Need Help? We are right here!
Search Results:
×Premium Customers
Integrations
Available for you

Secure autonomous systems that make decisions, chain actions, and move faster than manual controls. Manage what Al agents can access, how they authenticate, and when permissions should change.
Al Agent Authentication
Non-Human Identity Management
Access Management
Audit and Compliance Visibility
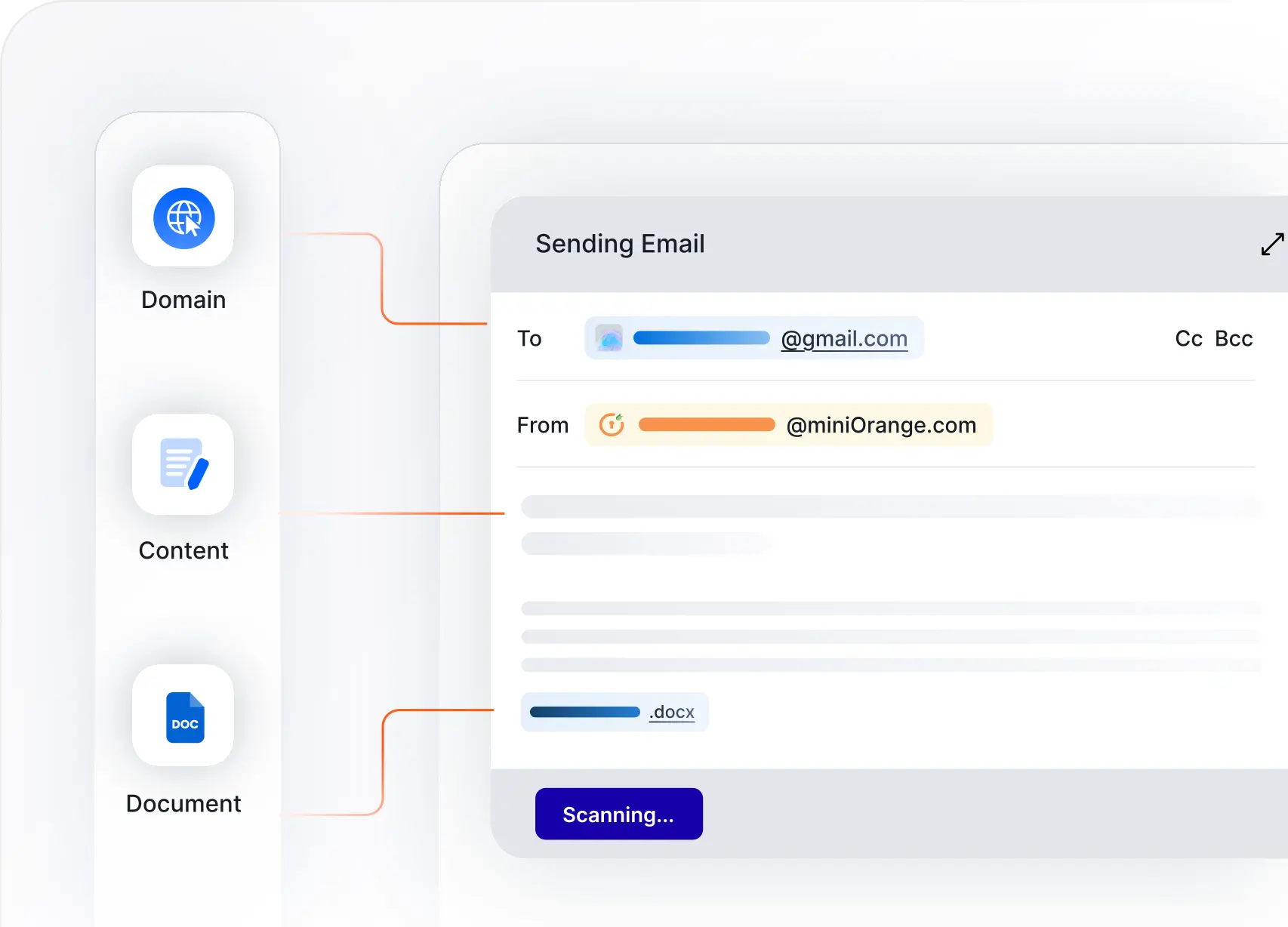
Gain complete control over personal data to prevent exposure and meet regulatory requirements with confidence.
