Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
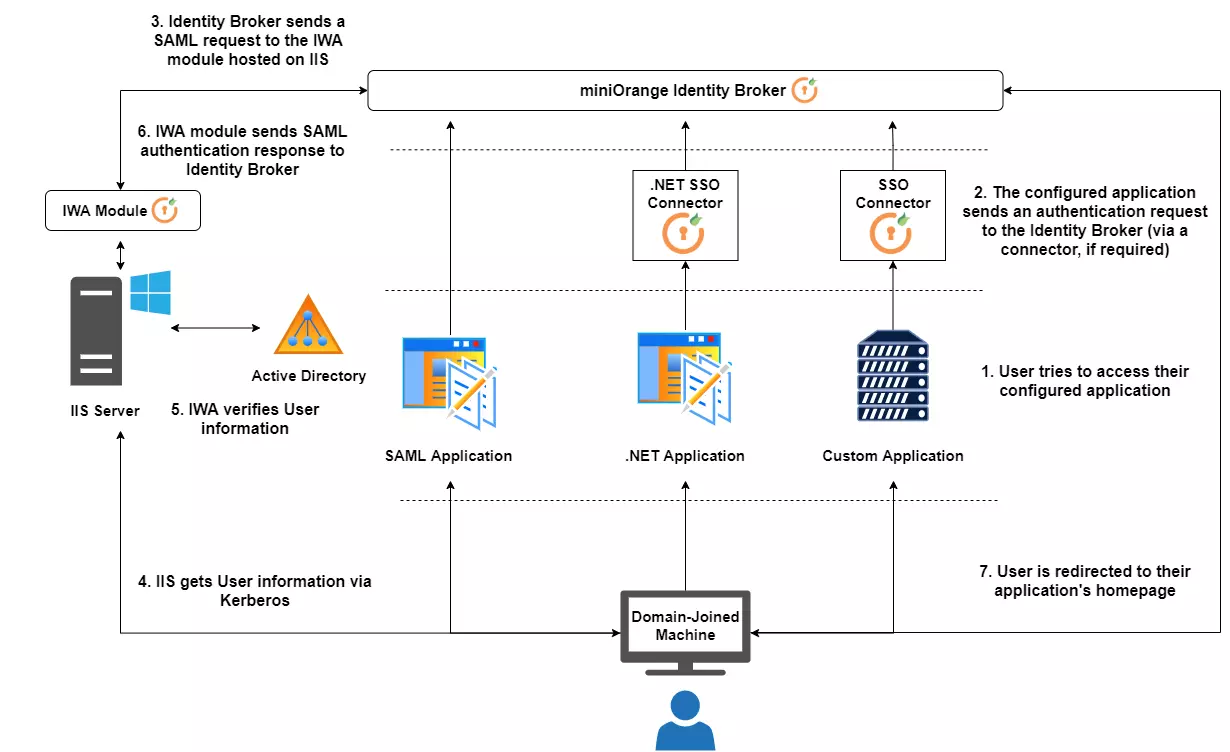
×This guide will give you an overview of how to set up Integrated Windows Authentication for Cloud Applications.
miniOrange Single Sign-On (SSO) server allows you to log into your application without having to re-enter your credentials. You will first need to successfully achieve windows authentication into the Windows domain, after having logged into a system integrated with an Active Directory domain. miniOrange achieves Windows integrated authentication by installing a component on a Windows Server linked to the Active Directory domain. This setup basically acts as a SAML 2.0 Identity Provider. When the user tries to access a cloud application like Salesforce, the request is forwarded to the miniOrange SSO Server. This Server forwards the request to the on-premise miniOrange SAML module installed on the Windows authentication machine. SSO is performed based on the response received from the module. This is how Windows authentication is used to achieve Windows integrated security.
