Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
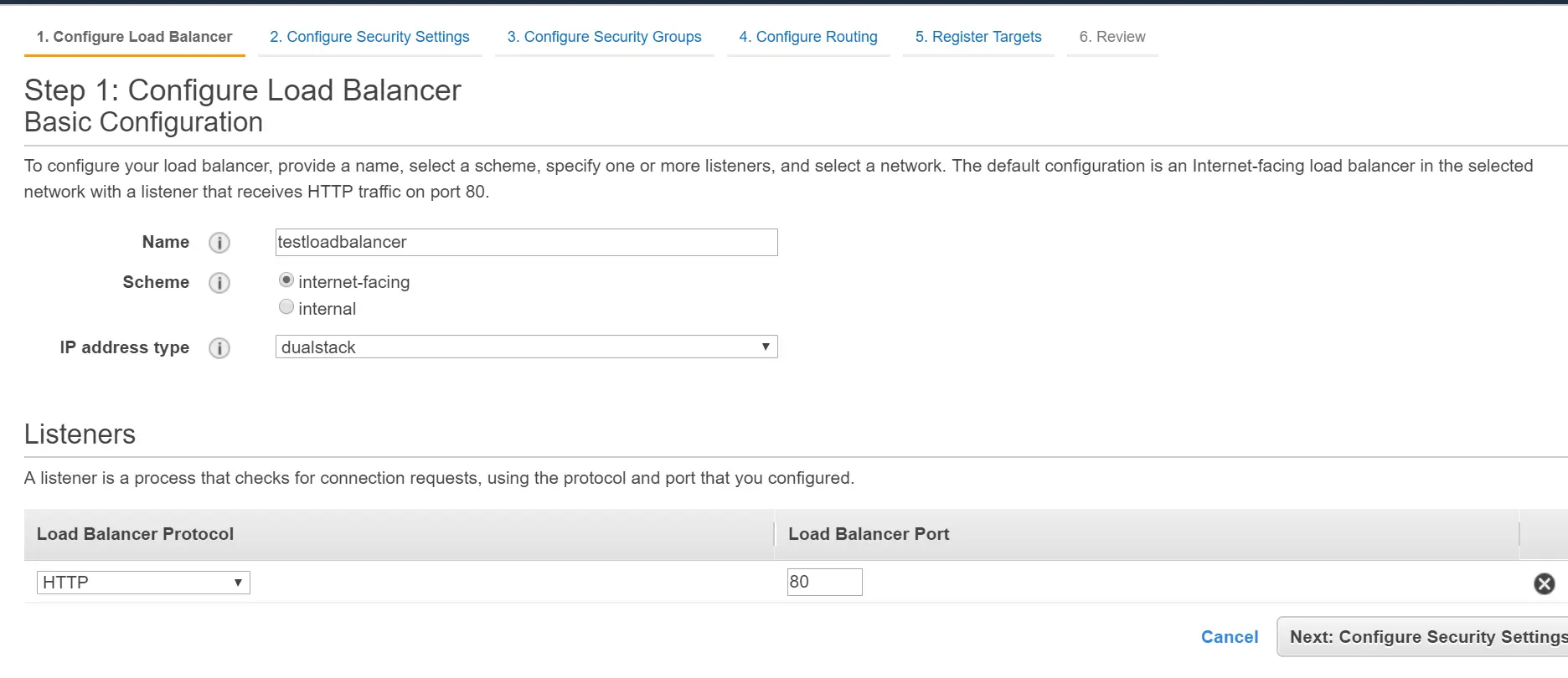
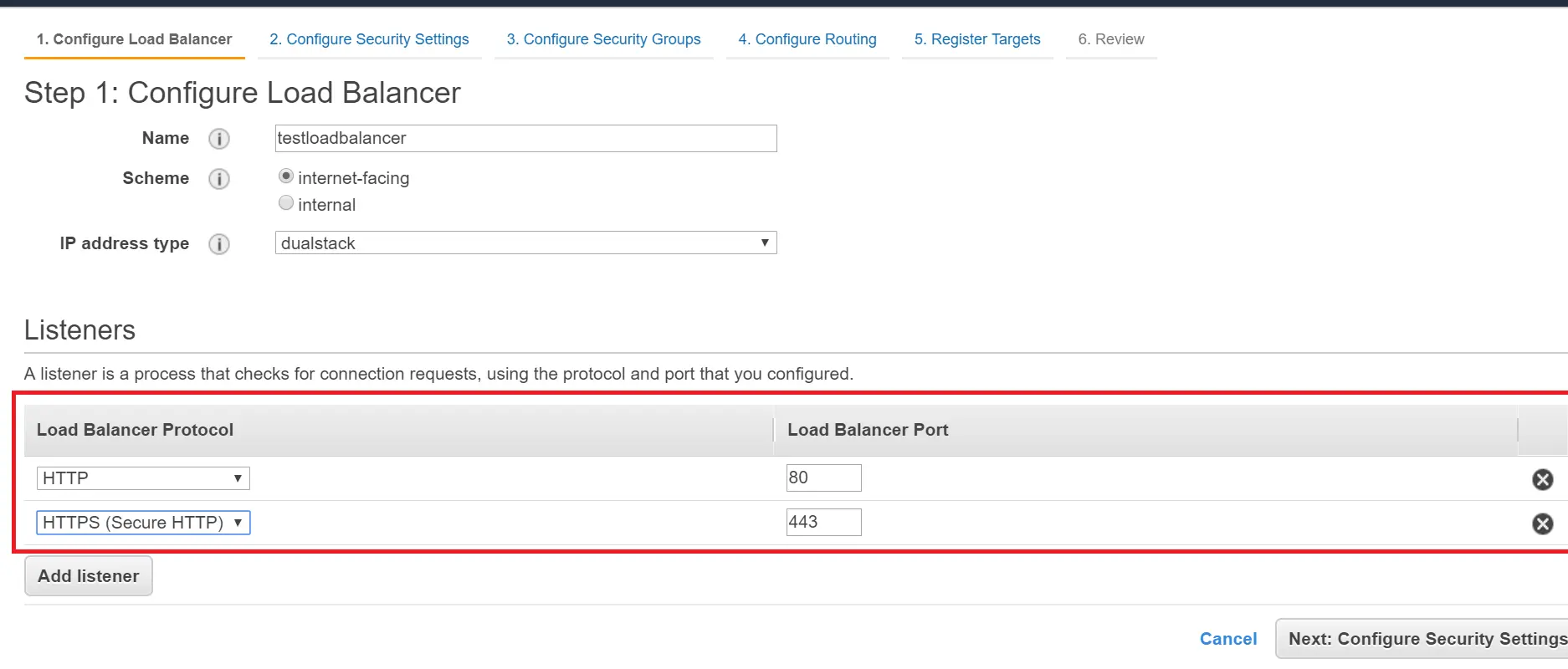
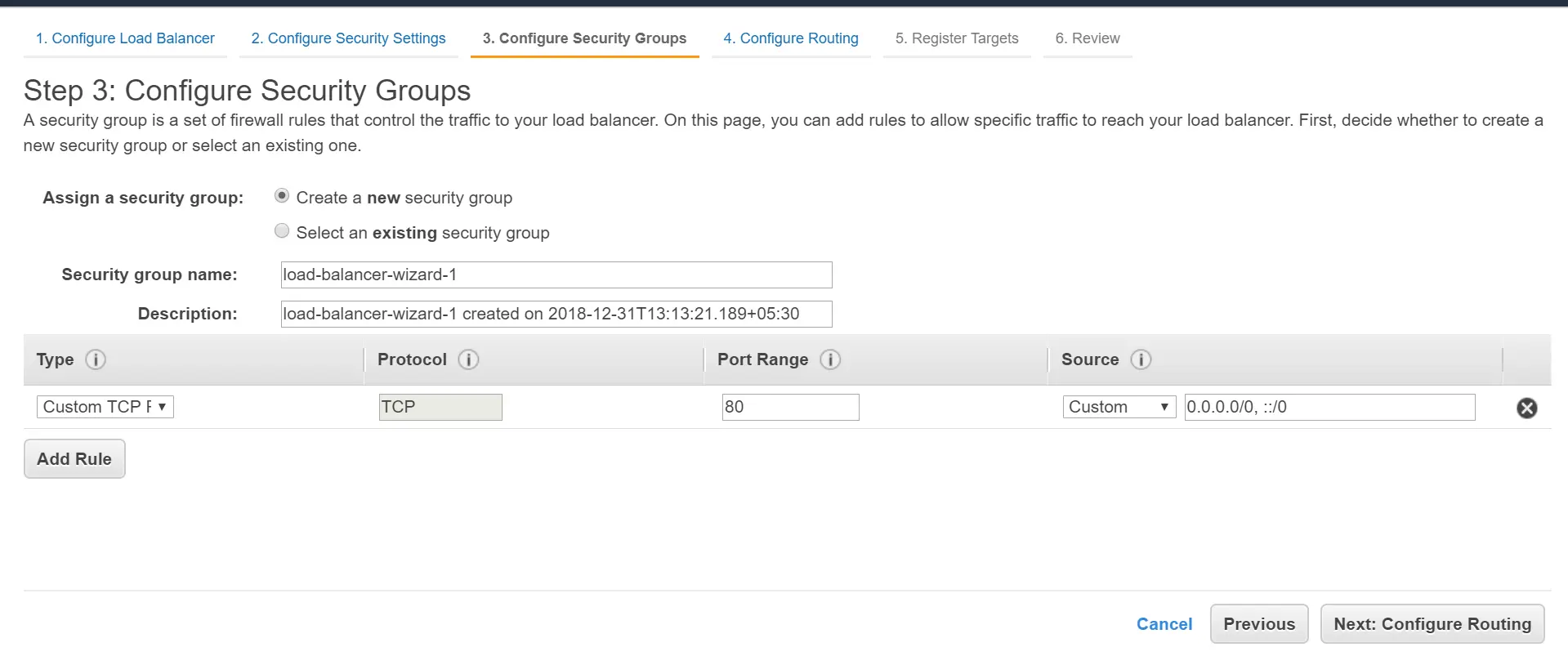
