Overview
Many enterprise applications support both Single Sign-On (SSO) and native login forms. While SSO can enforce Multi-Factor Authentication (MFA), a native login page can create a critical security gap.
Users may bypass the SSO flow by directly accessing the application's login page and authenticating with application credentials, effectively circumventing MFA enforcement.
Security teams require stronger authentication governance that ensures MFA enforcement cannot be bypassed through alternate login paths.
Modern enterprise security teams require:
- Centralized MFA enforcement across applications
- Control over authentication entry points
- Prevention of SSO and MFA bypass attacks
- Identity verification through a centralized Identity Provider
- Secure access architecture without modifying application code
Many legacy and third-party applications do not provide built-in controls to enforce SSO-only authentication, creating potential security vulnerabilities.
The Enterprise Requirement
The organization needed to:
- Enforce Multi-Factor Authentication (MFA) for all users accessing the application
- Prevent users from accessing the native application login page directly
- Ensure authentication always occurs through the miniOrange Identity Provider (IdP)
- Introduce an authentication enforcement layer before application access
- Validate the approach through a controlled proof-of-concept deployment
Although the application was already configured as a SAML application with MFA enabled through miniOrange, the presence of a native login form allowed users to authenticate directly.
The objectiv+e was clear:
Ensure users cannot access the application unless authentication and MFA validation occur through the centralized Identity Provider.