setspn -S HTTP/##Server FQDN## ##Domain Service Account##setspn -S HTTP/server.contoso.com CONTOSO\iwauser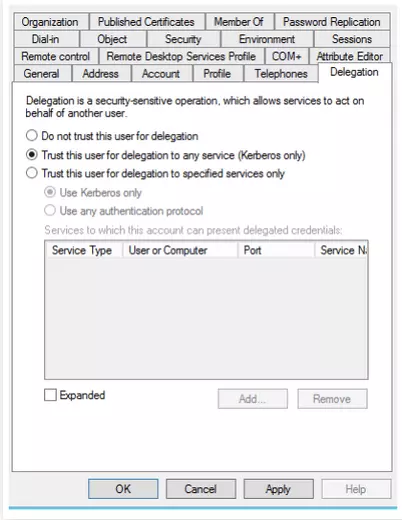
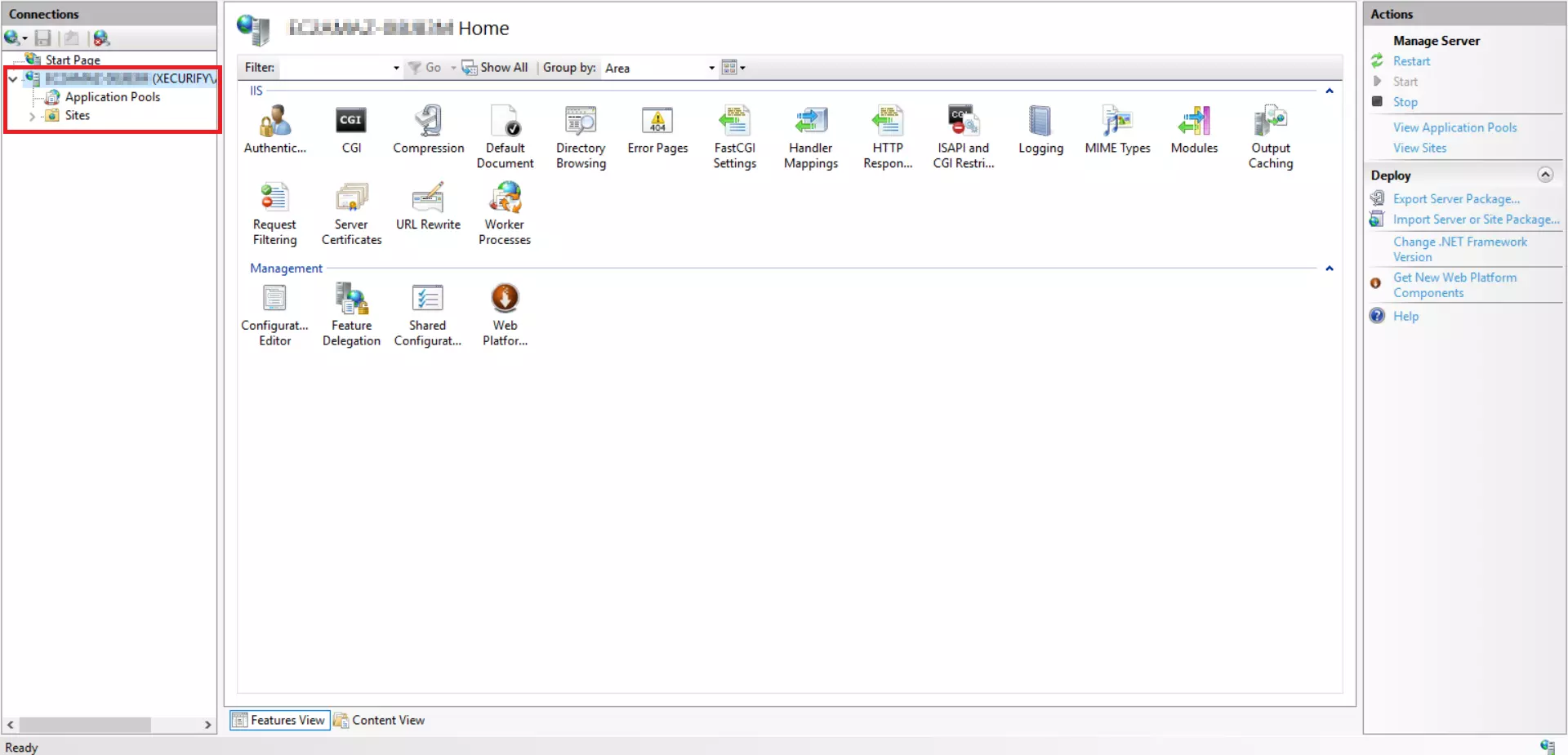
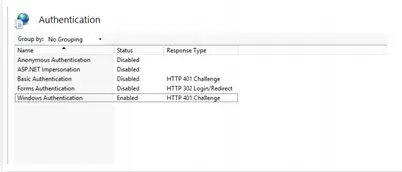
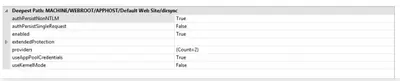
system.webServer/security/authentication/windowsAuthentication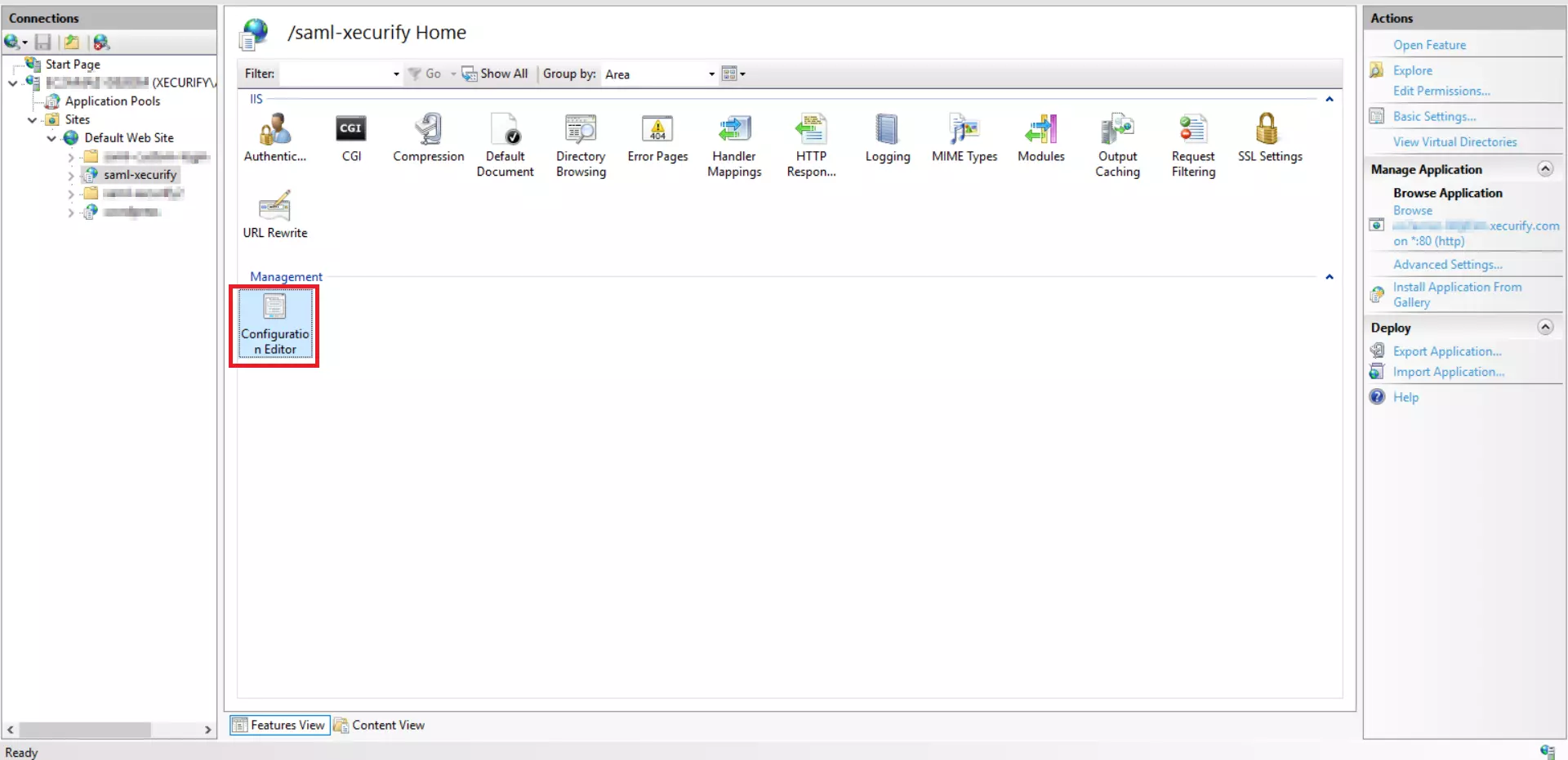
| Parameter | Description | Sample Value |