Discover And Classify PIl Across All Environments
Stop Unauthorized PII Transfer In Real Time
Control access to personal data based on policies
Track every Pll interaction with tamper-proof logs
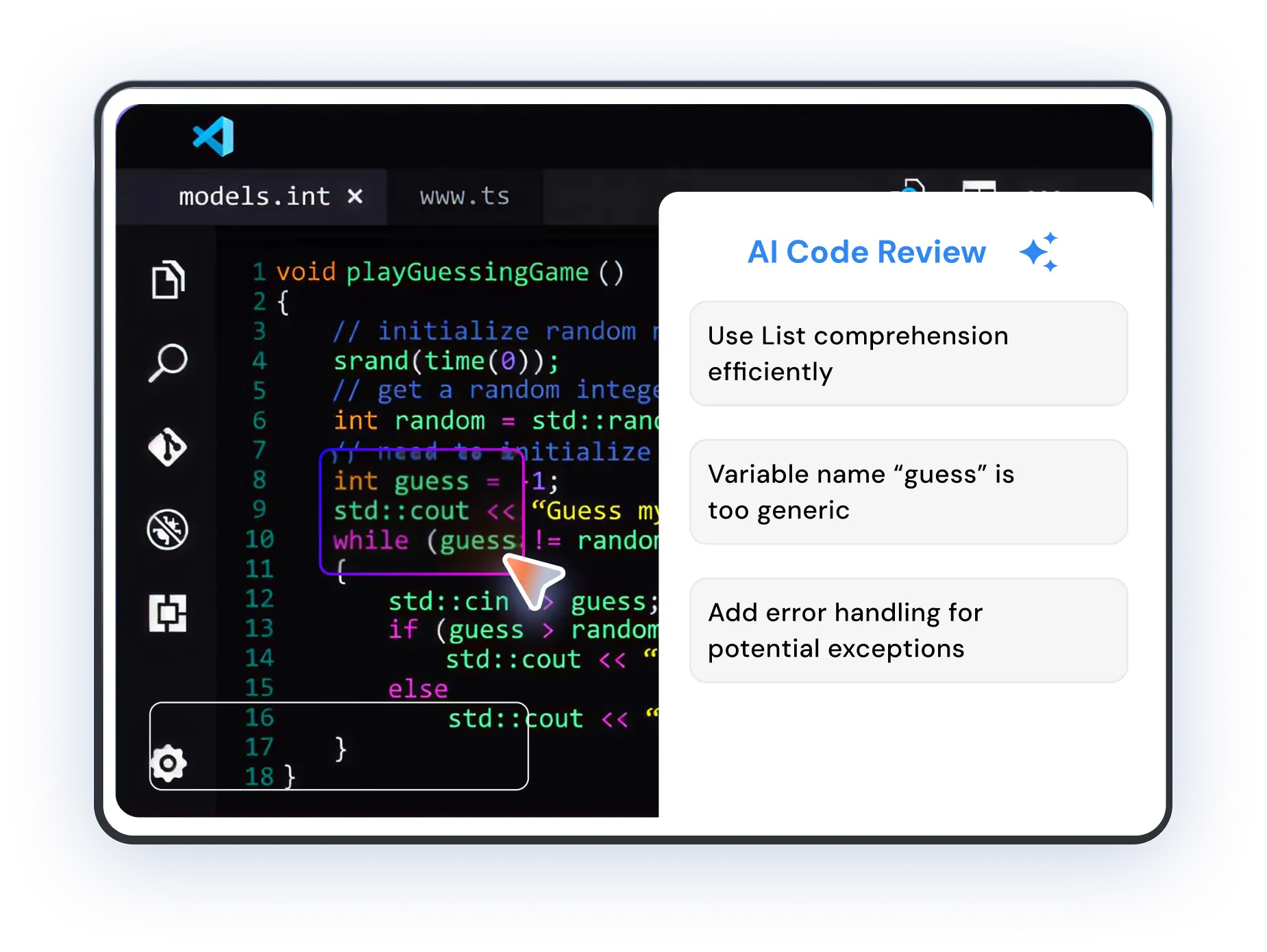
Automate code reviews using the Al model of your choice. This plugin comes with a preset of industry standard coding guidelines, with additional support for custom rules that might be specific to your organization. Comments, suggestions and status changes will automatically be added to the PRS, with an added layer of role based access for security.