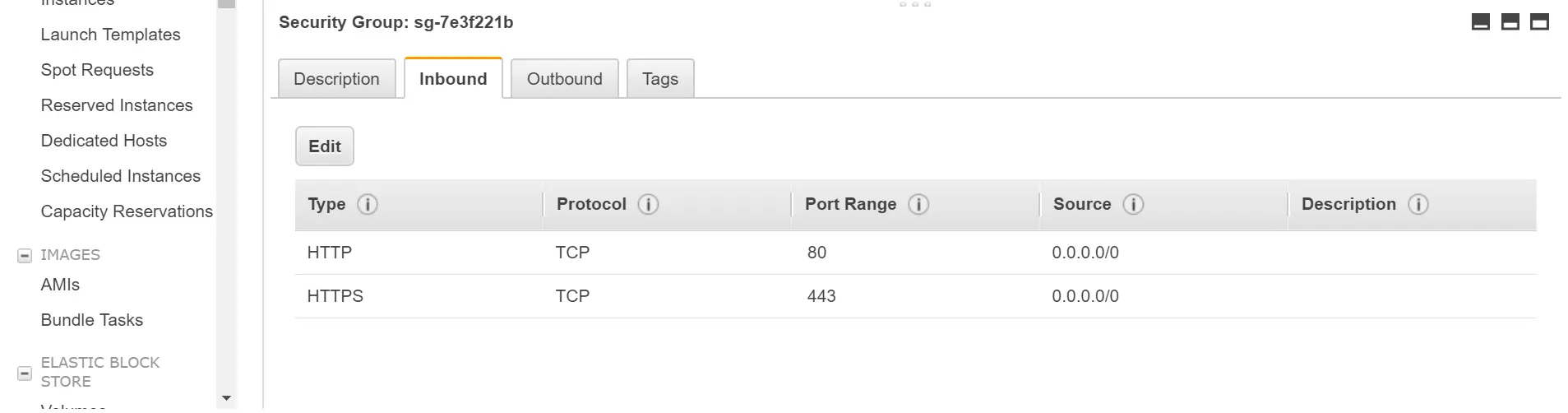
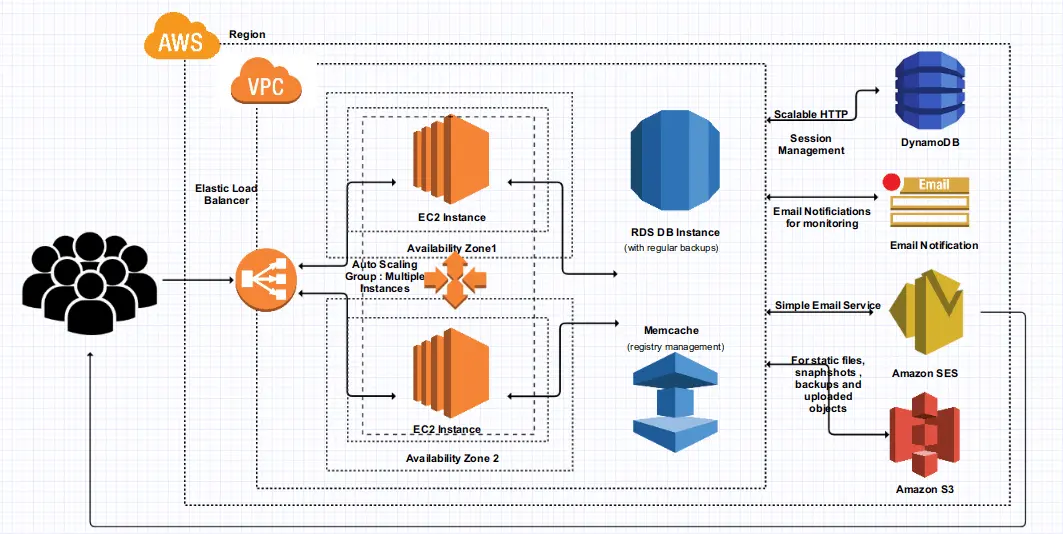
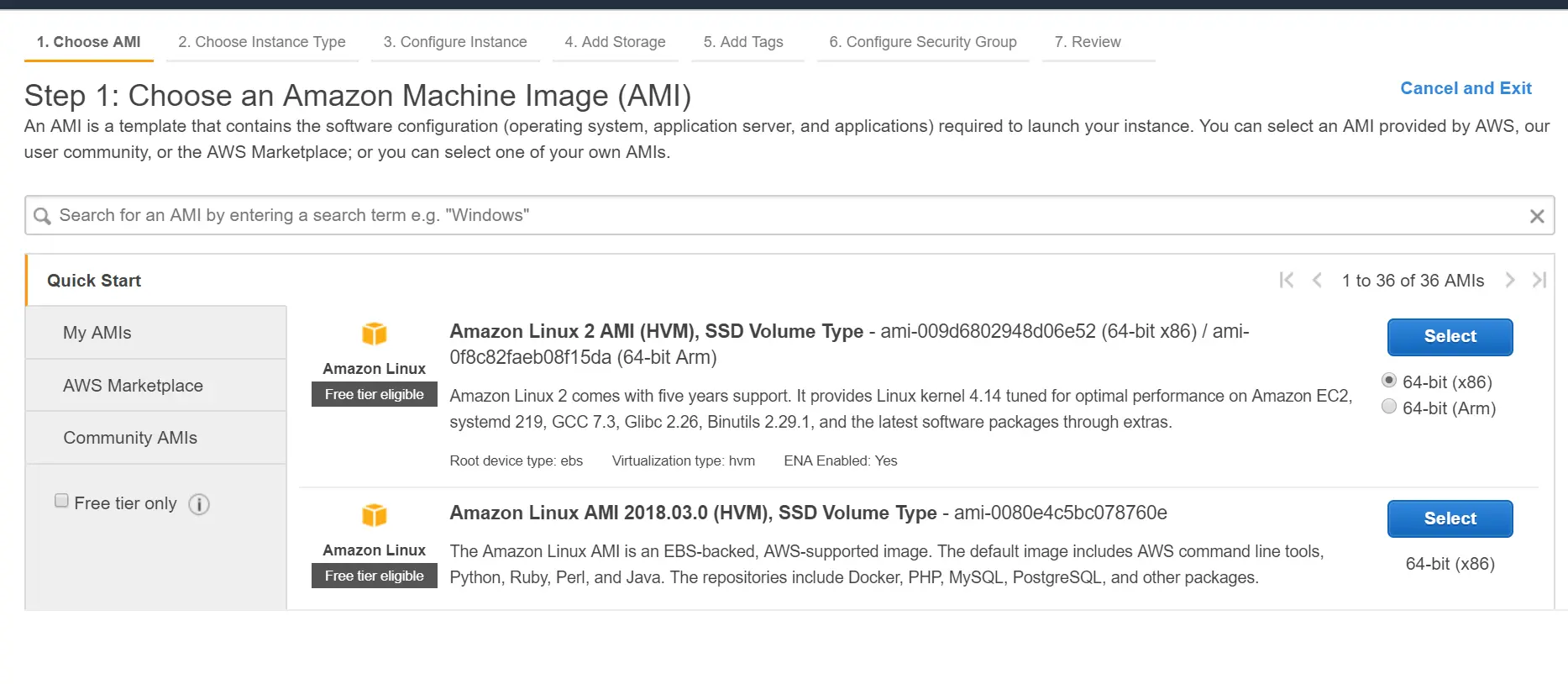
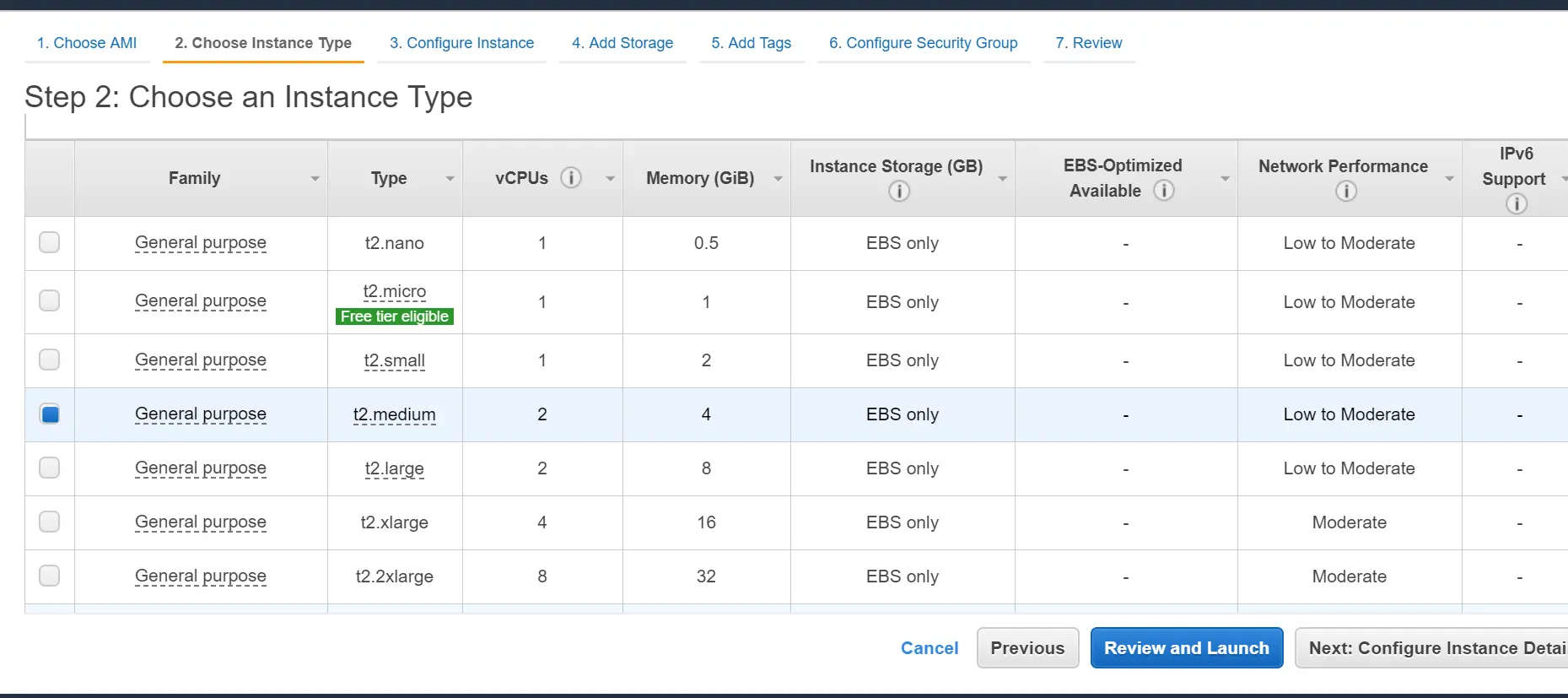
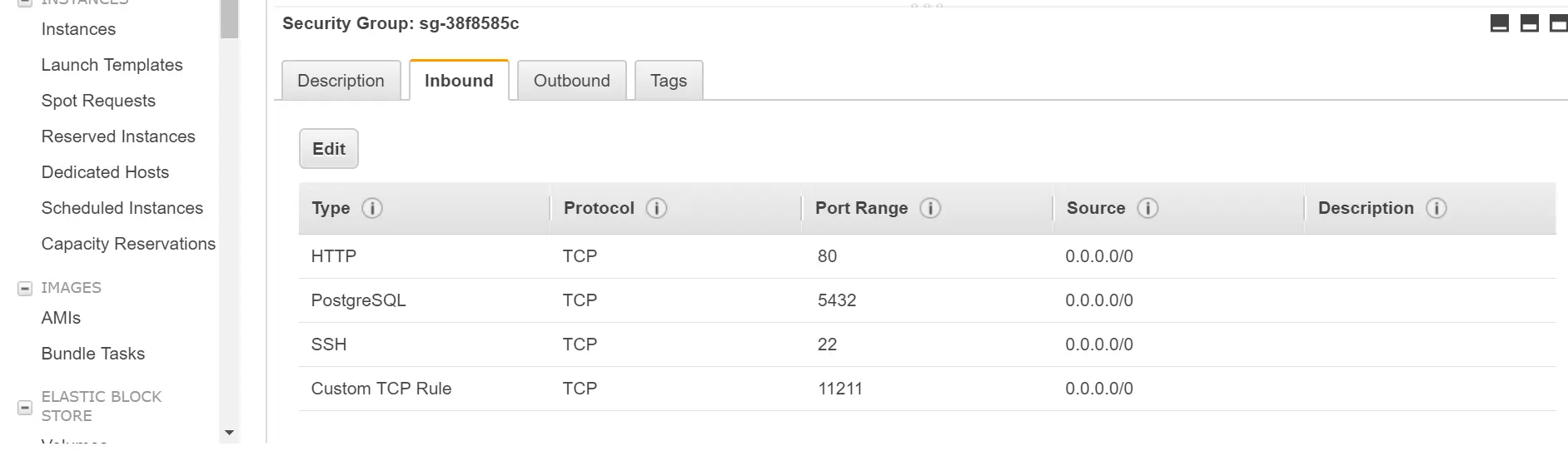