| $this->ldap_server_url | Full URL of your LDAP server, with port | ldap://server.contoso.com:389 |
| $this->ldap_bind_account_dn | Distinguished Name of your LDAP Service Account | CN=Service User,CN=Users,DC=contoso,DC=com |
| $this->ldap_bind_account_password | Password of your LDAP Service Account | - |
| $this->search_base | Search base in which to look for users | CN=Users,DC=contoso,DC=com |
| $this->search_filter | Search filter | (|(userprincipalname=?)(samaccountname=?)) |
| $this->user_attributes | List of attributes that you want to fetch from AD & send in response | array("givenname", "sn", "mail", "department", "userprincipalname") |
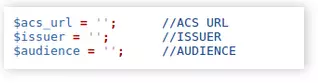
| Parameter | Value |
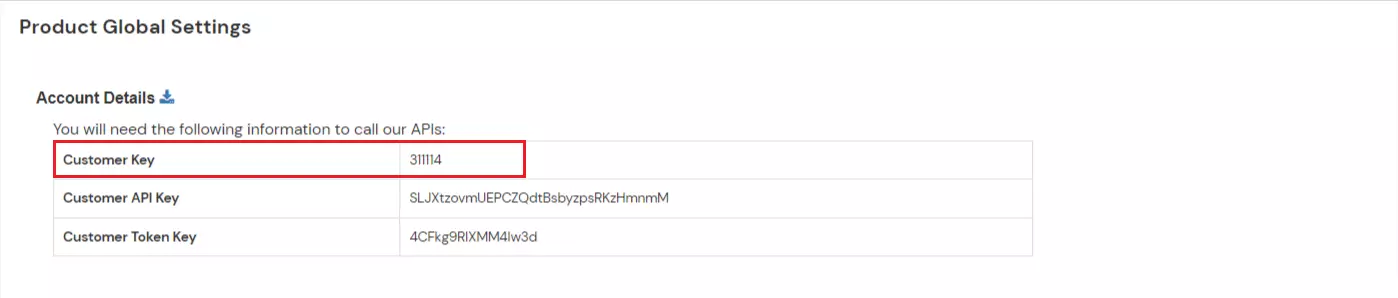
| ACS URL | https://<branding>.xecurify.com/moas/broker/login/saml/acs/<CustomerID> For