The Solution: Proxy-Based Authentication Enforcement
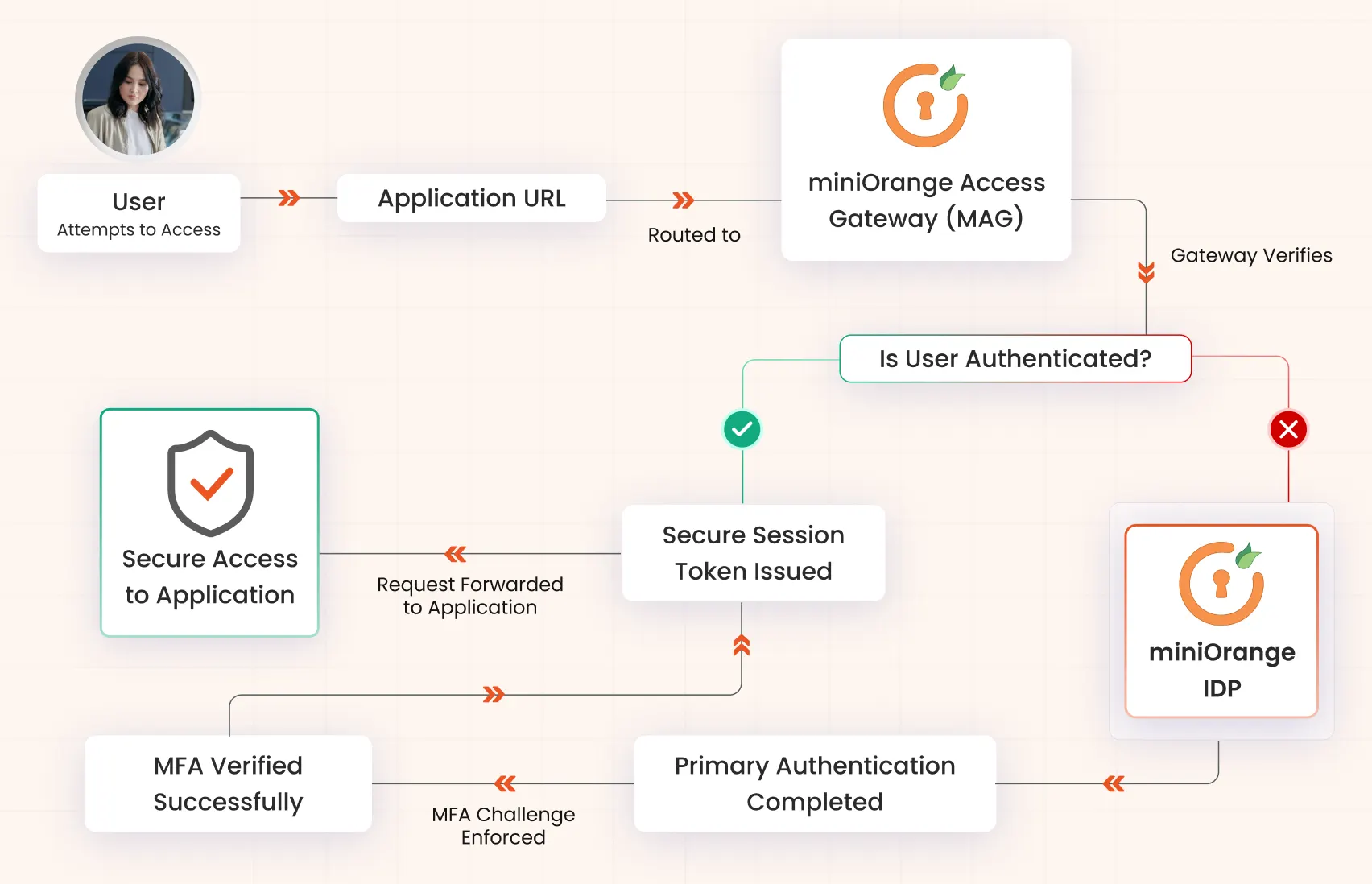
miniOrange implemented a secure access architecture using miniOrange Access Gateway (MAG) deployed as a reverse proxy in front of the application.
The gateway acts as an authentication enforcement layer, ensuring that all user requests are validated before reaching the application.
Instead of allowing users to directly access the application login page, authentication is enforced through the miniOrange Identity Provider with MFA.
Core Components

miniOrange Access Gateway (MAG)
Reverse proxy and authentication enforcement point

miniOrange Identity Provider (IdP)
Centralized authentication and MFA validation engine

Enterprise Application
Protected application accessible only through the Access Gateway
No application session is established until identity verification and MFA validation are successfully completed.
How the Authentication Flow Works
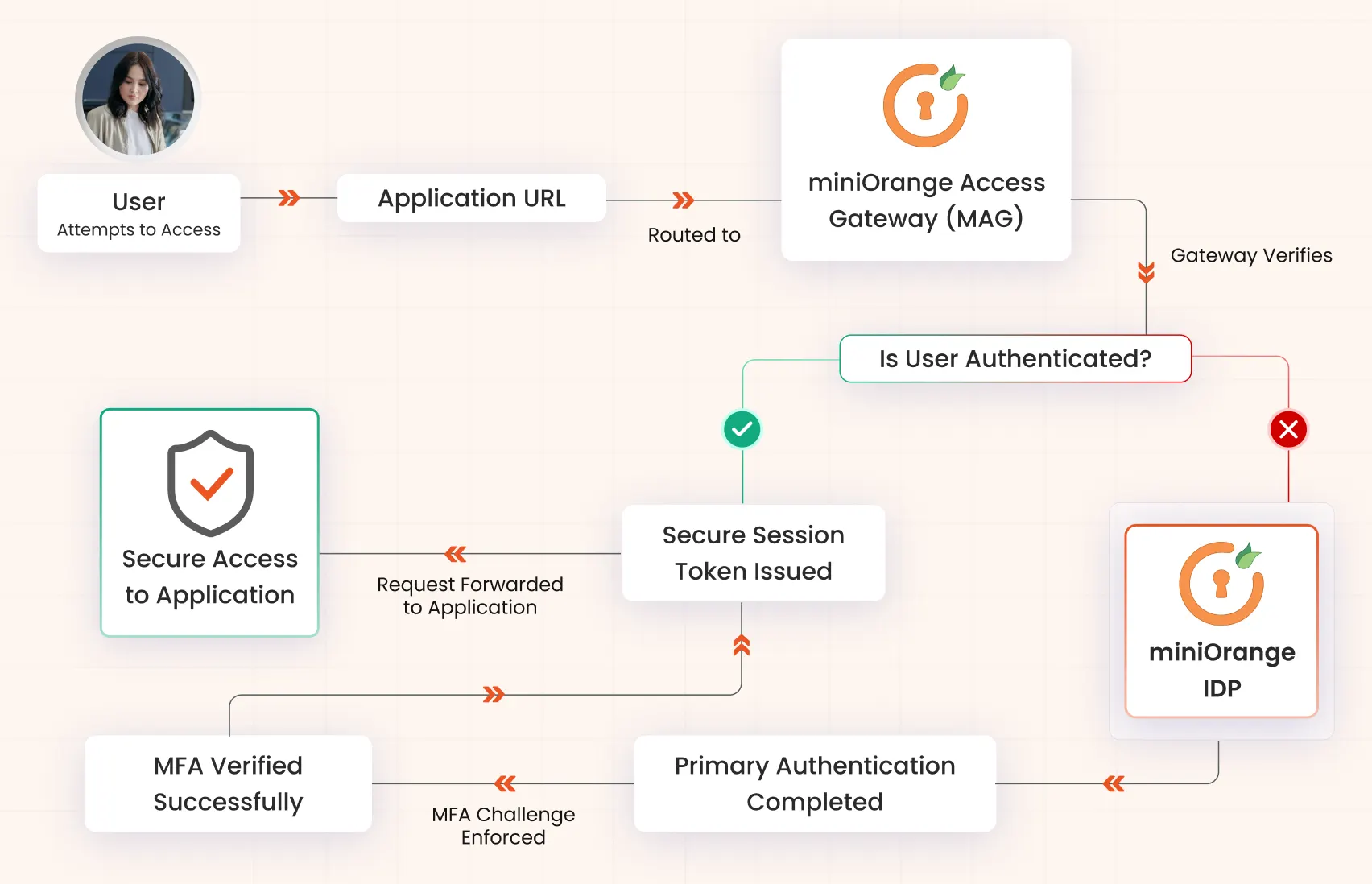
- User attempts to access the application URL
- The request is routed through the miniOrange Access Gateway
- The gateway verifies whether the user is authenticated
- If the user is not authenticated, they are redirected to the miniOrange Identity Provider
- The user completes primary authentication
- The Identity Provider enforces Multi-Factor Authentication (MFA)
- After successful authentication and MFA verification, a secure session token is issued
- The Access Gateway forwards the authenticated request to the application
- The user gains access to the application through the secure proxy path
MFA enforcement occurs before the application session is created, eliminating authentication bypass.