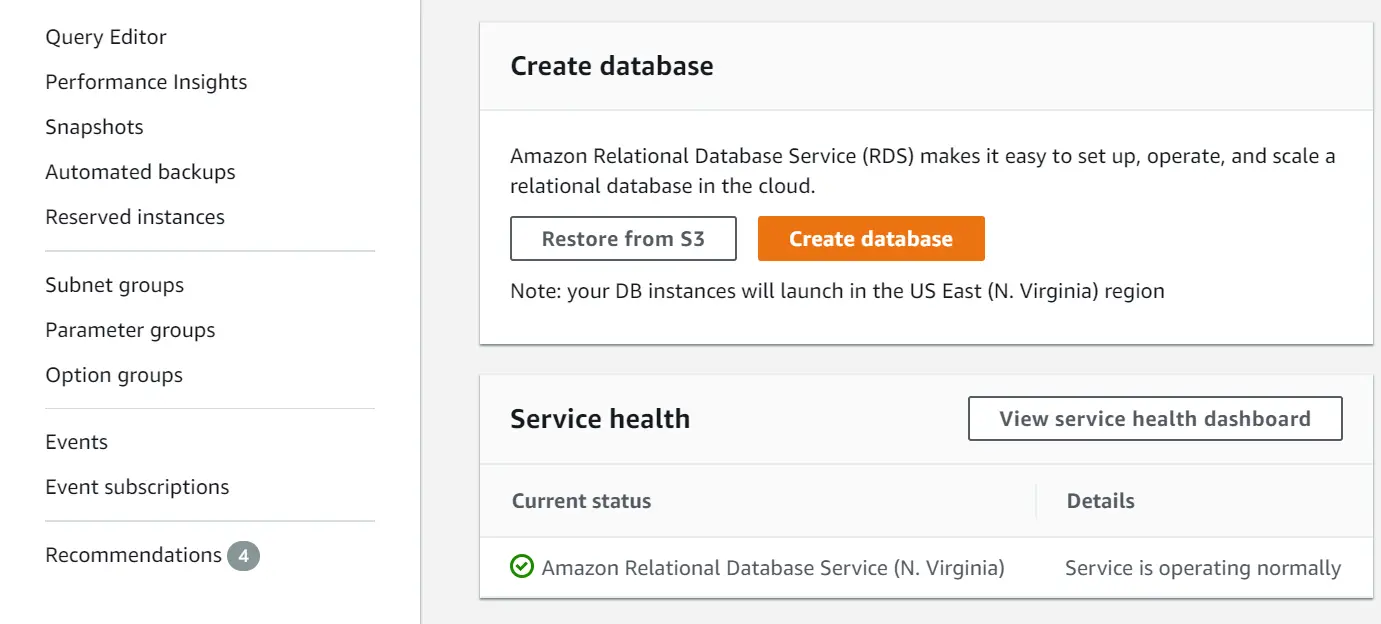
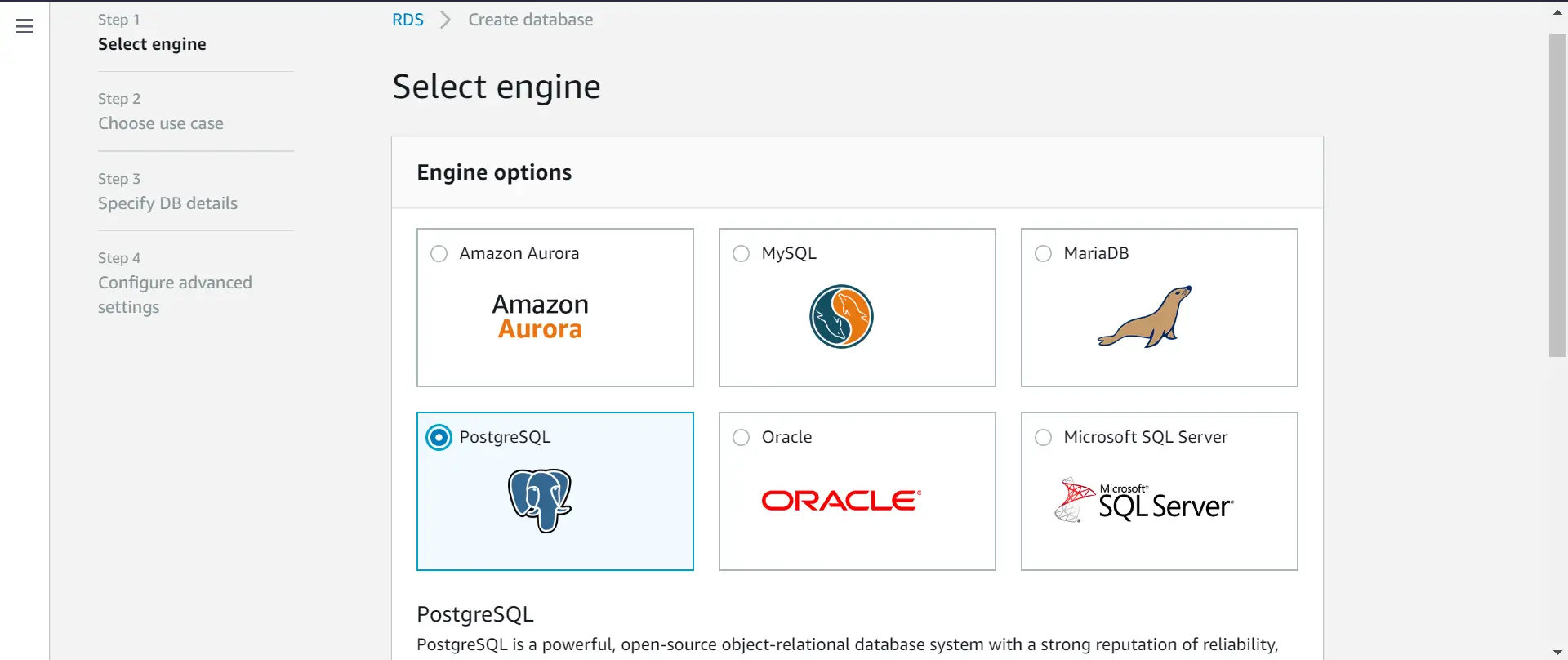
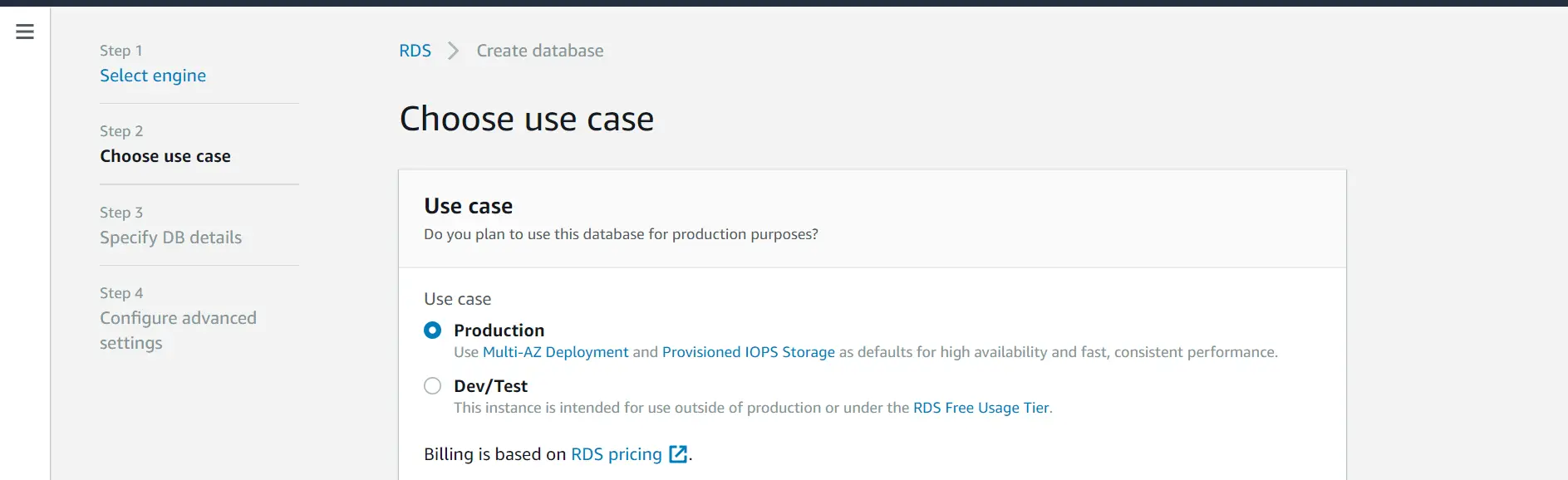
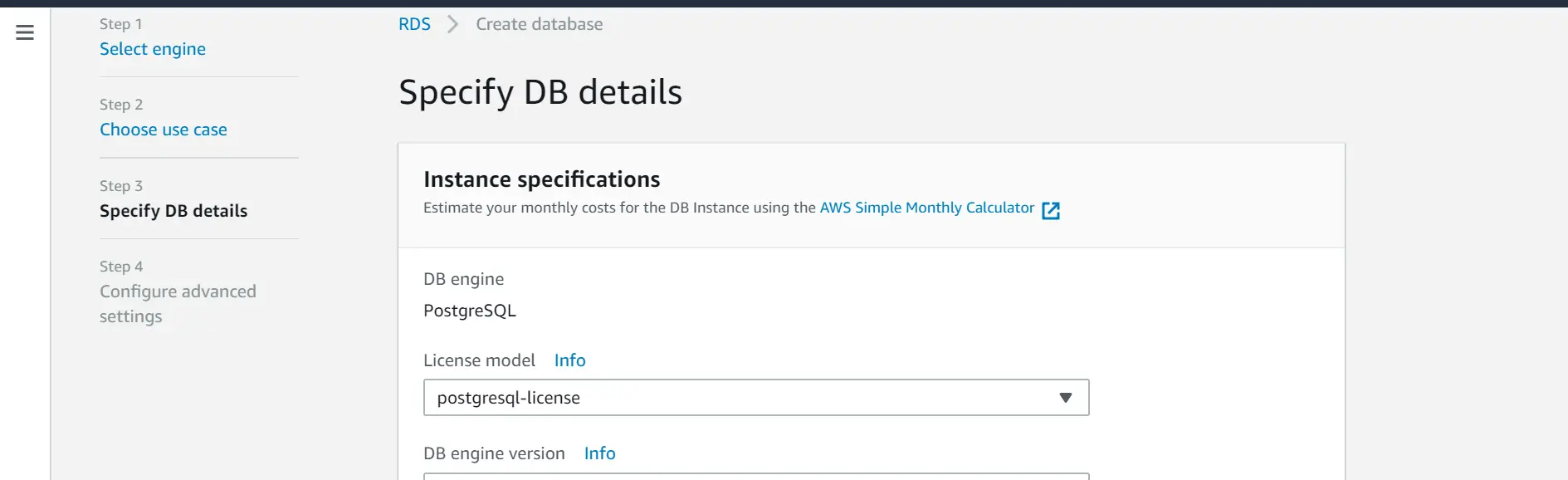
×This guide includes steps to configure a Clustering environment with a load balancer. You can set up miniOrange On-Premise identity servers on multiple servers behind a load balancer with a common database and Memcache environment. You can refer to the architecture diagram below on how miniOrange clustered environment looks like. The following figure summarizes the steps for a two-server configuration.
miniOrange offers free help through a consultation call with our System Engineers to set up our on-premise server.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
When you have large number of concurrent users visiting the site and single server is not able to handle all requests. You can setup a clustered environment to handle traffic and distribute the load properly among multiple servers.