example, if the branding set in your miniOrange account is iwatest, with customer ID 123456, then the value of this parameter will be: https://iwatest.xecurify.com/moas/broker/login/saml/acs/123456 |
| Issuer | Hostname of the Windows Server, for example https://server.contoso.com |
| Audience | https://login.xecurify.com/moas |
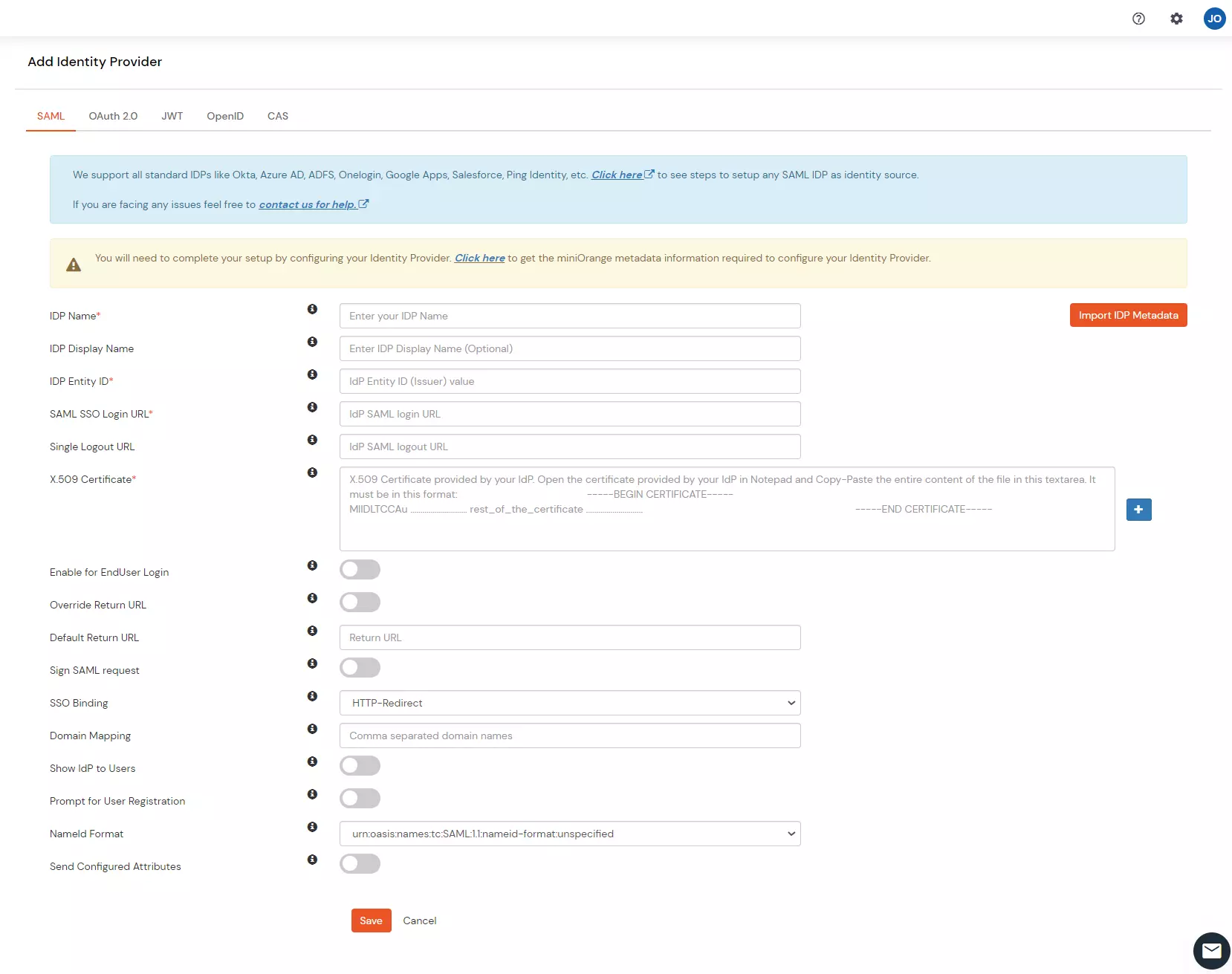
| Parameter | Value |
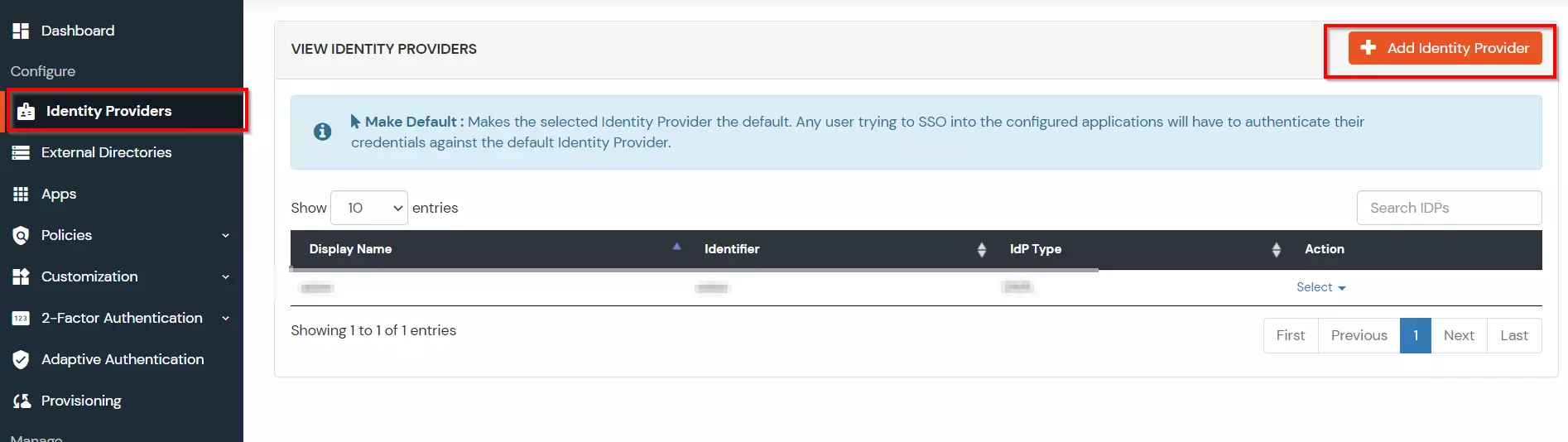