Why Native Authentication Was Not Sufficient
- Direct access to the application's login page allowed users to bypass SSO authentication
- MFA enforcement applied only to the SSO flow
- No control existed over the authentication entry point
- Authentication policies could not be enforced consistently across access paths
By introducing a proxy-based authentication enforcement layer, the organization gained centralized identity governance and complete control over how users access the application.
Security & Operational Outcomes
- Mandatory MFA enforcement for all application access
- Prevention of direct login bypass through native login pages
- Centralized authentication via the Identity Provider
- Stronger identity verification and access control
- Secure application access without modifying application code
- Improved authentication governance and security posture
The proof-of-concept successfully demonstrated that SSO and MFA bypass could be completely prevented.
Production-Ready Architecture
- The validated architecture supports enterprise deployment with:
- High-availability Identity Provider infrastructure
- Load-balanced Access Gateway nodes
- Secure proxy-based application access
- Centralized authentication logging and monitoring
- Scalable IAM infrastructure for enterprise workloads
The POC confirmed both security enforcement and scalability for production deployment..
Ideal For Organizations That
- Need to enforce MFA for applications with native login pages
- Want to prevent SSO bypass attacks
- Require centralized Identity and Access Management (IAM)
- Need to enforce authentication without modifying application code
- Operate in security-sensitive or compliance-driven environments