You can setup clustering using On-Premise identity server in following ways:
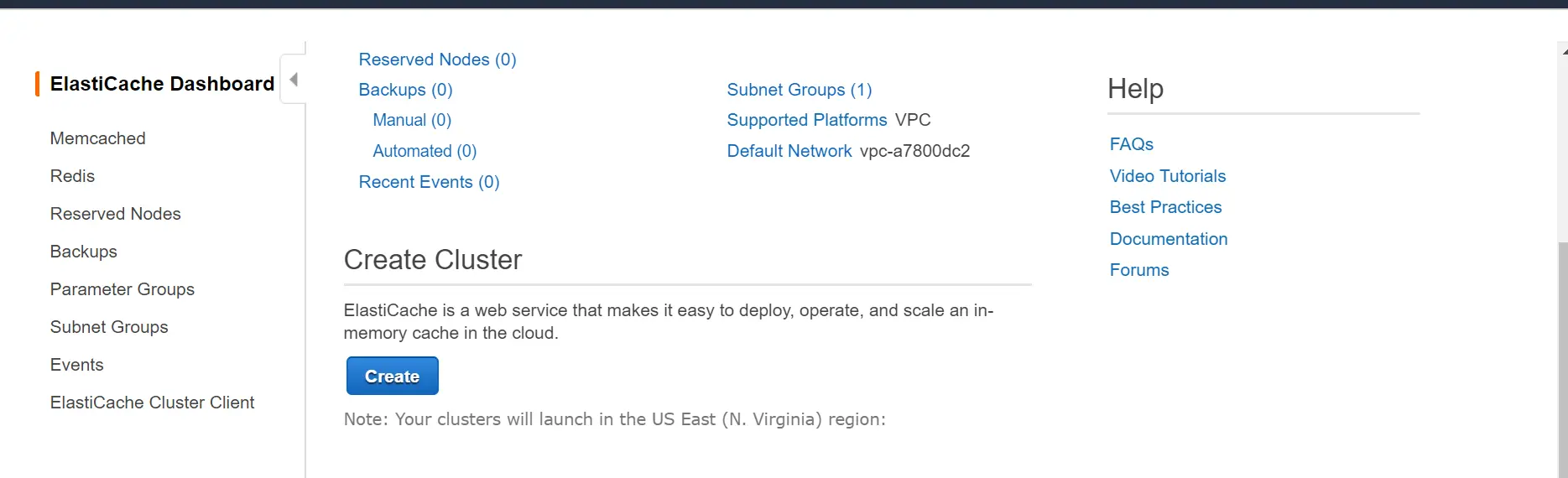
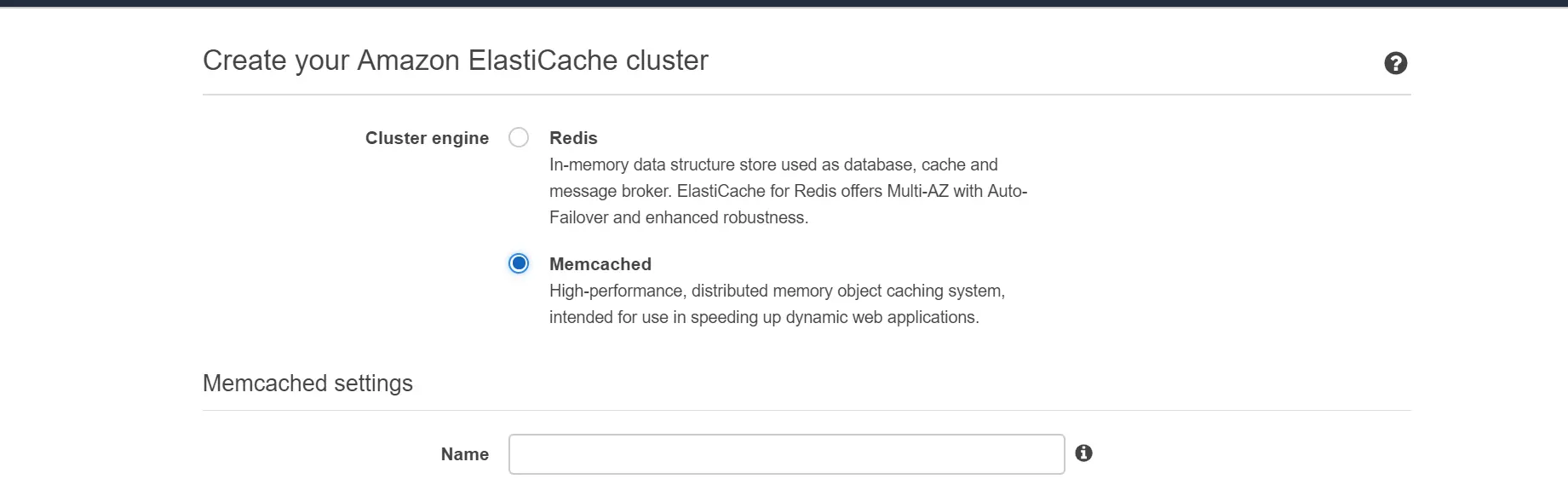
| memcached.server.address | Select the cluster name from aws admin console and copy configuration endpoint here. |
| server.id | beta |