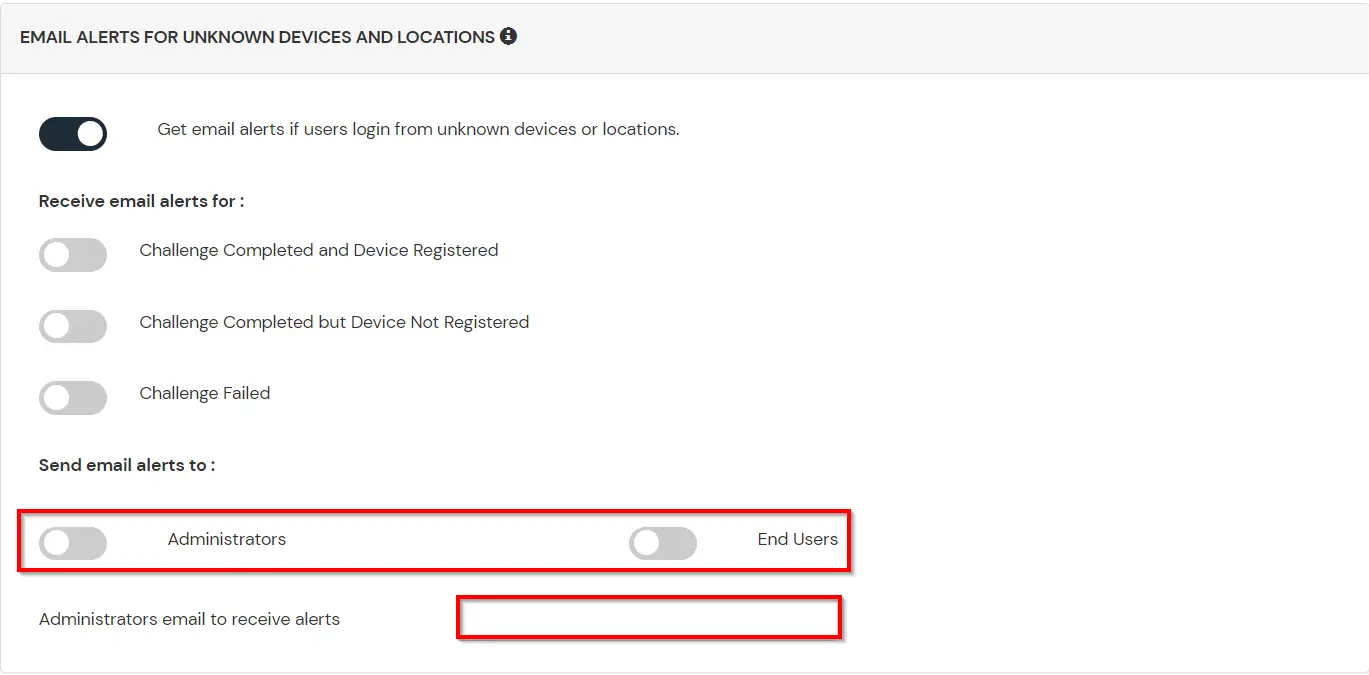
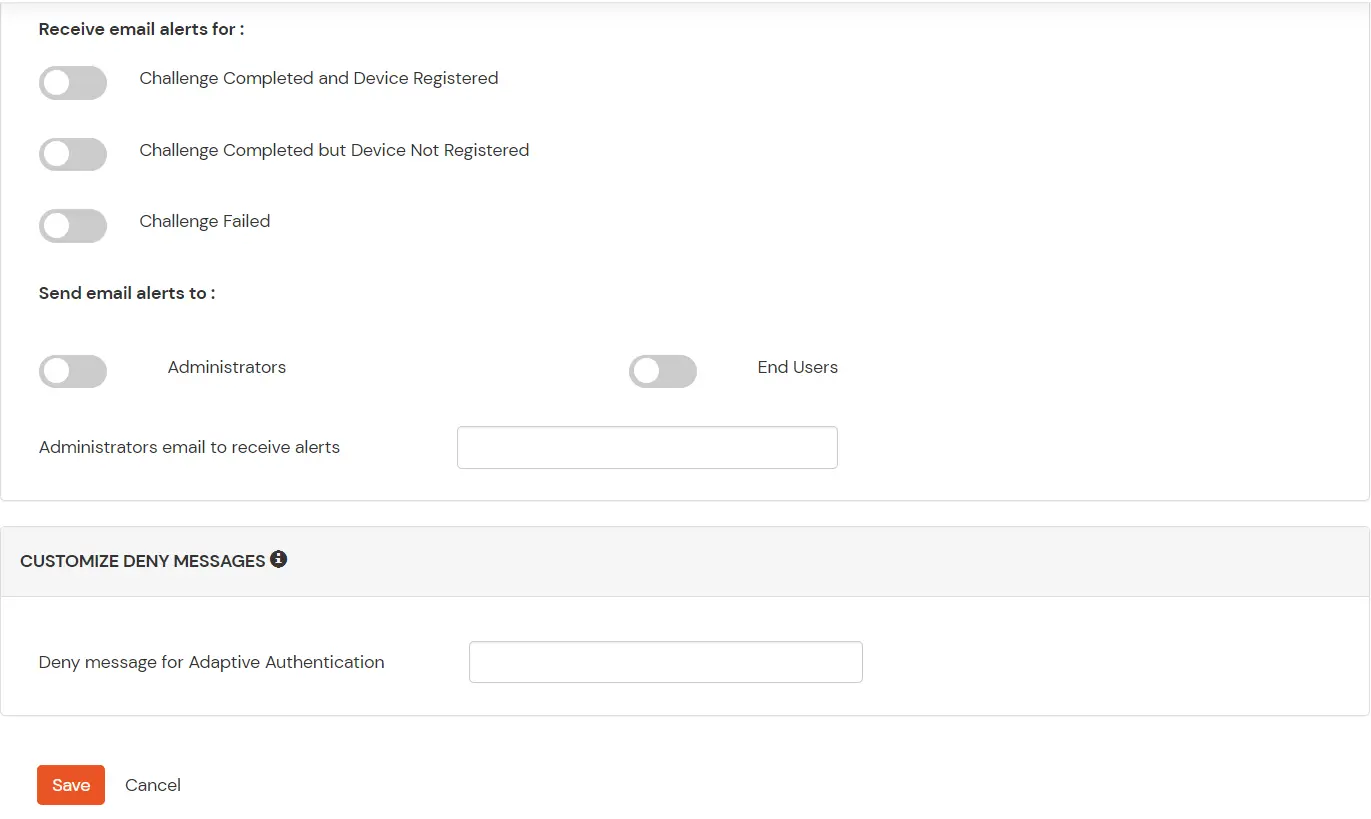
D. Notification and Alert Message.
This section handles the notifications and alerts related to Adaptive Authentication. It provides the following options :
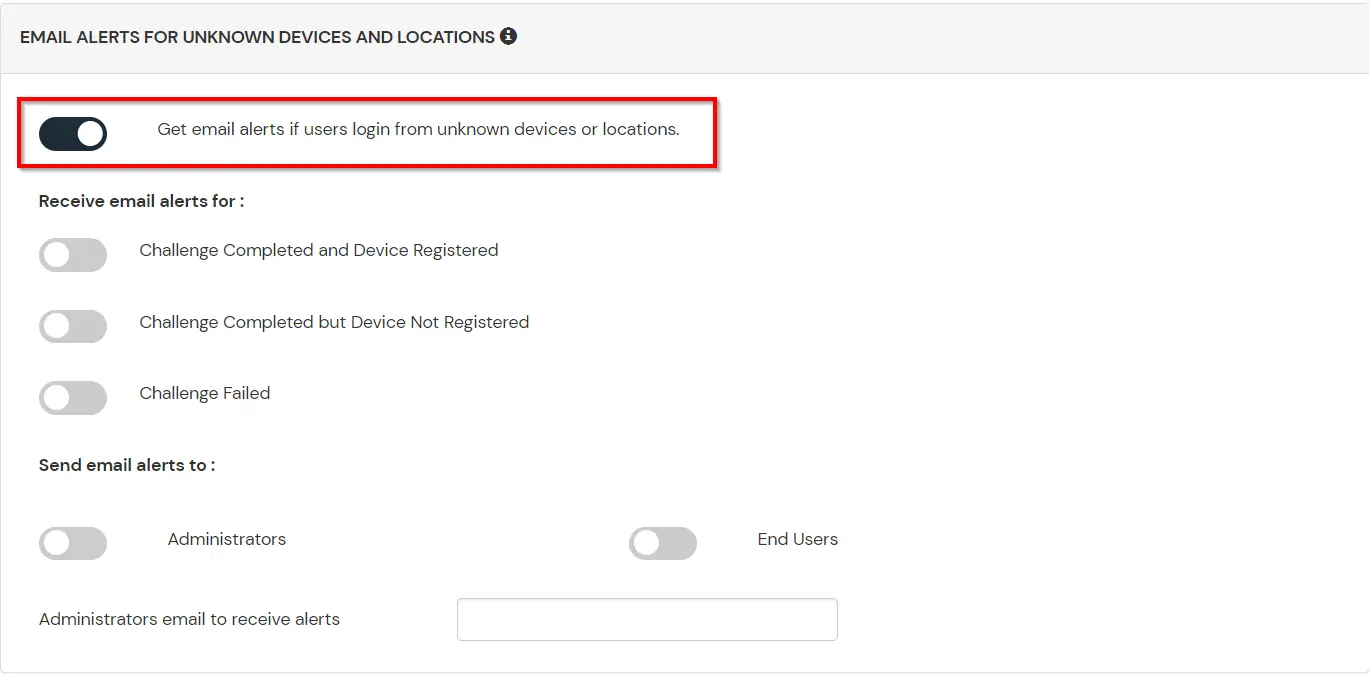
| Option | Description |
|---|---|
| Users login from unknown IP addresses, devices or locations | Enabling this option allows you to login from unknown IP addresses or devices and even locations. |
| Number of Device registrations exceeded allowed count | This option will allow you to register more devices than the devices you have numbered. |
| Challenge Completed and Device Registered | Enabling this option allows you to send an email alert when an end-user completes a challenge and registers a device. |
| Challenge Completed but Device Not Registered | Enabling this option allows you to send an email alert when an end-user completes a challenge but do not registers the device. |
| Challenge Failed | Enabling this option allows you to send an email alert when an end-user fails to complete the challenge. |