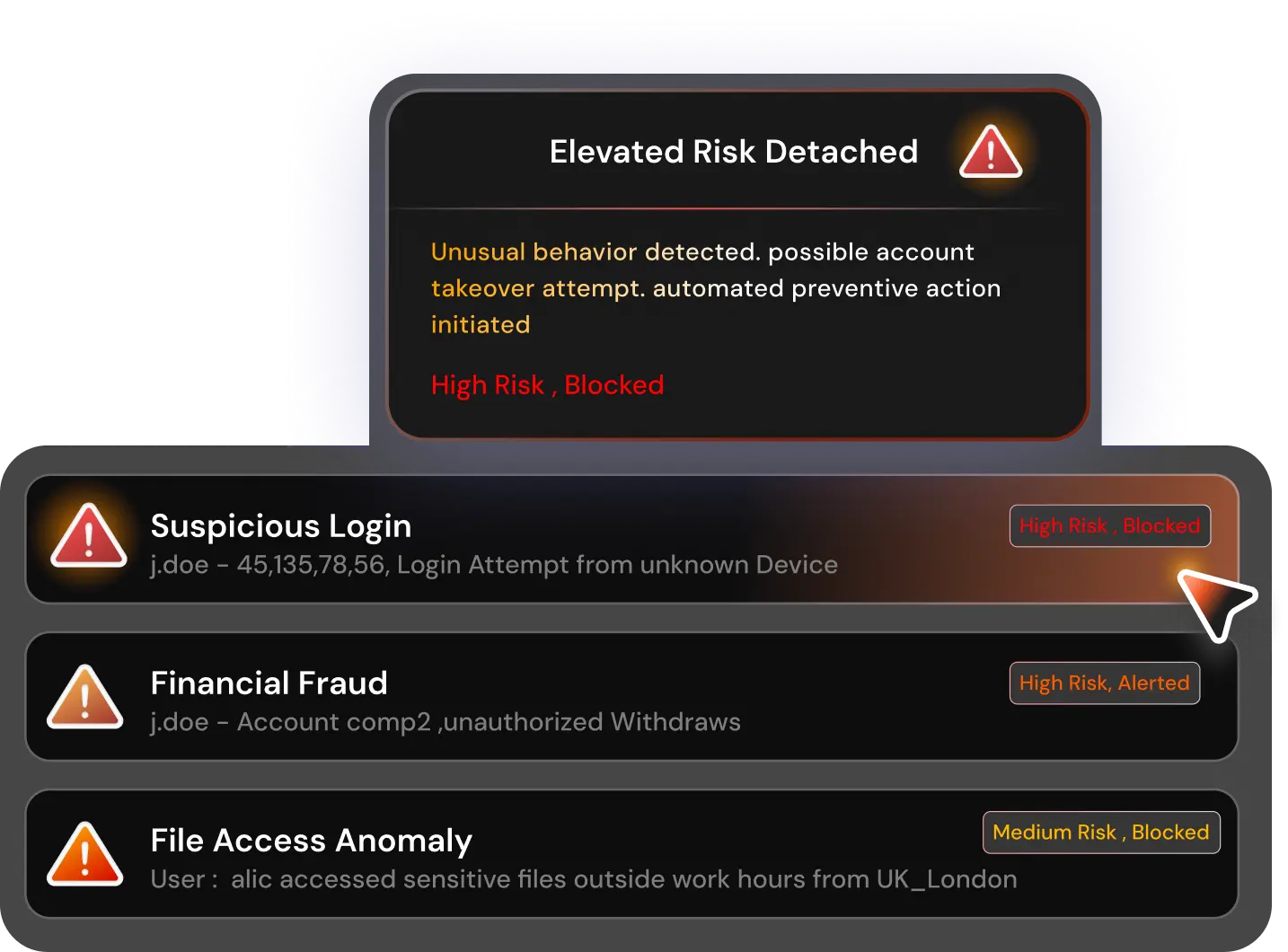
Risk engine leveraging machine learning model to compute risk score, that acts as a behavioural intelligence layer over the application layer. Instead of relying only on predefined rules or known attack signatures, it continuously learns how users, devices, and systems normally behave - and identifies deviations that may indicate fraud, compromise, or insider threats and automatically takes preventive action or flags it based on severity & impact.