| IDP Entity ID | As set in the previous section under Issuer |
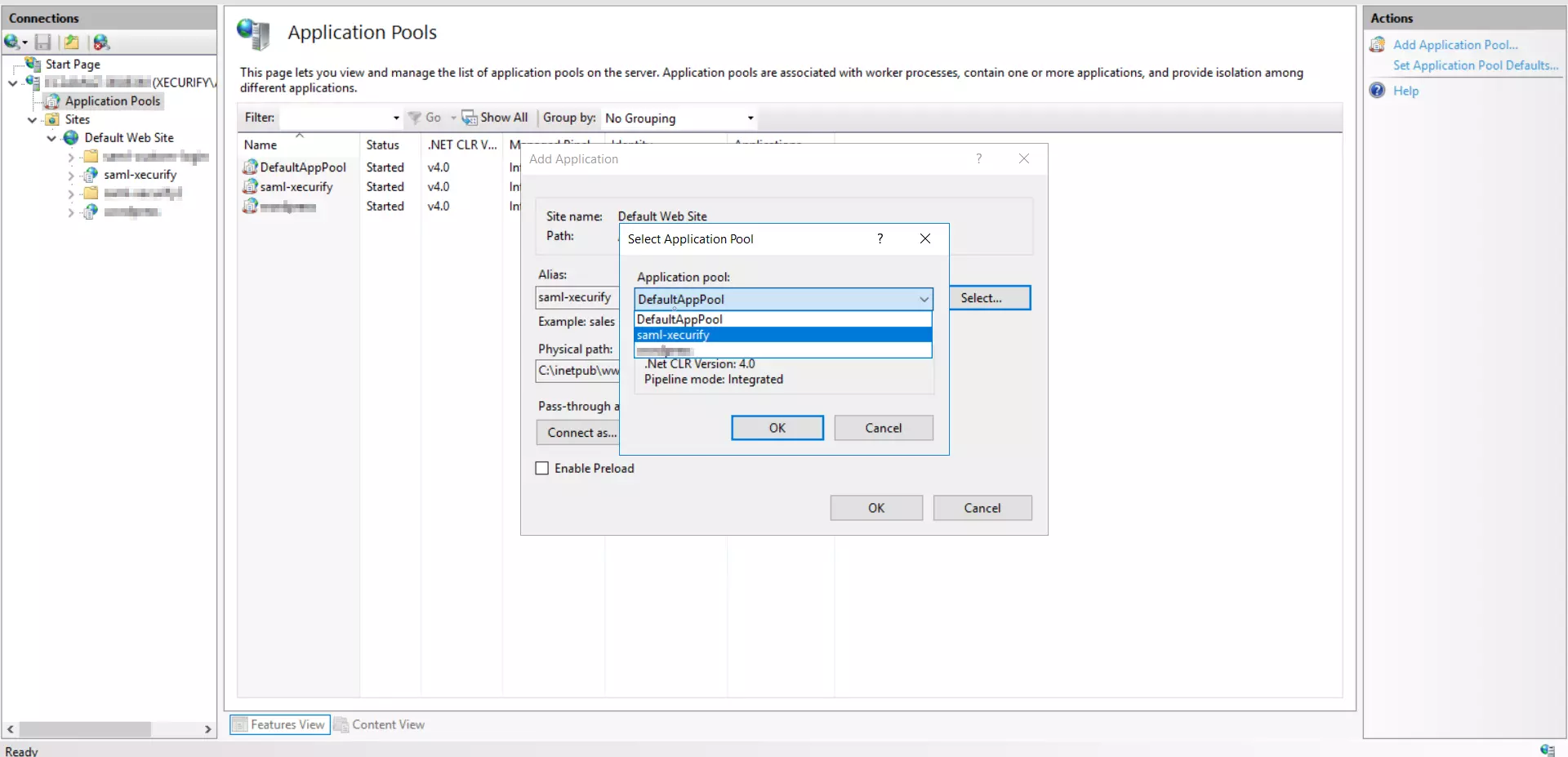
| SAML SSO Login URL | Of the format http://<hostname-of-server>/saml-xecurify/samlsso.php For example, if the FQDN of your Windows Server is server.contoso.com, then the value of this parameter will be: http://server.contoso.com/saml-xecurify/samlsso.php |
| Audience | https://login.xecurify.com/moas |